Deploy、Service与Ingress
Deployment
自愈
介绍:控制Pod,使Pod拥有多副本,自愈,扩缩容等能力
# 清除所有Pod,比较下面两个命令有何不同效果?
kubectl run mynginx --image=nginxkubectl create deployment mytomcat --image=tomcat:8.5.68
# 自愈能力
删除pod测试

# 查看部署
kubectl get deploy
# 删除部署
kubectl delete deploy mytomcat
- 删除部署后容器不会再重启
多副本

kubectl create deployment my-dep --image=nginx --replicas=3
- replicas:指定副本数量
使用配置文件方式
apiVersion: apps/v1
kind: Deployment # 资源类型
metadata:labels:app: my-depname: my-dep
spec:replicas: 3 #副本数量selector:matchLabels:app: my-deptemplate:metadata:labels:app: my-depspec:containers:- image: nginxname: nginx
扩缩容

kubectl scale --replicas=5 deploy/my-dep
修改配置文件方式
kubectl edit deployment my-dep
自愈与故障转移

- 停机
- 删除Pod
- 容器崩溃
k8s总会保障运行中的容器与预期一致
滚动更新

kubectl set image deployment/my-dep nginx=nginx:1.16.1 --record
k8s更新pod版本会先针对一个pod创建一个新版本的pod出来,等待启动成功后将老的pod进行下线k8s更新pod会一个一个更新,而不是一次性全部更新,如果更新失败,会停止后续更新
版本回退
#历史记录
kubectl rollout history deployment/my-dep#查看某个历史详情
kubectl rollout history deployment/my-dep --revision=2#回滚(回到上次)
kubectl rollout undo deployment/my-dep#回滚(回到指定版本)
kubectl rollout undo deployment/my-dep --to-revision=2
更多:
除了Deployment,k8s还有
StatefulSet、DaemonSet、Job等 类型资源。我们都称为工作负载。有状态应用使用
StatefulSet部署,无状态应用使用Deployment部署
https://kubernetes.io/zh/docs/concepts/workloads/controllers/

Service
将一组 Pods公开为网络服务的抽象方法。

#暴露Deploy
kubectl expose deployment my-dep --port=8000 --target-port=80#使用标签检索Pod
kubectl get pod -l app=my-dep#查看pod的标签
kubectl get pod --show-labels#查看service
kubectl get service
- 服务暴露后可以通过公共
IP或者域名两种方式进行访问- 域名:
服务名.所在名称空间.svc只能在集群中的pod进行访问
- 域名:
通过yaml方式配置
apiVersion: v1
kind: Service #资源类型:服务
metadata:labels:app: my-depname: my-dep #服务名称
spec:selector:app: my-dep #暴露的pod组名 key:app value:my-dep ports:- port: 8000 #pod内端口protocol: TCPtargetPort: 80 #公共访问端口

- 默认暴露方式为
ClusterIP,只能在集群内部访问,如果需要在集群外部访问需要改为NodePort类型,它为为随机每个pod暴露一个相同的端口,供外部访问
# 查看端口
kubectl get service
NodePort范围在 30000-32767 之间
Ingress

