Tomcat Notes: Web Security, HTTPS In Tomcat
This is a personal study notes of Apache Tomcat. Below are main reference material.
- YouTube Apache Tomcat Full Tutorial,owed by Alpha Brains Courses. https://www.youtube.com/watch?v=rElJIPRw5iM&t=801s
- 1、Overview
- 2、Two Levels Of Web Security
- 2.1、Trace Of A Full Security Example
- 3、Some Security Conceptions
- 3.1、Man-In-The-Middle
- 3.2、 Key Store And Trust Store
- 3.3、Message Digests
- 3.4、Symmetric Encryption And Decryption
- 3.5、Asymmetric Encryption And Decryption
- 4、Process Of HTTPS
1、Overview
This article is about problems in web security, how HTTPS secure sending messages and some basic cryptology algorithm.
I’m not very confident with this article since I never make any practice on those concetions or theorys.
Any advice or correction is welcomed.
2、Two Levels Of Web Security
Web server and web app security covers two distinct but related levels.
Wire-level(transport-level): In this level it encrypts data transmission through all nodes.Users/roles security: User authentication and role authorization. Good news is Tomcat supports ‘Container-managed security’ in which Catalina, rather than a particular web app does this heavy lifting.
HTTPS is a way to secure in this two levels. HTTPS is a way to secure in this level. S of course stands for secure, There a lot of layers atop HTTPS but HTTPS is the most popular and dominant one.
Tomcat uses HTTP by default. We need to turn HTTPS on in TOMCAT_HOME/conf/server.xml. And other operations are also required.
Three problems HTTPS need to solve.
1. The one who sends you messages is who you think it is rather than other one who pretends to be it.
2. The messages are encrypted, even though other people capture the messages but we have the confidence they can't decrypt it.
3. The request(response) recieved by the server(the browser) is exactly same with initially sent by the brower(the server).
Here is the wire-level security and services in Alice-to-Bob messages sending scenario.
-
Peer Authentication (aka mutual chanllenge)
messages #Is it real Bob?Alice <------------->Bob#Is it real Alice? -
Confidentiality (message decryption/encryption)
message encrypted message messageAlice --------->encryption engine------------------>decryption engine--------> Bob -
Integrity:
message messageAlice--------->route------->Bob # does sent messge == recieved message?
2.1、Trace Of A Full Security Example
We are going to explore the details of web security with curl. The curlis used to issue a request over a HTTPSto a deployed web app.
Below is the output of curlissuing a HTTPSrequest.
* About to connect() to localhost port 8443 (#0) # 8443 is the conventional port fo HTTPS in Tomcat
* Trying ::1... connected # while 8080 is for HTTP
* Connected to localhost (::1) port 8443 (#0)
* successfully set certificate verify locations:
* CAfile: none CApath: /etc/ssl/certs #Exchange for certificates
* SSLv3, TLS handshake, Client hello (1):
* SSLv3, TLS handshake, Server hello (2):
* SSLv3, TLS handshake, CERT (11):
* SSLv3, TLS handshake, Server key exchange (12):
* SSLv3, TLS handshake, Server finished (14):
* SSLv3, TLS handshake, Client key exchange (16):
* SSLv3, TLS change cipher, Client hello (1):
* SSLv3, TLS handshake, Finished (20):
* SSLv3, TLS change cipher, Client hello (1):
* SSLv3, TLS handshake, Finished (20): #In handshake, the server and the client need to discuss
* SSL connection using EDH-RSA-DES-CBC3-SHA # which encryption to use and digital certificates.
* Server certificate: ...
* SSL certificate verify result: self signed certificate (18), continuing anyway.
* Server auth using Basic with user 'moe'
# one the SSl and TLS secure the connection, server begins to handle request
> GET /predictions HTTP/1.1
> Authorization: Basic bW9lOk1vZU1vZU1vZQ==
> User-Agent: curl libcurl OpenSSL zlib libidn
> Host: localhost:8443
> Accept: */*
>
< HTTP/1.1 200 OK
< Server: Apache-Coyote/1.1
< Cache-Control: private
< Transfer-Encoding: chunked
...
<
<html>
3、Some Security Conceptions
3.1、Man-In-The-Middle
Man-in-the-middle scenario.
Alice(sender)---------------------->Bob(intended recepient)|| Eve(eavesdropper)
Alice sends messages to Bob and Alice thinks the person she sent messages to is Bob but it is Eve in fact.
Bob thinks he receives messages from Alice but it is Eve in fact.
This is where peer authentication phase come in. It is meant to build trust on the Alice and Bob sides. In other words Alice
sends certificates to Bob to assure Bob that it is really Alice on the other side and Bob do the same thing to Alice to get trust.
3.2、 Key Store And Trust Store
Now let me intrduce more jargon which are key storeand trust store.
Java uses this terminology all over the place and it is also what we are going to use.
They bear directly on the topic of digital certificates.
The key storeis where we keep our digital certificates. So it’s database of our digital certificates. They are just some files.
The trust storeis database of digital certificates that I trust. The trust stroecould be the same with key storeby the way.
3.3、Message Digests
We see this thing before. When we download the Tomcat from Apache official site, we can see sha-1or md5used to verify the integrity, making sure the package we download has exactly same with that in Apache server.
By the way output of the Message Digestcould be encrypted forming a digital signature.
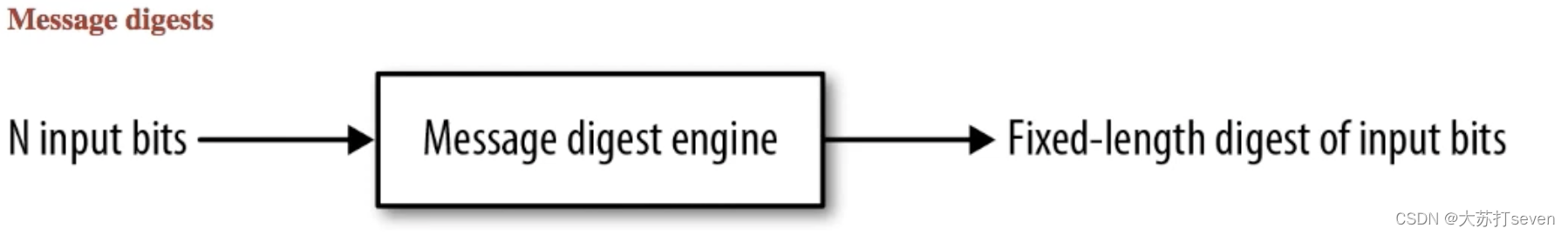
Below is the processes of sending a message, and Message Digestis part of the encryption engine.

