跟着 Lua 5.1 官方参考文档学习 Lua (5)
文章目录
- 2.10 – Garbage Collection
- 2.10.1 – Garbage-Collection Metamethods
- 2.10.2 – Weak Tables
2.10 – Garbage Collection
Lua performs automatic memory management. This means that you have to worry neither about allocating memory for new objects nor about freeing it when the objects are no longer needed. Lua manages memory automatically by running a garbage collector from time to time to collect all dead objects (that is, objects that are no longer accessible from Lua). All memory used by Lua is subject to automatic management: tables, userdata, functions, threads, strings, etc.
补充:
Since its first version until version 5.0, Lua always used a simple mark-andsweep garbage collector. This collector is sometimes called a “stop-the-world” collector. This means that, from time to time, Lua stops interpreting the main program to perform a whole garbage-collection cycle. Each cycle comprises four phases: mark, cleaning, sweep, and finalization.
Lua starts the mark phase marking as alive its root set, the objects that Lua has direct access to: the registry and the main thread. Any object stored in a live object is reachable by the program, and therefore is marked as alive too. The mark phase ends when all reachable objects are marked as alive.
Before starting the sweep phase, Lua performs the cleaning phase, which is related to finalizers and weak tables.
First, it traverses all userdata looking for non-marked userdata with a __gc metamethod; those userdata are marked as alive and put in a separate list, to be used in the finalization phase.
Second, Lua traverses its weak tables and removes from them all entries wherein either the key or the value is not marked.
The sweep phase traverses all Lua objects. (To allow this traversal, Lua keeps all objects it creates in a linked list.) If an object is not marked as alive, Lua collects it. Otherwise, Lua clears its mark, in preparation for the next cycle.
The last phase, finalization, calls the finalizers of the userdata that were separated in the cleaning phase. This is done after the other phases to simplify error handling. A wrong finalizer may throw an error, but the garbage collector cannot stop during other phases of a collection, at the risk of leaving Lua in an inconsistent state. If it stops during this last phase, however, there is no problem: the next cycle will call the finalizers of the userdata that were left in the list.
With version 5.1 Lua got an incremental collector. This new incremental collector performs the same steps as the old one, but it does not need to stop the world while it runs. Instead, it runs interleaved with the interpreter. Every time the interpreter allocates some fixed amount of memory, the collector runs a small step. This means that, while the collector works, the interpreter may change an object’s reachability. To ensure the correctness of the collector, some operations in the interpreter have barriers that detect dangerous changes and correct the marks of the objects involved.
To avoid too much complexity, the incremental collector performs some operations atomically; that is, it cannot stop while performing those operations. In other words, Lua still “stops the world” during an atomic operation. If an atomic operation takes too long to complete, it may interfere with the timing of your program. The main atomic operations are table traversal and the cleaning phase.
The atomicity of table traversal means that the collector never stops while traversing a table. This can be a problem only if your program has a really huge table. If you have this kind of problem, you should break the table in smaller parts. (That may be a good idea even if you do not have problems with the garbage collector.) A typical reorganization is to break the table hierarchically, grouping related entries into subtables. Notice that what matters is the number of entries in the table, not the size of each entry.
The atomicity of the cleaning phase implies that the collector collects all userdata to be finalized and clears all weak tables in one step. This can be a problem if your program has huge quantities of userdata or huge numbers of entries in weak tables (either in a few large weak tables or in countless weak tables).
Lua implements an incremental mark-and-sweep collector. It uses two numbers to control its garbage-collection cycles: the garbage-collector pause and the garbage-collector step multiplier. Both use percentage points as units (so that a value of 100 means an internal value of 1).
The garbage-collector pause controls how long the collector waits before starting a new cycle. Larger values make the collector less aggressive. Values smaller than 100 mean the collector will not wait to start a new cycle. A value of 200 means that the collector waits for the total memory in use to double before starting a new cycle.
