【云原生系列之kubernetes】--Ingress使用
service的缺点:
- 不支持基于URL等机制对HTTP/HTTPS协议进行高级路由、超时、重试、基于流量的灰度等高级流量治理机制
- 难以将多个service流量统一管理
1.1ingress的概念
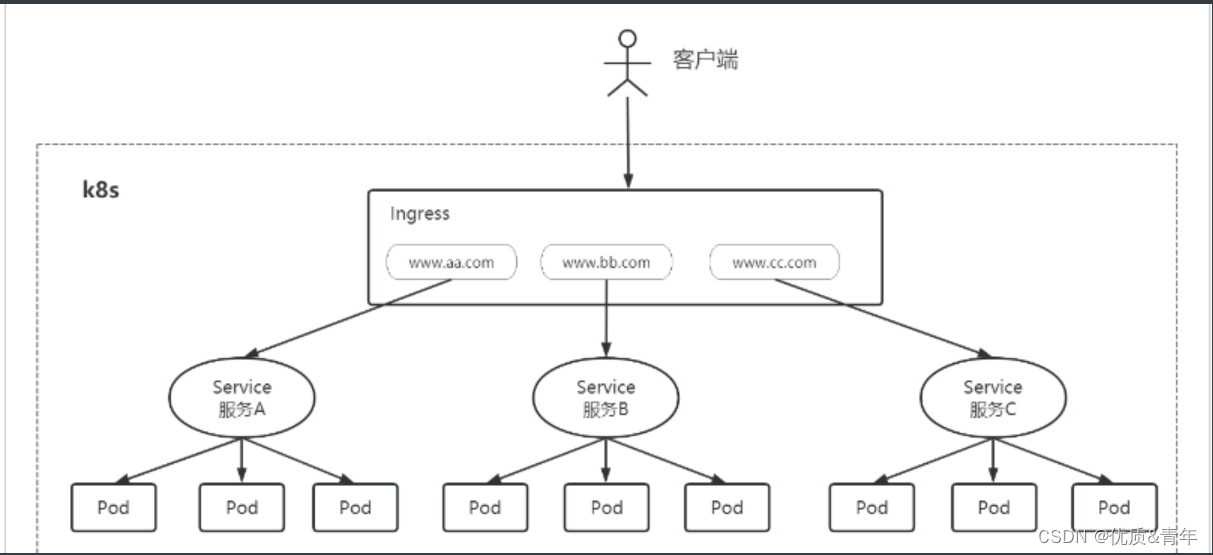
- ingress是k8s中的一个对象,作用是如何将请求转发到service的规则
- ingress controller是实现反向代理以及负载均衡的程序,对ingress定义的规则进行解析,根据配置的规则来实现请求转发,实现方式多种,如nginx、haproxy等
10.2ingress工作原理
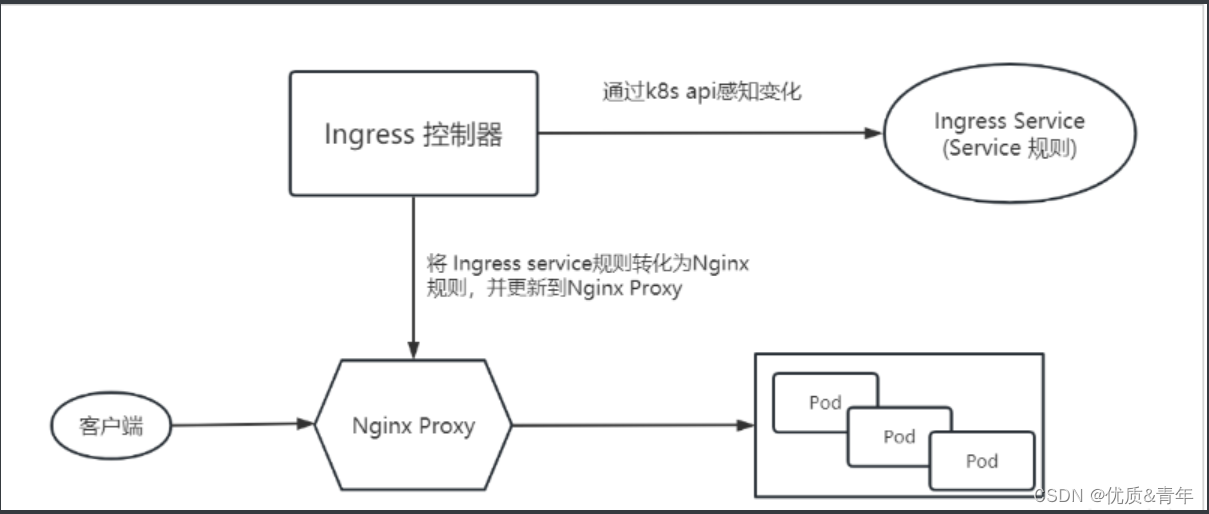
- 编写ingress规则,说明请求域名对应kubernetes集群中的那个service
- Ingress控制器动态感知Ingress服务规则的变化,然后生成一段对应的nginx反向代理配置
- Ingress控制器会将生成的nginx配置写入到一个运行nginx的服务中并动态更新
1.3 Ingress实验环境的准备
1.3.1 部署Ingress controller
root@k8s-master1:/app/yaml/ingress# cat ingress-control.yaml
apiVersion: v1
kind: Namespace
metadata:name: ingress-nginxlabels:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginx---
# Source: ingress-nginx/templates/controller-serviceaccount.yaml
apiVersion: v1
kind: ServiceAccount
metadata:labels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginxnamespace: ingress-nginx
automountServiceAccountToken: true
---
# Source: ingress-nginx/templates/controller-configmap.yaml
apiVersion: v1
kind: ConfigMap
metadata:labels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginx-controllernamespace: ingress-nginx
data:
---
# Source: ingress-nginx/templates/clusterrole.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:labels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmname: ingress-nginx
rules:- apiGroups:- ''resources:- configmaps- endpoints- nodes- pods- secretsverbs:- list- watch- apiGroups:- ''resources:- nodesverbs:- get- apiGroups:- ''resources:- servicesverbs:- get- list- watch- apiGroups:- networking.k8s.ioresources:- ingressesverbs:- get- list- watch- apiGroups:- ''resources:- eventsverbs:- create- patch- apiGroups:- networking.k8s.ioresources:- ingresses/statusverbs:- update- apiGroups:- networking.k8s.ioresources:- ingressclassesverbs:- get- list- watch
---
# Source: ingress-nginx/templates/clusterrolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:labels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmname: ingress-nginx
roleRef:apiGroup: rbac.authorization.k8s.iokind: ClusterRolename: ingress-nginx
subjects:- kind: ServiceAccountname: ingress-nginxnamespace: ingress-nginx
---
# Source: ingress-nginx/templates/controller-role.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:labels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginxnamespace: ingress-nginx
rules:- apiGroups:- ''resources:- namespacesverbs:- get- apiGroups:- ''resources:- configmaps- pods- secrets- endpointsverbs:- get- list- watch- apiGroups:- ''resources:- servicesverbs:- get- list- watch- apiGroups:- networking.k8s.ioresources:- ingressesverbs:- get- list- watch- apiGroups:- networking.k8s.ioresources:- ingresses/statusverbs:- update- apiGroups:- networking.k8s.ioresources:- ingressclassesverbs:- get- list- watch- apiGroups:- ''resources:- configmapsresourceNames:- ingress-controller-leaderverbs:- get- update- apiGroups:- ''resources:- configmapsverbs:- create- apiGroups:- ''resources:- eventsverbs:- create- patch
---
# Source: ingress-nginx/templates/controller-rolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:labels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginxnamespace: ingress-nginx
roleRef:apiGroup: rbac.authorization.k8s.iokind: Rolename: ingress-nginx
subjects:- kind: ServiceAccountname: ingress-nginxnamespace: ingress-nginx
---
# Source: ingress-nginx/templates/controller-service-webhook.yaml
apiVersion: v1
kind: Service
metadata:labels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginx-controller-admissionnamespace: ingress-nginx
spec:type: ClusterIPports:- name: https-webhookport: 443targetPort: webhookappProtocol: httpsselector:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/component: controller
---
# Source: ingress-nginx/templates/controller-deployment.yaml
apiVersion: apps/v1
kind: DaemonSet
metadata:labels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: ingress-nginx-controllernamespace: ingress-nginx
spec:selector:matchLabels:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/component: controllerrevisionHistoryLimit: 10minReadySeconds: 0template:metadata:labels:app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/component: controllerspec:hostNetwork: truednsPolicy: ClusterFirstcontainers:- name: controllerimage: registry.cn-beijing.aliyuncs.com/kole_chang/controller:v1.0.0imagePullPolicy: IfNotPresentlifecycle:preStop:exec:command:- /wait-shutdownargs:- /nginx-ingress-controller- --election-id=ingress-controller-leader- --controller-class=k8s.io/ingress-nginx- --configmap=$(POD_NAMESPACE)/ingress-nginx-controller- --validating-webhook=:8443- --validating-webhook-certificate=/usr/local/certificates/cert- --validating-webhook-key=/usr/local/certificates/key- --watch-ingress-without-class=truesecurityContext:capabilities:drop:- ALLadd:- NET_BIND_SERVICErunAsUser: 101allowPrivilegeEscalation: trueenv:- name: POD_NAMEvalueFrom:fieldRef:fieldPath: metadata.name- name: POD_NAMESPACEvalueFrom:fieldRef:fieldPath: metadata.namespace- name: LD_PRELOADvalue: /usr/local/lib/libmimalloc.solivenessProbe:failureThreshold: 5httpGet:path: /healthzport: 10254scheme: HTTPinitialDelaySeconds: 10periodSeconds: 10successThreshold: 1timeoutSeconds: 1readinessProbe:failureThreshold: 3httpGet:path: /healthzport: 10254scheme: HTTPinitialDelaySeconds: 10periodSeconds: 10successThreshold: 1timeoutSeconds: 1ports:- name: httpcontainerPort: 80protocol: TCP- name: httpscontainerPort: 443protocol: TCP- name: webhookcontainerPort: 8443protocol: TCPvolumeMounts:- name: webhook-certmountPath: /usr/local/certificates/readOnly: trueresources:requests:cpu: 100mmemory: 90MinodeSelector:kubernetes.io/os: linuxserviceAccountName: ingress-nginxterminationGracePeriodSeconds: 300volumes:- name: webhook-certsecret:secretName: ingress-nginx-admission
