血的教训--kail系统免密centos7的坑【高版本ssh免密低版本ssh的坑】
血的教训–kail系统免密centos7的坑【高版本ssh免密低版本ssh的坑】
最近下载了一个2023版本的kail系统,但是经过几次设置免密后,ssh过去一直让提供密码,所以就仔细的分析了一下,果然还是发现了点猫腻
接上一个博客,大家可以看看,ssh免密之间的坑
入侵redis之准备—linux之间的免密通信原来是这么的简单
ssh免密其实很简单,但是没想到还是有一些坑
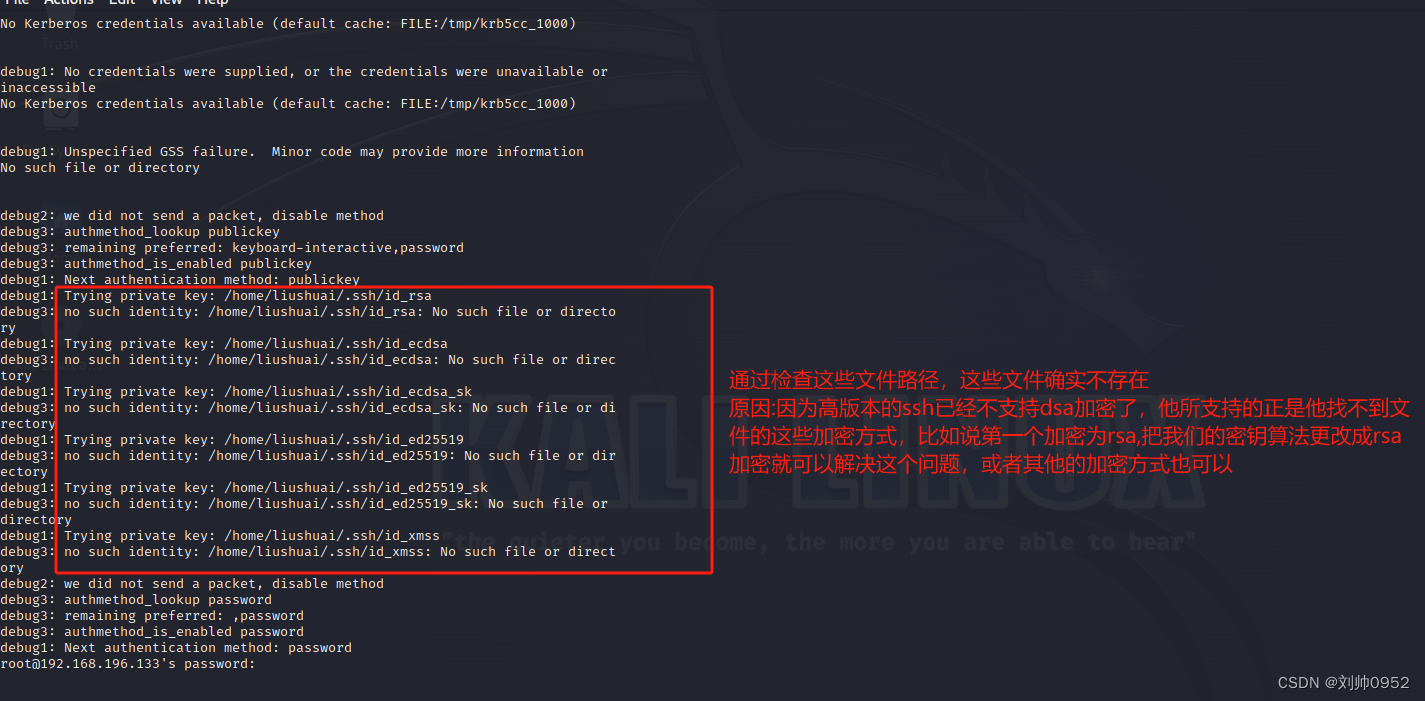
出现免密失败的情况,我也是百度了好多,都是让更改目录的权限,但是都失败了,其实这跟权限有关系,但是我们基本上也不会动这些目录的权限,如果你的权限没有问题,那就可以往我这个方向考虑了,那就是高版本的ssh加密方式和低版本ssh啊hi见的加密方式不一样,大家知道最近ssh低于9版本有漏洞,所以ssh版本都升级到9以上了,但是部分还是9一下版本,这个就是免密失败的原因。
关键报错:
debug2: we did not send a packet, disable method
debug3: authmethod_lookup publickey
debug3: remaining preferred: keyboard-interactive,password
debug3: authmethod_is_enabled publickey
debug1: Next authentication method: publickey
debug1: Trying private key: /home/liushuai/.ssh/id_rsa
debug3: no such identity: /home/liushuai/.ssh/id_rsa: No such file or directory
debug1: Trying private key: /home/liushuai/.ssh/id_ecdsa
debug3: no such identity: /home/liushuai/.ssh/id_ecdsa: No such file or directory
debug1: Trying private key: /home/liushuai/.ssh/id_ecdsa_sk
debug3: no such identity: /home/liushuai/.ssh/id_ecdsa_sk: No such file or directory
debug1: Trying private key: /home/liushuai/.ssh/id_ed25519
debug3: no such identity: /home/liushuai/.ssh/id_ed25519: No such file or directory
debug1: Trying private key: /home/liushuai/.ssh/id_ed25519_sk
debug3: no such identity: /home/liushuai/.ssh/id_ed25519_sk: No such file or directory
debug1: Trying private key: /home/liushuai/.ssh/id_xmss
debug3: no such identity: /home/liushuai/.ssh/id_xmss: No such file or directory
debug2: we did not send a packet, disable method
debug3: authmethod_lookup password
debug3: remaining preferred: ,password
debug3: authmethod_is_enabled password
debug1: Next authentication method: password
其他文章:
入侵redis并实现反弹shell控制【实战一】
- 学习大概步骤如下
- 第一步:先学习怎么安装部署kail系统服务器
入侵redis之准备—VMware安装部署kail镜像服务器【详细包含云盘镜像】 - 第二步:再学习怎么安装部署centos系统服务器
入侵redis之准备—VMware上面安装部署centos7镜像系统【详细含云盘镜像】 - 再学习下linux下面的定时任务crontab相关知识打下基础
入侵redis之准备—Linux关于定时任务crontab相关知识了解配合理解shell反弹远程控制 - 再学习下centos7上面部署redis,毕竟咱们还是要入侵他的哈
入侵redis之准备—Centos7上面部署redis - 再学习下如何使用python来破解下redis的密码
血的教训------入侵redis之利用python来破解redis密码 - 最后就是我们精彩的入侵redis并远程控制你的机器复现
血的教训—入侵redis并远程控制你的机器场景复现
入侵redis并实现免密登录服务器【实战二】
- 学习大概步骤如下
- 第一步:先学习怎么安装部署kail系统服务器
入侵redis之准备—VMware安装部署kail镜像服务器【详细包含云盘镜像】 - 第二步:再学习怎么安装部署centos系统服务器
入侵redis之准备—VMware上面安装部署centos7镜像系统【详细含云盘镜像】 - 再学习下linux之间的免密通信原来是这么的简单
入侵redis之准备—linux之间的免密通信原来是这么的简单 - 再学习下ssh免密登录的一些坑,ssh高版本免密低版本的坑
血的教训–kail系统免密centos7的坑【高版本ssh免密低版本ssh的坑】 - 再学习下centos7上面部署redis,毕竟咱们还是要入侵他的哈
入侵redis之准备—Centos7上面部署redis - 再学习下如何使用python来破解下redis的密码
血的教训------入侵redis之利用python来破解redis密码 - 最后就是我们精彩的入侵redis并免密登录redis所在服务器
血的教训—入侵redis并免密登录redis所在服务器
废话不多说,直接开干
| 系统 | ip | 介绍 |
|---|---|---|
| kail系统 | 192.168.126.132 | 生成公钥,并推送到centos7上 |
| centos7 | 192.168.126.133 | 接受免密,实现kail往centos7方向免密 |
先按照老的免密方式搞一波
生成密钥
┌──(liushuai㉿bogon)-[~]
└─$ ssh-keygen -t dsa ###注意看,咱这边的加密方式是dsa,这个就是坑
Generating public/private dsa key pair.
Enter file in which to save the key (/home/liushuai/.ssh/id_dsa):
Created directory '/home/liushuai/.ssh'.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /home/liushuai/.ssh/id_dsa
Your public key has been saved in /home/liushuai/.ssh/id_dsa.pub
The key fingerprint is:
SHA256:k47VhY43db0GBtwHoUvZIVgnPDYui3QtT4vsGgBXewQ liushuai@bogon
The key's randomart image is:
+---[DSA 1024]----+
| E..==.=o |
| . o. BO..o |
| . . . .=+=+o .|
| o ..O.*o.. .|
| .. S %.. o |
| .= * + . |
| ..o |
| .. |
| .. |
+----[SHA256]-----+
拷贝密钥
┌──(liushuai㉿bogon)-[~]
└─$ ssh-copy-id root@192.168.196.133
/usr/bin/ssh-copy-id: INFO: Source of key(s) to be installed: "/home/liushuai/.ssh/id_dsa.pub"
The authenticity of host '192.168.196.133 (192.168.196.133)' can't be established.