补充:
The pause parameter controls how long the collector waits between finishing a collection and starting a new one. Lua uses an adaptive algorithm to start a collection: given that Lua is using m Kbytes when a collection ends, it waits until it is using m*pause Kbytes to start a new collection. So, a pause of 100% starts a new collection as soon as the previous one ends. A pause of 200% waits for memory usage to double before starting the collector; this is the default value. You can set a lower pause if you want to trade more CPU time for lower memory usage. Typically, you should keep this value between 100% and 300%.
The step multiplier controls the relative speed of the collector relative to memory allocation. Larger values make the collector more aggressive but also increase the size of each incremental step. Values smaller than 100 make the collector too slow and can result in the collector never finishing a cycle. The default, 200, means that the collector runs at “twice” the speed of memory allocation.
补充:
The stepmul parameter controls how much work the collector does for each kilobyte of memory allocated. The higher this value the less incremental is the collector. A huge value like 100000000% makes the collector work like a nonincremental collector. The default value is 200%. Values lower than 100% make the collector so slow that it may never finish a collection.
You can change these numbers by calling lua_gc in C or collectgarbage in Lua. With these functions you can also control the collector directly (e.g., stop and restart it).
补充:
Lua offers an API that allows us to exert some control over the garbage collector.
From C we use lua_gc:
int lua_gc (lua_State *L, int what, int data);From Lua we use the collectgarbage function:
collectgarbage(what [, data])Both offer the same functionality. The what argument (an enumeration value in C, a string in Lua) specifies what to do. The options are:
LUA_GCSTOP (“stop”): stops the collector until another call to collectgarbage (or to lua_gc) with the option “restart”, “collect”, or “step”.
LUA_GCRESTART (“restart”): restarts the collector.
LUA_GCCOLLECT (“collect”): performs a complete garbage-collection cycle, so that all unreachable objects are collected and finalized. This is the default option for collectgarbage.
LUA_GCSTEP (“step”): performs some garbage-collection work. The amount of work is given by the value of data in a non-specified way (larger values mean more work).
LUA_GCCOUNT (“count”): returns the number of kilobytes of memory currently in use by Lua. The count includes dead objects that were not collected yet.
LUA_GCCOUNTB (not available): returns the fraction of the number of kilobytes of memory currently in use by Lua.
In C, the total number of bytes can be computed by the next expression (assuming that it fits in an int):
lua_gc(L, LUA_GCCOUNT, 0)*1024 + lua_gc(L, LUA_GCCOUNTB, 0)In Lua, the result of collectgarbage(“count”) is a floating-point number, and the total number of bytes can be computed as follows:
collectgarbage("count") * 1024So, collectgarbage has no equivalent to this option.
LUA_GCSETPAUSE (“setpause”): sets the collector’s pause parameter. The value is given by data in percentage points: when data is 100 the parameter is set to 1 (100%).
LUA_GCSETSTEPMUL (“setstepmul”): sets the collector’s stepmul parameter. The value is given by data also in percentage points.
The other options of lua_gc give you more explicit control over the collector.
Games are typical clients for this kind of control. For instance, if you do not want any garbage-collection work during some periods, you can stop it with a call collectgarbage(“stop”) and then restart it with collectgarbage(“restart”).
In systems where you have periodic idle phases, you can keep the collector stopped and call collectgarbage(“step”,n) during the idle time. To set how much work to do at each idle period, you can either choose experimentally an appropriate value for n or calls collectgarbage in a loop, with n set to zero (meaning small steps), until the period expires.
2.10.1 – Garbage-Collection Metamethods
Using the C API, you can set garbage-collector metamethods for userdata (see §2.8). These metamethods are also called finalizers. Finalizers allow you to coordinate Lua’s garbage collection with external resource management (such as closing files, network or database connections, or freeing your own memory).
Garbage userdata with a field __gc in their metatables are not collected immediately by the garbage collector. Instead, Lua puts them in a list. After the collection, Lua does the equivalent of the following function for each userdata in that list:
function gc_event (udata)local h = metatable(udata).__gcif h thenh(udata)endend