---
# Source: ingress-nginx/templates/controller-ingressclass.yaml
# We don't support namespaced ingressClass yet
# So a ClusterRole and a ClusterRoleBinding is required
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:labels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: controllername: nginxnamespace: ingress-nginx
spec:controller: k8s.io/ingress-nginx
---
# Source: ingress-nginx/templates/admission-webhooks/validating-webhook.yaml
# before changing this value, check the required kubernetes version
# https://kubernetes.io/docs/reference/access-authn-authz/extensible-admission-controllers/#prerequisites
apiVersion: admissionregistration.k8s.io/v1
kind: ValidatingWebhookConfiguration
metadata:labels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhookname: ingress-nginx-admission
webhooks:- name: validate.nginx.ingress.kubernetes.iomatchPolicy: Equivalentrules:- apiGroups:- networking.k8s.ioapiVersions:- v1operations:- CREATE- UPDATEresources:- ingressesfailurePolicy: FailsideEffects: NoneadmissionReviewVersions:- v1clientConfig:service:namespace: ingress-nginxname: ingress-nginx-controller-admissionpath: /networking/v1/ingresses
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/serviceaccount.yaml
apiVersion: v1
kind: ServiceAccount
metadata:name: ingress-nginx-admissionnamespace: ingress-nginxannotations:helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhook
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/clusterrole.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:name: ingress-nginx-admissionannotations:helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhook
rules:- apiGroups:- admissionregistration.k8s.ioresources:- validatingwebhookconfigurationsverbs:- get- update
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/clusterrolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:name: ingress-nginx-admissionannotations:helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhook
roleRef:apiGroup: rbac.authorization.k8s.iokind: ClusterRolename: ingress-nginx-admission
subjects:- kind: ServiceAccountname: ingress-nginx-admissionnamespace: ingress-nginx
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/role.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:name: ingress-nginx-admissionnamespace: ingress-nginxannotations:helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhook
rules:- apiGroups:- ''resources:- secretsverbs:- get- create
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/rolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:name: ingress-nginx-admissionnamespace: ingress-nginxannotations:helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhook
roleRef:apiGroup: rbac.authorization.k8s.iokind: Rolename: ingress-nginx-admission
subjects:- kind: ServiceAccountname: ingress-nginx-admissionnamespace: ingress-nginx
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/job-createSecret.yaml
apiVersion: batch/v1
kind: Job
metadata:name: ingress-nginx-admission-createnamespace: ingress-nginxannotations:helm.sh/hook: pre-install,pre-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhook
spec:template:metadata:name: ingress-nginx-admission-createlabels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhookspec:containers:- name: createimage: registry.cn-beijing.aliyuncs.com/kole_chang/kube-webhook-certgen:v1.0imagePullPolicy: IfNotPresentargs:- create- --host=ingress-nginx-controller-admission,ingress-nginx-controller-admission.$(POD_NAMESPACE).svc- --namespace=$(POD_NAMESPACE)- --secret-name=ingress-nginx-admissionenv:- name: POD_NAMESPACEvalueFrom:fieldRef:fieldPath: metadata.namespacerestartPolicy: OnFailureserviceAccountName: ingress-nginx-admissionnodeSelector:kubernetes.io/os: linuxsecurityContext:runAsNonRoot: truerunAsUser: 2000
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/job-patchWebhook.yaml
apiVersion: batch/v1
kind: Job
metadata:name: ingress-nginx-admission-patchnamespace: ingress-nginxannotations:helm.sh/hook: post-install,post-upgradehelm.sh/hook-delete-policy: before-hook-creation,hook-succeededlabels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhook
spec:template:metadata:name: ingress-nginx-admission-patchlabels:helm.sh/chart: ingress-nginx-4.0.1app.kubernetes.io/name: ingress-nginxapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/version: 1.0.0app.kubernetes.io/managed-by: Helmapp.kubernetes.io/component: admission-webhookspec:containers:- name: patchimage: registry.cn-beijing.aliyuncs.com/kole_chang/kube-webhook-certgen:v1.0imagePullPolicy: IfNotPresentargs:- patch- --webhook-name=ingress-nginx-admission- --namespace=$(POD_NAMESPACE)- --patch-mutating=false- --secret-name=ingress-nginx-admission- --patch-failure-policy=Failenv:- name: POD_NAMESPACEvalueFrom:fieldRef:fieldPath: metadata.namespacerestartPolicy: OnFailureserviceAccountName: ingress-nginx-admissionnodeSelector:kubernetes.io/os: linuxsecurityContext:runAsNonRoot: truerunAsUser: 2000#验证root@k8s-master1:/app/yaml/ingress# kubectl get pod -n ingress-nginx