ED25519 key fingerprint is SHA256:ieG7iUYRDYyuZcBk5f2ABb9S2us0LzsIZEJqzhQwdFM.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
/usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
root@192.168.196.133's password: Number of key(s) added: 1Now try logging into the machine, with: "ssh 'root@192.168.196.133'"
and check to make sure that only the key(s) you wanted were added.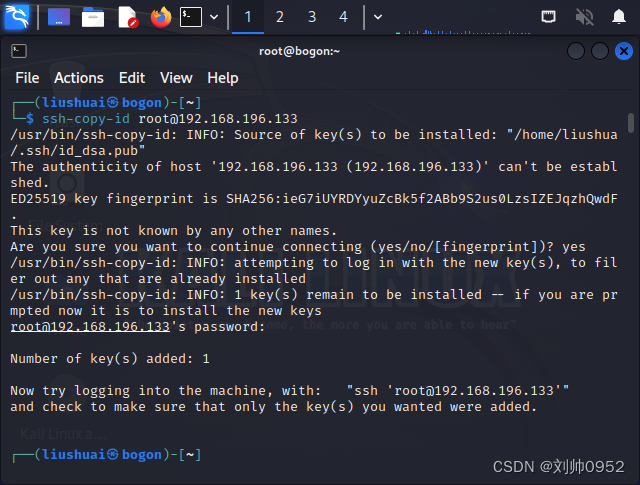
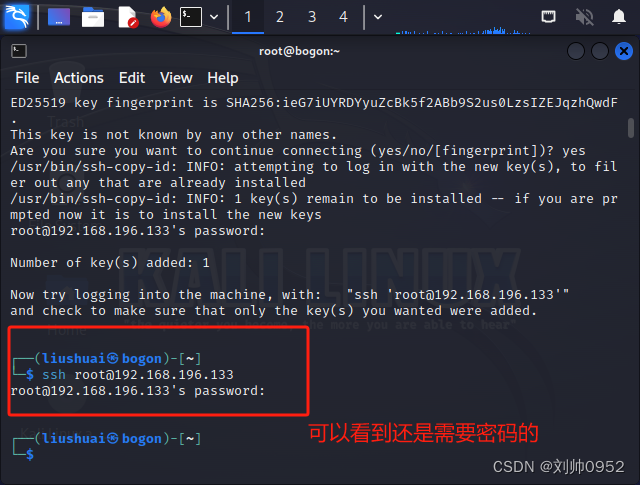
测试免密登录
┌──(liushuai㉿bogon)-[~]
└─$ ssh root@192.168.196.133
root@192.168.196.133's password: ####还是需要密码的,为什么的接着往下看
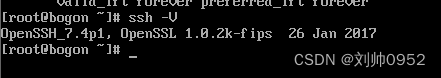
原因分析
经过排查,是因为两台主机的ssh版本问题
kail系统的版本:OpenSSH_9.3p2 Debian-1
┌──(liushuai㉿bogon)-[~]
└─$ ssh -V
OpenSSH_9.3p2 Debian-1, OpenSSL 3.0.10 1 Aug 2023
centos的版本:7.4P1
进一步分析
利用ssh -vvv的功能,查看问题出现在哪里
┌──(liushuai㉿bogon)-[~]
└─$ ssh root@192.168.196.133
root@192.168.196.133's password:
Last login: Wed Nov 29 07:52:35 2023
[root@bogon ~]# exit
logout
Connection to 192.168.196.133 closed.┌──(liushuai㉿bogon)-[~]
└─$ ssh root@192.168.196.133 -vvv
OpenSSH_9.3p2 Debian-1, OpenSSL 3.0.10 1 Aug 2023
debug1: Reading configuration data /etc/ssh/ssh_config
debug1: /etc/ssh/ssh_config line 19: include /etc/ssh/ssh_config.d/*.conf matched no files
debug1: /etc/ssh/ssh_config line 21: Applying options for *
debug2: resolve_canonicalize: hostname 192.168.196.133 is address
debug3: expanded UserKnownHostsFile '~/.ssh/known_hosts' -> '/home/liushuai/.ssh/known_hosts'
debug3: expanded UserKnownHostsFile '~/.ssh/known_hosts2' -> '/home/liushuai/.ssh/known_hosts2'
debug3: ssh_connect_direct: entering
debug1: Connecting to 192.168.196.133 [192.168.196.133] port 22.
debug3: set_sock_tos: set socket 3 IP_TOS 0x10
debug1: Connection established.
debug1: identity file /home/liushuai/.ssh/id_rsa type -1
debug1: identity file /home/liushuai/.ssh/id_rsa-cert type -1
debug1: identity file /home/liushuai/.ssh/id_ecdsa type -1
debug1: identity file /home/liushuai/.ssh/id_ecdsa-cert type -1
debug1: identity file /home/liushuai/.ssh/id_ecdsa_sk type -1
debug1: identity file /home/liushuai/.ssh/id_ecdsa_sk-cert type -1
debug1: identity file /home/liushuai/.ssh/id_ed25519 type -1
debug1: identity file /home/liushuai/.ssh/id_ed25519-cert type -1
debug1: identity file /home/liushuai/.ssh/id_ed25519_sk type -1
debug1: identity file /home/liushuai/.ssh/id_ed25519_sk-cert type -1
debug1: identity file /home/liushuai/.ssh/id_xmss type -1
debug1: identity file /home/liushuai/.ssh/id_xmss-cert type -1
debug1: identity file /home/liushuai/.ssh/id_dsa type 1
debug1: identity file /home/liushuai/.ssh/id_dsa-cert type -1
debug1: Local version string SSH-2.0-OpenSSH_9.3p2 Debian-1
debug1: Remote protocol version 2.0, remote software version OpenSSH_7.4
debug1: compat_banner: match: OpenSSH_7.4 pat OpenSSH_7.4* compat 0x04000006
debug2: fd 3 setting O_NONBLOCK
debug1: Authenticating to 192.168.196.133:22 as 'root'
debug3: record_hostkey: found key type ED25519 in file /home/liushuai/.ssh/known_hosts:1
debug3: record_hostkey: found key type ECDSA in file /home/liushuai/.ssh/known_hosts:2
debug3: load_hostkeys_file: loaded 2 keys from 192.168.196.133
debug1: load_hostkeys: fopen /home/liushuai/.ssh/known_hosts2: No such file or directory
debug1: load_hostkeys: fopen /etc/ssh/ssh_known_hosts: No such file or directory
debug1: load_hostkeys: fopen /etc/ssh/ssh_known_hosts2: No such file or directory
debug3: order_hostkeyalgs: have matching best-preference key type ssh-ed25519-cert-v01@openssh.com, using HostkeyAlgorithms verbatim
debug3: send packet: type 20
debug1: SSH2_MSG_KEXINIT sent
debug3: receive packet: type 20
debug1: SSH2_MSG_KEXINIT received
debug2: local client KEXINIT proposal
debug2: KEX algorithms: sntrup761x25519-sha512@openssh.com,curve25519-sha256,curve25519-sha256@libssh.org,ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group16-sha512,diffie-hellman-group18-sha512,diffie-hellman-group14-sha256,ext-info-c
debug2: host key algorithms: ssh-ed25519-cert-v01@openssh.com,ecdsa-sha2-nistp256-cert-v01@openssh.com,ecdsa-sha2-nistp384-cert-v01@openssh.com,ecdsa-sha2-nistp521-cert-v01@openssh.com,sk-ssh-ed25519-cert-v01@openssh.com,sk-ecdsa-sha2-nistp256-cert-v01@openssh.com,rsa-sha2-512-cert-v01@openssh.com,rsa-sha2-256-cert-v01@openssh.com,ssh-ed25519,ecdsa-sha2-nistp256,ecdsa-sha2-nistp384,ecdsa-sha2-nistp521,sk-ssh-ed25519@openssh.com,sk-ecdsa-sha2-nistp256@openssh.com,rsa-sha2-512,rsa-sha2-256
debug2: ciphers ctos: chacha20-poly1305@openssh.com,aes128-ctr,aes192-ctr,aes256-ctr,aes128-gcm@openssh.com,aes256-gcm@openssh.com
debug2: ciphers stoc: chacha20-poly1305@openssh.com,aes128-ctr,aes192-ctr,aes256-ctr,aes128-gcm@openssh.com,aes256-gcm@openssh.com
debug2: MACs ctos: umac-64-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-256-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-64@openssh.com,umac-128@openssh.com,hmac-sha2-256,hmac-sha2-512,hmac-sha1
debug2: MACs stoc: umac-64-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-256-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-64@openssh.com,umac-128@openssh.com,hmac-sha2-256,hmac-sha2-512,hmac-sha1
debug2: compression ctos: none,zlib@openssh.com,zlib
debug2: compression stoc: none,zlib@openssh.com,zlib
debug2: languages ctos:
debug2: languages stoc:
debug2: first_kex_follows 0
debug2: reserved 0
debug2: peer server KEXINIT proposal
debug2: KEX algorithms: curve25519-sha256,curve25519-sha256@libssh.org,ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group16-sha512,diffie-hellman-group18-sha512,diffie-hellman-group-exchange-sha1,diffie-hellman-group14-sha256,diffie-hellman-group14-sha1,diffie-hellman-group1-sha1
debug2: host key algorithms: ssh-rsa,rsa-sha2-512,rsa-sha2-256,ecdsa-sha2-nistp256,ssh-ed25519
debug2: ciphers ctos: chacha20-poly1305@openssh.com,aes128-ctr,aes192-ctr,aes256-ctr,aes128-gcm@openssh.com,aes256-gcm@openssh.com,aes128-cbc,aes192-cbc,aes256-cbc,blowfish-cbc,cast128-cbc,3des-cbc
debug2: ciphers stoc: chacha20-poly1305@openssh.com,aes128-ctr,aes192-ctr,aes256-ctr,aes128-gcm@openssh.com,aes256-gcm@openssh.com,aes128-cbc,aes192-cbc,aes256-cbc,blowfish-cbc,cast128-cbc,3des-cbc
debug2: MACs ctos: umac-64-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-256-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-64@openssh.com,umac-128@openssh.com,hmac-sha2-256,hmac-sha2-512,hmac-sha1
debug2: MACs stoc: umac-64-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-256-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-64@openssh.com,umac-128@openssh.com,hmac-sha2-256,hmac-sha2-512,hmac-sha1
debug2: compression ctos: none,zlib@openssh.com
debug2: compression stoc: none,zlib@openssh.com
debug2: languages ctos:
debug2: languages stoc:
debug2: first_kex_follows 0
debug2: reserved 0
debug1: kex: algorithm: curve25519-sha256
debug1: kex: host key algorithm: ssh-ed25519
debug1: kex: server->client cipher: chacha20-poly1305@openssh.com MAC: <implicit> compression: none
debug1: kex: client->server cipher: chacha20-poly1305@openssh.com MAC: <implicit> compression: none
debug3: send packet: type 30
debug1: expecting SSH2_MSG_KEX_ECDH_REPLY
debug3: receive packet: type 31
debug1: SSH2_MSG_KEX_ECDH_REPLY received
debug1: Server host key: ssh-ed25519 SHA256:ieG7iUYRDYyuZcBk5f2ABb9S2us0LzsIZEJqzhQwdFM
debug3: record_hostkey: found key type ED25519 in file /home/liushuai/.ssh/known_hosts:1
debug3: record_hostkey: found key type ECDSA in file /home/liushuai/.ssh/known_hosts:2
debug3: load_hostkeys_file: loaded 2 keys from 192.168.196.133
debug1: load_hostkeys: fopen /home/liushuai/.ssh/known_hosts2: No such file or directory
debug1: load_hostkeys: fopen /etc/ssh/ssh_known_hosts: No such file or directory
debug1: load_hostkeys: fopen /etc/ssh/ssh_known_hosts2: No such file or directory
debug1: Host '192.168.196.133' is known and matches the ED25519 host key.
