【Android】Mobile-Security-Framework-MobSF Manifest 静态扫描规则
前言
移动安全框架(MobSF)是一个自动化的一体化移动应用程序(Android/iOS/Windows)测试、恶意软件分析和安全评估框架,能够执行静态和动态分析。MobSF支持移动应用程序二进制文件(APK、XAPK、IPA和APPX)以及压缩源代码,并提供REST API,可与您的CI/CD或DevSecOps管道无缝集成。动态分析器可帮助您执行运行时安全评估和交互式仪器测试。
通过分析源码中对manifest的检测规则,来学习其可能存在的安全风险。
正文
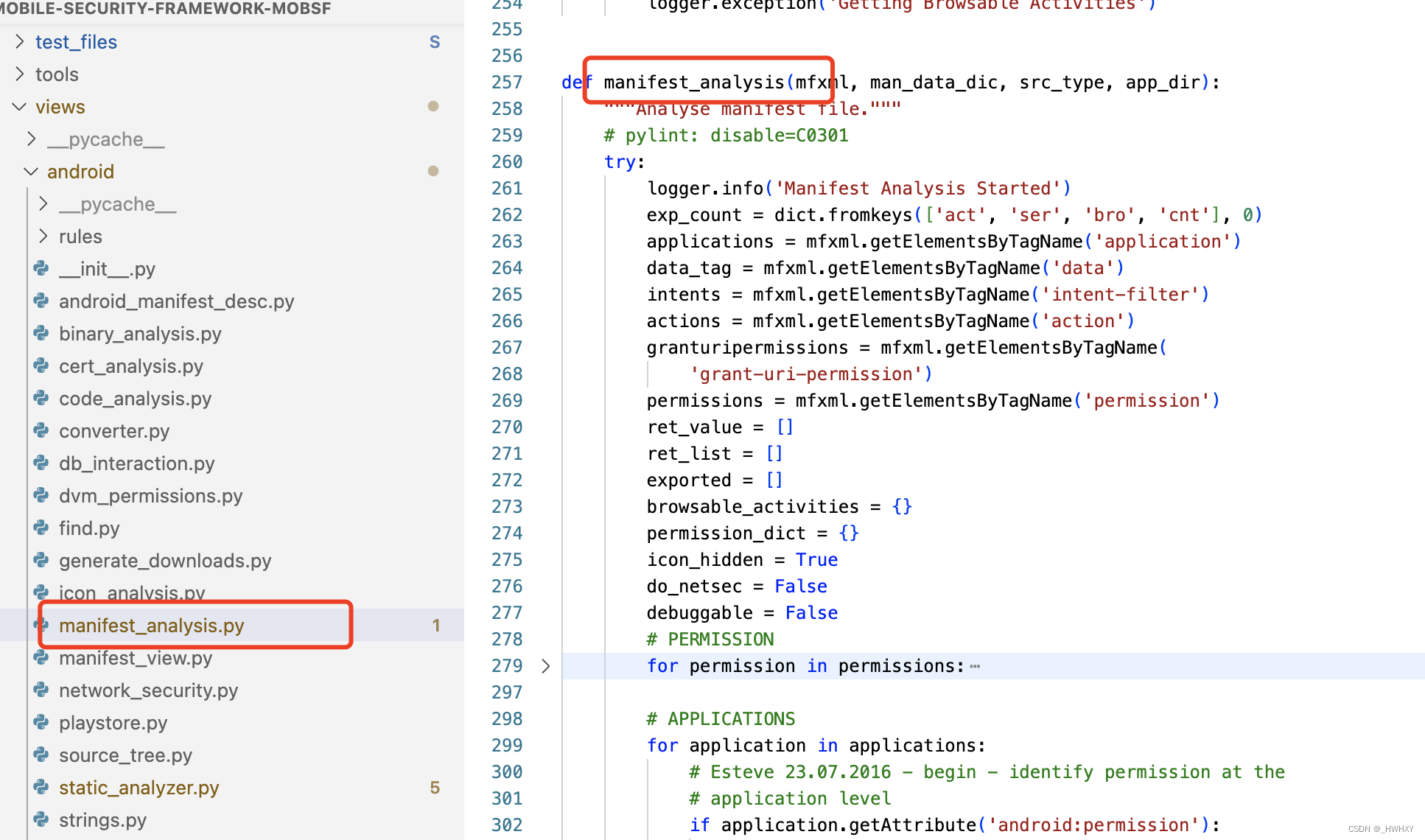
源码位置views/android/manifest_analysis.py的manifest_analysis函数
high*6
| 规则名 | 条件 | 级别 | 描述 |
| a_clear_text | android:usesCleartextTraffic=true | high | The app intends to use cleartext network traffic, such as cleartext HTTP, FTP stacks, DownloadManager, and MediaPlayer. The default value for apps that target API level 27 or lower is "true". Apps that target API level 28 or higher default to "false". The key reason for avoiding cleartext traffic is the lack of confidentiality, authenticity, and protections against tampering; a network attacker can eavesdrop on transmitted data and also modify it without being detected. |
| a_debuggable | android:debuggable=true | high | Debugging was enabled on the app which makes it easier for reverse engineers to hook a debugger to it. This allows dumping a stack trace and accessing debugging helper classes. |
| a_testonly | android:testOnly=true | high | It may expose functionality or data outside of itself that would cause a security hole. |
| a_launchmode | android:launchMode = singleInstance or singleTask | high | An Activity should not be having the launch mode attribute set to "singleTask/singleInstance" as it becomes root Activity and it is possible for other applications to read the contents of the calling Intent. So it is required to use the "standard" launch mode attribute when sensitive information is included in an Intent. |
| a_not_protected | android:exported=true | high | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. |
| a_improper_provider | android:pathPrefix == / | high | A content provider permission was set to allows access from any other app on the device. Content providers may contain sensitive information about an app and therefore should not be shared. |
warning*28
| 规则名 | 条件 | 级别 | 描述 |
| a_allowbackup | Application Data can be Backed up [android:allowBackup=true] | warning | This flag allows anyone to backup your application data via adb. It allows users who have enabled USB debugging to copy application data off of the device. |
| a_allowbackup_miss | Application Data can be Backed up [android:allowBackup] flag is missing. | warning | The flag [android:allowBackup] should be set to false. By default it is set to true and allows anyone to backup your application data via adb. It allows users who have enabled USB debugging to copy application data off of the device. |
| a_taskaffinity | TaskAffinity is set for Activity | warning | If taskAffinity is set, then other application could read the Intents sent to Activities belonging to another task. Always use the default setting keeping the affinity as the package name in order to prevent sensitive information inside sent or received Intents from being read by another application. |
| a_prot_normal | is Protected by a permission, but the protection level of the permission should be checked.[android:exported=true] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by a permission. However, the protection level of the permission is set to normal. This means that a malicious application can request and obtain the permission and interact with the component. If it was set to signature, only applications signed with the same certificate could obtain the permission. |
| a_prot_danger | is Protected by a permission, but the protection level of the permission should be checked.[android:exported=true] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by a permission. However, the protection level of the permission is set to dangerous. This means that a malicious application can request and obtain the permission and interact with the component. If it was set to signature, only applications signed with the same certificate could obtain the permission. |
| a_prot_unknown | is Protected by a permission, but the protection level of the permission should be checked.[android:exported=true] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by a permission which is not defined in the analysed application. As a result, the protection level of the permission should be checked where it is defined. If it is set to normal or dangerous, a malicious application can request and obtain the permission and interact with the component. If it is set to signature, only applications signed with the same certificate can obtain the permission. |
| a_prot_normal_appl | is Protected by a permission at the application level, but the protection level of the permission should be checked.[android:exported=true] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by a permission at the application level. However, the protection level of the permission is set to normal. This means that a malicious application can request and obtain the permission and interact with the component. If it was set to signature, only applications signed with the same certificate could obtain the permission. |
| a_prot_danger_appl | is Protected by a permission at the application level, but the protection level of the permission should be checked.[android:exported=true] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by a permission at the application level. However, the protection level of the permission is set to dangerous. This means that a malicious application can request and obtain the permission and interact with the component. If it was set to signature, only applications signed with the same certificate could obtain the permission. |