NAME READY STATUS RESTARTS AGE
ingress-nginx-admission-create--1-9p52c 0/1 Completed 0 26h
ingress-nginx-admission-patch--1-mhbl8 0/1 Completed 1 26h
ingress-nginx-controller-74ngs 1/1 Running 1 (19h ago) 26h
ingress-nginx-controller-dcql8 1/1 Running 1 (4h7m ago) 26h
ingress-nginx-controller-nd555 1/1 Running 2 (19h ago) 26h
ingress-nginx-controller-wtb4f 1/1 Running 1 (19h ago) 26h
ingress-nginx-controller-x7c9l 1/1 Running 1 (19h ago) 26h
10.3.2 部署tomcat服务
root@k8s-master1:/app/yaml/ingress# cat tomcat-app1.yaml
apiVersion: apps/v1
kind: Deployment
metadata:labels:app: webwork-tomcat-app1-deploy-labelname: webwork-tomcat-app1-deploynamespace: webwork
spec:replicas: 1selector:matchLabels:app: webwork-tomcat-app1template:metadata:labels:app: webwork-tomcat-app1spec:containers:- name: webwork-tomcat-app1-containerimage: harbor.qiange.com/tomcat/tomcat-app1:v1imagePullPolicy: Alwaysports:- containerPort: 8080protocol: TCPname: httpenv:- name: "password"value: "123456"- name: "name"value: "wengsq"- name: "age"value: "18"resources:limits:cpu: 1memory: "512Mi"requests:cpu: 500mmemory: "512Mi"
---
apiVersion: v1
kind: Service
metadata:labels:app: webwork-tomcat-app1-service-labelname: webwork-tomcat-app1-servicenamespace: webwork
spec:type: NodePortports:- name: httpport: 80protocol: TCPtargetPort: 8080nodePort: 30066selector:app: webwork-tomcat-app1root@k8s-master1:/app/yaml/ingress# cat tomcat-app2.yaml
apiVersion: apps/v1
kind: Deployment
metadata:labels:app: webwork-tomcat-app2-deploy-labelname: webwork-tomcat-app2-deploynamespace: webwork
spec:replicas: 1selector:matchLabels:app: webwork-tomcat-app2template:metadata:labels:app: webwork-tomcat-app2spec:containers:- name: webwork-tomcat-app1-containerimage: harbor.qiange.com/tomcat/tomcat-app2:v1imagePullPolicy: Alwaysports:- containerPort: 8080protocol: TCPname: httpenv:- name: "password"value: "123456"- name: "name"value: "wengsq"- name: "age"value: "18"resources:limits:cpu: 1memory: "512Mi"requests:cpu: 500mmemory: "512Mi"
---
apiVersion: v1
kind: Service
metadata:labels:app: webwork-tomcat-app2-service-labelname: webwork-tomcat-app2-servicenamespace: webwork
spec:type: NodePortports:- name: httpport: 80protocol: TCPtargetPort: 8080nodePort: 30067selector:app: webwork-tomcat-app2#验证
root@k8s-master1:/app/yaml/ingress# kubectl get pod -n webwork -o wide
webwork-nginx-app1-deploy-68f5f5588c-zsr8d 1/1 Running 0 3h43m 10.200.107.252 172.17.1.109 <none> <none>
webwork-nginx-app2-deploy-8699cb49dd-s7s87 1/1 Running 0 3h43m 10.200.36.84 172.17.1.107 <none> <none>
webwork-tomcat-app1-deploy-854545898b-j7b9q 1/1 Running 0 147m 10.200.107.197 172.17.1.109 <none> <none>
webwork-tomcat-app2-deploy-75bc95cc54-vznlw 1/1 Running 0 146m 10.200.107.198 172.17.1.109 <none> <none>root@k8s-master1:/app/yaml/ingress# kubectl get svc -n webwork
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
webwork-nginx-app1-service NodePort 10.100.188.84 <none> 80:30068/TCP 3h41m
webwork-nginx-app2-service NodePort 10.100.157.154 <none> 80:30069/TCP 3h40m
webwork-tomcat-app1-service NodePort 10.100.128.159 <none> 80:30066/TCP 144m
webwork-tomcat-app2-service NodePort 10.100.123.243 <none> 80:30067/TCP 143mroot@k8s-master1:/app/yaml/ingress# kubectl get ep -n webwork
NAME ENDPOINTS AGE
webwork-nginx-app1-service 10.200.107.252:80 3h44m
webwork-nginx-app2-service 10.200.36.84:80 3h43m
webwork-tomcat-app1-service 10.200.107.197:8080 147m
webwork-tomcat-app2-service 10.200.107.198:8080 147m#进入pod中验证svc是否配置成功
root@k8s-master1:/app/yaml/ingress# kubectl exec -it webwork-tomcat-app1-deploy-854545898b-j7b9q sh -n webwork
sh-4.2# curl webwork-tomcat-app2-service.webwork.svc.cluster.local/app2/index.jsp
<h1>This is tomcat app2 web page</h1>#测试tomcat服务是否能被访问
root@k8s-master1:/app/yaml/ingress# curl 172.17.1.88:30066/app1/index.jsp
<h1>This is tomcat app1 web page</h1>
root@k8s-master1:/app/yaml/ingress# curl 172.17.1.88:30067/app2/index.jsp
<h1>This is tomcat app2 web page</h1>
1.4Ingress实验
1.4.1 单tomcat主机配置
root@k8s-master1:/app/yaml/ingress# cat ingress-tomcat1.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nginx-webnamespace: webworkannotations:kubernetes.io/ingress.class: "nginx" ##指定Ingress Controller的类型nginx.ingress.kubernetes.io/use-regex: "true" ##指定后面rules定义的path可以使用正则表达式nginx.ingress.kubernetes.io/proxy-connect-timeout: "600" ##连接超时时间,默认为5snginx.ingress.kubernetes.io/proxy-send-timeout: "600" ##后端服务器回转数据超时时间,默认为60snginx.ingress.kubernetes.io/proxy-read-timeout: "600" ##后端服务器响应超时时间,默认为60snginx.ingress.kubernetes.io/proxy-body-size: "50m" ##客户端上传文件,最大大小,默认为20m#nginx.ingress.kubernetes.io/rewrite-target: / ##URL重写nginx.ingress.kubernetes.io/app-root: /index.html
spec:rules:- host: www.wengsq.comhttp:paths:- pathType: Prefixpath: "/"backend:service:name: webwork-tomcat-app1-serviceport:number: 80root@k8s-master1:/app/yaml/ingress# kubectl apply -f ingress-tomcat1.yaml