debug1: Found key in /home/liushuai/.ssh/known_hosts:1
debug3: send packet: type 21
debug2: ssh_set_newkeys: mode 1
debug1: rekey out after 134217728 blocks
debug1: SSH2_MSG_NEWKEYS sent
debug1: expecting SSH2_MSG_NEWKEYS
debug3: receive packet: type 21
debug1: SSH2_MSG_NEWKEYS received
debug2: ssh_set_newkeys: mode 0
debug1: rekey in after 134217728 blocks
debug3: ssh_get_authentication_socket_path: path '/tmp/ssh-6WK2JhuI1VHD/agent.1125'
debug1: get_agent_identities: bound agent to hostkey
debug1: get_agent_identities: ssh_fetch_identitylist: agent contains no identities
debug1: Skipping ssh-dss key /home/liushuai/.ssh/id_dsa - corresponding algo not in PubkeyAcceptedAlgorithms
debug1: Will attempt key: /home/liushuai/.ssh/id_rsa
debug1: Will attempt key: /home/liushuai/.ssh/id_ecdsa
debug1: Will attempt key: /home/liushuai/.ssh/id_ecdsa_sk
debug1: Will attempt key: /home/liushuai/.ssh/id_ed25519
debug1: Will attempt key: /home/liushuai/.ssh/id_ed25519_sk
debug1: Will attempt key: /home/liushuai/.ssh/id_xmss
debug2: pubkey_prepare: done
debug3: send packet: type 5
debug3: receive packet: type 7
debug1: SSH2_MSG_EXT_INFO received
debug1: kex_input_ext_info: server-sig-algs=<rsa-sha2-256,rsa-sha2-512>
debug3: receive packet: type 6
debug2: service_accept: ssh-userauth
debug1: SSH2_MSG_SERVICE_ACCEPT received
debug3: send packet: type 50
debug3: receive packet: type 51
debug1: Authentications that can continue: publickey,gssapi-keyex,gssapi-with-mic,password
debug3: start over, passed a different list publickey,gssapi-keyex,gssapi-with-mic,password
debug3: preferred gssapi-with-mic,publickey,keyboard-interactive,password
debug3: authmethod_lookup gssapi-with-mic
debug3: remaining preferred: publickey,keyboard-interactive,password
debug3: authmethod_is_enabled gssapi-with-mic
debug1: Next authentication method: gssapi-with-mic
debug1: No credentials were supplied, or the credentials were unavailable or inaccessible
No Kerberos credentials available (default cache: FILE:/tmp/krb5cc_1000)debug1: No credentials were supplied, or the credentials were unavailable or inaccessible
No Kerberos credentials available (default cache: FILE:/tmp/krb5cc_1000)debug1: Unspecified GSS failure. Minor code may provide more information
No such file or directorydebug2: we did not send a packet, disable method
debug3: authmethod_lookup publickey
debug3: remaining preferred: keyboard-interactive,password
debug3: authmethod_is_enabled publickey
debug1: Next authentication method: publickey
debug1: Trying private key: /home/liushuai/.ssh/id_rsa ###出现找不到文件
debug3: no such identity: /home/liushuai/.ssh/id_rsa: No such file or directory
debug1: Trying private key: /home/liushuai/.ssh/id_ecdsa ###出现找不到文件
debug3: no such identity: /home/liushuai/.ssh/id_ecdsa: No such file or directory
debug1: Trying private key: /home/liushuai/.ssh/id_ecdsa_sk ###出现找不到文件
debug3: no such identity: /home/liushuai/.ssh/id_ecdsa_sk: No such file or directory
debug1: Trying private key: /home/liushuai/.ssh/id_ed25519 ###出现找不到文件
debug3: no such identity: /home/liushuai/.ssh/id_ed25519: No such file or directory
debug1: Trying private key: /home/liushuai/.ssh/id_ed25519_sk ###出现找不到文件
debug3: no such identity: /home/liushuai/.ssh/id_ed25519_sk: No such file or directory
debug1: Trying private key: /home/liushuai/.ssh/id_xmss ###出现找不到文件
debug3: no such identity: /home/liushuai/.ssh/id_xmss: No such file or directory
debug2: we did not send a packet, disable method
debug3: authmethod_lookup password
debug3: remaining preferred: ,password
debug3: authmethod_is_enabled password
debug1: Next authentication method: password
root@192.168.196.133's password:
更改加密方式为rsa
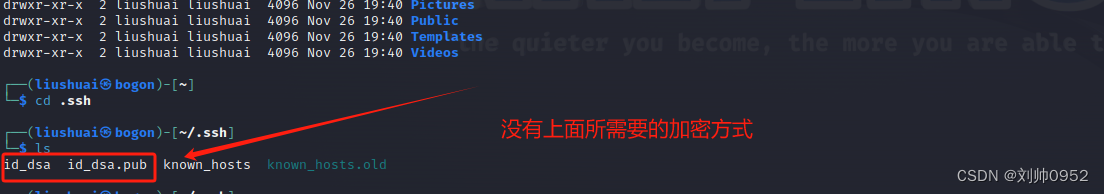
清理掉之前的密钥文件
──(liushuai㉿bogon)-[~]
└─$ cd .ssh ┌──(liushuai㉿bogon)-[~/.ssh]
└─$ ls
id_dsa id_dsa.pub known_hosts known_hosts.old┌──(liushuai㉿bogon)-[~/.ssh] ###直接在.ssh目录下,清理即可,如有需要建议备份
└─$ rm -rf *
zsh: sure you want to delete all 4 files in /home/liushuai/.ssh [yn]? y┌──(liushuai㉿bogon)-[~/.ssh]
└─$ ls ### 重新生成密钥
### 重新生成密钥
┌──(liushuai㉿bogon)-[~/.ssh]
└─$ ssh-keygen -t rsa ##更换了加密算法为rsa
Generating public/private rsa key pair.
Enter file in which to save the key (/home/liushuai/.ssh/id_rsa):
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /home/liushuai/.ssh/id_rsa
Your public key has been saved in /home/liushuai/.ssh/id_rsa.pub
The key fingerprint is:
SHA256:VvO9A4ARor8FdlPJ2n6mpUy0ZOp3jRQpaitbqKTGTRI liushuai@bogon
The key's randomart image is:
+---[RSA 3072]----+
| . oo.. |
| . . +o |
| . o +o+ . |
| E o o.o*+o. |
| . . SB oo.. |
| . . =+ + =. . |
| . +. oo.+ B oo |
| oo....o = o .. |
| .. . .o . . |
+----[SHA256]-----+推送密钥
──(liushuai㉿bogon)-[~/.ssh]
└─$ ssh-copy-id root@192.168.196.133 ###推送方式不变
/usr/bin/ssh-copy-id: INFO: Source of key(s) to be installed: "/home/liushuai/.ssh/id_rsa.pub"
The authenticity of host '192.168.196.133 (192.168.196.133)' can't be established.