| a_prot_unknown_appl | is Protected by a permission at the application, but the protection level of the permission should be checked.[android:exported=true] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by a permission at the application level which is not defined in the analysed application. As a result, the protection level of the permission should be checked where it is defined. If it is set to normal or dangerous, a malicious application can request and obtain the permission and interact with the component. If it is set to signature, only applications signed with the same certificate can obtain the permission. |
| a_not_protected_filter | is not Protected.An intent-filter exists. | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. The presence of intent-filter indicates that the %s is explicitly exported. |
| c_not_protected | is not Protected.[[Content Provider, targetSdkVersion < 17] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is a Content Provider that targets an API level under 17, which makes it exported by default, regardless of the API level of the system that the application runs on. |
| c_not_protected2 | would not be Protected if the application ran on a device where the the API level was less than 17.[Content Provider, targetSdkVersion >= 17] | warning | The Content Provider(%s %s) would be exported if the application ran on a device where the the API level was less than 17. In that situation, it would be shared with other apps on the device therefore leaving it accessible to any other application on the device. |
| c_prot_normal | is Protected by a permission, but the protection level of the permission should be checked.[Content Provider, targetSdkVersion < 17] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by a permission. However, the protection level of the permission is set to normal. This means that a malicious application can request and obtain the permission and interact with the component. If it was set to signature, only applications signed with the same certificate could obtain the permission. |
| c_prot_danger | is Protected by a permission, but the protection level of the permission should be checked.[Content Provider, targetSdkVersion < 17] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by a permission. However, the protection level of the permission is set to dangerous. This means that a malicious application can request and obtain the permission and interact with the component. If it was set to signature, only applications signed with the same certificate could obtain the permission. |
| c_prot_unknown | is Protected by a permission, but the protection level of the permission should be checked.[Content Provider, targetSdkVersion < 17] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by a permission which is not defined in the analysed application. As a result, the protection level of the permission should be checked where it is defined. If it is set to normal or dangerous, a malicious application can request and obtain the permission and interact with the component. If it is set to signature, only applications signed with the same certificate can obtain the permission. |
| c_prot_normal_appl | is Protected by a permission at the application level, but the protection level of the permission should be checked.[Content Provider, targetSdkVersion < 17] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by a permission at the application level. However, the protection level of the permission is set to normal. This means that a malicious application can request and obtain the permission and interact with the component. If it was set to signature, only applications signed with the same certificate could obtain the permission. |
| c_prot_danger_appl | is Protected by a permission at the application level, but the protection level of the permission should be checked.[Content Provider, targetSdkVersion < 17] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by a permission at the application level. However, the protection level of the permission is set to dangerous. This means that a malicious application can request and obtain the permission and interact with the component. If it was set to signature, only applications signed with the same certificate could obtain the permission. |
| c_prot_unknown_appl | is Protected by a permission at application level, but the protection level of the permission should be checked.[Content Provider, targetSdkVersion < 17] | warning | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by a permission at application level which is not defined in the analysed application. As a result, the protection level of the permission should be checked where it is defined. If it is set to normal or dangerous, a malicious application can request and obtain the permission and interact with the component. If it is set to signature, only applications signed with the same certificate can obtain the permission. |