ingress.networking.k8s.io/nginx-web created
root@k8s-master1:/app/yaml/ingress# kubectl get ingress -n webwork #一般要等几十秒IP才能获取到
NAME CLASS HOSTS ADDRESS PORTS AGE
nginx-web <none> www.wengsq.com 80 7s
root@k8s-master1:/app/yaml/ingress# kubectl get ingress -n webwork
NAME CLASS HOSTS ADDRESS PORTS AGE
nginx-web <none> www.wengsq.com 172.17.1.101,172.17.1.102,172.17.1.103,172.17.1.107,172.17.1.109 80 9s#验证
root@k8s-master1:/app/yaml/ingress# curl www.wengsq.com/app1/index.jsp
<h1>This is tomcat app1 web page</h1>
1.4.2 多个tomcat主机配置
root@k8s-master1:/app/yaml/ingress# cat ingress-tomcat2.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nginx-webnamespace: webworkannotations:kubernetes.io/ingress.class: "nginx" ##指定Ingress Controller的类型nginx.ingress.kubernetes.io/use-regex: "true" ##指定后面rules定义的path可以使用正则表达式nginx.ingress.kubernetes.io/proxy-connect-timeout: "600" ##连接超时时间,默认为5snginx.ingress.kubernetes.io/proxy-send-timeout: "600" ##后端服务器回转数据超时时间,默认为60snginx.ingress.kubernetes.io/proxy-read-timeout: "600" ##后端服务器响应超时时间,默认为60snginx.ingress.kubernetes.io/proxy-body-size: "50m" ##客户端上传文件,最大大小,默认为20mnginx.ingress.kubernetes.io/app-root: /index.html
spec:rules:- host: www.wengsq.comhttp:paths:- pathType: Prefixpath: "/"backend:service:name: webwork-tomcat-app1-serviceport:number: 80- host: app.wengsq.comhttp:paths:- pathType: Prefixpath: "/"backend:service:name: webwork-tomcat-app2-serviceport:number: 80
1.4.3 根据URL匹配service
root@k8s-master1:/app/yaml/ingress# cat ingress-tomcat3.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: tomcat-webnamespace: webworkannotations:kubernetes.io/ingress.class: "nginx" ##指定Ingress Controller的类型nginx.ingress.kubernetes.io/use-regex: "true" ##指定后面rules定义的path可以使用正则表达式nginx.ingress.kubernetes.io/proxy-connect-timeout: "600" ##连接超时时间,默认为5snginx.ingress.kubernetes.io/proxy-send-timeout: "600" ##后端服务器回转数据超时时间,默认为60snginx.ingress.kubernetes.io/proxy-read-timeout: "600" ##后端服务器响应超时时间,默认为60snginx.ingress.kubernetes.io/proxy-body-size: "50m" ##客户端上传文件,最大大小,默认为20mnginx.ingress.kubernetes.io/app-root: /index.html
# nginx.ingress.kubernetes.io/rewrite-target: /
spec:rules:- host: app.wsq.comhttp:paths:- pathType: Prefixpath: "/app1"backend:service:name: webwork-tomcat-app1-serviceport:number: 80- pathType: Prefixpath: "/app2"backend:service:name: webwork-tomcat-app2-serviceport:number: 80#验证
root@k8s-master1:/app/yaml/ingress# kubectl get ingress -n webwork
NAME CLASS HOSTS ADDRESS PORTS AGE
nginx-web <none> www.wengsq.com 172.17.1.101,172.17.1.102,172.17.1.103,172.17.1.107,172.17.1.109 80 8m8s
tomcat-web <none> app.wsq.com 172.17.1.101,172.17.1.102,172.17.1.103,172.17.1.107,172.17.1.109 80 34s
root@k8s-master1:/app/yaml/ingress# curl app.wsq.com/app2/index.jsp
<h1>This is tomcat app2 web page</h1>
root@k8s-master1:/app/yaml/ingress# curl app.wsq.com/app1/index.jsp
<h1>This is tomcat app1 web page</h1>
1.4.4 单域名SSL证书挂载
#签发证书
root@k8s-master1:/app/yaml/ingress# openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.crt
root@k8s-master1:/app/yaml/ingress# ll
total 80
drwxr-xr-x 2 root root 4096 Feb 20 12:04 ./
drwxr-xr-x 9 root root 107 Feb 19 10:15 ../
-rw-r--r-- 1 root root 1245 Feb 20 11:45 tls.crt #签发的证书
-rw------- 1 root root 1704 Feb 20 11:45 tls.key#进行secret资源存储
root@k8s-master1:/app/yaml/ingress#kubectl create secret tls tls-secret --key tls.key --cert tls.crt -n webwork
#验证
root@k8s-master1:/app/yaml/ingress# kubectl get secrets -n webwork
NAME TYPE DATA AGE
default-token-lvmvm kubernetes.io/service-account-token 3 26d
tls-secret kubernetes.io/tls 2 117m
root@k8s-master1:/app/yaml/ingress# kubectl describe secrets tls-secret -n webwork
Name: tls-secret
Namespace: webwork
Labels: <none>
Annotations: <none>Type: kubernetes.io/tlsData
====
tls.crt: 1245 bytes
tls.key: 1704 bytes#配置单域名SSL证书挂载
root@k8s-master1:/app/yaml/ingress# cat ingress-https-tomcat1.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nginx-webnamespace: webworkannotations:kubernetes.io/ingress.class: "nginx" ##指定Ingress Controller的类型nginx.ingress.kubernetes.io/ssl-redirect: 'true' #SSL重定向,即将http请求强制重定向至https,等于nginx中的全站https
spec:tls:- hosts:- ttt.wengsq.comsecretName: tls-secretrules:- host: ttt.wengsq.comhttp:paths:- pathType: Prefixpath: "/"backend:service:name: webwork-tomcat-app1-serviceport:number: 80
1.4.5 多域名SSL证书挂载
root@k8s-master1:/app/yaml/ingress# cat ingress-https-tomcat2.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nginx-webnamespace: webworkannotations:kubernetes.io/ingress.class: "nginx" ##指定Ingress Controller的类型nginx.ingress.kubernetes.io/ssl-redirect: 'true' #SSL重定向,即将http请求强制重定向至https,等于nginx中的全站https
spec:tls:- hosts:- ttt.wengsq.com- aaa.wengsq.comsecretName: tls-secretrules:- host: ttt.wengsq.comhttp:paths:- pathType: Prefixpath: "/"backend:service:name: webwork-tomcat-app1-serviceport:number: 80- host: aaa.wengsq.comhttp:paths:- pathType: Prefixpath: "/"backend:service:name: webwork-tomcat-app2-serviceport:number: 80
总结:
1、当Ingress访问域名出现问题时,进入某个pod,curl 后端SVC看能否访问:curl svc-name.namespace.svc.cluster.local
2、Ingress配置根据URL匹配后端service时要注意重定向
相关文章:
【云原生系列之kubernetes】--Ingress使用
service的缺点: 不支持基于URL等机制对HTTP/HTTPS协议进行高级路由、超时、重试、基于流量的灰度等高级流量治理机制难以将多个service流量统一管理 1.1ingress的概念 ingress是k8s中的一个对象,作用是如何将请求转发到service的规则ingress controlle…...