安装
wget https://raw.githubusercontent.com/kubernetes/ingress-nginx/controller-v0.47.0/deploy/static/provider/baremetal/deploy.yaml#修改镜像
vi deploy.yaml
#将image的值改为如下值:
registry.cn-hangzhou.aliyuncs.com/lfy_k8s_images/ingress-nginx-controller:v0.46.0# 检查安装的结果
kubectl get pod,svc -n ingress-nginx# 最后别忘记把svc暴露的端口要放行
yaml部署
apiVersion: v1
kind: Namespace
metadata:name: ingress-nginxlabels:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginx---
# Source: ingress-nginx/templates/controller-serviceaccount.yaml
apiVersion: v1
kind: ServiceAccount
metadata:labels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginxnamespace: ingress-nginx
automountServiceAccountToken: true
---
# Source: ingress-nginx/templates/controller-configmap.yaml
apiVersion: v1
kind: ConfigMap
metadata:labels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginx-controllernamespace: ingress-nginx
data:
---
# Source: ingress-nginx/templates/clusterrole.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:labels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmname: ingress-nginx
rules:- apiGroups:- ''resources:- configmaps- endpoints- nodes- pods- secretsverbs:- list- watch- apiGroups:- ''resources:- nodesverbs:- get- apiGroups:- ''resources:- servicesverbs:- get- list- watch- apiGroups:- extensions- networking.k8s.io # k8s 1.14+resources:- ingressesverbs:- get- list- watch- apiGroups:- ''resources:- eventsverbs:- create- patch- apiGroups:- extensions- networking.k8s.io # k8s 1.14+resources:- ingresses/statusverbs:- update- apiGroups:- networking.k8s.io # k8s 1.14+resources:- ingressclassesverbs:- get- list- watch
---
# Source: ingress-nginx/templates/clusterrolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:labels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmname: ingress-nginx
roleRef:apiGroup: rbac.authorization.k8s.iokind: ClusterRolename: ingress-nginx
subjects:- kind: ServiceAccountname: ingress-nginxnamespace: ingress-nginx
---
# Source: ingress-nginx/templates/controller-role.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:labels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginxnamespace: ingress-nginx
rules:- apiGroups:- ''resources:- namespacesverbs:- get- apiGroups:- ''resources:- configmaps- pods- secrets- endpointsverbs:- get- list- watch- apiGroups:- ''resources:- servicesverbs:- get- list- watch- apiGroups:- extensions- networking.k8s.io # k8s 1.14+resources:- ingressesverbs:- get- list- watch- apiGroups:- extensions- networking.k8s.io # k8s 1.14+resources:- ingresses/statusverbs:- update- apiGroups:- networking.k8s.io # k8s 1.14+resources:- ingressclassesverbs:- get- list- watch- apiGroups:- ''resources:- configmapsresourceNames:- ingress-controller-leader-nginxverbs:- get- update- apiGroups:- ''resources:- configmapsverbs:- create- apiGroups:- ''resources:- eventsverbs:- create- patch
---
# Source: ingress-nginx/templates/controller-rolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:labels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginxnamespace: ingress-nginx
roleRef:apiGroup: rbac.authorization.k8s.iokind: Rolename: ingress-nginx
subjects:- kind: ServiceAccountname: ingress-nginxnamespace: ingress-nginx
---
# Source: ingress-nginx/templates/controller-service-webhook.yaml
apiVersion: v1
kind: Service
metadata:labels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginx-controller-admissionnamespace: ingress-nginx
spec:type: ClusterIPports:- name: https-webhookport: 443targetPort: webhookselector:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/component: controller
---
# Source: ingress-nginx/templates/controller-service.yaml
apiVersion: v1
kind: Service
metadata:annotations:labels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginx-controllernamespace: ingress-nginx
spec:type: NodePortports:- name: httpport: 80protocol: TCPtargetPort: http- name: httpsport: 443protocol: TCPtargetPort: httpsselector:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/component: controller
---
# Source: ingress-nginx/templates/controller-deployment.yaml
apiVersion: apps/v1
kind: Deployment
metadata:labels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginx-controllernamespace: ingress-nginx
spec:selector:matchLabels:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/component: controllerrevisionHistoryLimit: 10minReadySeconds: 0template:metadata:labels:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/component: controllerspec:dnsPolicy: ClusterFirstcontainers:- name: controllerimage: registry.cn-hangzhou.aliyuncs.com/lfy_k8s_images/ingress-nginx-controller:v0.46.0imagePullPolicy: IfNotPresentlifecycle:preStop:exec:command:- /wait-shutdownargs:- /nginx-ingress-controller- --election-id=ingress-controller-leader- --ingress-class=nginx- --configmap=$(POD_NAMESPACE)/ingress-nginx-controller- --validating-webhook=:8443- --validating-webhook-certificate=/usr/local/certificates/cert- --validating-webhook-key=/usr/local/certificates/keysecurityContext:capabilities:drop:- ALLadd:- NET_BIND_SERVICErunAsUser: 101allowPrivilegeEscalation: trueenv:- name: POD_NAMEvalueFrom:fieldRef:fieldPath: metadata.name- name: POD_NAMESPACEvalueFrom:fieldRef:fieldPath: metadata.namespace- name: LD_PRELOADvalue: /usr/local/lib/libmimalloc.solivenessProbe:failureThreshold: 5httpGet:path: /healthzport: 10254scheme: HTTPinitialDelaySeconds: 10periodSeconds: 10successThreshold: 1timeoutSeconds: 1readinessProbe:failureThreshold: 3httpGet:path: /healthzport: 10254scheme: HTTPinitialDelaySeconds: 10periodSeconds: 10successThreshold: 1timeoutSeconds: 1ports:- name: httpcontainerPort: 80protocol: TCP- name: httpscontainerPort: 443protocol: TCP- name: webhookcontainerPort: 8443protocol: TCPvolumeMounts:- name: webhook-certmountPath: /usr/local/certificates/readOnly: trueresources:requests:cpu: 100mmemory: 90MinodeSelector:kubernetes.io/os: linuxserviceAccountName: ingress-nginxterminationGracePeriodSeconds: 300volumes:- name: webhook-certsecret:secretName: ingress-nginx-admission
---
# Source: ingress-nginx/templates/admission-webhooks/validating-webhook.yaml
# before changing this value, check the required kubernetes version
# https://kubernetes.io/docs/reference/access-authn-authz/extensible-admission-controllers/#prerequisites
apiVersion: admissionregistration.k8s.io/v1