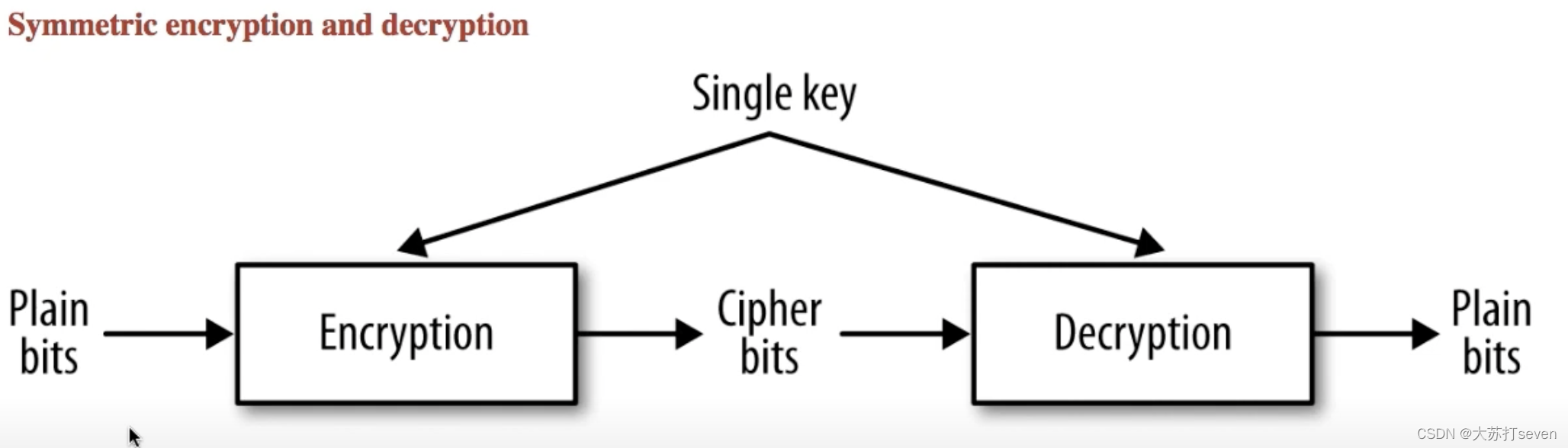
3.4、Symmetric Encryption And Decryption
Now we are going to get further about the encryption keyand the decryption key.
In the modal called Symmetric encryption and decryption, encryption keyand decryption keyis the same one.
It brings a new problem, if Alice has the single key, how can she manage to send the single key to Bob safely or vice versa?
That’s sometimes called the key distribution problem.
The upside of this modal is that it’s fast. Roughly speaking it 1000 times faster than Asymmetric encryption and decryption.
3.5、Asymmetric Encryption And Decryption
In this modal, it uses a pair of key, containing a public keyand a private key, to encryption and decryption.
This pair of key is generated by the recipient. The public keyis used to encryption and the encrypted message can be decrypted only with the private key.
The pulic key can be held by anyone just like its name so it basically can be percieved as an indentity, while the private name can only be held by the recipient.
Supposing Alice wants to send a message to Bob.
- Alice firstly get Bob’s
public key. - Alice encrypts message with the
public key. - Bob recieves the encrypted message then decrypts it with it’s private key.
In this way it assure Alice that her messages can be understood only by Bob.
While it’s not perfect, Alice knows who she sent messages to but Bob does’t know where the messages come from.