| c_prot_normal_new | is Protected by a permission, but the protection level of the permission should be checked if the application runs on a device where the the API level is less than 17 [Content Provider, targetSdkVersion >= 17] | warning | The Content Provider (%s) would be exported if the application ran on a device where the the API level was less than 17. In that situation, it would still be protected by a permission. However, the protection level of the permission is set to normal. This means that a malicious application could request and obtain the permission and interact with the component. If it was set to signature, only applications signed with the same certificate could obtain the permission. |
| c_prot_danger_new | is Protected by a permission, but the protection level of the permission should be checked if the application runs on a device where the the API level is less than 17.[Content Provider, targetSdkVersion >= 17] | warning | The Content Provider(%s) would be exported if the application ran on a device where the the API level was less than 17. In that situation, it would still be protected by a permission. However, the protection level of the permission is set to dangerous. This means that a malicious application could request and obtain the permission and interact with the component. If it was set to signature, only applications signed with the same certificate could obtain the permission. |
| c_prot_unknown_new | is Protected by a permission, but the protection level of the permission should be checked if the application runs on a device where the the API level is less than 17.[Content Provider, targetSdkVersion >= 17] | warning | The Content Provider(%s) would be exported if the application ran on a device where the the API level was less than 17. In that situation, it would still be protected by a permission which is not defined in the analysed application. As a result, the protection level of the permission should be checked where it is defined. If it is set to normal or dangerous, a malicious application can request and obtain the permission and interact with the component. If it is set to signature, only applications signed with the same certificate can obtain the permission. |
| c_prot_normal_new_appl | is Protected by a permission at the application level should be checked, but the protection level of the permission if the application runs on a device where the the API level is less than 17.[Content Provider, targetSdkVersion >= 17] | warning | The Content Provider (%s) would be exported if the application ran on a device where the the API level was less than 17. In that situation, it would still be protected by a permission. However, the protection level of the permission is set to normal. This means that a malicious application could request and obtain the permission and interact with the component. If it was set to signature, only applications signed with the same certificate could obtain the permission. |
| c_prot_danger_new_appl | is Protected by a permission at the application level, but the protection level of the permission should be checked if the application runs on a device where the the API level is less than 17.[Content Provider, targetSdkVersion >= 17] | warning | The Content Provider(%s) would be exported if the application ran on a device where the the API level was less than 17. In that situation, it would still be protected by a permission. However, the protection level of the permission is set to dangerous. This means that a malicious application could request and obtain the permission and interact with the component. If it was set to signature, only applications signed with the same certificate could obtain the permission. |
| c_prot_unknown_new_appl | is Protected by a permission at the application level, but the protection level of the permission should be checked if the application runs on a device where the the API level is less than 17.[Content Provider, targetSdkVersion >= 17] | warning | The Content Provider(%s) would be exported if the application ran on a device where the the API level was less than 17. In that situation, it would still be protected by a permission which is not defined in the analysed application. As a result, the protection level of the permission should be checked where it is defined. If it is set to normal or dangerous, a malicious application can request and obtain the permission and interact with the component. If it is set to signature, only applications signed with the same certificate can obtain the permission. |
| a_dailer_code | Dailer Code: Found <br>[android:scheme="android_secret_code"] | warning | A secret code was found in the manifest. These codes, when entered into the dialer grant access to hidden content that may contain sensitive information. |
| a_sms_receiver_port | Data SMS Receiver Set on Port: Found<br>[android:port] | warning | A binary SMS receiver is configured to listen on a port. Binary SMS messages sent to a device are processed by the application in whichever way the developer choses. The data in this SMS should be properly validated by the application. Furthermore, the application should assume that the SMS being received is from an untrusted source. |
| a_high_intent_priority | High Intent Priority [android:priority] | warning | By setting an intent priority higher than another intent, the app effectively overrides other requests. |
| a_high_action_priority | High Action Priority [android:priority] | warning | By setting an action priority higher than another action, the app effectively overrides other requests. |
info*14
| 规则名 | 条件 | 级别 | 描述 |