kind: ValidatingWebhookConfiguration
metadata:labels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhookname: ingress-nginx-admission
webhooks:- name: validate.nginx.ingress.kubernetes.iomatchPolicy: Equivalentrules:- apiGroups:- networking.k8s.ioapiVersions:- v1beta1operations:- CREATE- UPDATEresources:- ingressesfailurePolicy: FailsideEffects: NoneadmissionReviewVersions:- v1- v1beta1clientConfig:service:namespace: ingress-nginxname: ingress-nginx-controller-admissionpath: /networking/v1beta1/ingresses
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/serviceaccount.yaml
apiVersion: v1
kind: ServiceAccount
metadata:name: ingress-nginx-admissionannotations:helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhooknamespace: ingress-nginx
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/clusterrole.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:name: ingress-nginx-admissionannotations:helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhook
rules:- apiGroups:- admissionregistration.k8s.ioresources:- validatingwebhookconfigurationsverbs:- get- update
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/clusterrolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:name: ingress-nginx-admissionannotations:helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhook
roleRef:apiGroup: rbac.authorization.k8s.iokind: ClusterRolename: ingress-nginx-admission
subjects:- kind: ServiceAccountname: ingress-nginx-admissionnamespace: ingress-nginx
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/role.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:name: ingress-nginx-admissionannotations:helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhooknamespace: ingress-nginx
rules:- apiGroups:- ''resources:- secretsverbs:- get- create
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/rolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:name: ingress-nginx-admissionannotations:helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhooknamespace: ingress-nginx
roleRef:apiGroup: rbac.authorization.k8s.iokind: Rolename: ingress-nginx-admission
subjects:- kind: ServiceAccountname: ingress-nginx-admissionnamespace: ingress-nginx
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/job-createSecret.yaml
apiVersion: batch/v1
kind: Job
metadata:name: ingress-nginx-admission-createannotations:helm.sh/hook: pre-install,pre-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhooknamespace: ingress-nginx
spec:template:metadata:name: ingress-nginx-admission-createlabels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhookspec:containers:- name: createimage: docker.io/jettech/kube-webhook-certgen:v1.5.1imagePullPolicy: IfNotPresentargs:- create- --host=ingress-nginx-controller-admission,ingress-nginx-controller-admission.$(POD_NAMESPACE).svc- --namespace=$(POD_NAMESPACE)- --secret-name=ingress-nginx-admissionenv:- name: POD_NAMESPACEvalueFrom:fieldRef:fieldPath: metadata.namespacerestartPolicy: OnFailureserviceAccountName: ingress-nginx-admissionsecurityContext:runAsNonRoot: truerunAsUser: 2000
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/job-patchWebhook.yaml
apiVersion: batch/v1
kind: Job
metadata:name: ingress-nginx-admission-patchannotations:helm.sh/hook: post-install,post-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhooknamespace: ingress-nginx
spec:template:metadata:name: ingress-nginx-admission-patchlabels:helm.sh/chart: ingress-nginx-3.33.0app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 0.47.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhookspec:containers:- name: patchimage: docker.io/jettech/kube-webhook-certgen:v1.5.1imagePullPolicy: IfNotPresentargs:- patch- --webhook-name=ingress-nginx-admission- --namespace=$(POD_NAMESPACE)- --patch-mutating=false- --secret-name=ingress-nginx-admission- --patch-failure-policy=Failenv:- name: POD_NAMESPACEvalueFrom:fieldRef:fieldPath: metadata.namespacerestartPolicy: OnFailureserviceAccountName: ingress-nginx-admissionsecurityContext:runAsNonRoot: truerunAsUser: 2000
使用
官网地址:https://kubernetes.github.io/ingress-nginx/
底层采用的是nginx
测试环境部署
应用如下
yaml,准备好测试环境
apiVersion: apps/v1
kind: Deployment
metadata:name: hello-server
spec:replicas: 2selector:matchLabels:app: hello-servertemplate:metadata:labels:app: hello-serverspec:containers:- name: hello-serverimage: registry.cn-hangzhou.aliyuncs.com/lfy_k8s_images/hello-serverports:- containerPort: 9000
---
apiVersion: apps/v1
kind: Deployment
metadata:labels:app: nginx-demoname: nginx-demo
spec:replicas: 2selector:matchLabels:app: nginx-demotemplate:metadata:labels:app: nginx-demospec:containers:- image: nginxname: nginx
---
apiVersion: v1
kind: Service
metadata:labels:app: nginx-demoname: nginx-demo
spec:selector:app: nginx-demoports:- port: 8000protocol: TCPtargetPort: 80
---
apiVersion: v1
kind: Service
metadata:labels:app: hello-servername: hello-server
spec:selector:app: hello-serverports:- port: 8000protocol: TCPtargetPort: 9000
域名访问
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: ingress-host-bar
spec:ingressClassName: nginxrules:- host: "hello.vmware.com"http:paths:- pathType: Prefixpath: "/"backend:service:name: hello-serverport:number: 8000- host: "demo.atguigu.com"http:paths:- pathType: Prefixpath: "/nginx" # 把请求会转给下面的服务,下面的服务一定要能处理这个路径,不能处理就是404backend:service:name: nginx-demo ## java,比如使用路径重写,去掉前缀nginxport:number: 8000
路径重写
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:annotations:nginx.ingress.kubernetes.io/rewrite-target: /$2name: ingress-host-bar
spec:ingressClassName: nginxrules:- host: "hello.vmware.com"http:paths:- pathType: Prefixpath: "/"backend:service:name: hello-serverport:number: 8000- host: "demo.vmware.com"http:paths:- pathType: Prefixpath: "/nginx(/|$)(.*)" # 把请求会转给下面的服务,下面的服务一定要能处理这个路径,不能处理就是404backend:service:name: nginx-demo ## java,比如使用路径重写,去掉前缀nginxport:number: 8000
流量限制
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: ingress-limit-rateannotations:nginx.ingress.kubernetes.io/limit-rps: "1"
spec:ingressClassName: nginxrules:- host: "haha.vmware.com"http:paths:- pathType: Exactpath: "/"backend:service:name: nginx-demoport:number: 8000
相关文章:

Deploy、Service与Ingress
Deployment 自愈 介绍:控制Pod,使Pod拥有多副本,自愈,扩缩容等能力 # 清除所有Pod,比较下面两个命令有何不同效果? kubectl run mynginx --imagenginxkubectl create deployment mytomcat --imagetomcat:8.5.68 # 自…...

定制化推送+精细化运营,Mobpush助力《迷你世界》用户留存率提升23%
随着智能设备的市场下沉,手游市场迎来了爆发式增长,《迷你世界》作为一款于2015年推出的手游,一经问世就饱受欢迎。上线短短三年,迷你世界在应用商店下载量已经高达2亿次,周下载量两千万,稳居第一名&#x…...
深度学习零基础教程
代码运行软件安装: anaconda:一个管理环境的软件–>https://blog.csdn.net/scorn_/article/details/106591160(可选装) pycharm:一个深度学习运行环境–>https://blog.csdn.net/scorn_/article/details/106591160…...
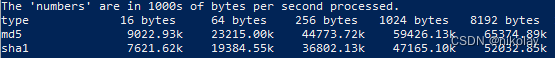
简单测试一下 展锐的 UDX710 性能
最近在接触 联通5G CPE VN007 ,发现使用的是 展锐的Unisoc UDX710 CPU,正好简单的测试一下这颗CPU CPU信息 UDX710 是一颗 双核 ARM Cortex-A55 处理器,主频高达 1.35GHz processor : 0 BogoMIPS : 52.00 Features : fp…...
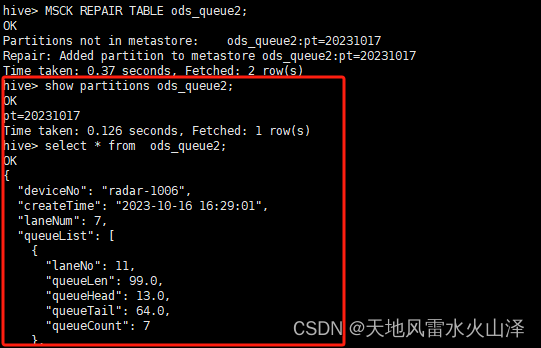
一百九十、Hive——Hive刷新分区MSCK REPAIR TABLE
一、目的 在用Flume采集Kafka中的数据直接写入Hive的ODS层静态分区表后,需要刷新表,才能导入分区和数据。原因很简单,就是Hive表缺乏分区的元数据 二、实施步骤 (一)问题——在Flume采集Kafka中的数据写入HDFS后&am…...