4、Process Of HTTPS
With the basis of above conceptions we are going to get into how ‘S’ in HTTPSworks.
Three terms play a role in wire-level security ‘peer authentication’ in particular.
-
Key Pair: A pulic key and a private key. Unlike the asymmetric cryptology, the public key in here is used to decryption while the private key is used to encryption. -
Digital Certificate: Including thekey pairand a digital signature as a voucher for message sent by someone.Digital signature is a message digest encrypted by the private key.
-
Certificate Authority: Company that voucher for adigital certificate.Company voucher for a
DCby adding it’s digital signature to theDC.
HTTPS addresses the man-in-the-middle by having the two sides(Alice and Bob) exchanges their DCto confirm their indenties.
Here’s is the five steps that Alice would go through in order to send messages to Bob.
- Alice sends a signed certificate reqeust containing her name her public key and perhaps some additional information to a
CA. - The
CAcreates a message M from Alice’s request. signing the message M with its private key, thereby creating a seperate signature message SIG, - The
CAreturns Alice the message M with its signature message M. Together M and SIG form Alice’s certificate. - Alice sends her newly minted certificate to Bob to give him access to her public key .
- Bob verfies the signature SIG using the
CA'spublic key. If the signature proves valid, which means the message does come from Alice, he accepts the public key in the certificates as Alice’s public key which is her identity.
相关文章:

Tomcat Notes: Web Security, HTTPS In Tomcat
This is a personal study notes of Apache Tomcat. Below are main reference material. - YouTube Apache Tomcat Full Tutorial,owed by Alpha Brains Courses. https://www.youtube.com/watch?vrElJIPRw5iM&t801s 1、Overview2、Two Levels Of Web Securi…...

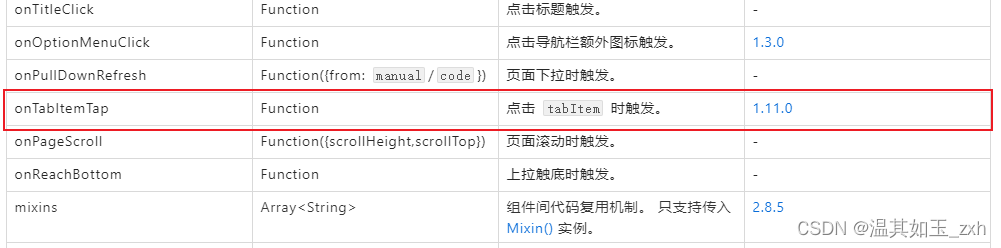
智能小程序登陆能力开发文档及示例代码
小程序登录 涂鸦官方提供了登录能力,开发者可以通过相关 API 获取 App 的用户身份标识,快速的建立小程序内的用户体系。 登录流程 说明 需要调用 ty.login() 获取 临时登录凭证 code,并将 code 传到开发者服务器开发者服务器调用涂鸦云开发…...
常见の算法
前言本文主要使用Java 什么,是快乐星球#¥%……什么是算法? 算法是一组完成任务的指令。任何代码片段都可视为算法,但我们主要介绍常见算法 一、引入——二分查找 二分查找是一种算法,其输入是一个有序的元素列表。如…...

openssl3.2/test/certs - 041 - 1024-bit leaf key
文章目录 openssl3.2/test/certs - 041 - 1024-bit leaf key概述笔记END openssl3.2/test/certs - 041 - 1024-bit leaf key 概述 openssl3.2 - 官方demo学习 - test - certs 笔记 /*! * \file D:\my_dev\my_local_git_prj\study\openSSL\test_certs\041\my_openssl_linux_…...