| a_boot_aware | App is direct-boot aware [android:directBootAware=true] | info | This app can run before the user unlocks the device. If you're using a custom subclass of Application, and if any component inside your application is direct - boot aware, then your entire custom application is considered to be direct - boot aware.During Direct Boot, your application can only access the data that is stored in device protected storage. |
| a_network_sec | App has a Network Security Configuration [android:networkSecurityConfig] | info | The Network Security Configuration feature lets apps customize their network security settings in a safe, declarative configuration file without modifying app code. These settings can be configured for specific domains and for a specific app. |
| a_prot_sign | is Protected by a permission.[android:exported=true] | info | A%s %s is found to be exported, but is protected by permission. |
| a_prot_sign_sys | is Protected by a permission, but the protection level of the permission should be checked.[android:exported=true] | info | A%s %s is found to be exported, but is protected by a permission. However, the protection level of the permission is set to signatureOrSystem. It is recommended that signature level is used instead. Signature level should suffice for most purposes, and does not depend on where the applications are installed on the device. |
| a_prot_sign_appl | Protected by a permission at the application level.[android:exported=true] | info | A%s %s is found to be exported, but is protected by a permission at the application level. |
| a_prot_sign_sys_appl | is Protected by a permission at the application level, but the protection level of the permission should be checked.[android:exported=true] | info | A%s %s is found to be exported, but is protected by a permission at the application level. However, the protection level of the permission is set to signatureOrSystem. It is recommended that signature level is used instead. Signature level should suffice for most purposes, and does not depend on where the applications are installed on the device. |
| c_prot_sign | is Protected by a permission.[Content Provider, targetSdkVersion < 17] | info | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by permission. |
| c_prot_sign_sys | is Protected by a permission, but the protection level of the permission should be checked.[Content Provider, targetSdkVersion < 17] | info | A%s %s is found to be exported, but is protected by a permission. However, the protection level of the permission is set to signatureOrSystem. It is recommended that signature level is used instead. Signature level should suffice for most purposes, and does not depend on where the applications are installed on the device. |
| c_prot_sign_appl | is Protected by a permission at the application level.[Content Provider, targetSdkVersion < 17] | info | A%s %s is found to be shared with other apps on the device therefore leaving it accessible to any other application on the device. It is protected by permission at the application level. |
| c_prot_sign_sys_appl | is Protected by a permission at the application level, but the protection level of the permission should be checked.[Content Provider, targetSdkVersion < 17] | info | A%s %s is found to be exported, but is protected by a permission at the application level. However, the protection level of the permission is set to signatureOrSystem. It is recommended that signature level is used instead. Signature level should suffice for most purposes, and does not depend on where the applications are installed on the device. |
| c_prot_sign_new | is Protected by a permission.[Content Provider, targetSdkVersion >= 17] | info | The Content Provider(%s) would be exported if the application ran on a device where the the API level was less than 17. Nevertheless, it is protected by a permission. |
| c_prot_sign_sys_new | is Protected by a permission, but the protection level of the permission should be checked.[Content Provider, targetSdkVersion >= 17] | info | The Content Provider(%s) would be exported if the application ran on a device where the API level was less than 17. In that situation, it would still be protected by a permission. However, the protection level of the permission is set to signatureOrSystem. It is recommended that signature level is used instead. Signature level should suffice for most purposes, and does not depend on where the applications are installed on the device. |
| c_prot_sign_new_appl | is Protected by a permission at the application level.[Content Provider, targetSdkVersion >= 17] | info | The Content Provider(%s) would be exported if the application ran on a device where the the API level was less than 17. Nevertheless, it is protected by a permission. |
| c_prot_sign_sys_new_appl | is Protected by a permission at the application level, but the protection level of the permission should be checked.[Content Provider, targetSdkVersion >= 17] | info | The Content Provider(%s) would be exported if the application ran on a device where the API level was less than 17. In that situation, it would still be protected by a permission. However, the protection level of the permission is set to signatureOrSystem. It is recommended that signature level is used instead. Signature level should suffice for most purposes, and does not depend on where the applications are installed on the device. |
后话
上述的48个manifest的风险项应该是比较全的了,可以当做学习资料和风险checklist进行查询。
相关文章:
【Android】Mobile-Security-Framework-MobSF Manifest 静态扫描规则
前言 移动安全框架(MobSF)是一个自动化的一体化移动应用程序(Android/iOS/Windows)测试、恶意软件分析和安全评估框架,能够执行静态和动态分析。MobSF支持移动应用程序二进制文件(APK、XAPK、IPA和APPX&am…...