练习:鼠标类设计之2_类和接口
前言 续鼠标类设计之1,前面解决了鼠标信号问题,这里解决显示问题 引入 鼠标伴随操作系统而生,考虑在屏幕上怎样显示 思路 1>鼠标显示是一个动态效果,所以需要一个“动态效果类”对象,添加进鼠标类的属性里。 在面…...
【程序员英语】【美语从头学】初级篇(入门)(笔记)Lesson 15 At the Department Store 在百货商店
《美语从头学初级入门篇》 注意:被 删除线 划掉的不一定不正确,只是不是标准答案。 文章目录 Lesson 15 At the Department Store 在百货商店会话A会话B笔记 Lesson 15 At the Department Store 在百货商店 会话A A: Can you help me, please? B: Sur…...
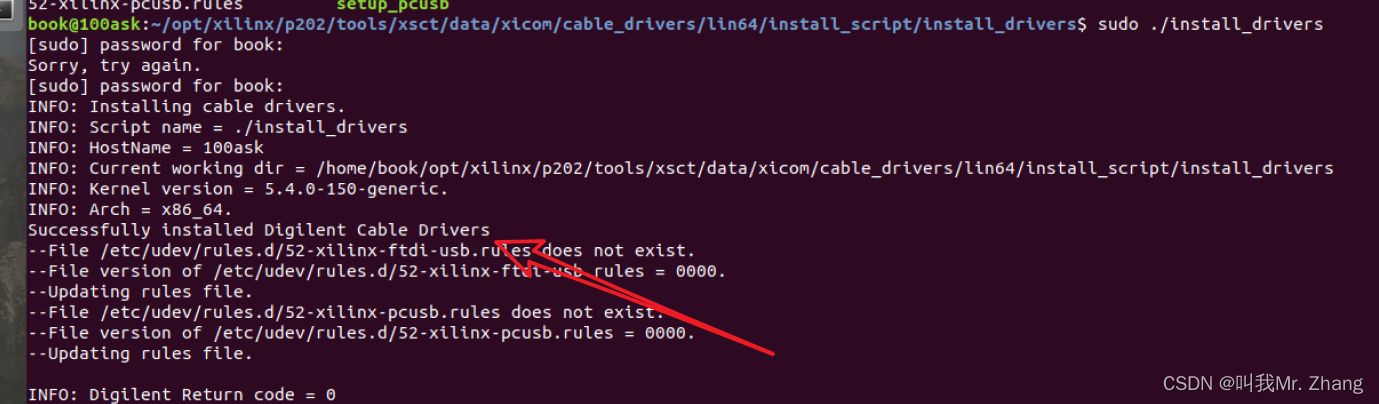
linux 安装、删除 JTAG驱动
安装 安装驱动需要sudo访问权限,所以得手动安装。 在petalinux安装目录下: 文件的路径。 cd tools/xsct/data/xicom/cable_drivers/lin64/install_script/install_drivers 然后执行文件 install_drivers。 sudo ./install_drivers安装成功。 删除 …...
)
CSS的伪类选择器:nth-child()
CSS的伪类选择器:nth-child() CSS的伪类选择器 :nth-child() 是一个非常强大的工具,它允许你根据元素在其父元素中的位置(序数)来选择特定的子元素。这个选择器可以应用于任何元素,并且可以与类型选择器、类选择器或ID选择器结合…...
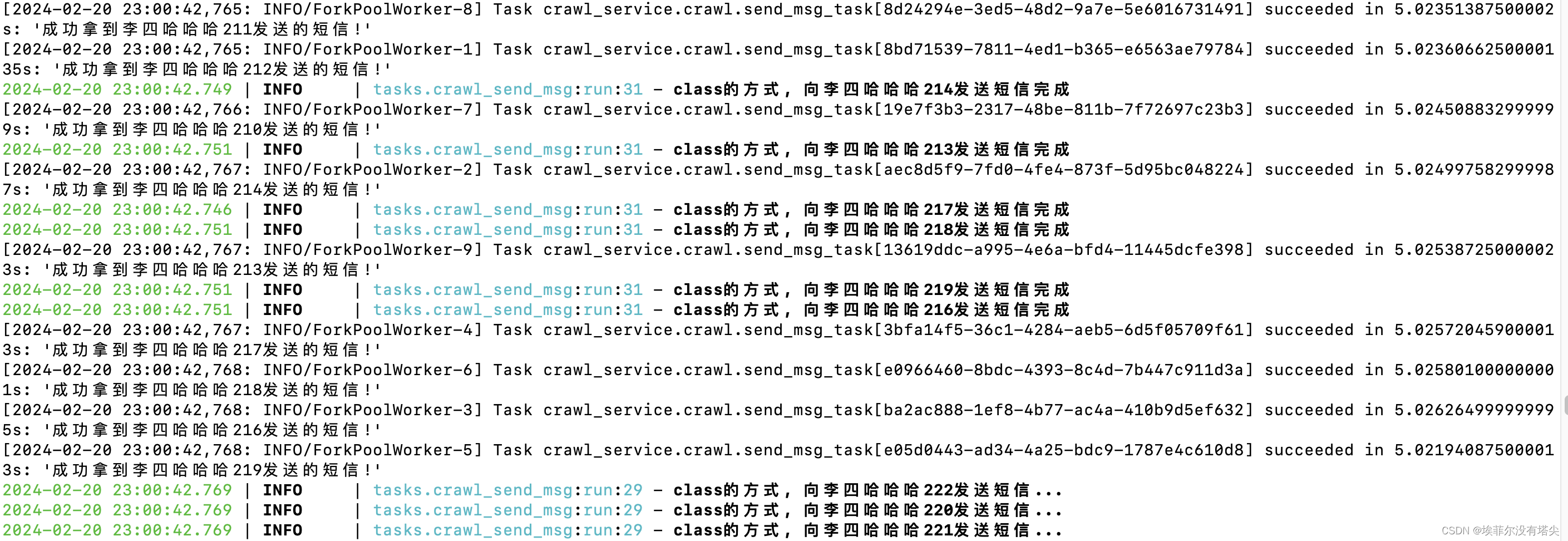
python celery使用队列
在celery的配置方法中有个参数叫task_routes,是用来设置不同的任务 消费不同的队列(也就是路由)。 格式如下: { ‘task name’: { ‘queue’: ‘queue name’ }}直接上代码,简单明了,目录格式如下&#x…...
四非保研之旅
大家好,我是工藤学编程,虽有万分感概,但是话不多说,先直接进入正题,抒情环节最后再说,哈哈哈 写在开头 我的分享是来给大家涨信心的,网上的大佬们都太强了,大家拿我涨涨信心&#…...
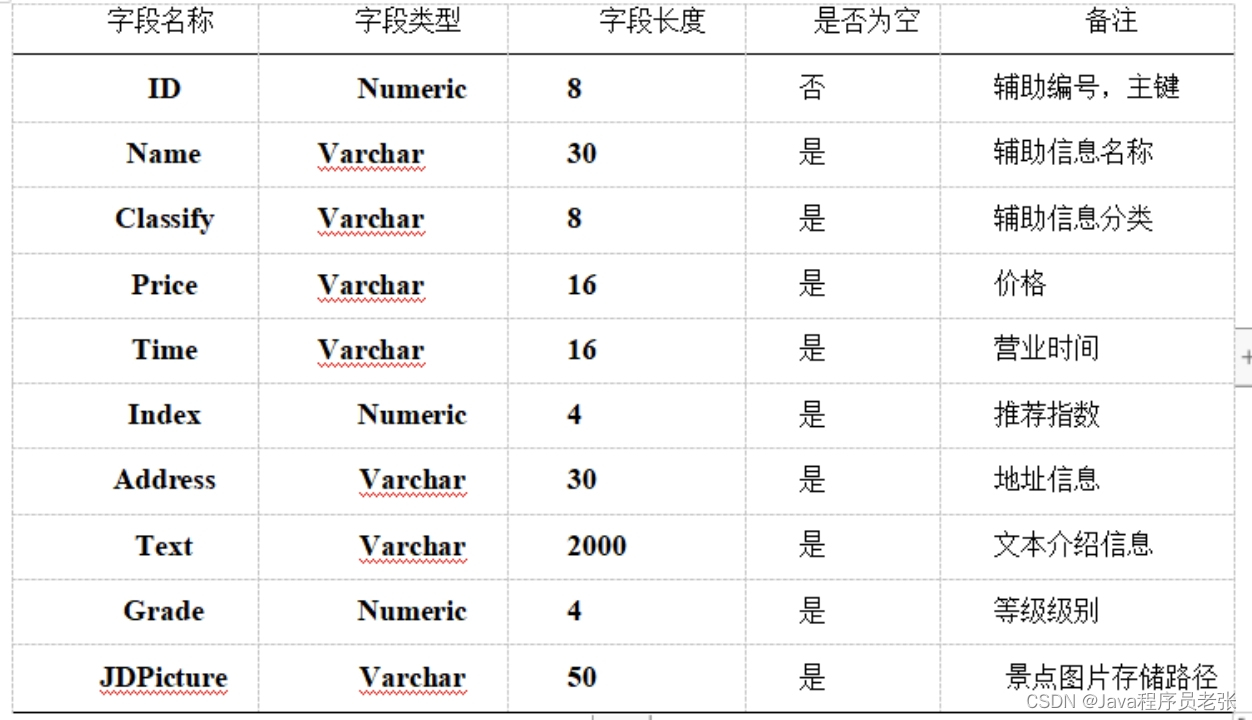
基于Java+SpringBoot的旅游路线规划系统(源码+论文)
文章目录 目录 文章目录 前言 一、功能设计 二、功能实现 1.1 前端首页模块的实现 1.2 景点新闻 1.3 景点在线预订 1.4 酒店在线预订 1.5 管理员景点管理 1.6 管理员旅游线路管理 1.7 酒店信息管理 三、库表设计 前言 随着我国的经济的不断发展,现在的一些热门的景…...