「创新引领未来」科东软件荣获第十二届中国创新创业大赛(广东·广州赛区)优胜奖
近日,广州市科学技术局公布第十二届中国创新创业大赛(广东广州赛区)暨2023年广州科技创新创业大赛常规赛拟获奖企业名单。科东软件凭借国产化技术创新优势、强大的应用场景落地能力和丰富的行业解决方案,荣获第十二届中国创新创业…...
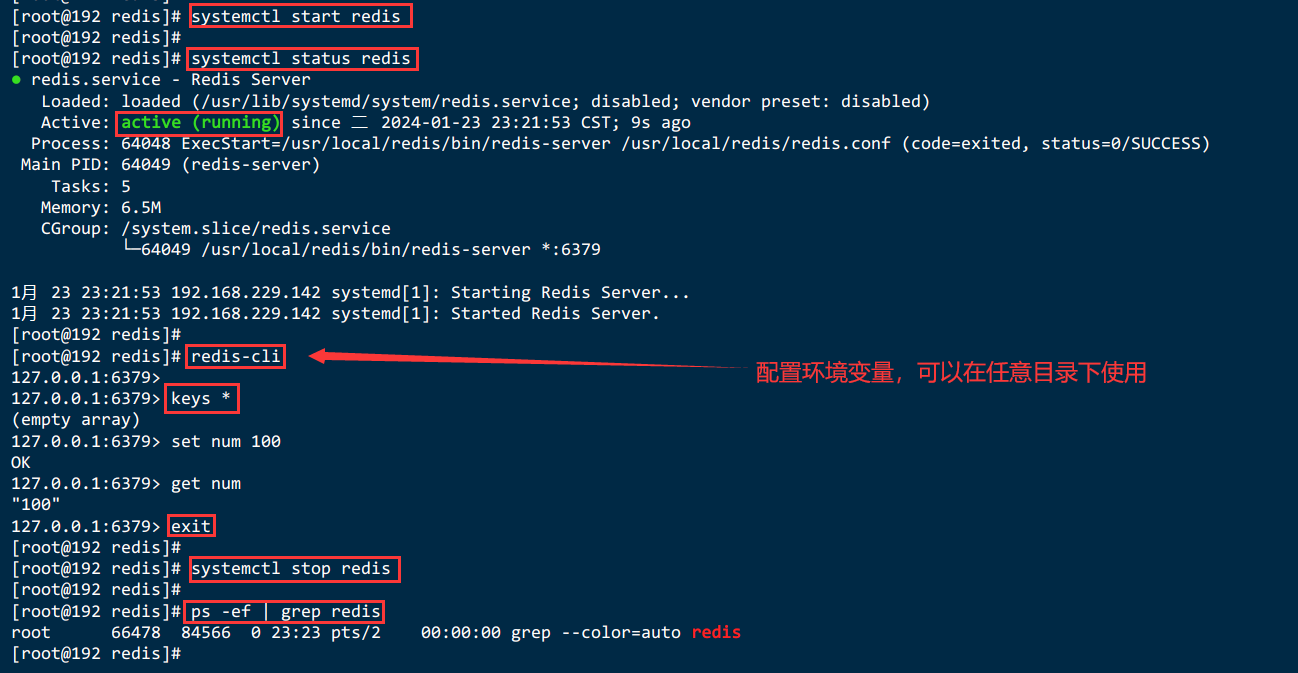
Linux下安装 Redis7
Linux下安装 Redis7 三、Linux下安装 Redis7【redis-7.2.4.tar.gz】3.1.下载redis的安装包3.1.1.手动下载Redis压缩包并上传【redis-7.2.4.tar.gz】3.1.2.wget工具下载redis-7.2.4.tar.gz 3.2.将安装包进行解压缩3.3.进入redis的安装包3.4.检查是否有gcc 环境3.5.编译和安装并指…...