ED25519 key fingerprint is SHA256:ieG7iUYRDYyuZcBk5f2ABb9S2us0LzsIZEJqzhQwdFM.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
/usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
root@192.168.196.133's password: Number of key(s) added: 1Now try logging into the machine, with: "ssh 'root@192.168.196.133'"
and check to make sure that only the key(s) you wanted were added.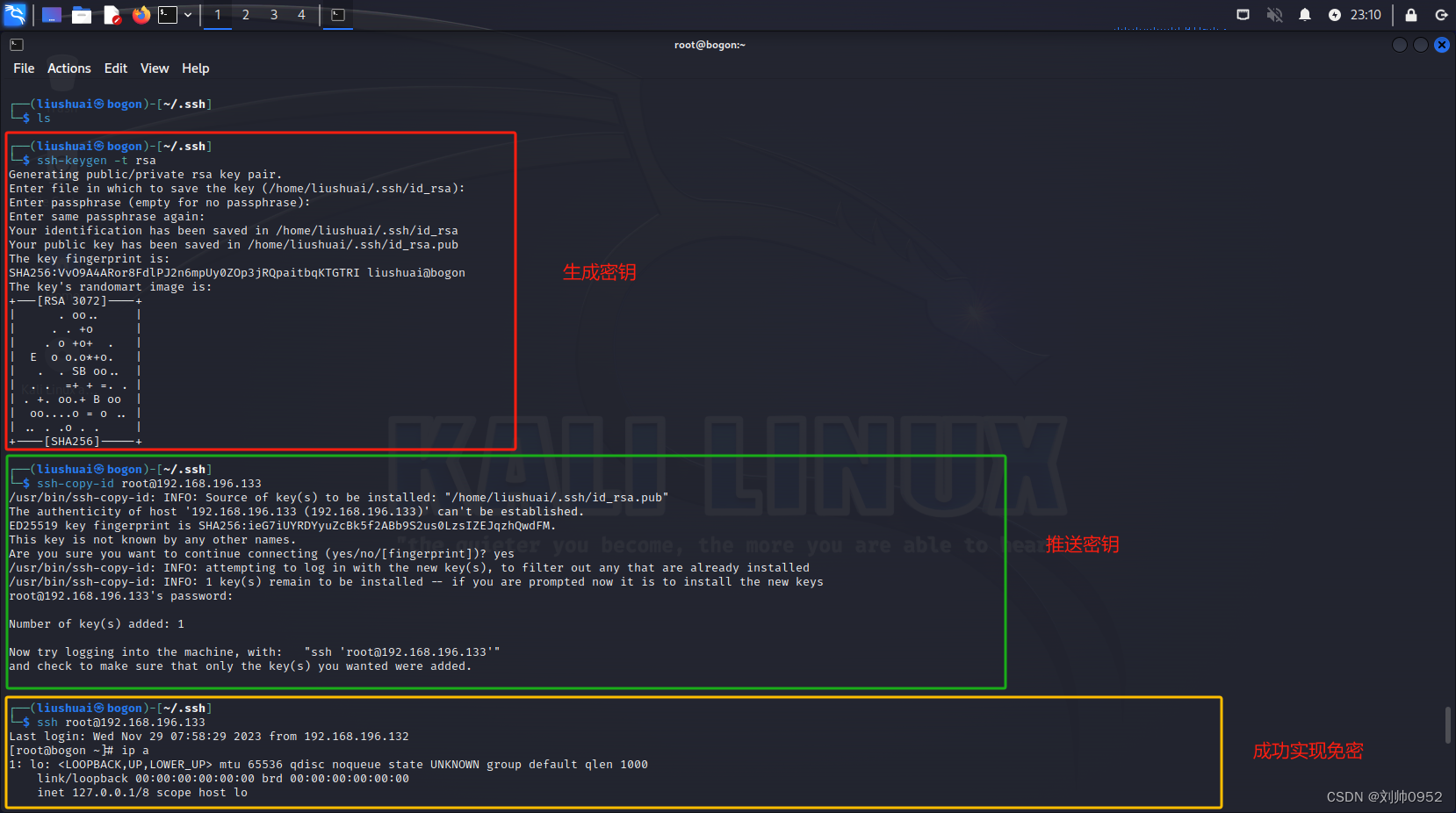
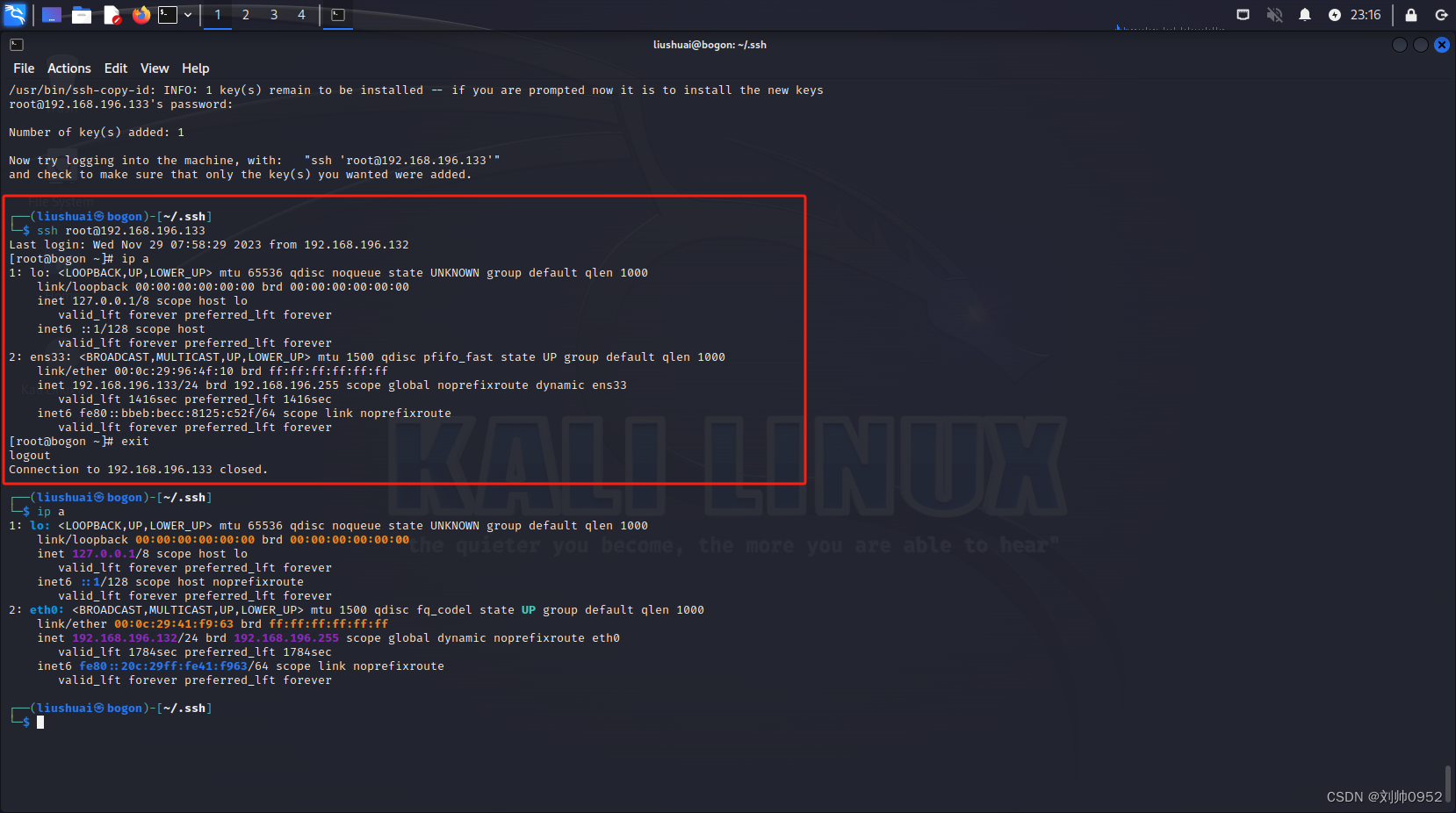
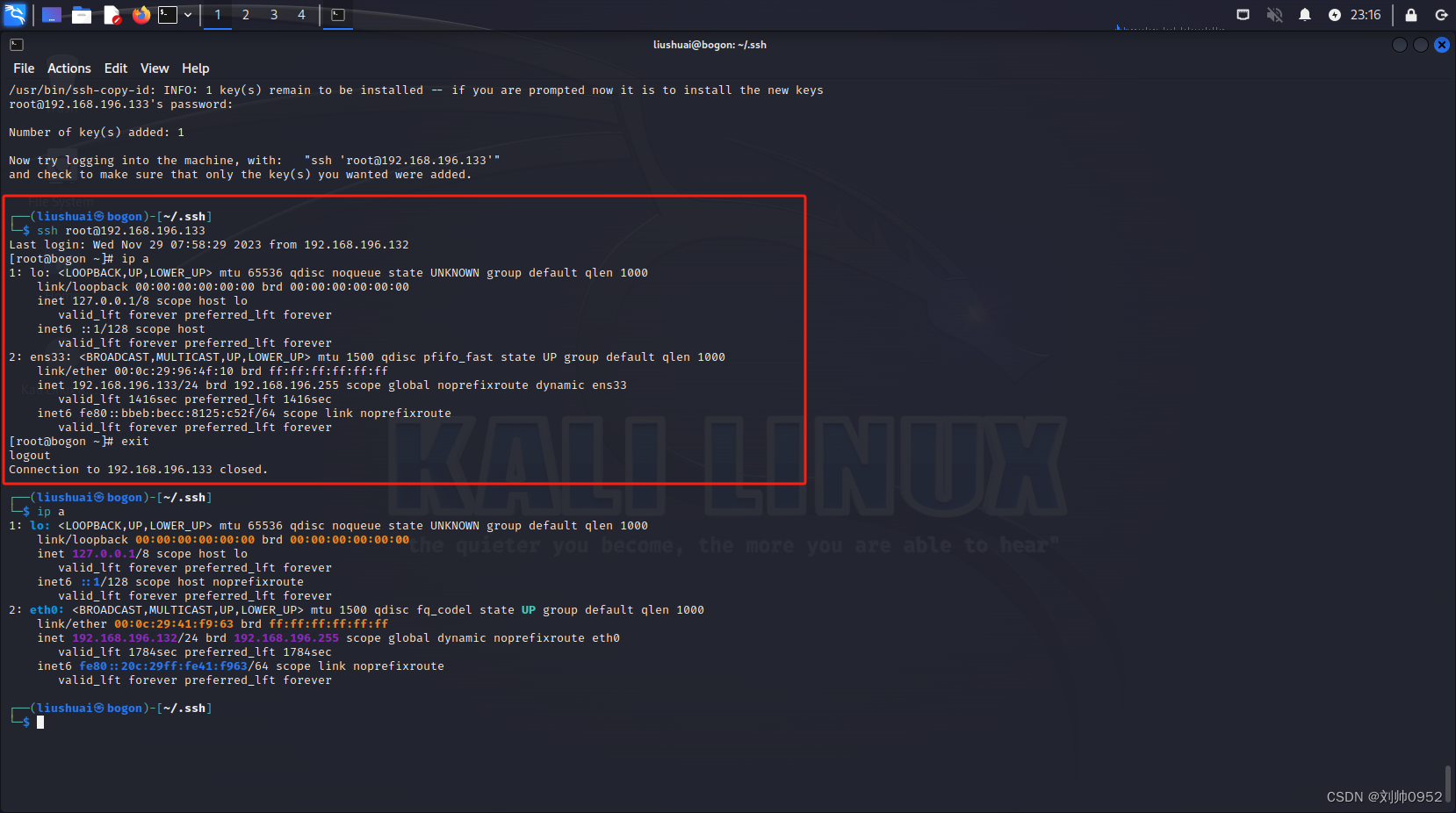
测试免密效果
└─$ ssh root@192.168.196.133
Last login: Wed Nov 29 07:58:29 2023 from 192.168.196.132
[root@bogon ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00inet 127.0.0.1/8 scope host lovalid_lft forever preferred_lft foreverinet6 ::1/128 scope host valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000link/ether 00:0c:29:96:4f:10 brd ff:ff:ff:ff:ff:ffinet 192.168.196.133/24 brd 192.168.196.255 scope global noprefixroute dynamic ens33valid_lft 1416sec preferred_lft 1416secinet6 fe80::bbeb:becc:8125:c52f/64 scope link noprefixroute valid_lft forever preferred_lft forever
[root@bogon ~]# exit
logout
Connection to 192.168.196.133 closed.
结束语
没有随随便便的成功,只有不断的努力
相关文章:
血的教训--kail系统免密centos7的坑【高版本ssh免密低版本ssh的坑】
血的教训–kail系统免密centos7的坑【高版本ssh免密低版本ssh的坑】 最近下载了一个2023版本的kail系统,但是经过几次设置免密后,ssh过去一直让提供密码,所以就仔细的分析了一下,果然还是发现了点猫腻 接上一个博客,大…...
javaagent字节码增强浅尝
概述 javaagent 技术广泛应用于对代码的增强,比如统计方法执行时间、GC 信息打印、分布式链路跟踪等;实现方式包括 javassist 和 bytebuddy,bytebuddy 是对 javassist 的改进;类似于 spring 中的 AOP; Instrumentati…...
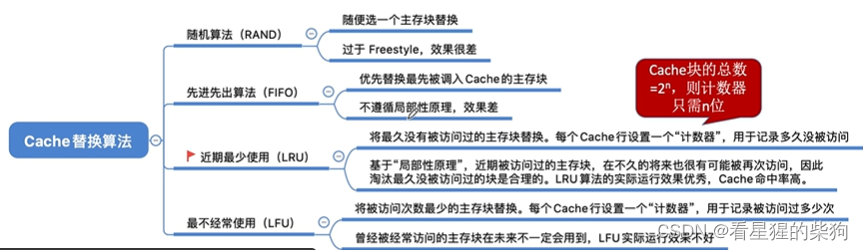
计算机组成原理-Cache替换算法
文章目录 总览随机算法(RAND)先进先出算法(FIFO)近期最少使用算法(LRU)最不经常使用算法(LFU)总结 总览 随机算法(RAND) 没有选择性地考虑替换哪一块Cache&a…...

Adobe 家族系列download
adobe 前言 Adobe公司的产品线中拥有多个家族桶,下面是Adobe全家桶产品的功能介绍: Creative Cloud(创意云):包含Photoshop、Illustrator、InDesign、Premiere Pro、After Effects、Lightroom等创意设计、视频制作和…...
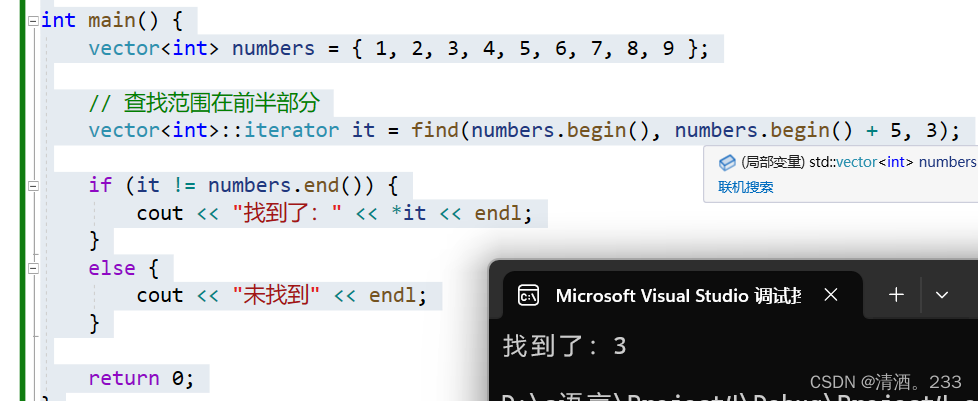
97.STL-查找算法 find
目录 STL-查找算法find 1.基本用法: 2.查找自定义类型: 3.查找范围: STL-查找算法find 在C的STL(标准模板库)中,find 算法用于在指定范围内查找指定值的元素。 功能描述: 查找指定元素&…...

如何应对雨天飞行的挑战?无人机机库防护能力解析
一、 背景介绍 无人机机库是无人机停放和起降场所,类似传统飞机的 hangar(飞机库)。它是一个专门用于存储、维护和保护无人机的设施。无人机机库的存在有助于提高无人机的安全性,同时也为无人机提供了一个有序的管理场所。 雨天…...
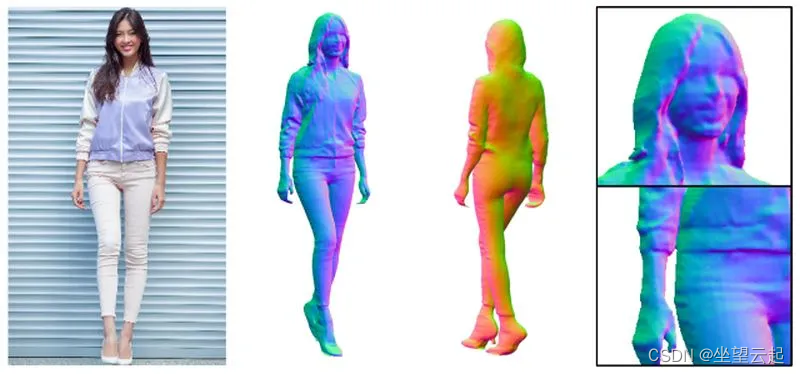
机器学习笔记 - 3D数据的常见表示方式
一、简述 从单一角度而自动合成3D数据是人类视觉和大脑的基本功能,这对计算机视觉算法来说是比较难的。但随着LiDAR、RGB-D 相机(RealSense、Kinect)和3D扫描仪等3D传感器的普及和价格的降低,3D 采集技术的最新进展取得了巨大飞跃。与广泛使用的 2D 数据不同,3D 数据具有丰…...