【C++】初谈迭代器
文章目录 前言一、什么是迭代器二、迭代器的分类三、迭代器的用法总结 前言 迭代器是一种可以访问和遍历容器中元素的对象,它类似于指针,但是具有更多的功能和灵活性。本文将介绍C迭代器的基本概念、分类、用法和注意事项。 一、什么是迭代器 迭代器&a…...
PL端案例开发手册
目 录 前 言 1 工程编译、程序加载方法 1.1 工程编译 1.2 程序加载 2 led-flash 2.1 案例说明 2.2 操作说明 2.3 关键代码 更多帮助 前 言 本文主要介绍PL端案例的使用说明,适用开发环境:Windows 7/10 64bit、Xilinx Unified 20…...

华为OD-整数对最小和
题目描述 给定两个整数数组array1、array2,数组元素按升序排列。假设从array1、array2中分别取出一个元素可构成一对元素,现在需要取出k对元素,并对取出的所有元素求和,计算和的最小值 代码实现 # coding:utf-8 class Solution:…...

Ubuntu 22LTS 配置静态IP
可行方法,需界面配置 转载自:哔哩哔哩链接地址 命令行配置:待补充...

【Python】Python爬虫:网络数据的提取利器
随着互联网的快速发展,网络数据已经成为了一项重要的资源。如何从海量的网络数据中提取出我们需要的信息,就成为了各个行业都需要解决的问题。而Python爬虫,就是解决这个问题的利器。 首先,让我们了解一下什么是Python爬虫。Pyth…...
20.图的遍历
目录 一. 深度优先遍历 二. 广度优先遍历 图的遍历算法和二叉树不同的是,图中可能存在回路,且图的任一顶点都可能与其它顶点相通,在访问完某个顶点之后可能会沿着某些边又回到了曾经访问过的顶点。为了避免重复访问,我们的解决思…...
ARM DIY(一)电源、SD卡座、SOC 调试
文章目录 前言加热台焊接热风枪吹焊电烙铁补焊电源调试SD 卡座调试DRAM 电路调试串口电路调试SOC 调试成品 前言 之前打样的几块 ARM 板,一直放着没去焊接。今天再次看到,决定把它焊起来。 加热台焊接 为了提高焊接效率,先使用加热台焊接…...