spire.doc合并word文档
文章目录 spire.doc合并word文档1. 引入maven依赖2. 需要合并的word3. 合并文档代码4. 合并结果 spire.doc合并word文档 1. 引入maven依赖 <repositories><repository><id>com.e-iceblue</id><name>e-iceblue</name><url>https://r…...
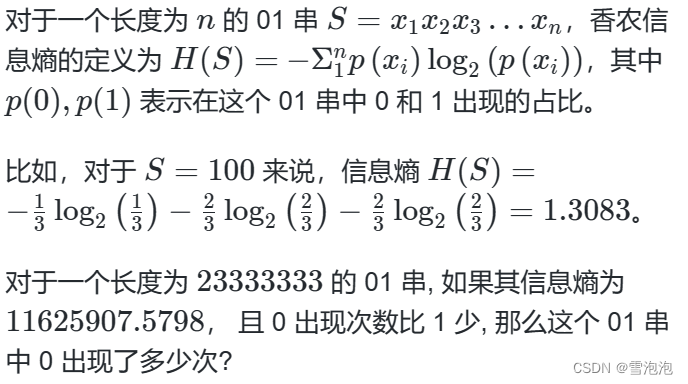
蓝桥杯官网填空题(01串的熵)
问题描述 答案提交 这是一道结果填空的题, 你只需要算出结果后提交即可。本题的结果为一 个整数, 在提交答案时只填写这个整数, 填写多余的内容将无法得分。 import java.util.*;public class Main {public static void main(String[] args) {for(double zero1;zero<2333…...
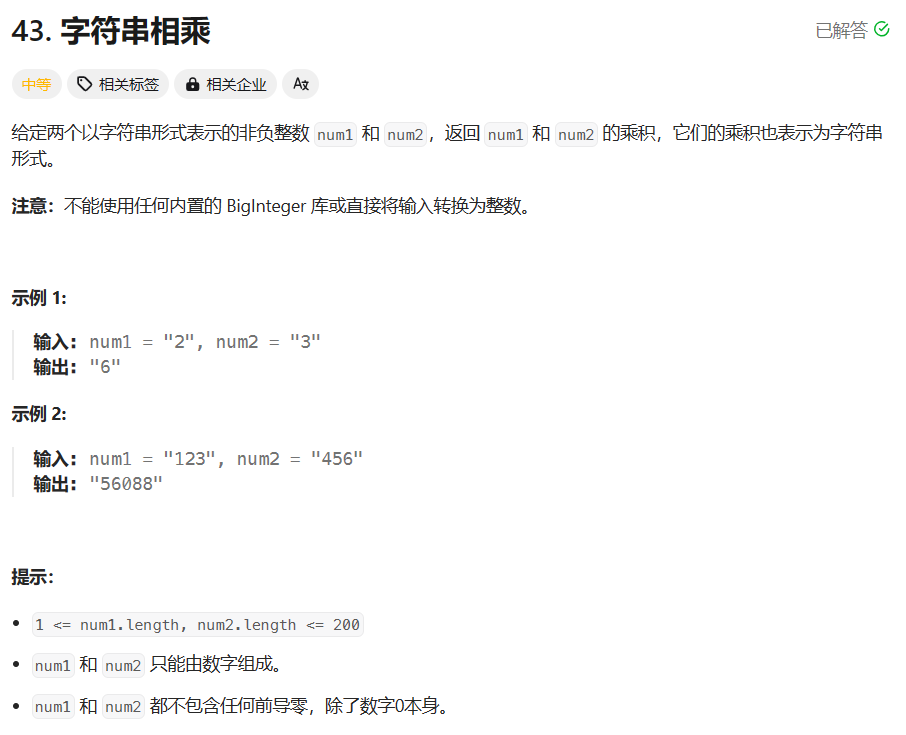
【CodeTop】TOP 100 刷题 51-60
文章目录 51. 缺失的第一个正数题目描述代码与解题思路 52. 训练计划 II题目描述代码与解题思路 53. 子集题目描述代码与解题思路 54. 最小覆盖子串题目描述代码与解题思路 55. 从前序与中序遍历序列构造二叉树题目描述代码与解题思路 56. 零钱兑换题目描述代码与解题思路 57. …...