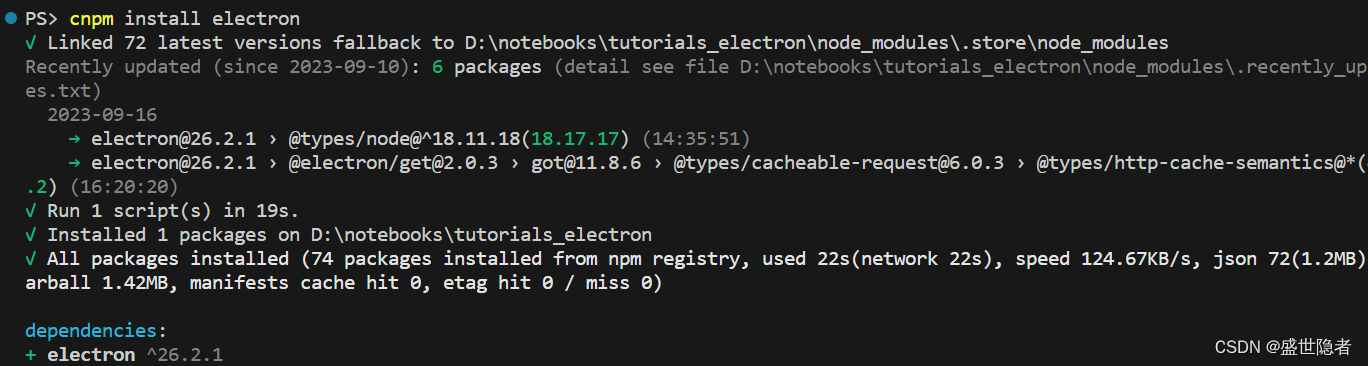
【Node.js】解决npm报错:RequestError: unable to verify the first certificate
1. 问题简述 帖主从nodejs官网下载安装nodejs后,发现使用以下命令安装electron会报错: npm install electron 报错信息如下: npm ERR! RequestError: unable to verify the first certificate 2. 解决方案 网上列举的方案,无…...
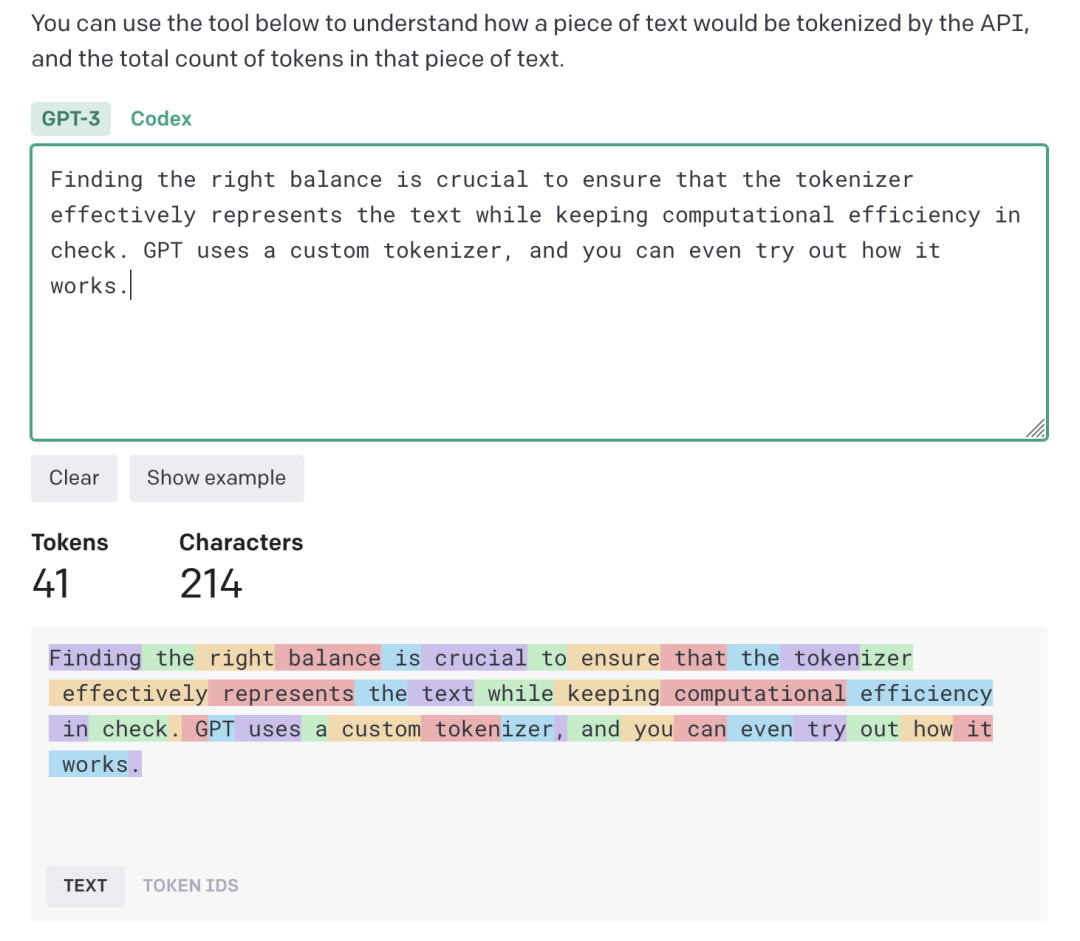
语言模型文本处理基石:Tokenizer简明概述
编者按:近年来,人工智能技术飞速发展,尤其是大型语言模型的问世,让 AI 写作、聊天等能力有了质的飞跃。如何更好地理解和利用这些生成式 AI,成为许多开发者和用户关心的问题。 今天,我们推出的这篇文章有助…...
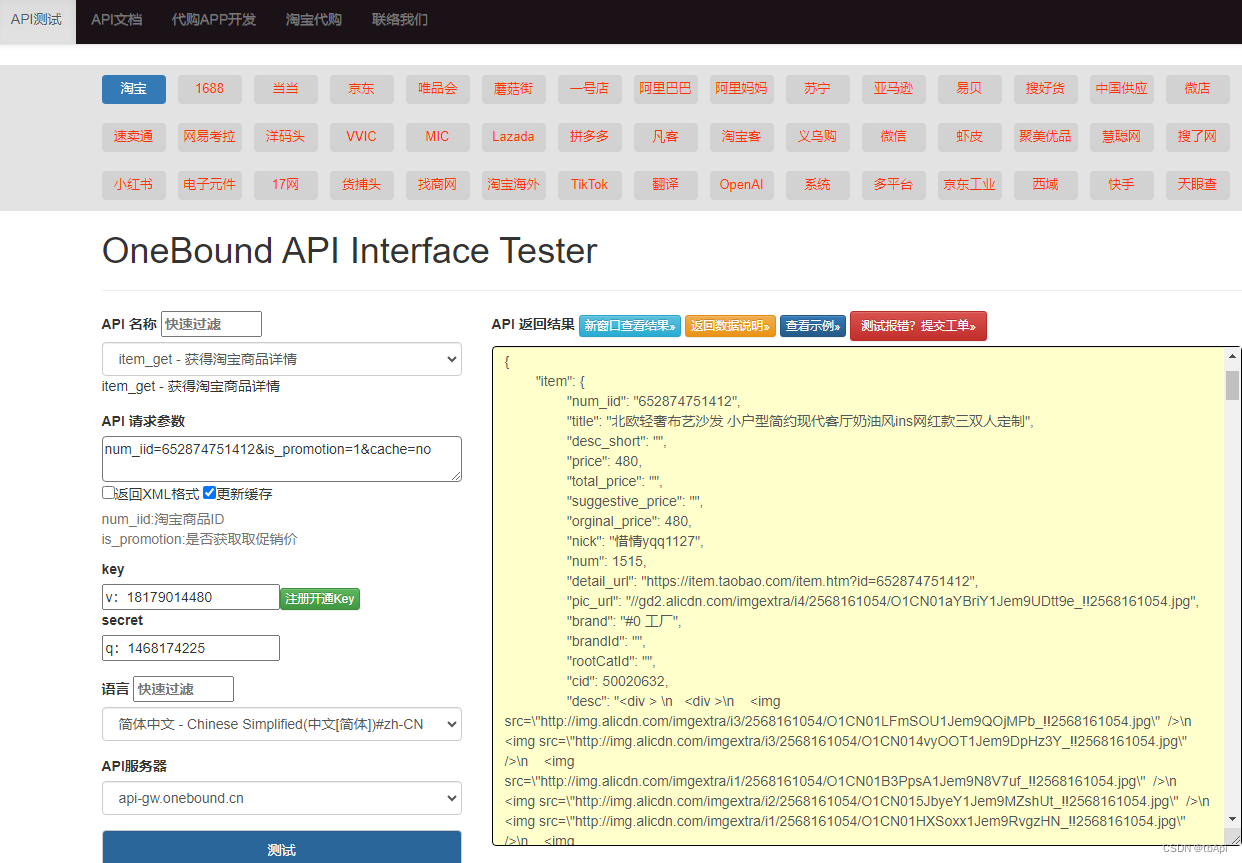
淘宝商品详情数据接口(店铺搬家、数据分析、代购商城、ERP选品、无货源铺货、品牌监控)
使用淘宝API接口需要以下步骤: 注册开发者账号:在淘宝开放平台(https://o0b.cn/anzexi)上注册一个开发者账号,并创建一个应用。 获取API密钥:在应用页面上获取API密钥,这是后续调用API接口的凭…...