At the end of each garbage-collection cycle, the finalizers for userdata are called in reverse order of their creation, among those collected in that cycle. That is, the first finalizer to be called is the one associated with the userdata created last in the program. The userdata itself is freed only in the next garbage-collection cycle.
2.10.2 – Weak Tables
A weak table is a table whose elements are weak references. A weak reference is ignored by the garbage collector. In other words, if the only references to an object are weak references, then the garbage collector will collect this object.
A weak table can have weak keys, weak values, or both. A table with weak keys allows the collection of its keys, but prevents the collection of its values. A table with both weak keys and weak values allows the collection of both keys and values. In any case, if either the key or the value is collected, the whole pair is removed from the table.
The weakness of a table is controlled by the __mode field of its metatable. If the __mode field is a string containing the character ‘k’, the keys in the table are weak. If __mode contains ‘v’, the values in the table are weak.
After you use a table as a metatable, you should not change the value of its __mode field. Otherwise, the weak behavior of the tables controlled by this metatable is undefined.
补充:
A garbage collector can collect only what it can be sure is garbage; it cannot guess what you consider garbage.
A typical example is a stack, implemented with an array and an index to the top. You know that the valid part of the array goes only up to the top, but Lua does not. If you pop an element by simply decrementing the top, the object left in the array is not garbage for Lua. Similarly, any object stored in a global variable is not garbage for Lua, even if your program will never use it again. In both cases, it is up to you (i.e., your program) to assign nil to these positions so that they do not lock an otherwise free object.
However, simply cleaning your references is not always enough. Some constructions need extra collaboration between the program and the collector.
A typical example happens when you want to keep a collection of all live objects of some kind (e.g., files) in your program. This task seems simple: all you have to do is to insert each new object into the collection. However, once the object is inside the collection, it will never be collected! Even if no one else points to it, the collection does. Lua cannot know that this reference should not prevent the reclamation of the object, unless you tell Lua about this fact.
Weak tables are the mechanism that you use to tell Lua that a reference should not prevent the reclamation of an object. A weak reference is a reference to an object that is not considered by the garbage collector. If all references pointing to an object are weak, the object is collected and somehow these weak references are deleted. Lua implements weak references as weak tables: A weak table is a table whose entries are weak. This means that, if an object is held only inside weak tables, Lua will eventually collect the object.
Tables have keys and values, and both may contain any kind of object. Under normal circumstances, the garbage collector does not collect objects that appear as keys or as values of an accessible table. That is, both keys and values are strong references, as they prevent the reclamation of objects they refer to. In a weak table, keys and values may be weak. This means that there are three kinds of weak tables: tables with weak keys, tables with weak values, and fully weak tables, where both keys and values are weak. Irrespective of the table kind, when a key or a value is collected the whole entry disappears from the table .
例子:弱表
-- 创建一个弱表
local weakTable = setmetatable({}, {__mode = "v"}) -- "v" 表示值是弱引用-- 创建一个对象
local obj = {name = "some object"}-- 将对象插入到弱表中
weakTable[1] = obj-- 此时,obj 还存在于 weakTable 中,并且没有其他引用指向它
print(weakTable[1].name) -- 输出: some object-- 删除强引用
obj = nil-- 因为 obj 没有其他强引用,Lua 会在下一次垃圾回收时回收它
collectgarbage() -- 强制进行垃圾回收-- 现在,weakTable[1] 会变成 nil,因为 obj 被回收
print(weakTable[1]) -- 输出: nil例子:弱表
a = {}
b = {__mode = "k"}
setmetatable(a, b) -- now ’a’ has weak keys
key = {} -- creates first key
a[key] = 1
key = {} -- creates second key
a[key] = 2
collectgarbage() -- forces a garbage collection cycle
for k, v in pairs(a) do print(v) end
--> 2
Notice that only objects can be collected from a weak table. Values, such as numbers and booleans, are not collectible. For instance, if we insert a numeric key in table a (from our previous example), it will never be removed by the collector. Of course, if the value corresponding to a numeric key is collected, then the whole entry is removed from the weak table.
From the programmer’s point of view, string s are values, not objects. Therefore, like a number or a boolean, a string is not removed from weak tables (unless its associated value is collected).