k8s的图形化工具---rancher
rancher是一个开源的企业级多集群的k8s管理平台。 rancher和k8s的区别:都是为了容器的调度和编排系统。但是rancher不仅可以调度还可以管理整个k8s集群。 rancher自带监控(普罗米修斯) 实验部署 master01 20.0.0.32 node01 20.0.0.34 node02 20.0.0.35 test …...
npm安装卡住问题(最新版)
npm安装卡住问题(最新版) 背景: 最近这两天用npm安装一些包的时候,发现一直卡住: 报错: idealTree:npm: sill idealTree buildDeps之前能用的现在不能用了,我一想,是不是源头的问题,还真是…...
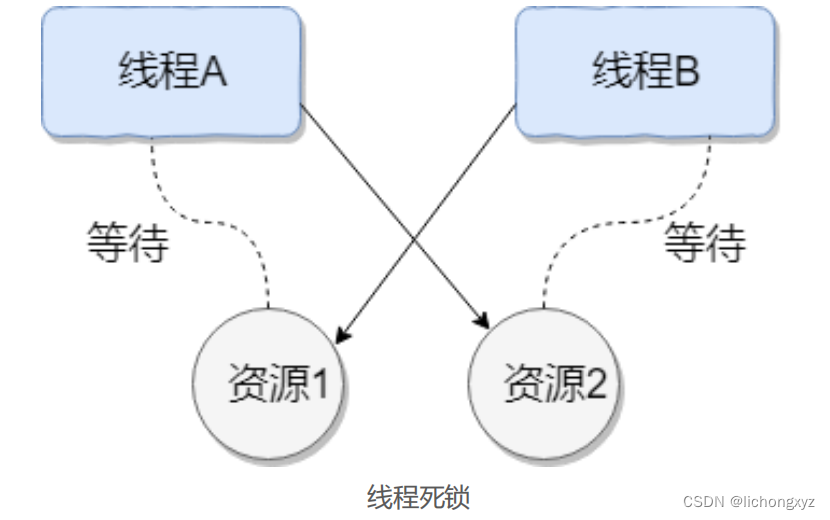
什么是线程死锁
死锁是指两个或两个以上的进程(线程)在执行过程中,由于竞争资 源或者由于彼此通信而造成的一种阻塞的现象,若无外力作用,它们都将无法推 进下去。此时称系统处于死锁状态或系统产生了死锁,这些永远在互相…...
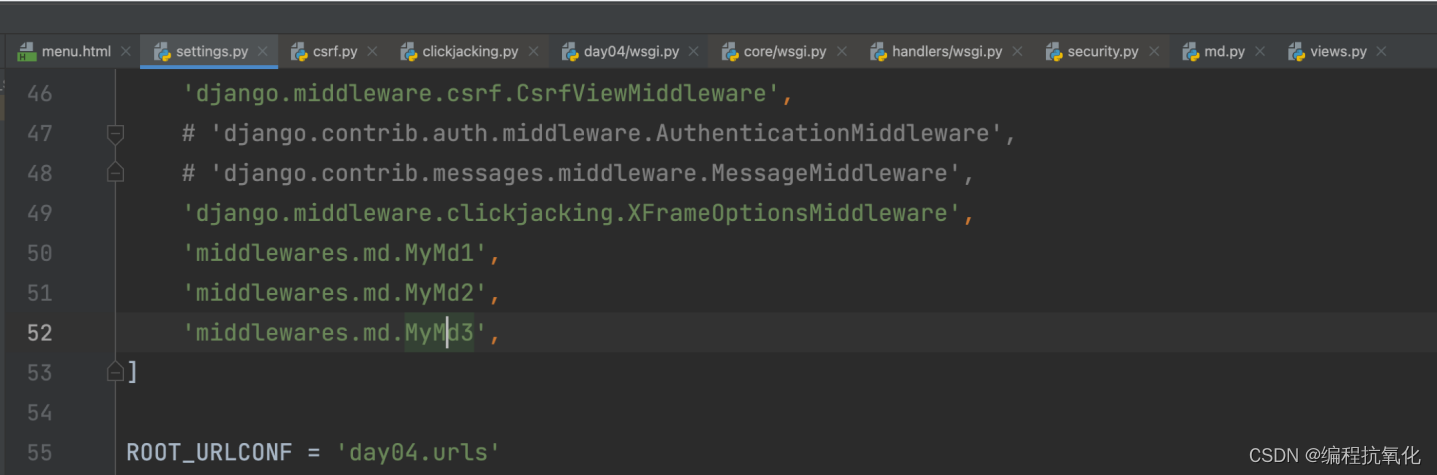
Django从入门到精通(二)
目录 三、视图 3.1、文件or文件夹 3.2、相对和绝对导入urls 3.3、视图参数requests 3.4、返回值 3.5、响应头 3.6、FBV和CBV FBV 四、静态资源 4.1、静态文件 4.2、媒体文件 五、模板 5.1、寻找html模板 5.2、模板处理的本质 5.3、常见模板语法 5.4、内置模板函…...