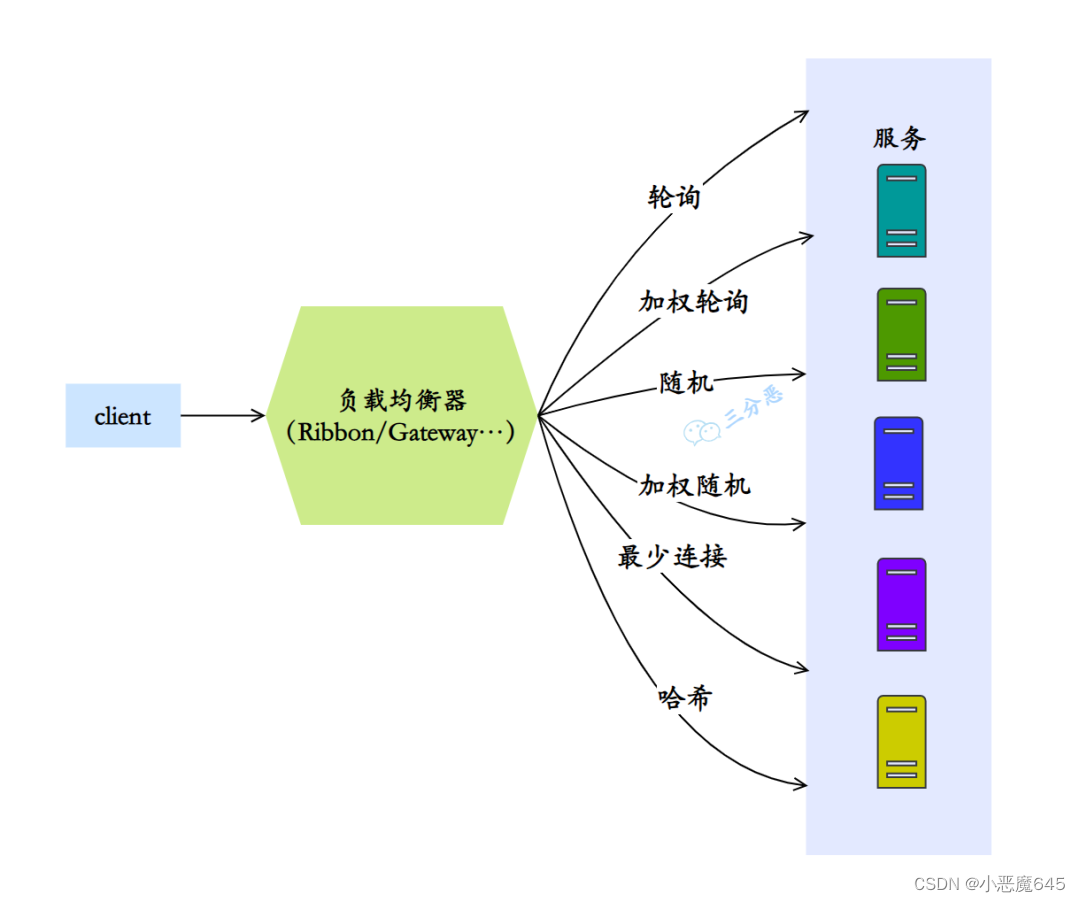
面试篇之微服务(一)
目录 概览 1.什么是微服务? 2.微服务带来了哪些挑战? 3.现在有哪些流行的微服务解决方案? 这三种方案有什么区别吗? 4.说下微服务有哪些组件? 注册中心 5.注册中心是用来干什么的? 6.SpringCloud可…...

智慧科研助力科研数据的分析处理
如今,科研领域的发展日新月异,数据量也越来越大。这时,智慧科研可视化技术不仅为科研人员提供了快速高效的数据分析手段,而且为科研工作的推进提供了新的思路和方法。通过可视化手段,我们可以将各种数据、信息、知识以…...

el-select实现分屏效果
动态绑定class值 ,多种判断 :class"type 8 ? home-stye-2 : type 24 ? home-stye-1 : home-stye-3" <div class"home-right-top"><div class"home-right-top-video"><el-row :gutter"20"><el-c…...
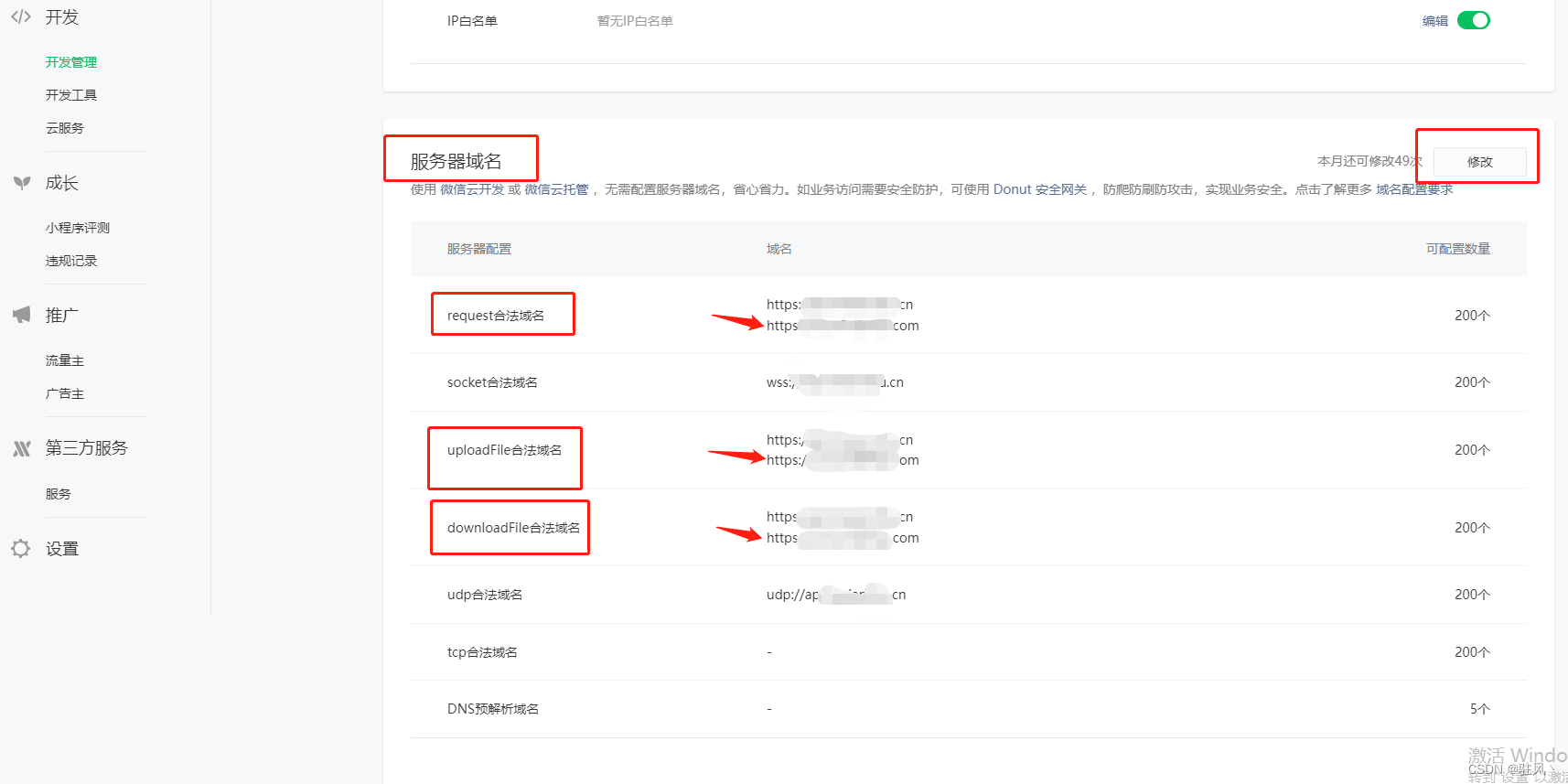
微信小程序本地和真机调试文件上传成功但体验版不成功
可能是微信小程序ip白名单的问题,去微信公众平台(小程序)上设置小程序的ip白名单 1、在本地中取消不校验 然后在本地去上传文件,就会发现控制台报错了,会提示一个https什么不在ip白名单,复制那个网址 2、…...
windows系统用nginx部署web应用
要在Windows系统上使用Nginx进行本地部署和运行Web应用程序,可以按照以下步骤进行操作: 1.首先下载nginx,需要去nginx官网: nginx: download 下载最新版本的: 2.解压缩Nginx:找个磁盘位置,新…...
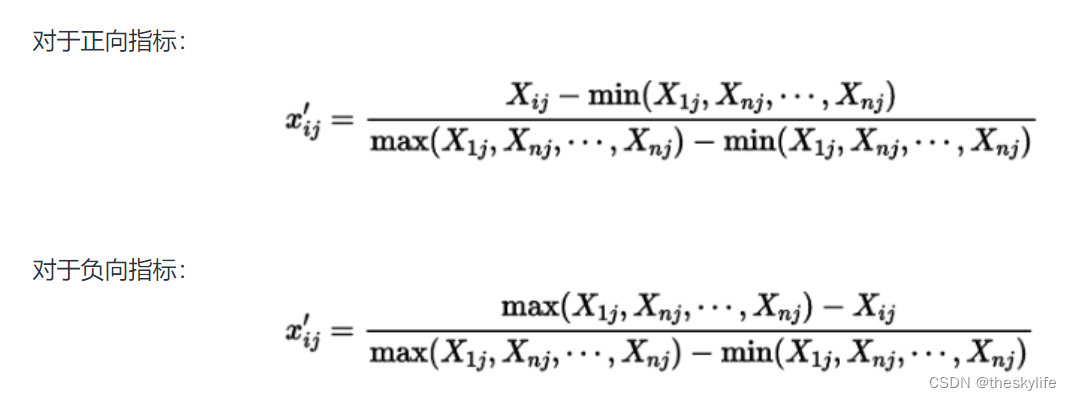
如何利用Python进行数据归一化?