A common programming technique is to trade space for time. You can speed up some functions by memoizing their results so that, later, when you call the function with the same argument, it can reuse the result.
例子:
-- the server can memoize the results from loadstring using an auxiliary table.
local results = {}
-- The savings with this scheme can be huge. However, it may also cause unsuspected waste.
-- A weak table providesa simple solution to this problem. If the results table has weak values, each
-- garbage-collection cycle will remove all translations not in use at that moment
-- (which means virtually all of them)
setmetatable(results, {__mode = "v"}) -- make values weakfunction mem_loadstring (s)local res = results[s]if res == nil then -- result not available?res = assert(loadstring(s)) -- compute new resultresults[s] = res -- save for later reuseendreturn res
end
The memoize technique is useful also to ensure the uniqueness of some kind of object. For instance, assume a system that represents colors as tables, with fields red, green, and blue in some range. A naive color factory generates a new color for each new request:
function createRGB (r, g, b)return {red = r, green = g, blue = b}
end
Using the memoize technique, we can reuse the same table for the same color. To create a unique key for each color, we simply concatenate the color indices with a separator in between:
local results = {}
setmetatable(results, {__mode = "v"}) -- make values weak
function createRGB (r, g, b)local key = r .. "-" .. g .. "-" .. blocal color = results[key]if color == nil thencolor = {red = r, green = g, blue = b}results[key] = colorendreturn color
end
An interesting consequence of this implementation is that the user can compare colors using the primitive equality operator, because two coexistent equal colors are always represented by the same table.
Another important use of weak tables is to associate attributes with objects. There are endless situations where we need to attach some attribute to an object: names to functions, default values to tables, sizes to arrays, and so on.
In all these cases, we need an alternative way to associate attributes to objects. Of course, an external table provides an ideal way to associate attributes to objects (it is not by chance that
tables are sometimes called associative arrays). We use the objects as keys, and their attributes as values. An external table can keep attributes of any type of object, as Lua allows us to use any type of object as a key. Moreover, attributes kept in an external table do not interfere with other objects, and can be as private as the table itself.
However, this seemingly perfect solution has a huge drawback: once we use an object as a key in a table, we lock the object into existence. Lua cannot collect an object that is being used as a key. If we use a regular table to associate functions to its names, none of these functions will ever be collected. As you might expect, we can avoid this drawback by using a weak table. This time,
however, we need weak keys. The use of weak keys does not prevent any key from being collected, once there are no other references to it. On the other hand, the table cannot have weak values; otherwise, attributes of live objects could be collected.
How to implement tables with non-nil default values.
In the first solution, we use a weak table to associate to each table its default value:
local defaults = {}
setmetatable(defaults, {__mode = "k"})
local mt = {__index = function (t) return defaults[t] end}
function setDefault (t, d)defaults[t] = dsetmetatable(t, mt)
end
In the second solution, we use distinct metatables for distinct default values, but we reuse the same metatable whenever we repeat a default value. This is a typical use of memoizing:
local metas = {}
setmetatable(metas, {__mode = "v"})
function setDefault (t, d)local mt = metas[d]if mt == nil thenmt = {__index = function () return d end}metas[d] = mt -- memoizeendsetmetatable(t, mt)
end
We use weak values, in this case, to allow the collection of metatables that are not being used anymore.
If your application has thousands of tables with a few distinct default values, the second implementation is clearly superior. On the other hand, if few tables share common defaults, then you should favor the first implementation.
相关文章:
)
跟着 Lua 5.1 官方参考文档学习 Lua (5)
文章目录 2.10 – Garbage Collection2.10.1 – Garbage-Collection Metamethods2.10.2 – Weak Tables 2.10 – Garbage Collection Lua performs automatic memory management. This means that you have to worry neither about allocating memory for new objects nor abo…...
第2遍)
9.PG数据库层权限管理(pg系列课程)第2遍
一、PostgreSQL数据库属主 Postgres中的数据库属主属于创建者,只要有createdb的权限就可以创建数据库,数据库属主不一定拥有存放在该数据库中其它用户创建的对象的访问权限。数据库在创建后,允许public角色连接,即允许任何人连接…...