智慧公厕:探索未来城市环境卫生设施建设新标杆
智慧公厕是当代城市建设的一项重要举措,它集先进技术、人性化设计和智能管理于一体,为人们提供更为舒适、便捷和卫生的厕所环境。现代智慧公厕的功能异常丰富,从厕位监测到多媒体信息交互,从自动化清洁到环境调控,每一…...
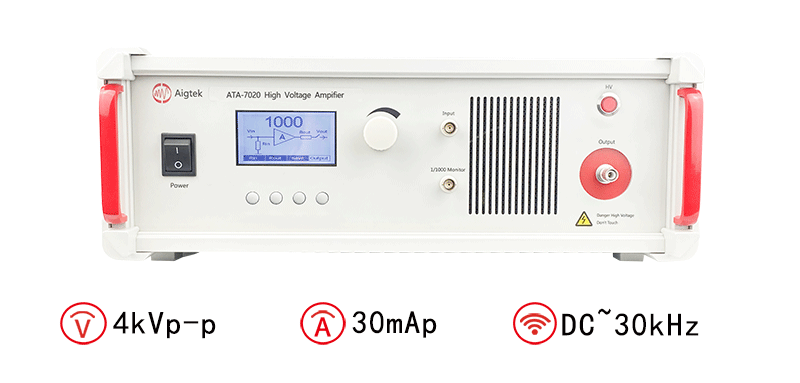
高压放大器在无线电能中应用有哪些
高压放大器是一种用于放大电信号的放大器,可以将输入的低电压信号放大到更高的输出电压水平。在无线电通信和其他相关领域中,高压放大器具有广泛的应用。本文将详细介绍高压放大器在无线电能中的应用。 无线电发射:高压放大器在无线电发射中起…...