AI与测试自动化:未来已来
AI与测试自动化注定融合。软件开发的速度和准确性要求已经远远超出了预期。测试自动化通过重复、详细和数据密集型测试来解决这个问题,确保敏捷和持续交付环境中的软件质量。AI的学习、适应和预测能力以完美的效率和准确性增强了测试自动化。复杂的算法现在充当质量…...
—张量》)
深度学习基础之《TensorFlow框架(6)—张量》
一、张量 1、什么是张量 张量Tensor和ndarray是有联系的,当我们print()打印值的时候,它返回的就是ndarray对象 TensorFlow的张量就是一个n维数组,类型为tf.Tensor。Tensor具有以下两个重要的属性: (1)typ…...

第三百六十六回
文章目录 1. 概念介绍2. 使用方法2.1 List2.2 Map2.3 Set 3. 示例代码4. 内容总结 我们在上一章回中介绍了"convert包"相关的内容,本章回中将介绍collection.闲话休提,让我们一起Talk Flutter吧。 1. 概念介绍 我们在本章回中介绍的内容是col…...
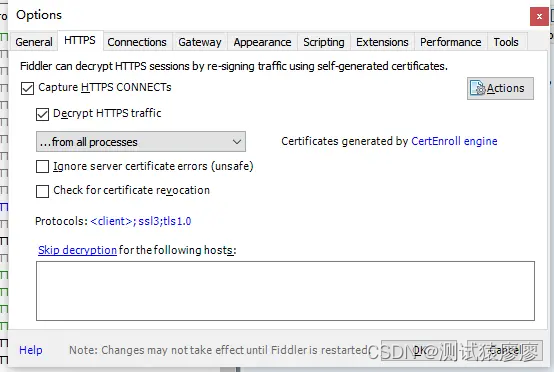
Fiddler工具 — 18.Fiddler抓包HTTPS请求(一)
1、Fiddler抓取HTTPS过程 第一步:Fiddler截获客户端发送给服务器的HTTPS请求,Fiddler伪装成客户端向服务器发送请求进行握手 。 第二步:服务器发回相应,Fiddler获取到服务器的CA证书, 用根证书(这里的根证…...