鸿蒙-canvas-画时钟
文章目录 前言准备分析组成部分数值计算过程 开始第一步 画圆环第二步 画格子第三步 画数字第四、五步 画指针&定时更新最后一步 前言 你在 Android 上能画出来的东西,在鸿蒙上画不出来? 画个时钟嘛,有啥难的? 你行你上&…...

【AI实践】阿里百炼文本对话Agent安卓版搭建
环境:安卓手机运行环境;WinsurfAI编程工具;阿里百炼提前创建Agent应用; 耗时:2小时; 1,新建安卓项目 完成文本输入,并将输入的文字显示出来。 2,安装SDK 参考文档 安…...

算法很美笔记(Java)——动态规划
解重叠子问题(当前解用到了以前求过的解) 形式:记忆型递归或递推(dp) 动态规划本质是递推,核心是找到状态转移的方式,也就是填excel表时的逻辑(填的方式),而…...

Jest单元测试
由于格式和图片解析问题,可前往 阅读原文 前端自动化测试在提高代码质量、减少错误、提高团队协作和加速交付流程方面发挥着重要作用。它是现代软件开发中不可或缺的一部分,可以帮助开发团队构建可靠、高质量的应用程序 单元测试(Unit Testi…...

《Stable Diffusion绘画完全指南:从入门到精通的Prompt设计艺术》-配套代码示例
第一章:模型加载与基础生成 1.1 基础模型加载 from diffusers import StableDiffusionPipeline import torch# 加载SD 1.5基础模型(FP32精度) pipe StableDiffusionPipeline.from_pretrained("runwayml/stable-diffusion-v1-5",…...

OnlyOffice:前端编辑器与后端API实现高效办公
OnlyOffice:前端编辑器与后端API实现高效办公 一、OnlyOffice概述二、前端编辑器:高效、灵活且易用1. 完善的编辑功能2. 实时协作支持3. 自动保存与版本管理4. 高度自定义的界面 三、后端API:管理文档、用户与权限1. 轻松集成与定制2. 实时协…...

springboot多实例部署时,@Scheduled注释的方法重复执行
问题:springboot多实例部署时,Scheduled注释的方法重复执行 在 Spring Boot 中要实现 Redis 的SET NX EX命令,可以借助 Spring Data Redis 来完成。SET NX EX命令用于在键不存在时设置键值对,并同时设置过期时间。 <dependen…...

coco格式
COCO(Common Objects in Context)格式是一种广泛用于图像识别和分割任务的数据格式,尤其是在目标检测、语义分割等任务中。COCO格式的核心包括以下几个部分: images: 包含图像的基本信息(如文件名、大小、ID等&#x…...

骶骨神经
骶骨肿瘤手术后遗症是什么_39健康网_癌症 [健康之路]匠心仁术(七) 勇闯禁区 骶骨肿瘤切除术...

Nacos学习(二)——继承Feign与Config中心
目录 一、集成Feign (一)基础用法 1.添加openfeign依赖 2. 开启openFeign注解扫描 3.创建ProviderService接口 4.修改ConsumerController (二)OpenFeign日志配置 (三)参数传递 1.参数传递的问题 2.参数传递的方式 2.1URL路径传参 2.2URL上拼接参数 2.3body传参 …...
计算机网络安全之一:网络安全概述
1.1 网络安全的内涵 随着计算机和网络技术的迅猛发展和广泛普及,越来越多的企业将经营的各种业务建立在Internet/Intranet环境中。于是,支持E-mail、文件共享、即时消息传送的消息和协作服务器成为当今商业社会中的极重要的IT基础设施。然而࿰…...

未来SLAM的研究方向和热点
SLAM(Simultaneous Localization and Mapping)是同时定位与地图构建的缩写,指的是机器人或设备在一个未知环境中一边进行自我定位,一边构建出环境的地图。SLAM广泛应用于机器人、自动驾驶、无人机等领域,涉及多个研究方…...

DuodooBMS源码解读之 purchase_change 模块
采购变更模块用户使用手册 一、模块概述 本扩展模块主要用于处理采购变更相关业务,包括采购变更单的创建、展示以及将采购变更信息导出为 Excel 文件等功能。以下将详细介绍该模块的具体使用方法。 二、模块功能及使用方法 (一)采购变更单…...
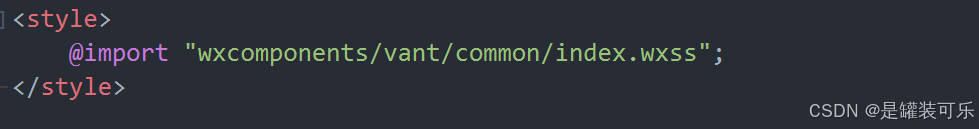
uniapp中引入Vant Weapp的保姆级教学(包含错误处理)
废话不多说,直接上方法,网上的教学好多都是错误的 1.安装vant weapp 在Hbuilder的终端,输入以下代码 npm install vant/weapp -S --production 2.新建wxcomponents文件夹 在项目的跟目录新建一个“wxcomponents’文件夹,与app.…...
)
Effective C++ 读书笔记(十二)
条款三十四:区分接口继承和实现继承 public继承由两部分组成:函数接口继承和函数实现继承。这两者的差异很像函数声明和函数定义之间的差异。 作为类的设计者,我们有时希望派生类只继承成员函数的接口(也就是函数声明࿰…...

【卡梅德生物】构建噬菌体文库与噬菌体展示文库构建服务新探索
在生命科学与生物技术快速发展的当下,抗体文库构建、构建噬菌体文库以及噬菌体展示文库构建服务在生物医药研发领域中占据着举足轻重的地位。它们不仅是基础研究的重要工具,更是推动抗体药物开发、疾病诊断技术进步的关键力量。 构建噬菌体文库是整个技…...
 》笔记-Chapter19-表单脚本)
【JavaScript】《JavaScript高级程序设计 (第4版) 》笔记-Chapter19-表单脚本
十九、表单脚本 表单脚本 JavaScript 较早的一个用途是承担一部分服务器端表单处理的责任。虽然 Web 和 JavaScript 都已经发展了很多年,但 Web 表单的变化不是很大。由于不能直接使用表单解决问题,因此开发者不得不使用JavaScript 既做表单验证…...