若依集成MybatisPlus
目录 一、依赖变更 1. MybatisPlus依赖 2. pagehelper依赖修改 二、相关配置 1. yml配置 1.1 注释掉原Mybatis配置 1.2 加入MybatisPlus的配置 1.3 注释掉原MybatisConfig.class 三、其他配置及功能实现 1. 自动补全create_time等信息 2. 实现MP分页 3. 实现Mybati…...
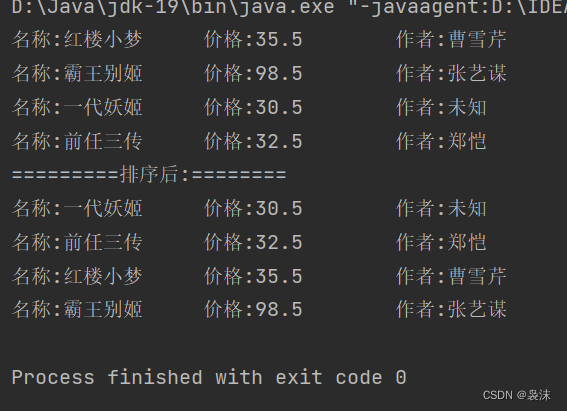
List小练习,实现添加图书,并且有序遍历
SuppressWarnings({"all"})public static void main(String[] args) {List list new LinkedList(); // List list new Vector(); // List list new ArrayList();list.add(new Book1("红楼小梦",35.5,"曹雪芹"));list.add(new B…...
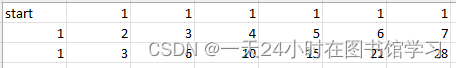
代码随想录二刷 Day42
62.不同路径 简单题目自己就可以写出来,注意下创建二维vector的方法就可以, dp table如下 class Solution { public:int uniquePaths(int m, int n) {vector<vector<int>> dp(m,vector<int>(n,0));for (int i 0; i < n; i ) {dp[…...

【Android】Drawable 和src 的区别和理解
详细讲解 在 Android 中,ImageView 的 src 属性和 background 属性用于设置不同类型的图像内容。下面是它们的详细解释: src 属性:该属性用于设置 ImageView 中显示的图像内容。它可以接受一个图像资源的引用,可以是一个图片文件…...