数学建模知识之小白入门篇
数学建模知识--小白入门篇 一、数学模型的定义二、建立数学模型的方法和步骤1. 模型准备2. 模型假设3. 模型构成4. 模型求解5. 模型分析 三、数模竞赛出题的指导思想四、竞赛中的常见题型1. 实际问题背景2.若干假设条件3.要求回答的问题 五、提交一篇论文…...
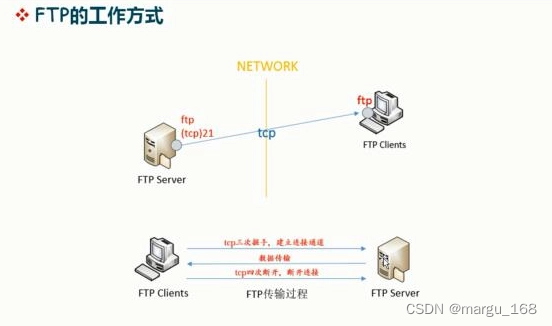
【日常积累】Linux下ftp服务安装
概述 FTP是一种在互联网中进行文件传输的协议,基于客户端/服务器模式,默认使用20、21号端口,其中端口20用于进行数据传输,端口21用于接受客户端发出的相关FTP命令与参数。FTP服务器普遍部署于内网中,具有容易搭建、方…...

确定了,TikTok将于9月12日正式关闭美国半闭环
外媒报道称,TikTok已对其官网的常见问题页面进行了更新。消息显示,其在美国和英国市场运营的半封闭模式将于9月12日正式结束,并将全力推进TikTok闭环小店业务。尽管我们早在本月初就获悉了这一消息,但实际得知后仍不免有些感慨。曾…...

ATFX汇评:英国7月零售销售年率大降,GBPUSD仍未升破1.3000
ATFX汇评:7月季调后零售销售年率,最新值-3.2%,前值-1.6%,降幅扩大;7月季调后核心零售销售年率,最新值-3.4%,前值-1.6%,降幅扩大。零售销售综合衡量除服务业外包括所有主要从事零售业…...
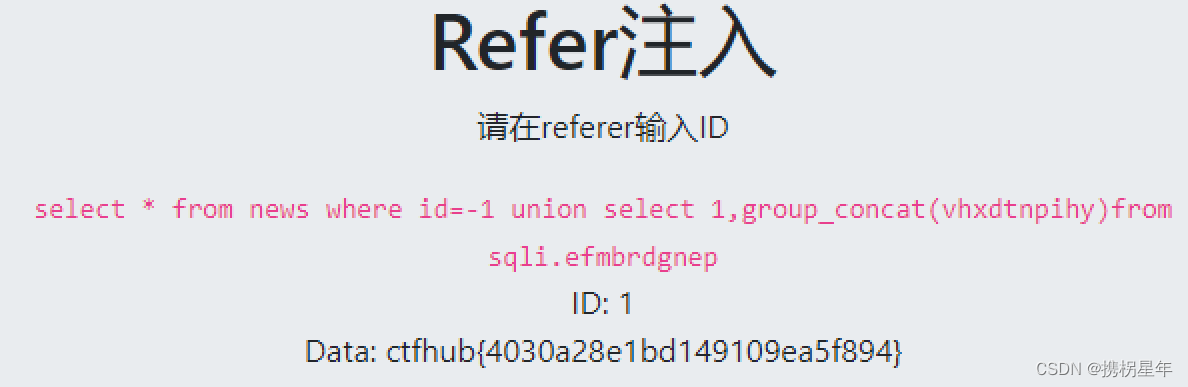
CTFhub-sqli注入-Referer注入
在最后添加 Referer: (注意 R 大写, Referer后面是 :,Content-Length: 与 Referer: 之间没有空行) 1 2 3 1 union select 1,database() -1 union select 1,database() -1 union select 1,group_concat(table_name)from information_sche…...