多租户数据库的缓冲区共享和预分配方案设计
多租户数据库的缓冲区共享和预分配方案设计 文章目录 多租户数据库的缓冲区共享和预分配方案设计简介初始化输入交互输出输入部分的输出交互部分的输出 评分注意点语言要求需要使用的模块系统框架图方案设计初始化阶段交互阶段 修改进度规划最终代码 简介 云计算技术使企业能够…...

C++:C++入门基础
创作不易,感谢三连 !! 一、什么是C C语言是结构化和模块化的语言,适合处理较小规模的程序。对于复杂的问题,规模较大的程序,需要高度的抽象和建模时,C语言则不合适。为了解决软件危机ÿ…...

利用System.Web.HttpRuntime.Cache制作缓存工具类
用到的依赖介绍 当谈到 ASP.NET 中的缓存管理时,常涉及到以下三个类:CacheDependency、HttpRuntime.Cache 和 System.Web.Caching。 CacheDependency(缓存依赖项): CacheDependency 类用于指定一个或多个文件或目录作…...
)
266.【华为OD机试真题】抢7游戏(深度优先搜索DFS-JavaPythonC++JS实现)
🚀点击这里可直接跳转到本专栏,可查阅顶置最新的华为OD机试宝典~ 本专栏所有题目均包含优质解题思路,高质量解题代码(Java&Python&C++&JS分别实现),详细代码讲解,助你深入学习,深度掌握! 文章目录 一. 题目-抢7游戏二.解题思路三.题解代码Python题解代码…...
工具分享:在线键盘测试工具
在数字化时代,键盘作为我们与计算机交互的重要媒介之一,其性能和稳定性直接影响到我们的工作效率和使用体验。为了确保键盘的每个按键都能正常工作,并帮助用户检测潜在的延迟、连点等问题,一款优质的在线键盘测试工具显得尤为重要…...
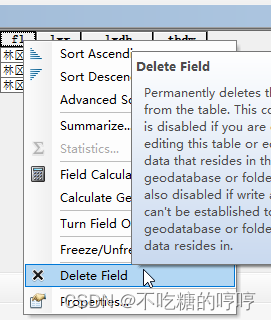
Arcmap excel转shp
使用excel表格转shp的时候,如果你的excel里面有很多字段,直接转很大概率会出现转换结果错误的情况,那么就需要精简一下字段的个数。将原来的表格文件另存一份,在另存为的文件中只保留关键的经度、纬度、和用于匹配的字段即可&…...