1. 知识简介 数据归一化是数据预处理的一项重要步骤,它对于提高模型性能、加速模型训练、避免数值计算问题以及提高模型的泛化能力都具有重要作用。进行数据归一化可以起到以下作用:消除量纲影响,加速模型收敛,提高模型性能&…...
Linux 基本语句_13_消息队列
概念: 不同进程能通过消息队列来进行通信,不同进程也能获取或发送特定类型的消息,即选择性的收发消息。 一般一个程序采取子进程发消息,父进程收消息的模式 常用函数功能: fork(); // 创建子进程 struct msgbuf{ …...
Maven——仓库
Maven坐标和依赖是任何一个构件在Maven世界中的逻辑表示方式;而构件的物理表示方式是文件,Maven通过仓库来统一管理这些文件。 1、何为Maven仓库 在Maven世界中,任何一个依赖、插件或者项目构建的输出,都可以称为构件。例如&…...

Pandas:一个实用高效的Python数据处理库
个人网站 文章首发公众号:小肖学数据分析 导语: Pandas是一个强大且易于使用的Python数据处理库,广泛应用于数据分析和数据科学领域。本文将介绍Pandas库的基本概念、功能和使用方法,并提供详细的示例,帮助小白快速…...
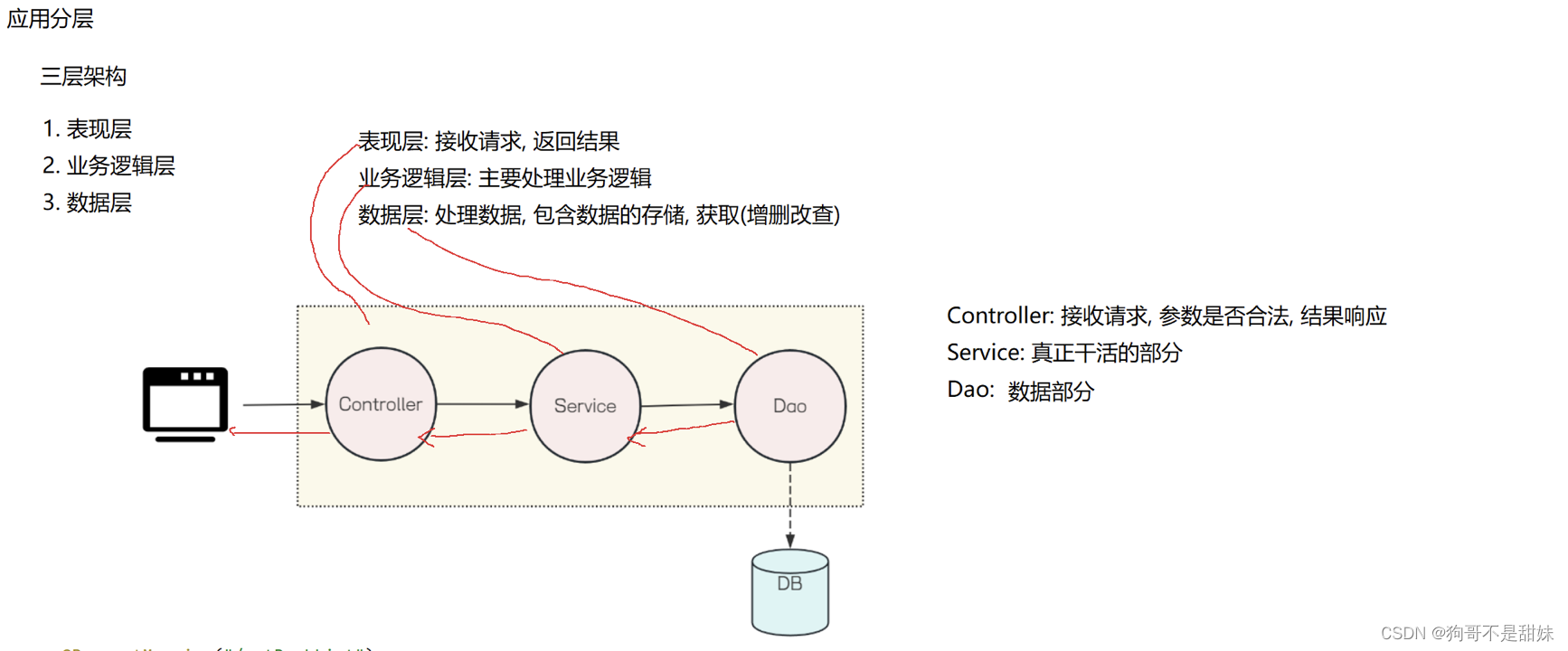
Spring第三课,Lombok工具包下载,对应图书管理系统列表和登录界面的后端代码,分层思想
目录 一、Lombok工具包下载 二、前后端互联的图书管理系统 规范 三、分层思想 三层架构: 1.表现层 2.业务逻辑层 3.数据层 一、Lombok工具包下载 这个工具包是为了做什么呢? 他是为了不去反复的设置setting and getting 而去产生的工具包 ⚠️工具…...

基于KS距离度量交通流分布偏移:提升DRL交通信号控制鲁棒性的工程实践
1. 项目概述与核心挑战在智能交通系统(ITS)领域,基于深度强化学习(DRL)的交通信号控制(Traffic Signal Control)正从研究走向实际部署。作为一名长期关注AI落地应用的从业者,我见过太…...

WarcraftHelper:让魔兽争霸3在现代电脑上完美运行的关键插件
WarcraftHelper:让魔兽争霸3在现代电脑上完美运行的关键插件 【免费下载链接】WarcraftHelper Warcraft III Helper , support 1.20e, 1.24e, 1.26a, 1.27a, 1.27b 项目地址: https://gitcode.com/gh_mirrors/wa/WarcraftHelper 你是否还在为《魔兽争霸3》这…...

Lovable电商网站搭建,为什么92%的初创团队在第3周就遭遇性能雪崩?
更多请点击: https://codechina.net 第一章:Lovable电商网站搭建 Lovable 是一个面向中小商户的轻量级电商解决方案,采用现代 Web 技术栈构建,强调可扩展性、用户体验与快速部署。其核心基于 Vue 3(Composition API&a…...

HarmonyOS DateUtil 日期工具入门:格式化、时间戳与今日信息
文章目录背景一、HarmonyOS 日期处理的痛点二、核心方法:getFormatDate三、时间戳自动补位四、核心方法:getFormatDateStr五、今日信息快速获取六、完整 Demo 演示6.1 刷新当前时间6.2 格式化演示6.3 常用格式展示6.4 基础信息 UI6.5 intl.DateTimeForma…...
)
【独家首发】DeepSeek边缘计算白皮书未公开章节:3类典型场景QoS SLA保障公式(含实测RTT抖动衰减模型)
更多请点击: https://intelliparadigm.com 第一章:DeepSeek边缘计算架构全景概览 DeepSeek边缘计算架构以“轻量、协同、自治”为核心设计理念,面向AI推理密集型场景构建端—边—云三级协同的分布式智能执行体。该架构并非传统云中心化模型的…...

多智能体协作系统:2026年企业级AI应用的核心架构范式
引言:AI Agent从单兵作战到团队协作的范式跃迁 2026年,人工智能领域正在经历一场深刻的架构变革。回想2024年,当ChatGPT、Claude等大语言模型横空出世时,我们惊叹于单个AI模型的强大能力。然而,随着企业级应用的深入,单一AI Agent的局限性日益凸显:它无法同时处理多领域…...

从UE/Unity转战Godot:一个老引擎开发者的踩坑与真香实录
从UE/Unity转战Godot:一个老引擎开发者的踩坑与真香实录 第一次双击Godot图标时,我正坐在堆满Unity参考书的办公桌前。作为用过五年Unity、三年Unreal的"引擎老油条",我带着审视新玩具的心态点开了这个不到100MB的绿色软件——没想…...

Redis Bitmap的隐藏用法:从“优惠券防超领”到“大数据去重”的实战避坑指南
Redis Bitmap的隐藏用法:从“优惠券防超领”到“大数据去重”的实战避坑指南 在数据密集型的现代应用中,如何高效处理海量数据的唯一性校验和状态标记,一直是开发者面临的挑战。Redis的Bitmap数据结构以其极低的内存消耗和O(1)时间复杂度的位…...

收藏|2026 新版大模型入行指南!风口红利期程序员小白均可入局
2026年人工智能行业发展势头迅猛,已然迈入全民争相布局的高速发展阶段。多模态技术持续更新升级,大模型各类商业化项目不断落地投产,市场专业人才缺口不断拉大,对应岗位薪酬待遇也迎来大幅上涨。 不管是毫无技术基础、打算从零起步…...

解决grunt-webfont常见问题:跨浏览器兼容与Firefox字体加载故障排除指南
解决grunt-webfont常见问题:跨浏览器兼容与Firefox字体加载故障排除指南 【免费下载链接】grunt-webfont SVG to webfont converter for Grunt 项目地址: https://gitcode.com/gh_mirrors/gr/grunt-webfont grunt-webfont 是一个强大的SVG转网页字体工具&…...