【案例】登录注册
<template><div class"loginhome"><Header :butShow"butShow"></Header><div class"formdiv"><div style"text-align:center;padding:10px;"><h3>你好登录账号{{ stauts 3? 注册:登录 }}…...
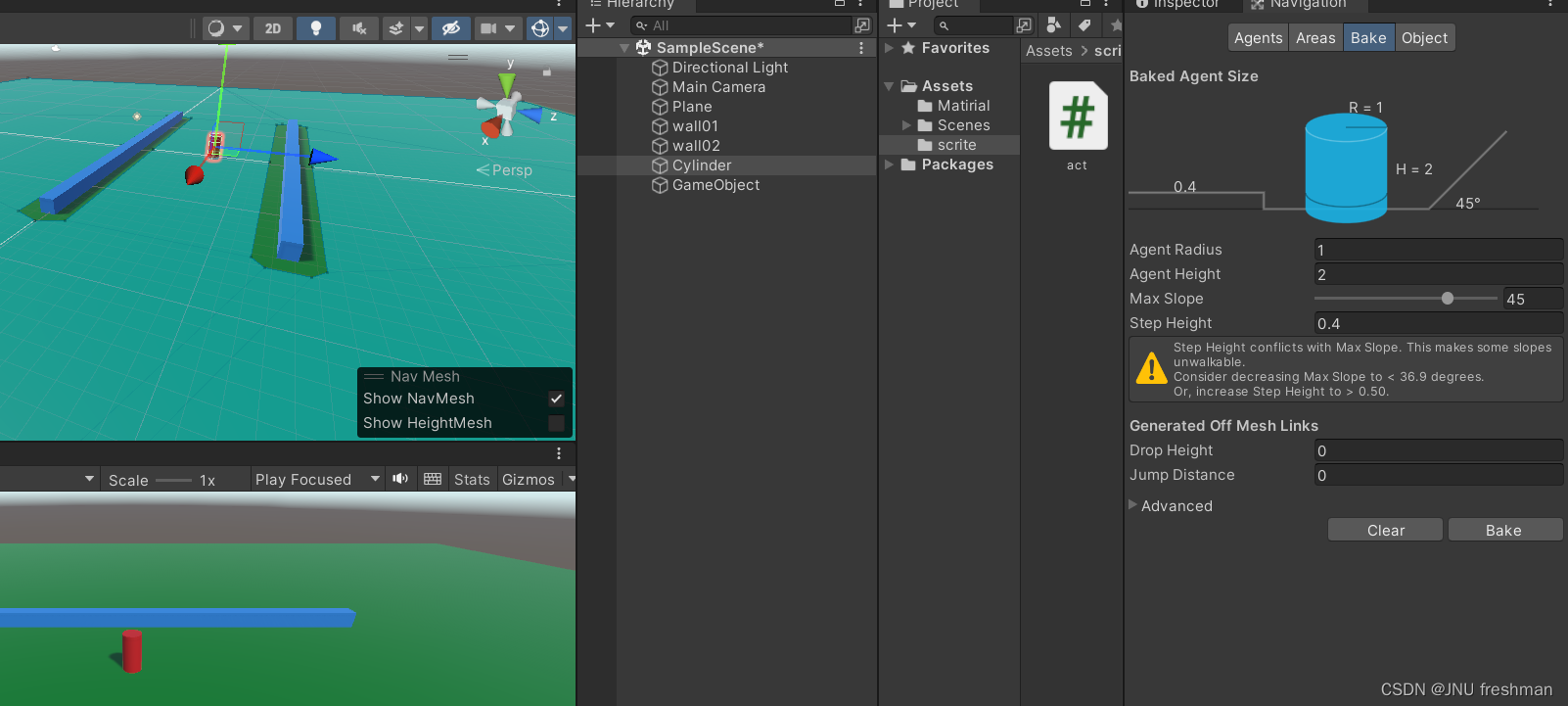
Unity 物体的运动之跟随鼠标
你想让鼠标点击哪里,你的运动的对象就运动到哪里吗? Please follow me ! 首先,你要先添加一个Plane ,以及你的围墙,你的移动的物体 想要实现跟随鼠标移动,我们先创建一个脚本 using System.Collections; using Syst…...
C++基础Ⅱ变量
目录儿 4 变量4.1 原始数据类型字符 char整型 short整型 int整型 long整型 long long单精度浮点型 float双精度浮点型 double布尔型 bool 4.2 sizeof 关键字 5 指针和引用 4 变量 4.1 原始数据类型 原始数据类型是构建C程序的最基础数据类型 所有数据都是基于这些原始数据类型…...

Linux管理SpringBoot应用shell脚本实现
Liunx系统如何部署和管理SpringBoot项目应用呢?最简单的方法就是写个shell脚本。 Spring Boot是Java的一个流行框架,用于开发企业级应用程序。下面我们将学习如何在Linux服务器上部署Spring Boot应用,并通过一个脚本实现启动、停止、重启等操…...
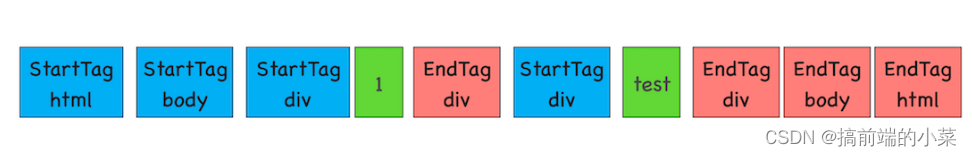
一篇搞懂浏览器的工作原理(万字详解)
摘要 本文是学习极客时间上的课程,进而整理出的浏览器工作原理。 第一部分:浏览器的进程和线程 (1)进程和线程的区别? 在浏览器中,各个进程负责处理自己的事情,而不同的进程中,也…...
)
C语言调用python训练的机器学习模型(项目需求轻体量)
问题描述 机器学习模型基本上都是python下的实现与使用,有关C如何调用训练好的模型或是C实现模型的相关教程相对较少 同时,项目需求整个模型大小尽可能小,大概在几十Kb 由于是表格类型的数据,因此主要考虑树模型 一般而言&#…...

get和post请求的区别以及post请求的url参数问题
1.主要区别 1.GET请求方法有以下几个特点: 默认的请求方法;GET请求通常用于获取信息,所以应该是安全的、幂等的;请求数据表现在URL上,以名称/值的形式发送。对请求的长度有限制;在IE和Opera等浏览器会产生…...