Linux网络-UDP/TCP协议详解
Linux网络-UDP/TCP协议详解 2023/10/17 14:32:49 Linux网络-UDP/TCP协议详解 零、前言一、UDP协议二、TCP协议 1、应答机制2、序号机制3、超时重传机制4、连接管理机制 三次握手四次挥手5、理解CLOSE_WAIT状态6、理解TIME_WAIT状态7、流量控制8、滑动窗口 丢包问题9、拥塞控制…...
C语言从入门到高级
C语言是“编程语言之首”(很多人学习的第一门编程语言),学好一门编程语言需要明确其学习路径,下面分享下我的学习路径,希望对您有所帮助。 一、C语言入门 (1)C语言概述 (2&#x…...
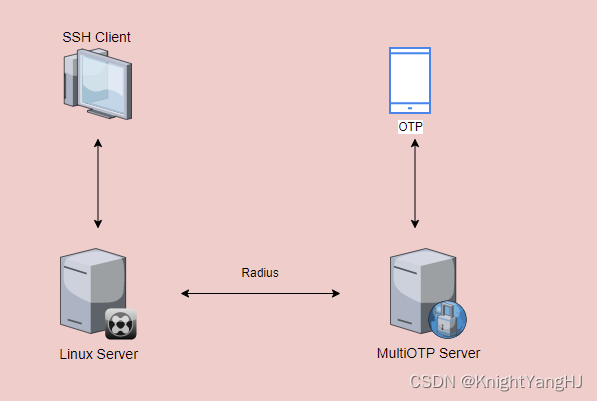
【MultiOTP】在Linux上使用MultiOTP进行SSH登录
在前面的文章中【FreeRADIUS】使用FreeRADIUS进行SSH身份验证已经了解过如何通过Radius去来实现SSH和SUDO的登录,在接下来的文章中只是将密码从【LDAP PASSWORD Googlt OTP】改成了【MultiOTP】生成的passcode,不在需要密码,只需要OTP去登录…...
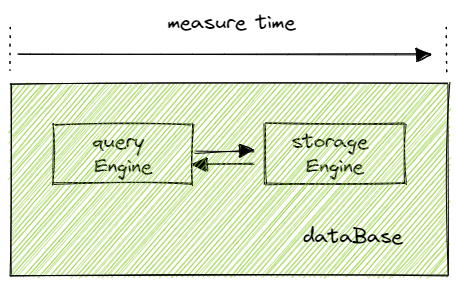
性能超越 Clickhouse | 物联网场景中的毫秒级查询案例
1 物联网应用场景简介 物联网(Internet of Things,简称 IoT)是指通过各种信息传感、通信和 IT 技术来实时连接、采集、监管海量的传感设备,从而实现对现实世界的精确感知和快速响应,继而实现自动化、智能化管理。在查…...
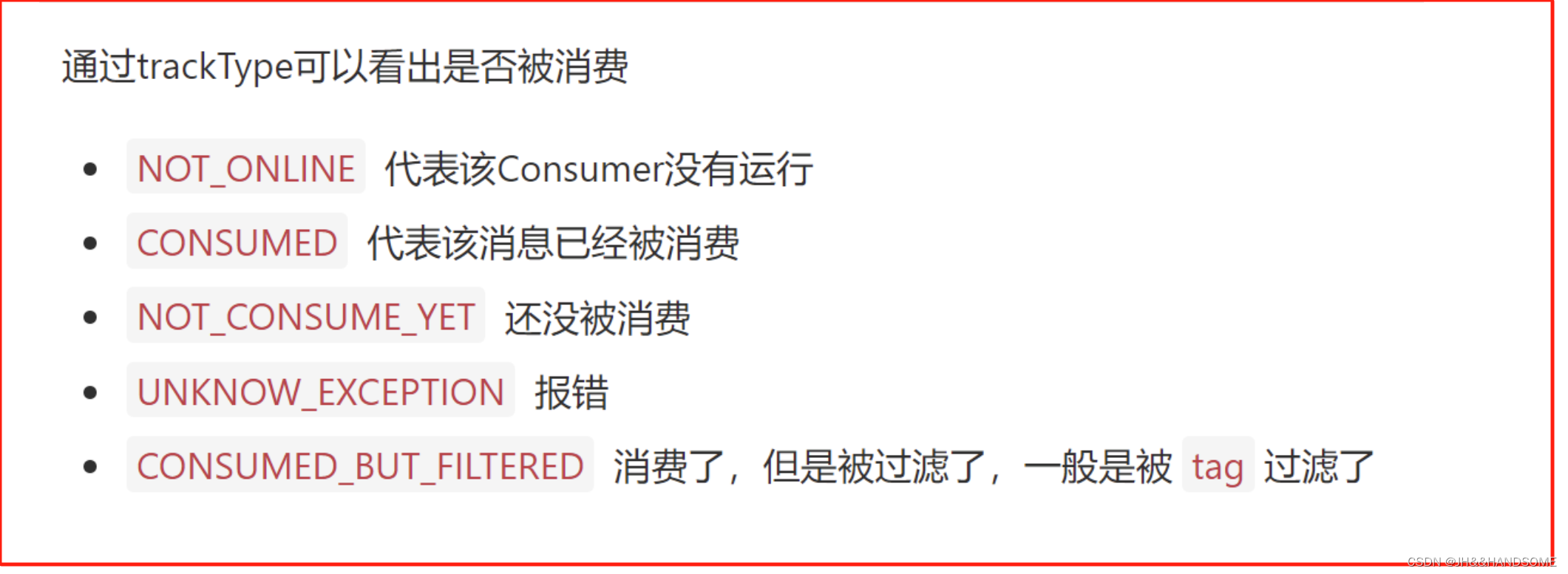
05、SpringBoot 集成 RocketMQ
目录 SpringBoot集成RocketMQ消息发送三种方式1、同步消息producer-springboot创建项目添加依赖配置文件同步消息发送代码启动类Test类 comsumer-springboot创建项目添加依赖配置文件同步消息消费代码 2、异步消息生产者消费者 3、一次性消息生产者消费者 消息消费两种方式1、集…...
PR2023中如何导入字幕
PR中如何导入字幕 方法一: 点开文本,字幕,新建字幕分段(点击右上角…三个点) 键入调整内容 方法二 点开基本图形,编辑,调整,拖动位置。...

读书笔记--华为数据之道有感
通过研读华为数据之道,了解到华为作为一家非数字原生企业,其业务涵盖研发、营销、制造、供应、采购、服务等,业务相当复杂。因此华为在开展数据治理过程中明确了由谁来对数据负责,特别是对数据质量负责,明确了数据质量的衡量或度量指标,并成立了数据管理部,确定其职能定…...

汽车数据安全事件频发,用户如何保护隐私信息?
面对日益增多的汽车数据安全事件,对于广大用户来说,有没有既廉价又安全的解决方案? 频发的汽车数据安全事件 随着汽车“新四化”大潮的来临,汽车用户从电动化、网联化、智能化、共享化中切实体验到了越来越多的便利,各…...