建筑物防雷检测安全接地应用解决方案
雷电是一种自然现象,具有极高的电压和电流,对建筑物及其内部设备、人员和财产可能造成严重的危害,如火灾、爆炸、电击、电磁干扰等。因此,建筑物必须采取有效的防雷措施,以保障建筑物的安全和可靠运行。建筑物防雷检测…...
支付宝小程序开发踩坑笔记(支付宝、学习强国小程序)
1、接口请求安卓端回调 success,IOS 端回调 fail 原因:dataType 设置不对,默认是 json 格式,对返回数据会进行 json 解析,如果解析失败,就会回调 fail 。加密传输一般是 text 格式。 2、input 禁止输入空格…...
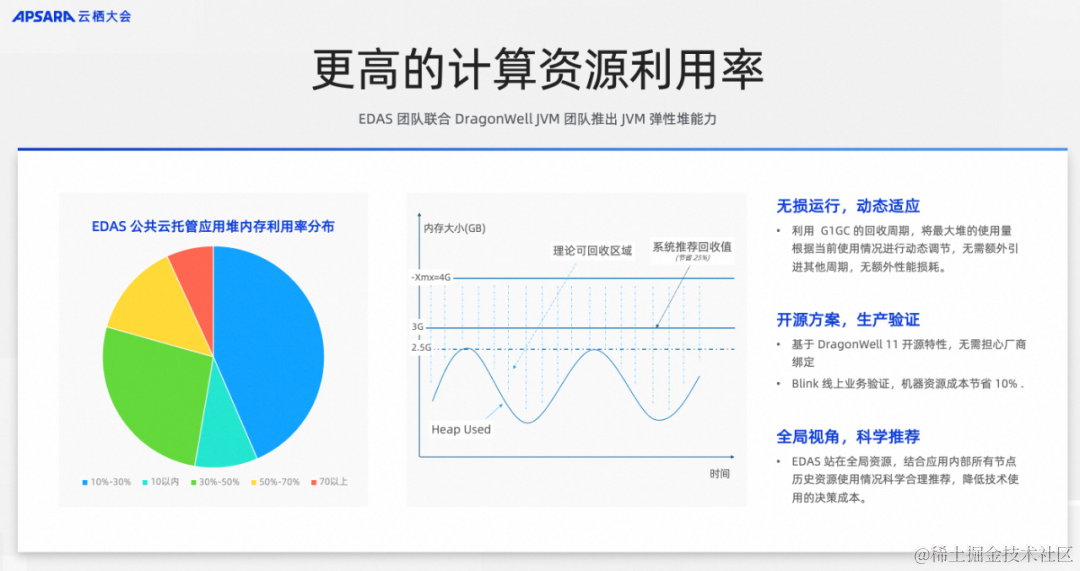
如何降低微服务复杂度丨云栖大会微服务主题分享实录
作者:谢吉宝 本文整理自阿里云资深技术专家、中间件负责人谢吉宝在2023云栖大会《极简微服务模式,降低微服务复杂度的最佳实践》的分享 2023 云栖大会现场 当面临复杂的挑战时,"分而治之"的方法往往能取得显著的效果。微服务架构…...
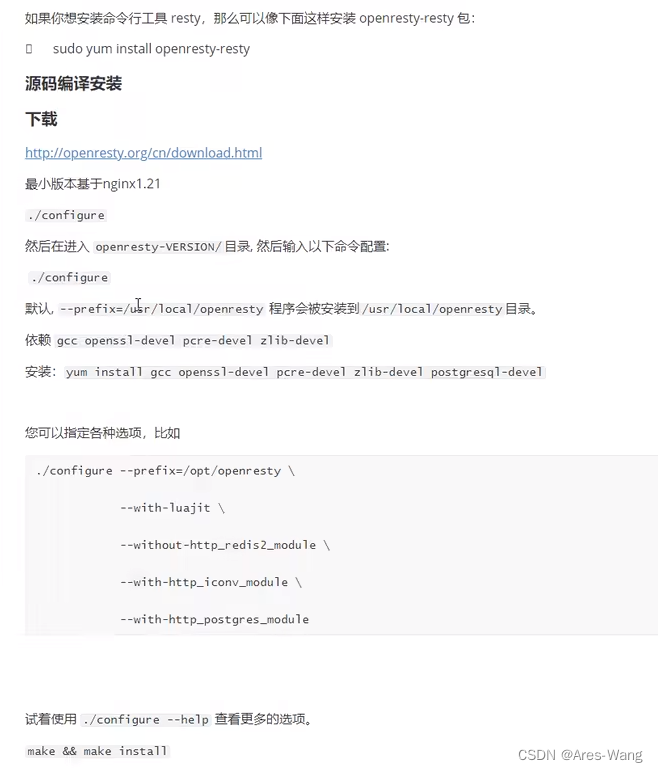
openresty 安装, nginx与 openresty
openresty VS nginx Nginx 是一款高性能的 Web 服务器和反向代理服务器,具备基础的功能如HTTP服务、负载均衡、反向代理以及动静分离等。它是许多互联网应用的核心组件,因其模块化和可扩展的设计而受到欢迎。1 OpenResty 是基于 Nginx 的 Web 平台&…...

puppeteer实现截图
Window服务器说明 1.在本地安装 puppeteer 先创建一个本地文件夹puppeteer,我的地址D:\common_workspace\puppeteer 然后使用cmd打开这个文件夹所在位置,再执行如下两条命令即可。 npm install -g cnpm --registryhttps://registry.npm.taobao.orgcnpm …...
【2024Java面试突击】并发编程、线程池面试实战
前言 最近在更新面试突击专栏,我把每一篇将字数都尽量控制在 2000 字以内,可能在文章里边写的没有那么细致,主要是提供一些 问题 以及 回答的思路 ,以及 面试中可能忽略的漏洞 ,所以在看完文章之后,如果自…...