别再只盯着ADC了!74HC4067的另类玩法:DIY一个简易多路信号切换器与逻辑分析仪探头
74HC4067的创意实践:打造多功能信号切换与逻辑分析工具 在电子设计与调试过程中,多路信号切换和逻辑分析是两项基础但至关重要的任务。传统解决方案往往需要昂贵的专业设备,而本文将展示如何利用常见的74HC4067芯片,配合开源硬件和…...
)
从零到一:用Air724UG 4G模块和Python,手把手搭建一个物联网数据上报系统(含完整代码)
从零构建基于Air724UG的物联网数据中台:Python全栈开发实战 当你拿起一块Air724UG 4G模块时,握在手中的不仅是通讯硬件,更是连接物理世界与数字世界的桥梁。这个火柴盒大小的模块能够将田间地头的土壤数据、工厂车间的设备状态、城市角落的环…...

深度解析causal-conv1d:CUDA加速的因果深度卷积专业指南
深度解析causal-conv1d:CUDA加速的因果深度卷积专业指南 【免费下载链接】causal-conv1d Causal depthwise conv1d in CUDA, with a PyTorch interface 项目地址: https://gitcode.com/gh_mirrors/ca/causal-conv1d causal-conv1d是一个专为时间序列数据优化…...

Unpaywall:当学术研究遇上智能助手,如何一键解锁全球开放获取文献
Unpaywall:当学术研究遇上智能助手,如何一键解锁全球开放获取文献 【免费下载链接】unpaywall-extension Firefox/Chrome extension that gives you a link to a free PDF when you view scholarly articles 项目地址: https://gitcode.com/gh_mirrors…...

6.滑动窗口和双指针
文章目录双指针对撞指针快慢指针滑动窗口双指针 双指针:指的是在遍历对象的过程中,不是普通的使用单个指针进行访问,而是使用两个相同方向(快慢指针)或者相反方向(对撞指针)的指针进行扫描&…...

Midscene.js:3大技术突破解决跨平台UI自动化的核心痛点
Midscene.js:3大技术突破解决跨平台UI自动化的核心痛点 【免费下载链接】midscene AI-powered, vision-driven UI automation for every platform. 项目地址: https://gitcode.com/GitHub_Trending/mid/midscene 在当今多平台应用爆发的时代,你是…...

终极指南:5分钟搞定MASA模组全家桶中文汉化,告别英文困扰
终极指南:5分钟搞定MASA模组全家桶中文汉化,告别英文困扰 【免费下载链接】masa-mods-chinese 一个masa mods的汉化资源包 项目地址: https://gitcode.com/gh_mirrors/ma/masa-mods-chinese 还在为Minecraft技术模组的英文界面而头疼吗࿱…...

为什么92%的开发者查不到真正“实时”新闻?Perplexity底层时间戳校验机制首度公开
更多请点击: https://intelliparadigm.com 第一章:为什么92%的开发者查不到真正“实时”新闻?Perplexity底层时间戳校验机制首度公开 当开发者在凌晨三点搜索“React 19 正式发布”,返回结果却显示“发布时间:2024-03…...

VMware Unlocker终极指南:如何在Windows/Linux上免费解锁macOS虚拟机支持
VMware Unlocker终极指南:如何在Windows/Linux上免费解锁macOS虚拟机支持 【免费下载链接】unlocker VMware Workstation macOS 项目地址: https://gitcode.com/gh_mirrors/unloc/unlocker 你是否曾经想在Windows或Linux电脑上运行macOS虚拟机,却…...

Vue3后台管理系统终极指南:V3 Admin Vite 5.0快速上手教程
Vue3后台管理系统终极指南:V3 Admin Vite 5.0快速上手教程 【免费下载链接】v3-admin-vite ☀️ A crafted Vue3 admin template | Vue Admin | Vue Template | Vue3 Admin | Vue3 Template | Vue 后台 | Vue 模板 | Vue3 后台 | Vue3 模板 项目地址: https://git…...