Redis主从复制流程
前言 Redis 支持部署多节点,然后按照 1:n 的方式构建主从集群,即一个主库、n 个从库。主从库之间会自动进行数据同步,但是只有主库同时允许读写,从库只允许读。 搭建主从复制集群的目的: 从库可用于容灾备份从库可以…...

亚马逊AMC数据驱动时代,选对ERP才能玩转精准投放
随着亚马逊广告生态的持续升级,AMC(Amazon Marketing Cloud)作为高阶数据分析工具,正成为头部卖家精细化运营的“标配”。AMC能够整合品牌在亚马逊站内外多渠道的广告与消费者行为数据,但其核心价值在于数据的打通与应…...

剪映高级感文字动画素材合集 预设+教程全整理
平时做口播视频时,总觉得文字动画的精致度跟不上内容节奏,找适配的素材又要花不少时间,所以最近整理了一份剪映高级感口播动态文字动画素材合集,涵盖预设、教程和配套排查资料,今天分享给有同样需求的朋友。 一、素材合…...

SenseVoice WebUI镜像体验:上传音频秒获文字+表情标签,小白也能玩转
SenseVoice WebUI镜像体验:上传音频秒获文字表情标签,小白也能玩转 1. 快速了解SenseVoice WebUI SenseVoice WebUI是一个开箱即用的语音识别工具,它能将你上传的音频文件快速转换成文字,并自动标注说话人的情感状态和音频中的特…...

Claude Code源码阅读分享
Claude Code 源码阅读分享 链接: https://pan.baidu.com/s/1oSUWD11Yjrn5_pVVfK8Y9g?pwdv4ta Quick Start Option 1: Use with Claude Code (Recommended) # Copy agents to your Claude Code directory cp -r agency-agents/* ~/.claude/agents/# Now activate any agent in …...

CES Asia 2026打造低空经济生态圈:从整机到核心部件全链覆盖
北京,2026年3月31日电——低空经济产业正迈向全链协同、规模化落地的关键阶段。CES Asia 2026将于6月10—12日在北京举办,以全产业链覆盖精准供需对接资本赋能为核心,构建从整机到核心部件的完整低空经济生态圈,助力企业一站式打通…...

QMCDecode:3分钟快速解锁QQ音乐加密文件,实现跨平台音乐自由
QMCDecode:3分钟快速解锁QQ音乐加密文件,实现跨平台音乐自由 【免费下载链接】QMCDecode QQ音乐QMC格式转换为普通格式(qmcflac转flac,qmc0,qmc3转mp3, mflac,mflac0等转flac),仅支持macOS,可自动识别到QQ音乐下载目录…...

快速上手ms-swift:图形界面操作大模型全流程,保姆级指导
快速上手ms-swift:图形界面操作大模型全流程,保姆级指导 1. 为什么选择ms-swift? 在人工智能领域,大模型的训练和部署一直是个技术门槛较高的工作。传统方式需要处理复杂的命令行参数、环境配置和代码调试,这让很多非…...
Pixel Couplet Gen完整指南:从GitHub Fork到微信小程序上线的像素春联项目闭环
Pixel Couplet Gen完整指南:从GitHub Fork到微信小程序上线的像素春联项目闭环 1. 项目介绍与核心价值 Pixel Couplet Gen是一款融合AI技术与复古游戏美学的创新应用,它将传统春联创作带入了数字时代。这个项目最吸引人的特点是: 8-bit像素…...

开发者的软实力:沟通、协作与影响力的修炼手册
在软件开发的精密世界里,代码是骨骼,架构是经脉,而沟通、协作与影响力,则是驱动整个系统顺畅运行的血液与神经。对于软件测试从业者而言,这种认知尤为深刻。我们早已超越了“找Bug”的单一角色,成为质量文化…...

JDK 17 + Spring Boot 3.5.8:企业级开发技术栈全景分析
JDK 17与Spring Boot 3.5.8的核心特性JDK 17 LTS特性 JDK 17作为长期支持版本(LTS),提供多项生产级增强:密封类(Sealed Classes):通过sealed和permits关键字限制类的继承关系,增强领…...