C++STL容器之map
1.介绍 map是 C 标准模板库(STL)中的一个关联容器,用于存储键值对(key-value pairs)。map中的元素是按照键(key)进行排序的,并且每个键在容器中是唯一的。map通常基于红黑树…...

基于Nanopi duo2的WiFi智能摄像头
1.固件包烧录 https://wiki.friendlyelec.com/wiki/index.php/NanoPi_Duo2/zh#.E8.BF.9E.E6.8E.A5WiFi 固件包链接以及烧录工具都在上面链接中 烧录过程 使用读卡器将SD卡插入到电脑,然后打开烧录工具 2.通过串口工具连接板子使其连接WiFi 对应的串口工具,就是这个HyperT…...

Java 内存区域详解
1 常见面试题 1.1 基本问题 介绍下Java内存区域(运行时数据区)Java对象的创建过程(五步,建议能够默写出来并且要知道每一步虚拟机做了什么)对象的访问定位的两种方式(句柄和直接指针两种方式)…...

MyBatis框架详解与核心配置解读
目录 前言 一、MyBatis框架概述 1.1 什么是MyBatis 1.2 MyBatis的优点 二、MyBatis的使用入门与案例 2.1 MyBatis核心配置文件(mybatis-config.xml) 2.2 XML映射文件(UserMapper.xml) 三、MyBatis的常用注解及其用法 3.1…...

Windows 快速搭建C++开发环境,安装C++、CMake、QT、Visual Studio、Setup Factory
安装C 简介 Windows 版的 GCC 有三个选择: CygwinMinGWmingw-w64 Cygwin、MinGW 和 mingw-w64 都是在 Windows 操作系统上运行的工具集,用于在 Windows 环境下进行开发和编译。 Cygwin 是一个在 Windows 上运行的开源项目,旨在提供类Uni…...

GO系列-IO 文件操作
os io 判断文件是否存在 func fileExist(filePath string) (bool, error) {_, err : os.Stat(filePath)if err nil {return true, nil}if os.IsNotExist(err) {return false, nil}return false, &CheckFileExistError{filePath} } 读取文件内容 func readFileContext(…...

Unity Excel导表工具转Lua文件
思路介绍 借助EPPlus读取Excel文件中的配置数据,根据指定的不同类型的数据配置规则来解析成对应的代码文本,将解析出的字符串内容写入到XXX.lua.txt文件中即可 EPPlus常用API //命名空间 using OfficeOpenXml;//Excel文件路径 var fileExcel new File…...
Helix——Figure 02发布通用人形机器人控制的VLA:一组神经网络权重下的快与慢双系统,让两个机器人协作干活
前言 过去一周,我花了很大的心思、力气,把deepseek的GRPO、MLA算法的代码解析通透,比如GRPO与PPO的详细对比,再比如MLA中,图片 公式 代码的一一对应 2.20日晚,无意中刷到figure 02发布Helix的一个演示视频…...

汽车自动驾驶辅助L2++是什么?
自动驾驶辅助级别有哪些? 依照SAE(SAE International,Society of Automotive Engineers国际自动机工程师学会)的标准,大致划分为6级(L0-L5): L0人工驾驶:即没有驾驶辅助…...

进程的介绍--进程状态/切换
1.冯 • 诺依曼体系结构 1.1 体系结构 冯•诺依曼结构也称普林斯顿结构,是一种将程序指令存储器和数据存储器合并在一起的存储器结构。数学家冯•诺依曼提出了计算机制造的三个基本原则,即采用二进制逻辑、程序存储执行以及计算机由五个部分组成&#x…...

goby(蓝队红队版)扫描工具扫描使用时候报错解决方法
1.Goby 是一款开源的网络安全扫描工具,主要用于漏洞扫描、资产发现和信息收集。它旨在帮助安全研究人员、渗透测试人员和红队成员自动化和简化网络漏洞扫描过程。Goby 提供了多种功能,能够在大量的目标中高效地识别出潜在的安全漏洞。 2.今天在官网下载…...