ASUS华硕无畏Pro15笔记本电脑(M6500QB,M6500QH)工厂模式原厂OEM预装Windows11.22H2系统 含Recovery恢复
原装出厂Windows11系统适用于华硕无畏15笔记本电脑型号:M6500QB和M6500QH 链接:https://pan.baidu.com/s/1AVGLN6-ILIRogOMj48Mk1w?pwdmi7d 提取码:mi7d 带有ASUS RECOVERY恢复功能、自带所有驱动、出厂主题专用壁纸、系统属性联机支持…...

洛谷题解:P15804 [GESP202603 八级] 消息查找
考场上的代码赛后发现改五十个字符就过了,呜呜呜。 题意 给一个图,每个节点指向上一个节点,有最多 100010001000 条附加边,从一个大编号的点指向小编号,快速求任意两点的距离。 思路 由于指向上一个节点的边太浪费…...

为什么你的.NET 9边缘服务在Raspberry Pi 5上启动慢400ms?——基于JIT预编译+LLVM IR优化的3层根因定位法
第一章:为什么你的.NET 9边缘服务在Raspberry Pi 5上启动慢400ms?——基于JIT预编译LLVM IR优化的3层根因定位法在 Raspberry Pi 5(Broadcom BCM2712,4Cortex-A76 2.4GHz,LPDDR4X-4267)上运行 .NET 9 自托…...

STM32内存优化实战:解决Keil5 L6406E报错与SRAM/FLASH分配策略
1. 认识Keil5 L6406E报错:内存不足的典型症状 第一次在Keil5里看到"Error: L6406E: No space in execution regions"这个红色报错时,我正把STM32F103的程序往STM32G0系列芯片移植。编译器的这个报错就像高速公路上的限高杆——明确告诉你装载的…...
)
Docker+SyncTV+cpolar三件套:手把手教你搭建私人同步影院(附固定域名技巧)
DockerSyncTVcpolar三件套:打造高可用私人同步影院实战指南 在数字娱乐需求日益个性化的今天,私人影院的搭建已经从单纯的本地播放升级为兼具社交属性的协同体验。想象一下,无论好友身处何地,都能实时同步观看你精选的影片&#x…...

vue3 父组件向子组件传参
vue3中父组件向子组件传递参数,核心方案是:父组件用 v-bind 绑定数据,子组件用 defineProps 接收数据(组合式 API 语法)。即:v-bind 传 (父) defineProps 收(子ÿ…...

Python AI爬虫实战:爬取张雪峰微博并进行情感分析与词云可视化怕
1. 引入 在现代 AI 工程中,Hugging Face 的 tokenizers 库已成为分词器的事实标准。不过 Hugging Face 的 tokenizers 是用 Rust 来实现的,官方只提供了 python 和 node 的绑定实现。要实现与 Hugging Face tokenizers 相同的行为,最好的办法…...

STM32开发避坑指南:KEIL中__use_no_semihosting报错的终极解决方案
STM32开发避坑指南:KEIL中__use_no_semihosting报错的终极解决方案 在嵌入式开发领域,STM32凭借其出色的性能和丰富的外设资源,成为众多开发者的首选。然而,在使用KEIL MDK进行开发时,不少开发者都会遇到一个令人头疼的…...

WeChatExporter:开源微信聊天记录备份与查看解决方案
WeChatExporter:开源微信聊天记录备份与查看解决方案 【免费下载链接】WeChatExporter 一个可以快速导出、查看你的微信聊天记录的工具 项目地址: https://gitcode.com/gh_mirrors/wec/WeChatExporter 微信作为日常沟通的重要工具,承载着大量有价…...

终极阴阳师自动化指南:如何用OAS脚本每天节省2小时
终极阴阳师自动化指南:如何用OAS脚本每天节省2小时 【免费下载链接】OnmyojiAutoScript Onmyoji Auto Script | 阴阳师脚本 项目地址: https://gitcode.com/gh_mirrors/on/OnmyojiAutoScript 还在为阴阳师无尽的日常任务感到疲惫吗?每天重复的御魂…...

Singularity网络配置完全手册:为集群环境优化容器网络
Singularity网络配置完全手册:为集群环境优化容器网络 【免费下载链接】singularity Singularity has been renamed to Apptainer as part of us moving the project to the Linux Foundation. This repo has been persisted as a snapshot right before the change…...