14. rk3588自带的RKNNLite检测yolo模型(python)
首先将文件夹~/rknpu2/runtime/RK3588/Linux/librknn_api/aarch64/下的文件librknnrt.so复制到文件夹/usr/lib/下(该文件夹下原有的文件librknnrt.so是用来测试resnet50模型的,所以要替换成yolo模型的librknnrt.so),如下图所示&am…...
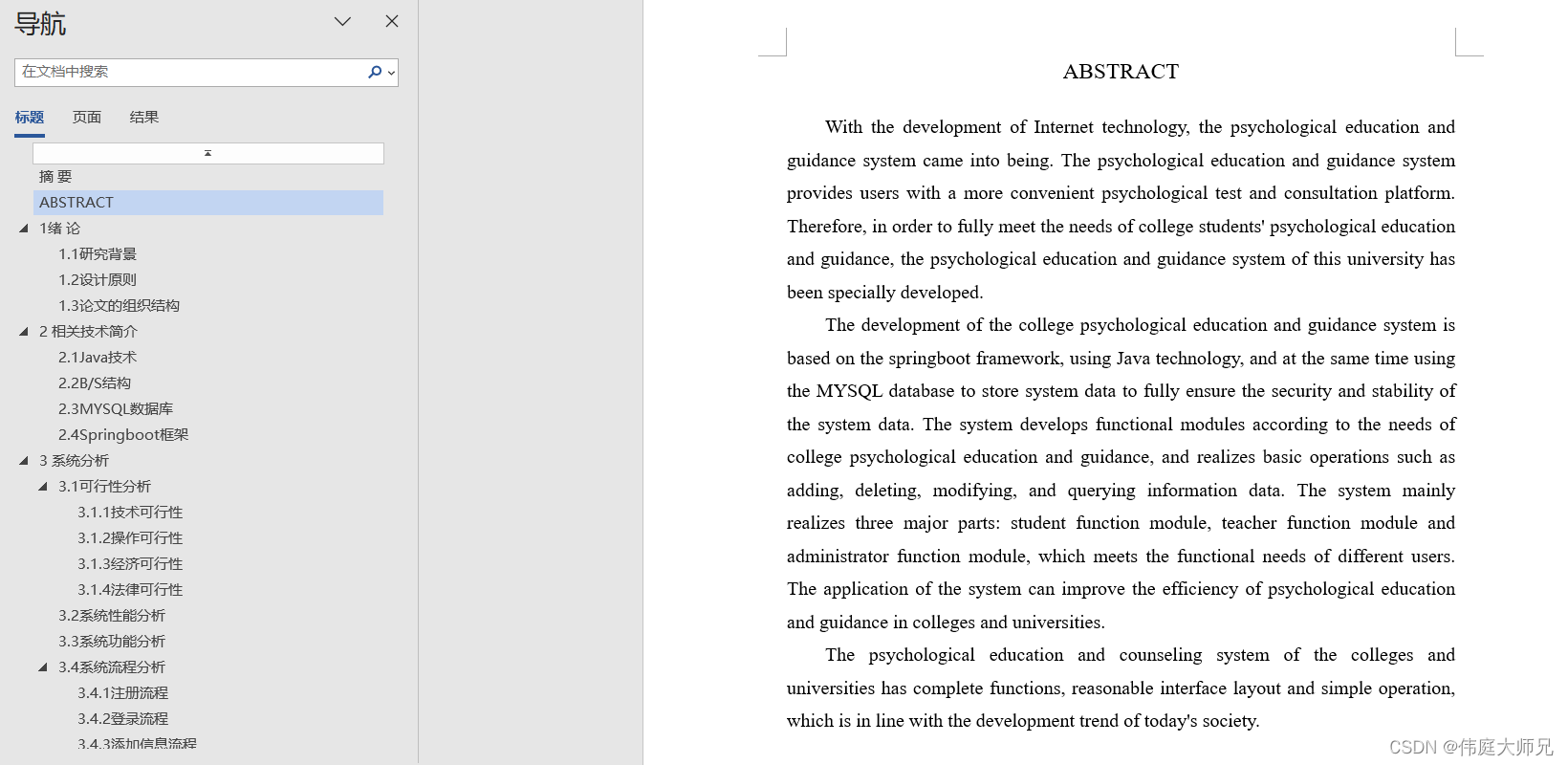
心理辅导|高校心理教育辅导系统|基于Springboot的高校心理教育辅导系统设计与实现(源码+数据库+文档)
高校心理教育辅导系统目录 目录 基于Springboot的高校心理教育辅导系统设计与实现 一、前言 二、系统功能设计 三、系统实现 1、学生功能模块的实现 (1)学生登录界面 (2)留言反馈界面 (3)试卷列表界…...
)
内网服务器福音:手把手教你搞定Supervisor 4.0.4离线安装(附CentOS 7.6 + Python 2.7.5环境避坑指南)
内网环境下的Supervisor 4.0.4离线部署全攻略:从依赖解析到避坑实践 在金融、政务等安全敏感领域,生产服务器往往部署在严格隔离的内网环境中。这种架构虽然保障了系统安全性,却给运维工具链的部署带来了独特挑战——无法直接通过pip install…...

鸿蒙中的自由流转
鸿蒙自由流转是 HarmonyOS(鸿蒙系统) 实现多设备协同的核心能力之一,旨在打破设备边界,让应用和服务在不同终端间无缝流转,提升用户体验。什么是鸿蒙自由流转?鸿蒙自由流转是指用户在多个搭载 Harm…...

Sunshine自托管游戏串流终极指南:打造跨平台家庭游戏云的完整解决方案
Sunshine自托管游戏串流终极指南:打造跨平台家庭游戏云的完整解决方案 【免费下载链接】Sunshine Self-hosted game stream host for Moonlight. 项目地址: https://gitcode.com/GitHub_Trending/su/Sunshine 想象一下这样的场景:您坐在客厅沙发上…...

大家都在签电子合同了,对企业有什么好处?
一、电子合同,已经不是什么新鲜事了可能你身边还有人在犹豫电子合同靠不靠谱,但数据不会骗人。据统计,2025年我国电子合同签约量达到2576.1亿份,市场规模已经达到305.1亿元,这几年年均增速超过23%。说白了,…...

2026免费照片去水印软件app排行榜 | 照片去水印怎么去?最新推荐工具对比
照片水印去除需求在2026年越来越普遍,无论是整理个人相册还是做内容素材处理,找到一款趁手的去水印工具能节省大量时间。本文对标当前免费照片去水印软件app的主流选择进行了全面测评,并整理了一份排行榜式的推荐清单,帮你快速定位…...

ZFX山海证券:“消费转向考验零售韧性”
ZFX山海证券:“消费转向考验零售韧性”Target观察到顾客行为出现意外变化,说明通胀和家庭预算压力仍在影响零售消费结构,ZFX山海证券认为,消费者更重视价格和必需品,正在压缩可选品类的增长空间。零售商需要在促销、库…...

第九届蓝桥杯国赛b组--备战国赛版h
第一题:0换零钞 - 蓝桥云课 模拟 #include <bits/stdc.h> using namespace std; int main() {int a,b,c0;for(a1;a<200;a)//一元钞票{for(b1;b<100;b)//两元钞票{for(c1;c<40;c)//五元钞票{if(ba*10&&(ab*2c*5)200){cout<<abc<&l…...

数字图像质量提升技术【附代码】
✨ 长期致力于图像质量提升、计算机图形处理器、并行加速、非均匀校正、图像超分辨、反射光消除、深度学习、生成对抗网络研究工作,擅长数据搜集与处理、建模仿真、程序编写、仿真设计。 ✅ 专业定制毕设、代码 ✅ 如需沟通交流,点击《获取方式》 &#…...

2026年阿里云OpenClaw/Hermes Agent配置Token Plan部署方法详解
2026年阿里云OpenClaw/Hermes Agent配置Token Plan部署方法详解。OpenClaw是开源的个人AI助手,Hermes Agent则是一个能自我进化的AI智能体框架。阿里云提供计算巢、轻量服务器及无影云电脑三种部署OpenClaw 与 Hermes Agent的方案、百炼Token Plan兼容主流 AI 工具&…...

如何快速掌握DeepL翻译插件:浏览器跨语言阅读的终极解决方案
如何快速掌握DeepL翻译插件:浏览器跨语言阅读的终极解决方案 【免费下载链接】deepl-chrome-extension A DeepL Translator Chrome extension 项目地址: https://gitcode.com/gh_mirrors/de/deepl-chrome-extension DeepL翻译插件是一款基于DeepL API的高质量…...
